Risk management, Arbitrage and Scenario generation for interest rates
... Prices of T -bonds are denoted by P(t, T ). Interest rates are governed by a market of (default free) zero-coupon bonds modelled by stochastic processes (P(t, T ))0≤t≤T for T ≥ 0. We assume the normalization P(T , T ) = 1. I T denotes the maturity of the bond, P(t, T ) its price at a time t before m ...
... Prices of T -bonds are denoted by P(t, T ). Interest rates are governed by a market of (default free) zero-coupon bonds modelled by stochastic processes (P(t, T ))0≤t≤T for T ≥ 0. We assume the normalization P(T , T ) = 1. I T denotes the maturity of the bond, P(t, T ) its price at a time t before m ...
- Whatcom Community College
... • Cyber Security Procurement Language for Control Systems — developed in March 2006 by the Procurement Project Workgroup • Established common procurement language to be used by all control system stakeholders ...
... • Cyber Security Procurement Language for Control Systems — developed in March 2006 by the Procurement Project Workgroup • Established common procurement language to be used by all control system stakeholders ...
View/Open - AgEcon Search
... mode, the tenth fractile, and the ninetieth fractile of each distribution. These values are then use to compute the first and second moments of each producer’s yield and price. – In Sherrick, et al. (2004), expected yields are elicited based on the conviction weight method in which farmers assign pr ...
... mode, the tenth fractile, and the ninetieth fractile of each distribution. These values are then use to compute the first and second moments of each producer’s yield and price. – In Sherrick, et al. (2004), expected yields are elicited based on the conviction weight method in which farmers assign pr ...
Answers
... framework to be applied in the preparation of the financial statements is acceptable. In considering this the auditor should assess the nature of the entity, the nature and purpose of the financial statements and whether law or regulations prescribes the applicable reporting framework. In addition t ...
... framework to be applied in the preparation of the financial statements is acceptable. In considering this the auditor should assess the nature of the entity, the nature and purpose of the financial statements and whether law or regulations prescribes the applicable reporting framework. In addition t ...
Summary of the papers on ”Increasing risk” by Rothschild and Stiglitz
... A comparison of the variability (or “riskiness”) of different random variables has been of a particular interest of many economists. Over past decades, several approaches to address this problem have been developed. One of the most essential works in this field is series of articles written by Rothsch ...
... A comparison of the variability (or “riskiness”) of different random variables has been of a particular interest of many economists. Over past decades, several approaches to address this problem have been developed. One of the most essential works in this field is series of articles written by Rothsch ...
Assessment of febrile child
... distress include recession, grunting, accessory muscle use, flared nostrils ...
... distress include recession, grunting, accessory muscle use, flared nostrils ...
GMPs for the 21st Century A Risk
... ◦ Faster approval of new products ◦ Continue to receive quality products FDA ◦ More product and process knowledge shared by industry ◦ More efficient resource allocation for review and inspection ◦ Increased trust and understanding of industry decision making OAI ...
... ◦ Faster approval of new products ◦ Continue to receive quality products FDA ◦ More product and process knowledge shared by industry ◦ More efficient resource allocation for review and inspection ◦ Increased trust and understanding of industry decision making OAI ...
international telecommunication union
... Results-based Management is a management approach that directs organizational processes, resources, products and services towards the achievement of measurable results. It provides the management frameworks and tools for strategic planning, risk management, performance monitoring and evaluation and ...
... Results-based Management is a management approach that directs organizational processes, resources, products and services towards the achievement of measurable results. It provides the management frameworks and tools for strategic planning, risk management, performance monitoring and evaluation and ...
Codominant Stems - Hayward Tree Service
... Though such stems may look fine to the casual observer, they may actually be dangerous. Early recognition of such stems allows remedial action when it does the most good. Many of our most common street, highway, and park trees commonly form codominant stems. o Maples and oaks o Conifers that have lo ...
... Though such stems may look fine to the casual observer, they may actually be dangerous. Early recognition of such stems allows remedial action when it does the most good. Many of our most common street, highway, and park trees commonly form codominant stems. o Maples and oaks o Conifers that have lo ...
Leading Practice Examples of Audit Committee Reporting
... There is no formal communication between AP and the Merchandising (Buyer) department to develop uniform, beneficial practices for supplier management, and communication with suppliers should be managed to establish mutually agreeable practices. ...
... There is no formal communication between AP and the Merchandising (Buyer) department to develop uniform, beneficial practices for supplier management, and communication with suppliers should be managed to establish mutually agreeable practices. ...
Vulnerability Management
... Automated tool performs the heavy lifting The most famous is the vulnerability scanner 7 out of 20 SANS Critical Controls can be automated in some way with a vulnerability tool Another 8 can be automated using additional ...
... Automated tool performs the heavy lifting The most famous is the vulnerability scanner 7 out of 20 SANS Critical Controls can be automated in some way with a vulnerability tool Another 8 can be automated using additional ...
Hang Chi Holdings Limited 恒智控股有限公司
... 5.7 to review the Company’s financial controls, and unless expressly addressed by a separate Board risk committee, or by the Board itself, risk management and internal control systems; 5.8 to discuss the risk management and internal control system with management to ensure that management has perf ...
... 5.7 to review the Company’s financial controls, and unless expressly addressed by a separate Board risk committee, or by the Board itself, risk management and internal control systems; 5.8 to discuss the risk management and internal control system with management to ensure that management has perf ...
Population Perspective
... • Study design – Is the evidence based on a strong study design • Judging the evidence – How many lines of evidence lead to the conclusion ...
... • Study design – Is the evidence based on a strong study design • Judging the evidence – How many lines of evidence lead to the conclusion ...
Urogynaecology
... – Mainly iatrogenic e.g.post hysterectomy – Consider risk management issues – Manage within a MDT – Catheterise – Find hole and close – Vaginal, abdominal or laparoscopic approach – Barrier between epithelial surfaces – Should be performed in large units with experienced surgeons ...
... – Mainly iatrogenic e.g.post hysterectomy – Consider risk management issues – Manage within a MDT – Catheterise – Find hole and close – Vaginal, abdominal or laparoscopic approach – Barrier between epithelial surfaces – Should be performed in large units with experienced surgeons ...
Can Financial Statement Auditors Detect More Fraud? How Can
... • Many firms believe that going beyond what GAAS requires exposes them to liability • Fraud detection procedures can be time‐consuming and expensive; audits are viewed as a commodity—i.e. why pay more for an audit than you have to; so price competition makes extra procedures commercially impract ...
... • Many firms believe that going beyond what GAAS requires exposes them to liability • Fraud detection procedures can be time‐consuming and expensive; audits are viewed as a commodity—i.e. why pay more for an audit than you have to; so price competition makes extra procedures commercially impract ...
Presentation, NDA, Site Restoration programme
... Undertake restoration as soon as reasonably practicable – Preference for continuous decommissioning Commence POCO on cessation of operations Act proportionately to ensure net level of risk does not increase in the long-term Balance range of relevant factors ...
... Undertake restoration as soon as reasonably practicable – Preference for continuous decommissioning Commence POCO on cessation of operations Act proportionately to ensure net level of risk does not increase in the long-term Balance range of relevant factors ...
Medical Statistics Presentation
... • The output of most statistical tests is a p-value. • A p-value is defined as ‘the probability that we observed a the result at least as extreme as the one we did given that the null hypothesis is true’. • The smaller the p-value, the more unlikely it is that we would have collected the data we did ...
... • The output of most statistical tests is a p-value. • A p-value is defined as ‘the probability that we observed a the result at least as extreme as the one we did given that the null hypothesis is true’. • The smaller the p-value, the more unlikely it is that we would have collected the data we did ...
Asset Management Accountability Framework
... Management) of the 2016 Standing Directions of the Minister for Finance on 1 July 2016 (published February 2016) • Applies to non-current assets controlled by government departments, portfolio agencies and other public bodies • Encourages good practice asset management • To ensure assets are managed ...
... Management) of the 2016 Standing Directions of the Minister for Finance on 1 July 2016 (published February 2016) • Applies to non-current assets controlled by government departments, portfolio agencies and other public bodies • Encourages good practice asset management • To ensure assets are managed ...
Estimating Impact and Frequency of Risks to
... and show how to use existing experience data to estimate the frequency of potential fault introduction and the magnitude of impact that these may have. In particular, we use the Common Vulnerability Scoring System (CVSS) and the paper describes a model developed to estimate risk level from frequency ...
... and show how to use existing experience data to estimate the frequency of potential fault introduction and the magnitude of impact that these may have. In particular, we use the Common Vulnerability Scoring System (CVSS) and the paper describes a model developed to estimate risk level from frequency ...
Auditor`s Responsibility
... the parties that affect it by linking sound controls to the actions of the BOD, management and other personnel • Identifies five interrelated components of internal control Control environment Control activities Monitoring of controls ...
... the parties that affect it by linking sound controls to the actions of the BOD, management and other personnel • Identifies five interrelated components of internal control Control environment Control activities Monitoring of controls ...
Cyber-Insurance--I Do Not Think That Word
... But, business also play a key role in maturing the cyber insurance industry. Realize that cybersecurity has never been more complicated or important ...
... But, business also play a key role in maturing the cyber insurance industry. Realize that cybersecurity has never been more complicated or important ...
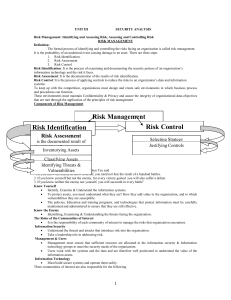
IT2042-UNIT3-Notes
... Serial Number: For hardware devices, the serial number can uniquely identify a specific device. Manufacturer Name: Record the manufacturer of the device or software component. This can be useful when responding to incidents that involve these devices or when certain manufacturers announce specific v ...
... Serial Number: For hardware devices, the serial number can uniquely identify a specific device. Manufacturer Name: Record the manufacturer of the device or software component. This can be useful when responding to incidents that involve these devices or when certain manufacturers announce specific v ...