- TUCAA: The Ultimate Computer Acronyms Archive
... on the subject of fax compatibility, UART requirements, and so on. But he's little out of date: The father asks, "So should I get one with a DSP?" "A what?" says the son. You just can't get far if you're not up on the lingo. You might squeak by in your company of technological nonexperts, but even s ...
... on the subject of fax compatibility, UART requirements, and so on. But he's little out of date: The father asks, "So should I get one with a DSP?" "A what?" says the son. You just can't get far if you're not up on the lingo. You might squeak by in your company of technological nonexperts, but even s ...
The Ultimate Computer Acronyms Archive
... FOR A PARTICULAR PURPOSE AND FREEDOM FROM INFRINGEMENT. The user assumes the entire risk as to the accuracy and the use of this document. This document may be copied and distributed subject to the following conditions: 1. This document must not be altered. 2. This document may not be distributed for ...
... FOR A PARTICULAR PURPOSE AND FREEDOM FROM INFRINGEMENT. The user assumes the entire risk as to the accuracy and the use of this document. This document may be copied and distributed subject to the following conditions: 1. This document must not be altered. 2. This document may not be distributed for ...
- TUCAA: The Ultimate Computer Acronyms Archive
... on the subject of fax compatibility, UART requirements, and so on. But he's little out of date: The father asks, "So should I get one with a DSP?" "A what?" says the son. You just can't get far if you're not up on the lingo. You might squeak by in your company of technological nonexperts, but even s ...
... on the subject of fax compatibility, UART requirements, and so on. But he's little out of date: The father asks, "So should I get one with a DSP?" "A what?" says the son. You just can't get far if you're not up on the lingo. You might squeak by in your company of technological nonexperts, but even s ...
Gnutella2: A Better Gnutella?
... ultrapeers cannot block certain hosts (do not have query keys or unique request addresses). ...
... ultrapeers cannot block certain hosts (do not have query keys or unique request addresses). ...
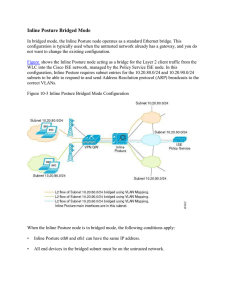
15360608-Inline Posture Bridged Mode
... Downloadable access control lists (DACLs) are building blocks for authorization profiles, and they provide the rules for the profiles to follow. Access control lists (ACLs) prevent unwanted traffic from entering the network by filtering source and destination IP addresses, transport protocols, and o ...
... Downloadable access control lists (DACLs) are building blocks for authorization profiles, and they provide the rules for the profiles to follow. Access control lists (ACLs) prevent unwanted traffic from entering the network by filtering source and destination IP addresses, transport protocols, and o ...
Collection Tree Protocol
... We assume that the collection layer updates stale routing information by sending control beacons. As with data packets, beacons contain the transmitter’s local cost estimate. Unlike data packets, however, control beacons are broadcasts. A single beacon updates many nearby nodes. Collection protocols ...
... We assume that the collection layer updates stale routing information by sending control beacons. As with data packets, beacons contain the transmitter’s local cost estimate. Unlike data packets, however, control beacons are broadcasts. A single beacon updates many nearby nodes. Collection protocols ...
Hyper Converged 250 System for VMware vSphere Installation Guide
... such products and services. Nothing herein should be construed as constituting an additional warranty. Hewlett Packard Enterprise shall not be liable for technical or editorial errors or omissions contained herein. Confidential computer software. Valid license from Hewlett Packard Enterprise require ...
... such products and services. Nothing herein should be construed as constituting an additional warranty. Hewlett Packard Enterprise shall not be liable for technical or editorial errors or omissions contained herein. Confidential computer software. Valid license from Hewlett Packard Enterprise require ...
Business Roles and Architecture to realize MUSE
... Judicious choice of ‘Tight’ & ‘Loose’ QoS Centralized or distributed CAC as per size of network ...
... Judicious choice of ‘Tight’ & ‘Loose’ QoS Centralized or distributed CAC as per size of network ...
Berkeley NOW - Computer Science Division
... • Network Architecture for vast, self-organized collections • Programming Environments for aggregate applications in a noisy world • Distributed Middleware Services (time, trigger, routing, allocation) • Techniques for Fine-grain distributed control • Demonstration Applications ...
... • Network Architecture for vast, self-organized collections • Programming Environments for aggregate applications in a noisy world • Distributed Middleware Services (time, trigger, routing, allocation) • Techniques for Fine-grain distributed control • Demonstration Applications ...
Aalborg Universitet Adaptive Capacity Management in Bluetooth Networks Son, L.T.
... cost VLSI device evolution, short range wireless communications have become more and more popular, especially Bluetooth. Bluetooth is a new short range radio technology that promises to be very convenient, low power, and low cost mobile ad hoc solution for the global interconnection of all mobile de ...
... cost VLSI device evolution, short range wireless communications have become more and more popular, especially Bluetooth. Bluetooth is a new short range radio technology that promises to be very convenient, low power, and low cost mobile ad hoc solution for the global interconnection of all mobile de ...
Robust Services in Dynamic Systems
... Our growing reliance on online services accessible on the Internet demands highlyavailable systems that work correctly without interruption. This thesis extends previous work on Byzantine-fault-tolerant replication to meet the new requirements of current Internet services: scalability and the abilit ...
... Our growing reliance on online services accessible on the Internet demands highlyavailable systems that work correctly without interruption. This thesis extends previous work on Byzantine-fault-tolerant replication to meet the new requirements of current Internet services: scalability and the abilit ...
20740A_08
... Virtual machines: 20740A-LON-DC1 20740A-LON-SVR1 20740A-LON-SVR2 20740A-LON-SVR3 20740A-LON-SVR5 20740A-LON-CL1 User name: Adatum\Administrator Password: Pa$$w0rd Estimated Time: 45 minutes ...
... Virtual machines: 20740A-LON-DC1 20740A-LON-SVR1 20740A-LON-SVR2 20740A-LON-SVR3 20740A-LON-SVR5 20740A-LON-CL1 User name: Adatum\Administrator Password: Pa$$w0rd Estimated Time: 45 minutes ...
RSVP Path computation request and reply messages
... Example: draft-ietf-tewg-interas-mpls-te-req-07.txt related to Inter-AS TE requirements: •“In some cases, policy control might be necessary at the AS boundaries, namely ingress policy controls enabling SPs to enforce the inter-AS policies per interconnect agreements or modify some requested paramete ...
... Example: draft-ietf-tewg-interas-mpls-te-req-07.txt related to Inter-AS TE requirements: •“In some cases, policy control might be necessary at the AS boundaries, namely ingress policy controls enabling SPs to enforce the inter-AS policies per interconnect agreements or modify some requested paramete ...
Practical Structures for Parallel Operating Systems
... UNIX for a PDP-11/23 (a uniprocessor). Provision was made for sharing memory among processes by inheritance. This was done by taking advantage of the existing “shared text” mechanism in the kernel. The normal purpose of the shared text mechanism is to allow several processes running the same program ...
... UNIX for a PDP-11/23 (a uniprocessor). Provision was made for sharing memory among processes by inheritance. This was done by taking advantage of the existing “shared text” mechanism in the kernel. The normal purpose of the shared text mechanism is to allow several processes running the same program ...
Understanding Operating Systems
... operating systems, their functions and goals, and how they interact and interrelate. Part One, the first 12 chapters, describes the theory of operating systems. It concentrates on each of the “managers” in turn and shows how they work together. Then it introduces network organization concepts, secur ...
... operating systems, their functions and goals, and how they interact and interrelate. Part One, the first 12 chapters, describes the theory of operating systems. It concentrates on each of the “managers” in turn and shows how they work together. Then it introduces network organization concepts, secur ...
MIDAS 4x System Design 1.5 MB
... See the Comtech EF Data website at http://www.comtechefdata.com for contact information for a Factory Authorized Service Center. Contact the Factory Authorized Service Center for: • Product support • Information on upgrading or returning a product Contact the Comtech EF Data Customer Support Depart ...
... See the Comtech EF Data website at http://www.comtechefdata.com for contact information for a Factory Authorized Service Center. Contact the Factory Authorized Service Center for: • Product support • Information on upgrading or returning a product Contact the Comtech EF Data Customer Support Depart ...
Red Hat Enterprise Linux 5 EAL4 High-Level Design Version 1.0.1
... 2.1 Product history.......................................................................................................................................3 2.1.1 Red Hat Enterprise Linux...............................................................................................................3 2 ...
... 2.1 Product history.......................................................................................................................................3 2.1.1 Red Hat Enterprise Linux...............................................................................................................3 2 ...
Physics-II: AP 201
... Total 8 no. questions: [Q. 1(a-f) 6X1.5(marks)(compulsory) + (any 4 from Q. 2-8) X 9(marks) = 45] UNIT I: Use of vectors in Physics, Different coordinate systems – Cartesian, cylindrical and spherical polar coordinates, Vector fields and their potentials, gradient, divergence, curl and their physica ...
... Total 8 no. questions: [Q. 1(a-f) 6X1.5(marks)(compulsory) + (any 4 from Q. 2-8) X 9(marks) = 45] UNIT I: Use of vectors in Physics, Different coordinate systems – Cartesian, cylindrical and spherical polar coordinates, Vector fields and their potentials, gradient, divergence, curl and their physica ...
SLES High Level Design Version 3.16 1
... Other company, product, and service names may be trademarks or service marks of others. This document is provided “AS IS” with no express or implied warranties. Use the information in this document at your own risk. This document may be reproduced or distributed in any form without prior permission ...
... Other company, product, and service names may be trademarks or service marks of others. This document is provided “AS IS” with no express or implied warranties. Use the information in this document at your own risk. This document may be reproduced or distributed in any form without prior permission ...
Technologies for Large-Scale Configuration Management
... number of complex network management products. The framework defines systems and sub-systems as collections of software components with certain properties. It provides mechanisms for describing these component collections, deploying and instantiating them and then managing them during their entire l ...
... number of complex network management products. The framework defines systems and sub-systems as collections of software components with certain properties. It provides mechanisms for describing these component collections, deploying and instantiating them and then managing them during their entire l ...
CodeMoctules O O O
... operating system and a system space having a number of memory locations. The core operating system is arranged to create a number of protection domains to partition the system space into a core operating system space and a ...
... operating system and a system space having a number of memory locations. The core operating system is arranged to create a number of protection domains to partition the system space into a core operating system space and a ...
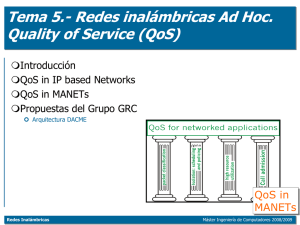
Redes Inalámbricas
... maximum possible power of a signal and the power of corrupting noise that affects the fidelity of its representation. The PSNR is most commonly used as a measure of quality of reconstruction in image compression ...
... maximum possible power of a signal and the power of corrupting noise that affects the fidelity of its representation. The PSNR is most commonly used as a measure of quality of reconstruction in image compression ...
p2p, Fall 05
... – Top 1 percent (333) hosts share 37% (1,142,645) of total files shared – Top 5 percent (1,667) hosts share 70% (1,142,645) of total files shared – Top 10 percent (3,334) hosts share 87% (2,692,082) of total files shared ...
... – Top 1 percent (333) hosts share 37% (1,142,645) of total files shared – Top 5 percent (1,667) hosts share 70% (1,142,645) of total files shared – Top 10 percent (3,334) hosts share 87% (2,692,082) of total files shared ...
Distributed operating system
A distributed operating system is a software over a collection of independent, networked, communicating, and physically separate computational nodes. Each individual node holds a specific software subset of the global aggregate operating system. Each subset is a composite of two distinct service provisioners. The first is a ubiquitous minimal kernel, or microkernel, that directly controls that node’s hardware. Second is a higher-level collection of system management components that coordinate the node's individual and collaborative activities. These components abstract microkernel functions and support user applications.The microkernel and the management components collection work together. They support the system’s goal of integrating multiple resources and processing functionality into an efficient and stable system. This seamless integration of individual nodes into a global system is referred to as transparency, or single system image; describing the illusion provided to users of the global system’s appearance as a single computational entity.