A New Hybrid Intelligent Based Approach to Islanding Detection in
... performed using PSCAD/EMTDC software and the parameter indices are determined. When the simulation is accomplished for all prescribed events the obtained parameter indices together with corresponding islanding detection index are stored in a matrix known as events matrix. This recent index is repre ...
... performed using PSCAD/EMTDC software and the parameter indices are determined. When the simulation is accomplished for all prescribed events the obtained parameter indices together with corresponding islanding detection index are stored in a matrix known as events matrix. This recent index is repre ...
Efficient Histogram Generation Using Scattering on GPUs
... targets can limit the accuracy of the resulting histogram: If we use an 8-bit render target to store the histogram bins, a bin is saturated after accumulating only 256 points into it. Saturated bins distort the true luminance distribution of the input image, and a histogram with saturated bins viola ...
... targets can limit the accuracy of the resulting histogram: If we use an 8-bit render target to store the histogram bins, a bin is saturated after accumulating only 256 points into it. Saturated bins distort the true luminance distribution of the input image, and a histogram with saturated bins viola ...
News Video Classification Using SVM
... probabilities, we scale the output value of decision functions into a range between zero and one as a posterior probability P(wweather|xj). The P(wnon-weather|xj) is 1- P(wweather|xj). The prior probability P(wj) was estimated from the training data, which was fixed in our case, i.e. P(wweather)=0.0 ...
... probabilities, we scale the output value of decision functions into a range between zero and one as a posterior probability P(wweather|xj). The P(wnon-weather|xj) is 1- P(wweather|xj). The prior probability P(wj) was estimated from the training data, which was fixed in our case, i.e. P(wweather)=0.0 ...
Comparison of Handwriting characters Accuracy using
... including Thai handwritten characters (65 classes), Bangla numeric (10 classes) and MNIST (10 classes). The data sets are then classified by the k-Nearest Neighbors algorithm using the Euclidean distance as function for computing distances between data points. In that study, the classification rates ...
... including Thai handwritten characters (65 classes), Bangla numeric (10 classes) and MNIST (10 classes). The data sets are then classified by the k-Nearest Neighbors algorithm using the Euclidean distance as function for computing distances between data points. In that study, the classification rates ...
Unsupervised Object Counting without Object Recognition
... extensively [1]–[11]. If the input observations are images, a straightforward approach would be to perform explicit object detection [5], [7], [12]–[14]. Also, regression-based approaches have been proposed, which translate the image features into the number of objects with a regression model [8], [ ...
... extensively [1]–[11]. If the input observations are images, a straightforward approach would be to perform explicit object detection [5], [7], [12]–[14]. Also, regression-based approaches have been proposed, which translate the image features into the number of objects with a regression model [8], [ ...
Basic Principles of Image Processing
... qualities of the original image. In this way, it is possible to exaggerate certain details in the digitized image not appreciated in the original form. Until recently, the computer and statistical analysis involved in image processing was deemed too complicated and time-consuming for routine use. Th ...
... qualities of the original image. In this way, it is possible to exaggerate certain details in the digitized image not appreciated in the original form. Until recently, the computer and statistical analysis involved in image processing was deemed too complicated and time-consuming for routine use. Th ...
sv-lncs
... In general, wrapper and filter method have been proposed for feature selection. Wrapper method adopts classification algorithms and performs cross validation to identify important features. Filter method utilizes correlation based approach. Wrapper method demands heavy computational resource for tra ...
... In general, wrapper and filter method have been proposed for feature selection. Wrapper method adopts classification algorithms and performs cross validation to identify important features. Filter method utilizes correlation based approach. Wrapper method demands heavy computational resource for tra ...
Generalizing Objects by Analyzing Language
... and argument 2 (knife&similars). In addition we have included a set of images of cups, which is not an argument of the verb ”slice”. The results demonstrate that reasonably well distinguishable image classes I˜ can be obtained and that other objects (cups) can also be discriminated. This concludes t ...
... and argument 2 (knife&similars). In addition we have included a set of images of cups, which is not an argument of the verb ”slice”. The results demonstrate that reasonably well distinguishable image classes I˜ can be obtained and that other objects (cups) can also be discriminated. This concludes t ...
Learning to Parse Images
... Neal [4] introduced generative models composed of multiple layers of stochastic logistic units connected in a directed acyclic graph. In general, as each unit has multiple parents, it is intractable to compute the posterior distribution over hidden variables when certain variables are observed. Howe ...
... Neal [4] introduced generative models composed of multiple layers of stochastic logistic units connected in a directed acyclic graph. In general, as each unit has multiple parents, it is intractable to compute the posterior distribution over hidden variables when certain variables are observed. Howe ...
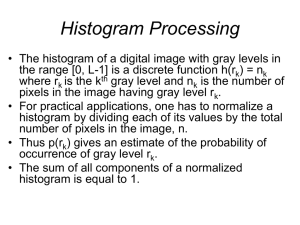
Image Enhancement in the Spatial Domain
... • At each location, the histogram of the points in the neighborhood is computed and either a histogram equalization or histogram specification transformation function is obtained. • This function is used to map the gray level of the pixel centered in the neighborhood. • The centre of the neighborhoo ...
... • At each location, the histogram of the points in the neighborhood is computed and either a histogram equalization or histogram specification transformation function is obtained. • This function is used to map the gray level of the pixel centered in the neighborhood. • The centre of the neighborhoo ...
Wildfire Smoke Detection Using Computational Intelligence
... extracted from the frame sequence. The computed features are then used as inputs of classifiers based on computational intelligence techniques, which output a Boolean value that represents the classes “smoke” and “non smoke.” ii) RGB extraction Algorithm: It is used for Feature Extraction. It also u ...
... extracted from the frame sequence. The computed features are then used as inputs of classifiers based on computational intelligence techniques, which output a Boolean value that represents the classes “smoke” and “non smoke.” ii) RGB extraction Algorithm: It is used for Feature Extraction. It also u ...
- Sacramento - California State University
... is an effective and efficient method for studying demographics of large wildlife populations [2]. Natural markings have been used to identify individuals recaptured across surveys and assist in the study of population dynamics for many species including harbor seals [3], polar bears [4], sharks [5], ...
... is an effective and efficient method for studying demographics of large wildlife populations [2]. Natural markings have been used to identify individuals recaptured across surveys and assist in the study of population dynamics for many species including harbor seals [3], polar bears [4], sharks [5], ...
IJPRAI Call for Papers - Face Recognition Homepage
... another research area where new solutions are urgently needed to enhance robustness of today's recognition systems and enable real-time, face-oriented processing and analysis of visual data. Thus, vigorous research is needed to solve such outstanding challenging problems and propose advanced solutio ...
... another research area where new solutions are urgently needed to enhance robustness of today's recognition systems and enable real-time, face-oriented processing and analysis of visual data. Thus, vigorous research is needed to solve such outstanding challenging problems and propose advanced solutio ...
various object recognition techniques for computer vision
... Appearance-based object recognition systems are currently the most successful approach for dealing with 3D recognition of arbitrary objects in the presence of clutter and occlusion. For appearance-based models, only the appearance is used, which is usually captured by different two-dimensional views ...
... Appearance-based object recognition systems are currently the most successful approach for dealing with 3D recognition of arbitrary objects in the presence of clutter and occlusion. For appearance-based models, only the appearance is used, which is usually captured by different two-dimensional views ...
An investigation on local wrinkle-based extractor of age estimation
... and this information was combined with some measures of facial geometry for an age range classification (Kwon and da Vitoria Lobo, 1999). The wrinkles were computed in several regions, such as on the forehead, next to the eyes, and near the cheek bones. The presence of wrinkles in a region was based ...
... and this information was combined with some measures of facial geometry for an age range classification (Kwon and da Vitoria Lobo, 1999). The wrinkles were computed in several regions, such as on the forehead, next to the eyes, and near the cheek bones. The presence of wrinkles in a region was based ...
Fig 2(d) - Academic Science,International Journal of Computer
... performed and results of proposed technique are promising. The problem is here as this algorithm enhances two much in low grained region so if breakage or crack in the bone then it is not possible to visualize the crack in the bone. N.J. Dhinagar et. al. [5] suggested that ultrasound images, though ...
... performed and results of proposed technique are promising. The problem is here as this algorithm enhances two much in low grained region so if breakage or crack in the bone then it is not possible to visualize the crack in the bone. N.J. Dhinagar et. al. [5] suggested that ultrasound images, though ...
Lab worksheet 5 – Retrieval and Classification
... process? Alternatively, what features are important for recognition? We often talk about colour, shape, and texture information being important visual cues for recognition. Here we focus on using colour information to represent image content. Feature vector representation: Objects may be compared fo ...
... process? Alternatively, what features are important for recognition? We often talk about colour, shape, and texture information being important visual cues for recognition. Here we focus on using colour information to represent image content. Feature vector representation: Objects may be compared fo ...
Leaf Vein Extraction Using Independent Component Analysis
... We use the FastICA training algorithm to learn the unmixing filters, W, in this paper. FastICA is an efficient and popular algorithm for independent component analysis invented by Aapo Hyvärinen [14]. The algorithm is based on a fixed-point iteration scheme maximizing non-gaussianity as a measure of ...
... We use the FastICA training algorithm to learn the unmixing filters, W, in this paper. FastICA is an efficient and popular algorithm for independent component analysis invented by Aapo Hyvärinen [14]. The algorithm is based on a fixed-point iteration scheme maximizing non-gaussianity as a measure of ...
IS 687 Transaction Mining / Fraud Detection Course Syllabus Fall
... IS 687 Transaction Mining / Fraud Detection Course Syllabus Fall 2014 Description of Course: In recent years, financial fraud, including credit card fraud, corporate fraud and money laundering, has attracted a great deal of concern and attention. Data mining plays an important role in fraud detectio ...
... IS 687 Transaction Mining / Fraud Detection Course Syllabus Fall 2014 Description of Course: In recent years, financial fraud, including credit card fraud, corporate fraud and money laundering, has attracted a great deal of concern and attention. Data mining plays an important role in fraud detectio ...
Video Understanding for Activity Monitoring
... Objective: Real-time Interpretation of videos from pixels to events Segmentation ...
... Objective: Real-time Interpretation of videos from pixels to events Segmentation ...
pattern recognition - CIS @ Temple University
... recognition systems when processing and locating fingerprints. All humans have a unique fingerprint and this trait is used to solve many crimes. With pattern recognition technology, authorities are able to process and categorize fingerprint patterns. There is useful information available relating to ...
... recognition systems when processing and locating fingerprints. All humans have a unique fingerprint and this trait is used to solve many crimes. With pattern recognition technology, authorities are able to process and categorize fingerprint patterns. There is useful information available relating to ...
ppt1
... COMPASS uses warpable metrics to emphasize (or minimize) the impact of the most (or less) relevant features of the image query set. [See references for details.] ...
... COMPASS uses warpable metrics to emphasize (or minimize) the impact of the most (or less) relevant features of the image query set. [See references for details.] ...
Eye detection using color cues and projection functions S. A.
... are two spatially disconnected low intensity clusters corresponding to the eye and the eyebrow. In most realistic situations, it is difficult to detect skin area below the eyebrow and hence the eyebrow cluster is eliminated. In each of the analysis windows, the angle of the linejoining the centroids ...
... are two spatially disconnected low intensity clusters corresponding to the eye and the eyebrow. In most realistic situations, it is difficult to detect skin area below the eyebrow and hence the eyebrow cluster is eliminated. In each of the analysis windows, the angle of the linejoining the centroids ...