Practical Type Inference Based on Success Typings
... inference and safely unboxes values, all values are tagged with their type during runtime. This in turn makes it possible to check the type of each value before its use as an argument to a function or a built-in operation and throw an exception if a type clash occurs. In addition to such runtime typ ...
... inference and safely unboxes values, all values are tagged with their type during runtime. This in turn makes it possible to check the type of each value before its use as an argument to a function or a built-in operation and throw an exception if a type clash occurs. In addition to such runtime typ ...
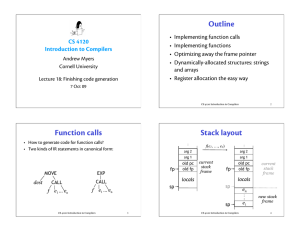
Finishing code generation
... • Simple way to get working code • Code is longer than necessary, slower • Also can allocate temporaries to registers until registers run out (3 temporaries on Pentium, 20+ on MIPS, Alpha) ...
... • Simple way to get working code • Code is longer than necessary, slower • Also can allocate temporaries to registers until registers run out (3 temporaries on Pentium, 20+ on MIPS, Alpha) ...
ppt
... start with an empty stack that can store numbers traverse the expression from left to right if next char is an operand (number or variable), push on the stack if next char is an operator (+, -, *, /, …), 1. pop 2 operands off the top of the stack 2. apply the operator to the operands 3. push the res ...
... start with an empty stack that can store numbers traverse the expression from left to right if next char is an operand (number or variable), push on the stack if next char is an operator (+, -, *, /, …), 1. pop 2 operands off the top of the stack 2. apply the operator to the operands 3. push the res ...
More on mild continuity
... Quasi-continuity is even an older concept than the one of near continuity. In 1899, Baire stated that first Volterra observed the fact that every separately continuous function f : R × R → R is quasi-continuous. It was Kempisty [18], who later on called this property of separately continuous functi ...
... Quasi-continuity is even an older concept than the one of near continuity. In 1899, Baire stated that first Volterra observed the fact that every separately continuous function f : R × R → R is quasi-continuous. It was Kempisty [18], who later on called this property of separately continuous functi ...
The Open World of Super-Recursive Algorithms and
... 2 recursion theory [20,21], and the polynomial approximation approach [22]. In 1963, Scarpellini introduced the class M1 of functions that are built with the help of five operations. The first three are elementary: substitutions, sums and products of functions. The two remaining operations are perfo ...
... 2 recursion theory [20,21], and the polynomial approximation approach [22]. In 1963, Scarpellini introduced the class M1 of functions that are built with the help of five operations. The first three are elementary: substitutions, sums and products of functions. The two remaining operations are perfo ...
Lecture Slides (PowerPoint)
... Problem-solving agents A definition: Problem-solving agents are goal based agents that decide what to do based on an action sequence leading to a goal state. ...
... Problem-solving agents A definition: Problem-solving agents are goal based agents that decide what to do based on an action sequence leading to a goal state. ...
Key to the first midterm, first version
... 7. Bob is using the struct defined on page 9 in his linked list program. The program contains a function Delete_all (see below). Its purpose is to delete all occurrences of a value from the list. It proceeds by searching the list for the user-specified value. Each time it finds the user-specified v ...
... 7. Bob is using the struct defined on page 9 in his linked list program. The program contains a function Delete_all (see below). Its purpose is to delete all occurrences of a value from the list. It proceeds by searching the list for the user-specified value. Each time it finds the user-specified v ...
Order of Growth - inst.eecs.berkeley.edu
... object, and prints the result. Nearly all interpreters can be organized into this REPL pattern! We're primarily interested in the E part of REPL, which stands for evaluation. This step is handled primarily by two functions in calc: calc_eval and calc_apply. calc_eval takes an expression object and r ...
... object, and prints the result. Nearly all interpreters can be organized into this REPL pattern! We're primarily interested in the E part of REPL, which stands for evaluation. This step is handled primarily by two functions in calc: calc_eval and calc_apply. calc_eval takes an expression object and r ...
Document
... placed between two lines passing through the origin of coordinates with positive direction coefficients, and thus passes through the third and first quarter, hence it is strictly increasing function at the zero point – in the sense of definition 2. ...
... placed between two lines passing through the origin of coordinates with positive direction coefficients, and thus passes through the third and first quarter, hence it is strictly increasing function at the zero point – in the sense of definition 2. ...
Principle of structural induction for fp
... [a1,a2,a3,…] is approximated by the collection undef, a1:undef, a1:a2:undef, a1:a2:a3:undef, … For some properties (admissible or continuous predicates) it is enough to show the property for all approximations to know that it will be valid for all infinite lists as well. In particular, this is true ...
... [a1,a2,a3,…] is approximated by the collection undef, a1:undef, a1:a2:undef, a1:a2:a3:undef, … For some properties (admissible or continuous predicates) it is enough to show the property for all approximations to know that it will be valid for all infinite lists as well. In particular, this is true ...
Blame Trees - Edward Z. Yang
... “source” version, the “target” version, and the “base” version, which is the least common ancestor of the source and target. Any intermediate history is thrown out, and the result of the merge relies on the diffs between the base and source and between the base and target. These diffs are split int ...
... “source” version, the “target” version, and the “base” version, which is the least common ancestor of the source and target. Any intermediate history is thrown out, and the result of the merge relies on the diffs between the base and source and between the base and target. These diffs are split int ...
Notes
... f(x) always gives the same result for the same x Node side effects: easier to reason about programs Better fit for modern hardware ...
... f(x) always gives the same result for the same x Node side effects: easier to reason about programs Better fit for modern hardware ...
Global Consistency for Continuous Constraints
... provide relatively poor results when applied to continuous CSPs: they ensure neither completeness nor convergence in the general case (a good insight into the problems encountered can be found in [1]). However, Faltings [5] has shown that some undesirable features of propagation algorithms with inte ...
... provide relatively poor results when applied to continuous CSPs: they ensure neither completeness nor convergence in the general case (a good insight into the problems encountered can be found in [1]). However, Faltings [5] has shown that some undesirable features of propagation algorithms with inte ...
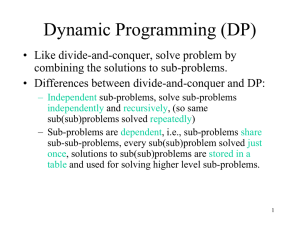
Dynamic Programming
... LCS DP –step 1: Optimal Substructure • Characterize optimal substructure of LCS. • Theorem 15.1: Let X= (= Xm) and
Y= (= Yn) and Z= (=
Zk) be any LCS of X and Y,
– 1. if xm= yn, then zk= xm= yn, and Zk-1 is the LCS of Xm-1
and Yn-1.
– 2. if xm yn, then zk ...
... LCS DP –step 1: Optimal Substructure • Characterize optimal substructure of LCS. • Theorem 15.1: Let X=
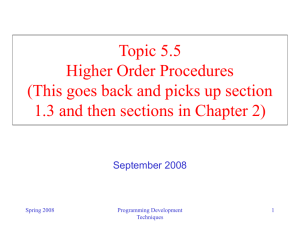
Slides 5.5
... • We have seen the use of procedures as abstractions. • So far we have defined cases where the abstractions that are captured are essentially compound operations on numbers. • What does that buy us? – Assign a name to a common pattern (e.g., cube) and then we can work with the abstraction instead of ...
... • We have seen the use of procedures as abstractions. • So far we have defined cases where the abstractions that are captured are essentially compound operations on numbers. • What does that buy us? – Assign a name to a common pattern (e.g., cube) and then we can work with the abstraction instead of ...
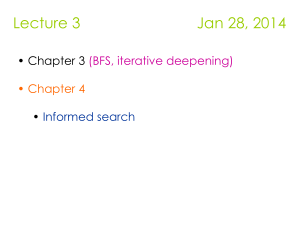
Informed search algorithms
... and greedy Best First Search Hill-climbing: choice of node to expand is limited to the children of the node previously expanded. Greedy Best-first search: all nodes in the open set are considered and the one with the smallest h value is expanded next. ...
... and greedy Best First Search Hill-climbing: choice of node to expand is limited to the children of the node previously expanded. Greedy Best-first search: all nodes in the open set are considered and the one with the smallest h value is expanded next. ...
TCSS 343: Large Integer Multiplication Suppose we want to multiply
... case, a = 3, b = 2, and d = 1 (since n = n1). Since a > bd (or, equivalently, logb a > d), then by the Master Theorem T(n) = (n logb a ) (n log2 3 ) . Is this running time better than the running time of the pencil-and-paper algorithm? Since log2 3 1.585, then the divide and conquer algorithm ...
... case, a = 3, b = 2, and d = 1 (since n = n1). Since a > bd (or, equivalently, logb a > d), then by the Master Theorem T(n) = (n logb a ) (n log2 3 ) . Is this running time better than the running time of the pencil-and-paper algorithm? Since log2 3 1.585, then the divide and conquer algorithm ...
STC 2016 Programming Language Storytime
... Creating Functions // This is the format to define a function. function functionname(parameters) { code ...
... Creating Functions // This is the format to define a function. function functionname(parameters) { code ...
Programming Lecture 1 notes
... Note to student: Python1 is a somewhat modern language by programming standards. It was first released in 1991 (in contrast C is forty years old). It has many features typical of modern languages that help computer users write more complex programs in less time. This handout2 will only teach you a s ...
... Note to student: Python1 is a somewhat modern language by programming standards. It was first released in 1991 (in contrast C is forty years old). It has many features typical of modern languages that help computer users write more complex programs in less time. This handout2 will only teach you a s ...
stochastic local search. - International Center for Computational Logic
... I We want to escape local minima by selecting non-improving steps. I Walk Probability wp ∈ [0, 1]. I stepURW the step function of uninformed random walk. I stepII a variant of the step function used in the iterative improvement algorithm, which differs only in that a minimally worsening neighbour is ...
... I We want to escape local minima by selecting non-improving steps. I Walk Probability wp ∈ [0, 1]. I stepURW the step function of uninformed random walk. I stepII a variant of the step function used in the iterative improvement algorithm, which differs only in that a minimally worsening neighbour is ...
Introduction to Computer Science
... A data structure A data structure is a way of storing data in a computer so that it can be used efficiently. Often a carefully chosen data structure will allow the most efficient algorithm to be used. ...
... A data structure A data structure is a way of storing data in a computer so that it can be used efficiently. Often a carefully chosen data structure will allow the most efficient algorithm to be used. ...
A New Parallel Skeleton for General Accumulative Computations
... to the target program, our approach provides a general recursive computation with accumulation as a library function (skeleton) with an optimized implementation. We are based on the data parallel programming model of BMF, which provides us with a concise way to describe and manipulate parallel progr ...
... to the target program, our approach provides a general recursive computation with accumulation as a library function (skeleton) with an optimized implementation. We are based on the data parallel programming model of BMF, which provides us with a concise way to describe and manipulate parallel progr ...
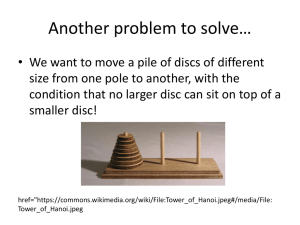
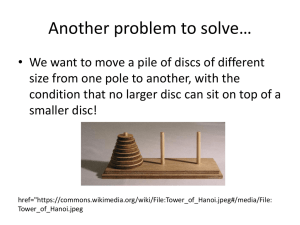
Recursion (computer science)
Recursion in computer science is a method where the solution to a problem depends on solutions to smaller instances of the same problem (as opposed to iteration). The approach can be applied to many types of problems, and recursion is one of the central ideas of computer science.""The power of recursion evidently lies in the possibility of defining an infinite set of objects by a finite statement. In the same manner, an infinite number of computations can be described by a finite recursive program, even if this program contains no explicit repetitions.""Most computer programming languages support recursion by allowing a function to call itself within the program text. Some functional programming languages do not define any looping constructs but rely solely on recursion to repeatedly call code. Computability theory proves that these recursive-only languages are Turing complete; they are as computationally powerful as Turing complete imperative languages, meaning they can solve the same kinds of problems as imperative languages even without iterative control structures such as “while” and “for”.