HSR - EPFL
... Nodes are arranged as a ring, each node has two identical interfaces, port A and port B. For each frame to send (“C”-frame), the source node sends two copies over port A and B. The source node removes the frames it injected into the ring. Each node relays a frame it receives from port A to port B an ...
... Nodes are arranged as a ring, each node has two identical interfaces, port A and port B. For each frame to send (“C”-frame), the source node sends two copies over port A and B. The source node removes the frames it injected into the ring. Each node relays a frame it receives from port A to port B an ...
Electrical Engineering and Computer Science Department Technical
... were developed with support from the NSF4 and the DoE5 . This dissertation will be of broad interest to those interested in the structure of system software aimed at massive parallelism. While the supercomputing arena has faced the significant challenges of parallelism for some time now, parallelism ...
... were developed with support from the NSF4 and the DoE5 . This dissertation will be of broad interest to those interested in the structure of system software aimed at massive parallelism. While the supercomputing arena has faced the significant challenges of parallelism for some time now, parallelism ...
Operating systems
... d. Real time. Often used in a dedicated application. The system reads information from sensors and must respond within a fixed amount of time to ensure correct performance. e. Distributed. Distributes computation among several physical processors. The processors do not share memory or a clock. Inste ...
... d. Real time. Often used in a dedicated application. The system reads information from sensors and must respond within a fixed amount of time to ensure correct performance. e. Distributed. Distributes computation among several physical processors. The processors do not share memory or a clock. Inste ...
Operating System - GH Raisoni College Of Engineering Nagpur
... 4) What are different techniques to resolve mutual exclusion ?explain briefly? 5) What is critical section? 6) What is critical region? 7) What is conditional critical region? 8) Write short note on monitor? 9) Explain dining –philosophers problem ? 10) Explain producer-consumer problem? 11) Explai ...
... 4) What are different techniques to resolve mutual exclusion ?explain briefly? 5) What is critical section? 6) What is critical region? 7) What is conditional critical region? 8) Write short note on monitor? 9) Explain dining –philosophers problem ? 10) Explain producer-consumer problem? 11) Explai ...
vRealize Automation Load Balancing
... your NSX topology is configured and that your version of NSX is supported. This document covers the load balancing aspect of an NSX configuration, and assumes that NSX is configured and validated to work properly on the target environment and networks. To verify that your version is supported, see t ...
... your NSX topology is configured and that your version of NSX is supported. This document covers the load balancing aspect of an NSX configuration, and assumes that NSX is configured and validated to work properly on the target environment and networks. To verify that your version is supported, see t ...
An Overlay Data Plane for PlanetLab Department of Computer Science Princeton University
... mentioned earlier) impact the control plane of the overlay while being fairly agnostic as to the form of the overlay’s data plane. In fact, our sense is that there is a significant community of overlay researchers who are mainly interested in working on the control plane. This community would be hap ...
... mentioned earlier) impact the control plane of the overlay while being fairly agnostic as to the form of the overlay’s data plane. In fact, our sense is that there is a significant community of overlay researchers who are mainly interested in working on the control plane. This community would be hap ...
Scalable Routing Strategies for Ad hoc Wireless Networks
... for collaborative, distributed computing) to disaster recovery (e.g., re, ood, earthquake), law enforcement (e.g., crowd control, search-and-rescue) and military (automated battle eld). Key characteristics of these systems are the large number of users, their mobility and the need to support multi ...
... for collaborative, distributed computing) to disaster recovery (e.g., re, ood, earthquake), law enforcement (e.g., crowd control, search-and-rescue) and military (automated battle eld). Key characteristics of these systems are the large number of users, their mobility and the need to support multi ...
Live Migration of Virtual Machines
... a cluster could easily consume the entire bandwidth available between them and hence starve the active services of resources. This service degradation will occur to some extent during any live migration scheme. We address this issue by carefully controlling the network and CPU resources used by the ...
... a cluster could easily consume the entire bandwidth available between them and hence starve the active services of resources. This service degradation will occur to some extent during any live migration scheme. We address this issue by carefully controlling the network and CPU resources used by the ...
FLIP: an Internetwork Protocol for Supporting Distributed Systems,
... traditional network systems. Network systems run all of a user’s applications on a single workstation. Workstations run a copy of the complete operating system; the only thing that is shared is the file system. Applications are sequential; they make no use of any available parallelism. In such an en ...
... traditional network systems. Network systems run all of a user’s applications on a single workstation. Workstations run a copy of the complete operating system; the only thing that is shared is the file system. Applications are sequential; they make no use of any available parallelism. In such an en ...
ElastiCon: An Elastic Distributed SDN Controller
... multi-threaded design [21, 2, 4, 8] in recent years. Despite the significant performance improvement over time, the single-controller systems still have limits on scalability and vulnerability. Some research papers have also explored the implementation of distributed controllers across multiple host ...
... multi-threaded design [21, 2, 4, 8] in recent years. Despite the significant performance improvement over time, the single-controller systems still have limits on scalability and vulnerability. Some research papers have also explored the implementation of distributed controllers across multiple host ...
reducing communication cost in scalable shared memory systems
... we recommend a remote data caching technique that significantly reduces communication cost. We analyze applications by instrumenting their assembly-code sources. During execution, an instrumented application pipes a detailed trace to configuration independent (CIAT) and configuration dependent (CDAT ...
... we recommend a remote data caching technique that significantly reduces communication cost. We analyze applications by instrumenting their assembly-code sources. During execution, an instrumented application pipes a detailed trace to configuration independent (CIAT) and configuration dependent (CDAT ...
using complete machine simulation to understand computer system
... understanding the behavior of modern computer systems. Complete machine simulation differs from existing simulation tools by modeling all of the hardware found in a typical computer system. This allows it to help investigators better understand the behavior of machines running commercial operating s ...
... understanding the behavior of modern computer systems. Complete machine simulation differs from existing simulation tools by modeling all of the hardware found in a typical computer system. This allows it to help investigators better understand the behavior of machines running commercial operating s ...
Bringing Virtualization to the x86 Architecture with the Original
... both the computing industry and academic research. In these early days of computing, virtual machine monitors (VMMs) allowed multiple users, each running their own single-user operating system instance, to share the same costly mainframe hardware [Goldberg 1974]. Virtual machines lost popularity wit ...
... both the computing industry and academic research. In these early days of computing, virtual machine monitors (VMMs) allowed multiple users, each running their own single-user operating system instance, to share the same costly mainframe hardware [Goldberg 1974]. Virtual machines lost popularity wit ...
Bringing Virtualization to the x86 Architecture with
... both the computing industry and academic research. In these early days of computing, virtual machine monitors (VMMs) allowed multiple users, each running their own single-user operating system instance, to share the same costly mainframe hardware [Goldberg 1974]. Virtual machines lost popularity wit ...
... both the computing industry and academic research. In these early days of computing, virtual machine monitors (VMMs) allowed multiple users, each running their own single-user operating system instance, to share the same costly mainframe hardware [Goldberg 1974]. Virtual machines lost popularity wit ...
Willem de Bruijn:
... data movement and processing. Over Unix, it reduces crossing cost by replacing copying with shared memory and indirect access and by replacing context switches with userlevel threading where possible and by batching switches elsewhere. It increases processing efficiency by moving logic to the most s ...
... data movement and processing. Over Unix, it reduces crossing cost by replacing copying with shared memory and indirect access and by replacing context switches with userlevel threading where possible and by batching switches elsewhere. It increases processing efficiency by moving logic to the most s ...
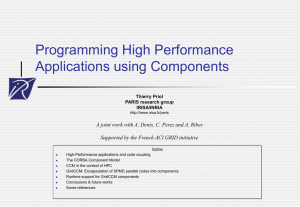
Programming High Performance Applications using Components
... High-Performance applications and code coupling The CORBA Component Model CCM in the context of HPC GridCCM: Encapsulation of SPMD parallel codes into components Runtime support for GridCCM components ...
... High-Performance applications and code coupling The CORBA Component Model CCM in the context of HPC GridCCM: Encapsulation of SPMD parallel codes into components Runtime support for GridCCM components ...
ABSTRACT PROPERTY-BASED INTEGRITY MONITORING OF OPERATING SYSTEM KERNELS
... isolation of, and independently from, the protected operating system and has direct access to the kernel’s runtime state. The basic strategy behind property-based monitoring is to identify a set of properties that are practical to check, yet are effective at detecting the types of ...
... isolation of, and independently from, the protected operating system and has direct access to the kernel’s runtime state. The basic strategy behind property-based monitoring is to identify a set of properties that are practical to check, yet are effective at detecting the types of ...
MODERN OPERATING SYSTEMS Third Edition ANDREW S. …
... • A capability supported by some operating systems that allows one process to communicate with another process. • The processes can be running on the same computer or on different computers connected through a network. • IPC enables one application to control another application, and for several app ...
... • A capability supported by some operating systems that allows one process to communicate with another process. • The processes can be running on the same computer or on different computers connected through a network. • IPC enables one application to control another application, and for several app ...
INS/Twine: A Scalable Peer-to-Peer Architecture for
... multiple orthogonal attributes. For example, imagine a metropolitan resource discovery system, where resolvers are hierarchically organized by institutions, neighborhoods, cities, and finally the metropolitan level. A client may be interested in locating all cameras filming main points of congestion ...
... multiple orthogonal attributes. For example, imagine a metropolitan resource discovery system, where resolvers are hierarchically organized by institutions, neighborhoods, cities, and finally the metropolitan level. A client may be interested in locating all cameras filming main points of congestion ...
Virtual Machines and Virtualization of Clusters and Data Centers
... The purpose of a VM is to enhance resource sharing by many users and improve computer performance in terms of resource utilization and application flexibility. Hardware resources (CPU, memory, I/O devices, etc.) or software resources (operating system and software libraries) can be virtualized in va ...
... The purpose of a VM is to enhance resource sharing by many users and improve computer performance in terms of resource utilization and application flexibility. Hardware resources (CPU, memory, I/O devices, etc.) or software resources (operating system and software libraries) can be virtualized in va ...
The APIC Approach to High Performance Network Interface Design
... Cell Batching: This refers to the ability to batch cells (from the same connection) that are to be read/written from/to contiguous locations in memory, when executing bus transfers. This is motivated by the fact that larger sized bus transfers are usually more efficient (especially when interfacing ...
... Cell Batching: This refers to the ability to batch cells (from the same connection) that are to be read/written from/to contiguous locations in memory, when executing bus transfers. This is motivated by the fact that larger sized bus transfers are usually more efficient (especially when interfacing ...
Distributed operating system
A distributed operating system is a software over a collection of independent, networked, communicating, and physically separate computational nodes. Each individual node holds a specific software subset of the global aggregate operating system. Each subset is a composite of two distinct service provisioners. The first is a ubiquitous minimal kernel, or microkernel, that directly controls that node’s hardware. Second is a higher-level collection of system management components that coordinate the node's individual and collaborative activities. These components abstract microkernel functions and support user applications.The microkernel and the management components collection work together. They support the system’s goal of integrating multiple resources and processing functionality into an efficient and stable system. This seamless integration of individual nodes into a global system is referred to as transparency, or single system image; describing the illusion provided to users of the global system’s appearance as a single computational entity.