Advanced Programming Guide
... Preface...........................................................................................................................................xi Acknowledgements......................................................................................................................xv Section 1 - In ...
... Preface...........................................................................................................................................xi Acknowledgements......................................................................................................................xv Section 1 - In ...
Chapter 1 and 2
... • Increment or Decrement: (++) or (--) are increment and decrement operators used to increase or decrease a value by 1 • Prefix and postfix: we can write ++I, this called prefix increment or I++, this is call postfix increment. The result is the same for simple logic but when involving complex expre ...
... • Increment or Decrement: (++) or (--) are increment and decrement operators used to increase or decrease a value by 1 • Prefix and postfix: we can write ++I, this called prefix increment or I++, this is call postfix increment. The result is the same for simple logic but when involving complex expre ...
Executable Formal Specifications with Clojure
... functions are easier to write, maintain and test compared to impure functions as the programmers who work with pure functions do not have to consider any code outside the function itself [Halloway and Bedra, 2012]. Applications written in functional programming languages consist mostly of pure func ...
... functions are easier to write, maintain and test compared to impure functions as the programmers who work with pure functions do not have to consider any code outside the function itself [Halloway and Bedra, 2012]. Applications written in functional programming languages consist mostly of pure func ...
Programming with Coq
... match x with 0 => 1 | S p => x * fact p end This simple schema only for natural numbers ! More complex schemas for other datatypes. ...
... match x with 0 => 1 | S p => x * fact p end This simple schema only for natural numbers ! More complex schemas for other datatypes. ...
Implementing a non-strict purely functional language in JavaScript
... The examples show that the translation is straightforward and preserves the structure of the original definitions. ...
... The examples show that the translation is straightforward and preserves the structure of the original definitions. ...
An introduction to C++ template programming
... perform arbitrary computations at compile-time. For instance, you can write a template that computes the factorial function during C++ compilation, and it might even output the result in compiler error messages for extra strangeness. However, in the latest C++11 standard, constexpr functions already ...
... perform arbitrary computations at compile-time. For instance, you can write a template that computes the factorial function during C++ compilation, and it might even output the result in compiler error messages for extra strangeness. However, in the latest C++11 standard, constexpr functions already ...
Notes
... You can have an insert before the head node, an insert after the tail node, an insert before the current node and an insert after the current node. You can think up many more, but should do at least insert before and after the current node. You should do a remove current node. ...
... You can have an insert before the head node, an insert after the tail node, an insert before the current node and an insert after the current node. You can think up many more, but should do at least insert before and after the current node. You should do a remove current node. ...
Programming with Multiple Paradigms in Lua - DI PUC-Rio
... where variables live in activation records allocated in an array-based stack. – It is amenable to a one-pass compiler that generates code on the fly, without intermediate representations. ...
... where variables live in activation records allocated in an array-based stack. – It is amenable to a one-pass compiler that generates code on the fly, without intermediate representations. ...
The given function f is continuous at
... On subtracting equation (1) from equation (2), we obtain 8a = 16 ⇒a=2 By putting a = 2 in equation (1), we obtain 2×2+b=5 ⇒4+b=5 ⇒b=1 Therefore, the values of a and b for which f is a continuous function are 2 and 1 respectively. Q.31 Show that the function defined by f (x) = cos (x2) is a continuou ...
... On subtracting equation (1) from equation (2), we obtain 8a = 16 ⇒a=2 By putting a = 2 in equation (1), we obtain 2×2+b=5 ⇒4+b=5 ⇒b=1 Therefore, the values of a and b for which f is a continuous function are 2 and 1 respectively. Q.31 Show that the function defined by f (x) = cos (x2) is a continuou ...
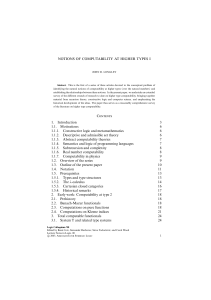
Notions of Computability at Higher Type
... §1. Introduction. This article is essentially a survey of fifty years of research on higher type computability. It was a great privilege to present much of this material in a series of three lectures at the Paris Logic Colloquium. In elementary recursion theory, one begins with the question: what do ...
... §1. Introduction. This article is essentially a survey of fifty years of research on higher type computability. It was a great privilege to present much of this material in a series of three lectures at the Paris Logic Colloquium. In elementary recursion theory, one begins with the question: what do ...
Solution
... In the following, use either a direct proof (by giving values for c and n0 in the definition of big-Oh notation) or cite one of the rules given in the book or in the lecture slides. (a) Show that if f(n) is O(g(n)) and d(n) is O(h(n)), then f(n)+d(n) is O(g(n)+ h(n)). Solution Recall the de_nition o ...
... In the following, use either a direct proof (by giving values for c and n0 in the definition of big-Oh notation) or cite one of the rules given in the book or in the lecture slides. (a) Show that if f(n) is O(g(n)) and d(n) is O(h(n)), then f(n)+d(n) is O(g(n)+ h(n)). Solution Recall the de_nition o ...
lecture notes in logic - UCLA Department of Mathematics
... 4A. Tarski and Gödel (First Incompleteness Theorem). . . . . . . . . . . 139 4B. Numeralwise representability in Q . . . . . . . . . . . . . . . . . . . . . . . . . . 145 4C. Rosser, more Gödel and Löb . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 150 4D. Computability and undec ...
... 4A. Tarski and Gödel (First Incompleteness Theorem). . . . . . . . . . . 139 4B. Numeralwise representability in Q . . . . . . . . . . . . . . . . . . . . . . . . . . 145 4C. Rosser, more Gödel and Löb . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 150 4D. Computability and undec ...
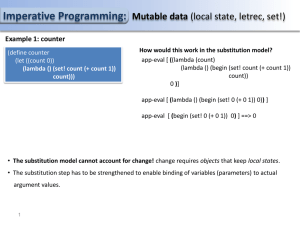
PS14
... (let ((piece-value (cond ((eq? piece 'queen) 9) ((eq? piece 'rook) 5) ((eq? piece 'bishop) 3) Local state (initialized) ((eq? piece 'knight) 3) ((eq? piece 'pawn) 1) ...
... (let ((piece-value (cond ((eq? piece 'queen) 9) ((eq? piece 'rook) 5) ((eq? piece 'bishop) 3) Local state (initialized) ((eq? piece 'knight) 3) ((eq? piece 'pawn) 1) ...
Introduction to the lambda calculus
... A term is in normal form if it cannot be reduced Examples: λx.x, λx.λy.z By the Church-Rosser theorem, every term reduces to at most one normal form Only for pure lambda calculus with non-deterministic evaluation Notice that for function application, the argument need not be in normal form ...
... A term is in normal form if it cannot be reduced Examples: λx.x, λx.λy.z By the Church-Rosser theorem, every term reduces to at most one normal form Only for pure lambda calculus with non-deterministic evaluation Notice that for function application, the argument need not be in normal form ...
PolyP | a polytypic programming language extension
... in the near future. In the future PolyP will be able to handle mutual recursive datatypes with an arbitrary number of type arguments and in which function spaces may occur. ...
... in the near future. In the future PolyP will be able to handle mutual recursive datatypes with an arbitrary number of type arguments and in which function spaces may occur. ...
Sept 2 - Joshua Stough
... • can only add to the top - push • can only remove from the top - pop ...
... • can only add to the top - push • can only remove from the top - pop ...
Lecture slides for Chapter 9
... Environment of evaluation • Arguments going to (apply f x a) (p.380) – f the function - lambda expression – x the parameters - bound formals – a the environment - existing environment with the addition of the bound formals ...
... Environment of evaluation • Arguments going to (apply f x a) (p.380) – f the function - lambda expression – x the parameters - bound formals – a the environment - existing environment with the addition of the bound formals ...
Thermodynamic Analysis of Interacting Nucleic Acid Strands
... 11] algorithms. Although pseudoknots exist in nature [43] and have been incorporated in synthetic DNA systems [46, 42], many natural and synthetic structures of interest do not include pseudoknots [23, 32, 38], and we will not consider them here. By employing a dynamic program, the unpseudoknotted M ...
... 11] algorithms. Although pseudoknots exist in nature [43] and have been incorporated in synthetic DNA systems [46, 42], many natural and synthetic structures of interest do not include pseudoknots [23, 32, 38], and we will not consider them here. By employing a dynamic program, the unpseudoknotted M ...
Proof Pearl: Defining Functions over Finite Sets
... induction. For example, the union of finitely many finite sets is itself finite. Traditionally, a set is finite if it can be put into one-to-one correspondence with the set of natural numbers less than some n. Another traditional definition says A is finite if every injection from A to A is also a surject ...
... induction. For example, the union of finitely many finite sets is itself finite. Traditionally, a set is finite if it can be put into one-to-one correspondence with the set of natural numbers less than some n. Another traditional definition says A is finite if every injection from A to A is also a surject ...
Pdf - Text of NPTEL IIT Video Lectures
... Second part is the limit of this function f (x), when x approaches to c must exist must exists and third condition is both should be identical, third is the limit of f (x), when x tends to c must coincide with the value f (x). If these three conditions are satisfied then, we say, the function f (x) ...
... Second part is the limit of this function f (x), when x approaches to c must exist must exists and third condition is both should be identical, third is the limit of f (x), when x tends to c must coincide with the value f (x). If these three conditions are satisfied then, we say, the function f (x) ...
LEC01 - aiub study guide
... To think algorithmically and get the spirit of how algorithms are designed. To get to know a toolbox of classical algorithms. To learn a number of algorithm design techniques (such as divide-and-conquer). To reason (in a precise and formal way) about the efficiency and the correctness of algorithms. ...
... To think algorithmically and get the spirit of how algorithms are designed. To get to know a toolbox of classical algorithms. To learn a number of algorithm design techniques (such as divide-and-conquer). To reason (in a precise and formal way) about the efficiency and the correctness of algorithms. ...
W. Dean. Algorithms and the mathematical foundations of computer
... can be justified by a supplemental mathematical proof that the algorithm is correct (i.e. that it computes the function that it is claimed to). I will refer to the view expressed by (A) as algorithmic realism.3 Although it is often not identified as a thesis requiring an explicit statement and defen ...
... can be justified by a supplemental mathematical proof that the algorithm is correct (i.e. that it computes the function that it is claimed to). I will refer to the view expressed by (A) as algorithmic realism.3 Although it is often not identified as a thesis requiring an explicit statement and defen ...
PDF - 4up
... this chapter are lists, stacks, queues, and binary trees. A list is a collection of data stored sequentially. It supports insertion and deletion anywhere in the list. A stack can be perceived as a special type of the list where insertions and deletions take place only at the one end, referred to as ...
... this chapter are lists, stacks, queues, and binary trees. A list is a collection of data stored sequentially. It supports insertion and deletion anywhere in the list. A stack can be perceived as a special type of the list where insertions and deletions take place only at the one end, referred to as ...
Proof Pearl: Defining Functions Over Finite Sets
... The only remaining case is if b 6= c. Here, we define the set D = B − {c}. Trivially B = {c} ∪ D, but we can also show C = {b} ∪ D by subtracting c from both sides of the set equation {b} ∪ B = {c} ∪ C. Because the set D is of smaller cardinality, the induction hypothesis tells us that (D, w ) ∈ fol ...
... The only remaining case is if b 6= c. Here, we define the set D = B − {c}. Trivially B = {c} ∪ D, but we can also show C = {b} ∪ D by subtracting c from both sides of the set equation {b} ∪ B = {c} ∪ C. Because the set D is of smaller cardinality, the induction hypothesis tells us that (D, w ) ∈ fol ...
Data Structures through C++ Lab Manual
... in response to the call. Dynamic Binding (also known as late binding) means that the code associated with a given function which is to be used is not known until the time of the call at run-time. A function call associated with a polymorphic reference depends on the dynamic type of that reference. 7 ...
... in response to the call. Dynamic Binding (also known as late binding) means that the code associated with a given function which is to be used is not known until the time of the call at run-time. A function call associated with a polymorphic reference depends on the dynamic type of that reference. 7 ...
Recursion (computer science)
Recursion in computer science is a method where the solution to a problem depends on solutions to smaller instances of the same problem (as opposed to iteration). The approach can be applied to many types of problems, and recursion is one of the central ideas of computer science.""The power of recursion evidently lies in the possibility of defining an infinite set of objects by a finite statement. In the same manner, an infinite number of computations can be described by a finite recursive program, even if this program contains no explicit repetitions.""Most computer programming languages support recursion by allowing a function to call itself within the program text. Some functional programming languages do not define any looping constructs but rely solely on recursion to repeatedly call code. Computability theory proves that these recursive-only languages are Turing complete; they are as computationally powerful as Turing complete imperative languages, meaning they can solve the same kinds of problems as imperative languages even without iterative control structures such as “while” and “for”.