Interfaces for Control Components
... Component must get at least 2 slots in a window of 5 Eventually component must get every alternate slot ...
... Component must get at least 2 slots in a window of 5 Eventually component must get every alternate slot ...
The joint distribution of the time to ruin and the number of claims
... as representing the probability that ruin occurs on the (n + 1)th claim and in the interval (t, t + dt). The surplus falls below 0 on the (n + 1)th claim and in the interval (t, t+dt) it there are n claims up to time t of total amount u + ct − x, so that the surplus is x at time t, and if a claim ex ...
... as representing the probability that ruin occurs on the (n + 1)th claim and in the interval (t, t + dt). The surplus falls below 0 on the (n + 1)th claim and in the interval (t, t+dt) it there are n claims up to time t of total amount u + ct − x, so that the surplus is x at time t, and if a claim ex ...
Alleviating tuning sensitivity in Approximate Dynamic Programming
... tool. For example, the LP approach enjoyed some notable success for the applications of playing backgammon [6], elevator scheduling [7], and stochastic reachability problems [8]. However, these examples required significant trial and error tuning in order to find a suitable choice of basis functions ...
... tool. For example, the LP approach enjoyed some notable success for the applications of playing backgammon [6], elevator scheduling [7], and stochastic reachability problems [8]. However, these examples required significant trial and error tuning in order to find a suitable choice of basis functions ...
Chapter 4 Multi-PON architecture 4.1 State-of-the-art
... a dynamic matrix to evaluate the behavior under fluctuations. The electrical queues at nodes are considered infinite. Concerning the traffic model, the packet interarrival time for any traffic class follows a self-similar process implemented as a superposition of 16 strictly alternating independent and id ...
... a dynamic matrix to evaluate the behavior under fluctuations. The electrical queues at nodes are considered infinite. Concerning the traffic model, the packet interarrival time for any traffic class follows a self-similar process implemented as a superposition of 16 strictly alternating independent and id ...
Thomas L. Magnanti and Georgia Perakis
... The constant L we have defined for a linear program defined over a bounded polyhedron satisfies conditions 1-3 of Definition 5 because the basic feasible solutions of a linear programming problem (2) are contained in a ball of radius 2 L (for a proof of this result, see Papadimitriou and Steiglitz [ ...
... The constant L we have defined for a linear program defined over a bounded polyhedron satisfies conditions 1-3 of Definition 5 because the basic feasible solutions of a linear programming problem (2) are contained in a ball of radius 2 L (for a proof of this result, see Papadimitriou and Steiglitz [ ...
Decentralized Control of Distributed Energy Resources in Radial
... Problem (21) amounts to an infinite dimensional convex program, and is, in general, computationally intractable. We therefore resort to approximation by restricting the space of admissible control policies to those which are affine in the disturbance. In addition, we construct a polyhedral inner app ...
... Problem (21) amounts to an infinite dimensional convex program, and is, in general, computationally intractable. We therefore resort to approximation by restricting the space of admissible control policies to those which are affine in the disturbance. In addition, we construct a polyhedral inner app ...
slides ppt
... TCP traffic model • When there are many TCP flows, the aggregate traffic rate xt varies smoothly, according to a differential equation ...
... TCP traffic model • When there are many TCP flows, the aggregate traffic rate xt varies smoothly, according to a differential equation ...
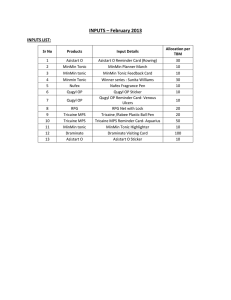
INPUTS – February 2013
... In patients with venous ulcers, reports state that 30% of the total number of isolates are anaerobes, where plain povidone-iodine offers incomplete treatment. In such cases, combination with Ornidazole is beneficial as it is effective against anaerobes, when applied topically. Sir, introducing Qugyl ...
... In patients with venous ulcers, reports state that 30% of the total number of isolates are anaerobes, where plain povidone-iodine offers incomplete treatment. In such cases, combination with Ornidazole is beneficial as it is effective against anaerobes, when applied topically. Sir, introducing Qugyl ...
KA3418051809
... is not considered. Loss Sensitivity Factor method (LSF) (Graham et al., 2000) is based on the principle of linearization of the original nonlinear equation (loss equation) around the initial operating point, which helps to reduce the amount of solution space. The LSF method has widely used to solve ...
... is not considered. Loss Sensitivity Factor method (LSF) (Graham et al., 2000) is based on the principle of linearization of the original nonlinear equation (loss equation) around the initial operating point, which helps to reduce the amount of solution space. The LSF method has widely used to solve ...
Chapter 5: Sample Questions, Problems and Solutions Örnek Sorular (Sample Questions):
... ABCD, ABCF, ABEF, ABEG, AGHD, AGHF, and AGEB The number of hops used is 24. ...
... ABCD, ABCF, ABEF, ABEG, AGHD, AGHF, and AGEB The number of hops used is 24. ...
Global Consistency for Continuous Constraints
... In the general case, constraint satisfaction problems (CSPs) are NP-complete. Trying to solve them by search algorithms, even if theoretically feasible, often results in prohibitive computational cost. One approach to overcome this complexity consists of pre-processing the initial problem using prop ...
... In the general case, constraint satisfaction problems (CSPs) are NP-complete. Trying to solve them by search algorithms, even if theoretically feasible, often results in prohibitive computational cost. One approach to overcome this complexity consists of pre-processing the initial problem using prop ...
IE 495 – Stochastic Programming Problem Set #2 1 Math Time
... Formulate a linear program that decides how much additional capacity to install on each arc in a way that minimizes the total amount of unserviced demand subject to the budgetary restriction. Hint: You will have variables xj for additional capacity, and fir for the amount of demand i that flows on r ...
... Formulate a linear program that decides how much additional capacity to install on each arc in a way that minimizes the total amount of unserviced demand subject to the budgetary restriction. Hint: You will have variables xj for additional capacity, and fir for the amount of demand i that flows on r ...
A Measurement-Based Algorithm to Maximize the Utility of Wireless
... the rate region. The procedure itself consists in a succession of gradient ascents (enhance phases) and random searches (explore phases), and is illustrated in Figure 2 for two flows. The algorithm starts from any rate allocation that is achievable by the scheduling layer and that, by definition, be ...
... the rate region. The procedure itself consists in a succession of gradient ascents (enhance phases) and random searches (explore phases), and is illustrated in Figure 2 for two flows. The algorithm starts from any rate allocation that is achievable by the scheduling layer and that, by definition, be ...
Queue - WordPress.com
... • The only difference between stack and queue is that in case of stack insertion and removable (PUSH and POP) operations are at one end (TOP) only, but in case of a queue Insertion and Deletion take place at two ends called REAR and FRONT of the queue respectively. ...
... • The only difference between stack and queue is that in case of stack insertion and removable (PUSH and POP) operations are at one end (TOP) only, but in case of a queue Insertion and Deletion take place at two ends called REAR and FRONT of the queue respectively. ...
Algorithms with large domination ratio, J. Algorithms 50
... The rest of this paper is organized as follows. In Section 2 we consider the partition problem, Section 3 deals with MaxCut, Section 4 deals with the more general problem of sparse linear equations over GF (2), Section 5 deals with a further generalization, the weighted constraint satisfaction probl ...
... The rest of this paper is organized as follows. In Section 2 we consider the partition problem, Section 3 deals with MaxCut, Section 4 deals with the more general problem of sparse linear equations over GF (2), Section 5 deals with a further generalization, the weighted constraint satisfaction probl ...
Minimax Open Shortest Path First Routing Algorithms in
... Define the following notation s max lL An equivalent formulation of IP’: ...
... Define the following notation s max lL An equivalent formulation of IP’: ...
Minimax Open Shortest Path First Routing Algorithms in Networks
... Define the following notation s max lL An equivalent formulation of IP’: ...
... Define the following notation s max lL An equivalent formulation of IP’: ...
IOSR Journal of Computer Engineering (IOSR-JCE)
... biological genetic and evolution process in the natural environment [1]. A general framework for solving the optimization problem of complex systems is provided, which does not depend on the specific areas of the problems and has strong robustness to various types of problems. An improved genetic al ...
... biological genetic and evolution process in the natural environment [1]. A general framework for solving the optimization problem of complex systems is provided, which does not depend on the specific areas of the problems and has strong robustness to various types of problems. An improved genetic al ...
Randomized local-spin mutual exclusion
... MX lock. Then spin trying to capture node lock. • In addition to randomized and deterministic promotion, an exiting process promotes also the process that holds the MX lock, if any. ...
... MX lock. Then spin trying to capture node lock. • In addition to randomized and deterministic promotion, an exiting process promotes also the process that holds the MX lock, if any. ...
PowerPoint **
... • In a IEEE802.15.4e TSCH network running DeTAS, all devices are assumed to be synchronized with the same slotframe, having size equal to S time slots. ...
... • In a IEEE802.15.4e TSCH network running DeTAS, all devices are assumed to be synchronized with the same slotframe, having size equal to S time slots. ...
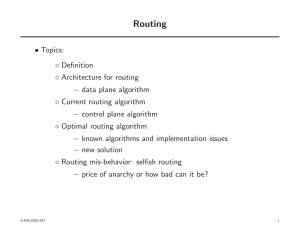
Routing
... • The Dijkstra’s algorithm is totally distributed ◦ It can also be implemented in parallel and ◦ Does not require synchronization • In the algorithm ◦ Dj can be thought of as estimate of shortest path length between 1 and j during the course of algorithm • The algorithm is one of the earliest exampl ...
... • The Dijkstra’s algorithm is totally distributed ◦ It can also be implemented in parallel and ◦ Does not require synchronization • In the algorithm ◦ Dj can be thought of as estimate of shortest path length between 1 and j during the course of algorithm • The algorithm is one of the earliest exampl ...
Round to - Ohio State Computer Science and Engineering
... Sums a range (using multiple criteria and multiple ranges) that meet a specific criteria • All criterion must be true in order for the cell to be summed =SUMIFS(sum_range, criteria_range1,criteria1,[criteria_range2,criteria2], …) Averages a range (using multiple criteria and multiple ranges) that me ...
... Sums a range (using multiple criteria and multiple ranges) that meet a specific criteria • All criterion must be true in order for the cell to be summed =SUMIFS(sum_range, criteria_range1,criteria1,[criteria_range2,criteria2], …) Averages a range (using multiple criteria and multiple ranges) that me ...
Example 1. Insufficiency of the optimality conditions
... and considered a specific example that proved our scheme to be highly effective. However, perfect situations like this are by no means frequent. Unfortunately, there are numerous obstacles on the way of solving optimization problems, and we should get prepared to overcome them. The first counterexam ...
... and considered a specific example that proved our scheme to be highly effective. However, perfect situations like this are by no means frequent. Unfortunately, there are numerous obstacles on the way of solving optimization problems, and we should get prepared to overcome them. The first counterexam ...
LP and Approximation
... polyhedron, then we can calculate the objective value at these points and take the best one as our optimal solution. The Simplex Method intelligently moves from corner ...
... polyhedron, then we can calculate the objective value at these points and take the best one as our optimal solution. The Simplex Method intelligently moves from corner ...
Near-Optimal Algorithms for Maximum Constraint Satisfaction Problems Moses Charikar Konstantin Makarychev
... Lewin, Livnat and Zwick [10] are 0.874 for MAX DICUT and 0.94 for MAX 2SAT. There is a simple approximation preserving reduction from MAX 2CSP to MAX DICUT. Therefore, their algorithm for MAX DICUT can be used for solving MAX 2CSP. Note that their approximation guarantee for an arbitrary MAX 2CSP al ...
... Lewin, Livnat and Zwick [10] are 0.874 for MAX DICUT and 0.94 for MAX 2SAT. There is a simple approximation preserving reduction from MAX 2CSP to MAX DICUT. Therefore, their algorithm for MAX DICUT can be used for solving MAX 2CSP. Note that their approximation guarantee for an arbitrary MAX 2CSP al ...