Introduction - Ilam university
... •packets are lost. No recover from lost. •packets are delivered out of order •duplicate copies of a packet are delivered •packets can be delayed for a long time ...
... •packets are lost. No recover from lost. •packets are delivered out of order •duplicate copies of a packet are delivered •packets can be delayed for a long time ...
AV200 Powerline Ethernet Wall Mount
... • Priority classification according to 802.1P tags, IP coding (IPv4 or IPv6) or TCP source/destination ports • Optimized support for broadcast and multicast traffic • MAC filtering - can discard Ethernet frames if they come from a source MAC address which is not present in a list of allowed MAC addr ...
... • Priority classification according to 802.1P tags, IP coding (IPv4 or IPv6) or TCP source/destination ports • Optimized support for broadcast and multicast traffic • MAC filtering - can discard Ethernet frames if they come from a source MAC address which is not present in a list of allowed MAC addr ...
presentation source
... you have N sites, there are N(N-1)/2 possible connections In this case, you would have 4(3)/2 or 6 possible connections Some vendors count this as 6 PVCs, others as 12 PVCs ...
... you have N sites, there are N(N-1)/2 possible connections In this case, you would have 4(3)/2 or 6 possible connections Some vendors count this as 6 PVCs, others as 12 PVCs ...
Internet Protocol (IP):
... Every host has an address on every network Gateways know how to map from an address in one network address space to an address in another network space ...
... Every host has an address on every network Gateways know how to map from an address in one network address space to an address in another network space ...
Ethernet
... – Hosts and legacy switches do not understand VLAN tags – Tag insertion/removal requires FCS recomputation – Frame length increases beyond legacy MTU ...
... – Hosts and legacy switches do not understand VLAN tags – Tag insertion/removal requires FCS recomputation – Frame length increases beyond legacy MTU ...
Sybex CCNA 640-802 Chapter 1: Internetworking Instructor
... Although rolled cable isn’t used to connect any Ethernet connections together, you can use a rolled Ethernet cable to connect a host to a router console serial communication (com) port. ...
... Although rolled cable isn’t used to connect any Ethernet connections together, you can use a rolled Ethernet cable to connect a host to a router console serial communication (com) port. ...
Full PDF - International Journal of Research in Computer
... participants that are not possible as in video phone. The main components for video conferencing includes Video input, Video output, computer Audio input, Audio and Network transmission, such as wired or wireless LAN and internet. [1][9]. In the OSI reference model, Ethernet technology operates at t ...
... participants that are not possible as in video phone. The main components for video conferencing includes Video input, Video output, computer Audio input, Audio and Network transmission, such as wired or wireless LAN and internet. [1][9]. In the OSI reference model, Ethernet technology operates at t ...
Logical addressing
... addressing employed by various networking schemes (e.g., Ethernet, ATM, FDDI, AppleTalk, PPP, HDLC, etc.) These network have different frame formats and use different addressing scheme. ...
... addressing employed by various networking schemes (e.g., Ethernet, ATM, FDDI, AppleTalk, PPP, HDLC, etc.) These network have different frame formats and use different addressing scheme. ...
Getting Connected (Chapter 2 Part 3) Networking CS 3470, Section 1
... Does not “keep the pipe full” Consider a 1.5 Mbps link with a 45 ms RTT and a 1KB frame size To use the link fully, then sender should transmit up to eight frames before having to wait for an acknowledgement ...
... Does not “keep the pipe full” Consider a 1.5 Mbps link with a 45 ms RTT and a 1KB frame size To use the link fully, then sender should transmit up to eight frames before having to wait for an acknowledgement ...
Week Eight
... In 1998, prices per port for 10Mbps - $212; 100Mbps - $432, 1000Mbps - $2,200. In 2003, prices per port for 10Mbps - $12; 100Mbps - $35; 1000Mbps - $100. ...
... In 1998, prices per port for 10Mbps - $212; 100Mbps - $432, 1000Mbps - $2,200. In 2003, prices per port for 10Mbps - $12; 100Mbps - $35; 1000Mbps - $100. ...
lecture03
... • Internet Protocol (IP): gives a standard way to “package” messages across different hardware types. 1. Message is put in IP packet. ...
... • Internet Protocol (IP): gives a standard way to “package” messages across different hardware types. 1. Message is put in IP packet. ...
physcial_sci_networks_part1
... – Does transmission proceed simultaneously in both directions – How are connections established and torn down – How many pins are on connectors and what each pin does. – What kind of transmission medium, wired, fiber optic ...
... – Does transmission proceed simultaneously in both directions – How are connections established and torn down – How many pins are on connectors and what each pin does. – What kind of transmission medium, wired, fiber optic ...
ConnectX®-4 Lx EN - Starline Computer GmbH
... I/O Virtualization ConnectX-4 Lx EN SR-IOV technology provides dedicated adapter resources and guaranteed isolation and protection for virtual machines (VMs) within the server. I/O virtualization with ConnectX-4 Lx EN gives data center administrators better server utilization while reducing cost, po ...
... I/O Virtualization ConnectX-4 Lx EN SR-IOV technology provides dedicated adapter resources and guaranteed isolation and protection for virtual machines (VMs) within the server. I/O virtualization with ConnectX-4 Lx EN gives data center administrators better server utilization while reducing cost, po ...
AR G3 Series Enterprise Routers
... In addition to one-stop deployment, plug and play capability, and remote commissioning functions, the ARs manage the customer premises equipment (CPE) remotely. The remote maintenance function improves efficiency and greatly reduces maintenance costs. ...
... In addition to one-stop deployment, plug and play capability, and remote commissioning functions, the ARs manage the customer premises equipment (CPE) remotely. The remote maintenance function improves efficiency and greatly reduces maintenance costs. ...
CS514: Intermediate Course in Operating Systems
... Reaction to NAT was to fix the network (IPv6), actively discourage “fixing” the host Laudable goal, but in a way opposite of E2E “spirit” ...
... Reaction to NAT was to fix the network (IPv6), actively discourage “fixing” the host Laudable goal, but in a way opposite of E2E “spirit” ...
Datasheet CEX2 - arcutronix GmbH
... and manage, HTML based WEB -OPI Inband management capability Fan less solution at Desktop Units ...
... and manage, HTML based WEB -OPI Inband management capability Fan less solution at Desktop Units ...
lecture2
... – Make service model undemanding enough so that any physical network could support service model – Best-effort over reliable network is fine, but reliable service over an unreliable network means lots of extra functionality for routers – IP design goal: keep routers simple ...
... – Make service model undemanding enough so that any physical network could support service model – Best-effort over reliable network is fine, but reliable service over an unreliable network means lots of extra functionality for routers – IP design goal: keep routers simple ...
arp
... For now assume set by hand, e.g. on monet: – Own IP address, e.g. 128.243.22.61 – Netmask (range of IP addresses on physical segment), e.g. 255.255.255.0 – Default router, e.g. 128.243.22.1 – DNS server address – (See later notes on auto-configuration) ...
... For now assume set by hand, e.g. on monet: – Own IP address, e.g. 128.243.22.61 – Netmask (range of IP addresses on physical segment), e.g. 255.255.255.0 – Default router, e.g. 128.243.22.1 – DNS server address – (See later notes on auto-configuration) ...
$doc.title
... • MAC address (e.g., 00-‐15-‐C5-‐49-‐04-‐A9) – Numerical address used within a link – Unique, hard-‐coded in the adapter when it is built – Flat name space of 48 bits ...
... • MAC address (e.g., 00-‐15-‐C5-‐49-‐04-‐A9) – Numerical address used within a link – Unique, hard-‐coded in the adapter when it is built – Flat name space of 48 bits ...
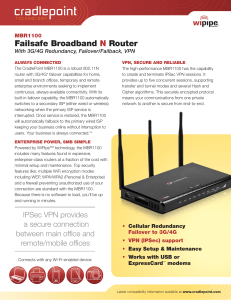
09-0226 MBR1100 Data Sheet.ai
... Cipher algorithms. This securely encrypted protocol means your communications from one private network to another is secure from end-to-end. ...
... Cipher algorithms. This securely encrypted protocol means your communications from one private network to another is secure from end-to-end. ...
Communications Model
... • The TCP/IP suite has four layers: Application, Transport, Network, and Data Link Layer • End systems (hosts) implement all four layers. Gateways (Routers) only have the bottom two layers. ...
... • The TCP/IP suite has four layers: Application, Transport, Network, and Data Link Layer • End systems (hosts) implement all four layers. Gateways (Routers) only have the bottom two layers. ...
Part I: Introduction
... cheap $20 for 100Mbs! first wildey used LAN technology Simpler, cheaper than token LANs and ATM Kept up with speed race: 10, 100, 1000 Mbps ...
... cheap $20 for 100Mbs! first wildey used LAN technology Simpler, cheaper than token LANs and ATM Kept up with speed race: 10, 100, 1000 Mbps ...
Chapter 12 SOLUTIONS to Practice Problems
... If there are 7 billion people in the world, and we disperse Ethernet addresses uniformly, how many addresses are available for each person? Solution: Dividing the number of possible addresses by 7 billion people results in 10,000 Ethernet addresses ...
... If there are 7 billion people in the world, and we disperse Ethernet addresses uniformly, how many addresses are available for each person? Solution: Dividing the number of possible addresses by 7 billion people results in 10,000 Ethernet addresses ...