Algorithms for Nearest Neighbor Search
... – Use only i bits per dimension (and speed-up the scan by a factor of 32/i) – Identify all points which could be returned as an answer – Verify the points using original data set ...
... – Use only i bits per dimension (and speed-up the scan by a factor of 32/i) – Identify all points which could be returned as an answer – Verify the points using original data set ...
A Comparison of Adaptive Radix Trees and Hash Tables
... linear node is a space efficient implementation for nodes with very small number of children. In Judy, the size of linear nodes is limited to one cache line.1 Linear nodes start with a sorted list that contains only the partial keys for branches to existing child nodes. This list is then followed by ...
... linear node is a space efficient implementation for nodes with very small number of children. In Judy, the size of linear nodes is limited to one cache line.1 Linear nodes start with a sorted list that contains only the partial keys for branches to existing child nodes. This list is then followed by ...
Lecture 9. Semantic Analysis – Scoping and Symbol Table
... Generally, symbol table is only needed to answer those two questions, i.e., once all declarations have been processed to build the symbol table, and all uses have been processed to link each ID node in the abstract-syntax tree with the corresponding symbol-table entry, then the symbol table itself i ...
... Generally, symbol table is only needed to answer those two questions, i.e., once all declarations have been processed to build the symbol table, and all uses have been processed to link each ID node in the abstract-syntax tree with the corresponding symbol-table entry, then the symbol table itself i ...
chap09
... Hashing • An alternative to comparison-based search • Requires storing data in a special data structure, called a hash table • Main objectives to choosing hash functions: – Choose a hash function that is easy to compute – Minimize the number of collisions ...
... Hashing • An alternative to comparison-based search • Requires storing data in a special data structure, called a hash table • Main objectives to choosing hash functions: – Choose a hash function that is easy to compute – Minimize the number of collisions ...
Data Structures So Far
... public E get(int i) throws IndexOutOfBoundsException; /** Removes and returns the element at index I, shifting the elements after this. */ public E remove(int i) throws IndexOutOfBoundsException; /** Replaces the element at index I with e, returning the previous element at i. */ ...
... public E get(int i) throws IndexOutOfBoundsException; /** Removes and returns the element at index I, shifting the elements after this. */ public E remove(int i) throws IndexOutOfBoundsException; /** Replaces the element at index I with e, returning the previous element at i. */ ...
Data Structures and Text Editing
... README.txt. We are looking for quantified comparisons of performance when you use different data structures to back the text editor modules. VisualVM can be used for memory profiling. While System.nanoTime() can be used for timing operations in general, the built-in timing functionality can be used ...
... README.txt. We are looking for quantified comparisons of performance when you use different data structures to back the text editor modules. VisualVM can be used for memory profiling. While System.nanoTime() can be used for timing operations in general, the built-in timing functionality can be used ...
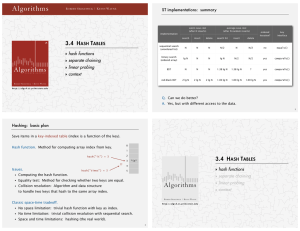
Algorithms
... ・Equality test: Method for checking whether two keys are equal. ・Collision resolution: Algorithm and data structure Computing the hash function. ...
... ・Equality test: Method for checking whether two keys are equal. ・Collision resolution: Algorithm and data structure Computing the hash function. ...
Similarity Search in High Dimension via Hashing
... • Exact vs. Approximate Answer – Approximate might be good-enough and much-faster – Time-quality trade-off ...
... • Exact vs. Approximate Answer – Approximate might be good-enough and much-faster – Time-quality trade-off ...
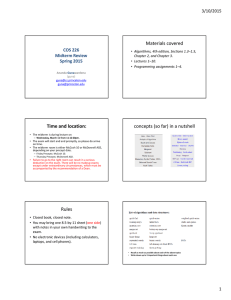
Time and location: Materials covered concepts (so far) in a nutshell COS 226
... Resizable array questions • resizing array by one gives amortized linear time per item (bad) • resizing array by doubling/halving gives amortized constant time (good) • What if instead of doubling the size of the array, we triple the size? good or bad? • Resizing also includes shrinking the array by ...
... Resizable array questions • resizing array by one gives amortized linear time per item (bad) • resizing array by doubling/halving gives amortized constant time (good) • What if instead of doubling the size of the array, we triple the size? good or bad? • Resizing also includes shrinking the array by ...
Java Review
... Performance of Hashing In the worst case, searches, insertions and removals on a hash table take O(n) time The worst case occurs when all the keys inserted into the map collide The load factor a = n/N affects the performance of a hash table Assuming that the hash values are like random numbers, it ...
... Performance of Hashing In the worst case, searches, insertions and removals on a hash table take O(n) time The worst case occurs when all the keys inserted into the map collide The load factor a = n/N affects the performance of a hash table Assuming that the hash values are like random numbers, it ...
COMP171H Notes: Hashing
... Graph Traversal: DFS Connectivity and cycle detection Time: O(M+N) Recursive function DFS tree ...
... Graph Traversal: DFS Connectivity and cycle detection Time: O(M+N) Recursive function DFS tree ...
Engineering a Sorted List Data Structure for 32 Bit Keys
... Our Stree is fastest over the entire range of inputs. For small n, it is much faster than comparison based structures up to a factor of 4.1. For random inputs of this size, locate mostly accesses the root-top data structure which fits in cache and hence is very fast. It even gets faster with increas ...
... Our Stree is fastest over the entire range of inputs. For small n, it is much faster than comparison based structures up to a factor of 4.1. For random inputs of this size, locate mostly accesses the root-top data structure which fits in cache and hence is very fast. It even gets faster with increas ...
Lecture 15
... compile after the syntax tree In some languages symbol table is involved during the process of parsing and even lexical analysis where they need to add some information in it or may need to look for something from it But in a careful designed language like Pascal or Ada, it is possible and reasonabl ...
... compile after the syntax tree In some languages symbol table is involved during the process of parsing and even lexical analysis where they need to add some information in it or may need to look for something from it But in a careful designed language like Pascal or Ada, it is possible and reasonabl ...
K - CS1001.py
... • Binary search trees are data structures used to represent collections of data items. They support operations like insert, search, delete, etc. • Each node in a binary search contains a single data record. As before, we will assume the record consists of a key and value. A node will also include po ...
... • Binary search trees are data structures used to represent collections of data items. They support operations like insert, search, delete, etc. • Each node in a binary search contains a single data record. As before, we will assume the record consists of a key and value. A node will also include po ...
Beyond Bloom Filters
... • Motivation: Try to turn non-terminating flow problem into an advantage. • Add a 1-bit flag to each cell, and a timer. – If a cell is not “touched” in a phase, 0 it out. ...
... • Motivation: Try to turn non-terminating flow problem into an advantage. • Add a 1-bit flag to each cell, and a timer. – If a cell is not “touched” in a phase, 0 it out. ...
Mid-term exam
... (a) Apply insertion sort to the array [4, 2, 3, 5, 1]. Give (at least) the intermediate result after every iteration of the for-loop. (b) Explain why the worst-case time complexity of insertion sort is in O(n2 ). Exercise 3. (8 points) This exercise is concerned with singly linked lists. (a) For a ...
... (a) Apply insertion sort to the array [4, 2, 3, 5, 1]. Give (at least) the intermediate result after every iteration of the for-loop. (b) Explain why the worst-case time complexity of insertion sort is in O(n2 ). Exercise 3. (8 points) This exercise is concerned with singly linked lists. (a) For a ...
Data structures and performance analysis
... In addition to the code you write for data structures and the text editor plugins, you should also submit any tests that you write. Testing is a component of the grade for this assignment. You should implement your test cases using JUnit, a framework for writing test suites. JUnit has excellent Ecli ...
... In addition to the code you write for data structures and the text editor plugins, you should also submit any tests that you write. Testing is a component of the grade for this assignment. You should implement your test cases using JUnit, a framework for writing test suites. JUnit has excellent Ecli ...
Teradata DBMS Features
... Row Hash is not sufficient to identify a specific row in a table. Multiple row can have same Row Hash either due to Hash Synonyms or NUPI. Row ID every row in a table uniquely identifiable. ...
... Row Hash is not sufficient to identify a specific row in a table. Multiple row can have same Row Hash either due to Hash Synonyms or NUPI. Row ID every row in a table uniquely identifiable. ...
Maintaining External Memory Efficient Hash Tables
... for a dynamic dictionary where the data associated with each key comprises r bits. Update operations are supported with high probability in constant time and the algorithm is stable. For the static case, Hagerup and Tholey [10] hold the space record: They show how to construct a minimal perfect has ...
... for a dynamic dictionary where the data associated with each key comprises r bits. Update operations are supported with high probability in constant time and the algorithm is stable. For the static case, Hagerup and Tholey [10] hold the space record: They show how to construct a minimal perfect has ...
Elementary Data Structures and Hash Tables
... All direct-address table operations are O(1)! So why isn’t every set implemented with a direct-address table? The space complexity is Θ(`U`) ...
... All direct-address table operations are O(1)! So why isn’t every set implemented with a direct-address table? The space complexity is Θ(`U`) ...
Slides for Exam 3 review
... – Compare with splay tree and RB tree • Operations – Find: according to key values as if it is a BST – Insert: as a leaf first as in BST, then rotate it to satisfy heap order – Delete: rotate the node to be deleted down according to heap order until it becomes a leaf, then delete it. – Support set u ...
... – Compare with splay tree and RB tree • Operations – Find: according to key values as if it is a BST – Insert: as a leaf first as in BST, then rotate it to satisfy heap order – Delete: rotate the node to be deleted down according to heap order until it becomes a leaf, then delete it. – Support set u ...
Hash table
In computing, a hash table (hash map) is a data structure used to implement an associative array, a structure that can map keys to values. A hash table uses a hash function to compute an index into an array of buckets or slots, from which the desired value can be found.Ideally, the hash function will assign each key to a unique bucket, but it is possible that two keys will generate an identical hash causing both keys to point to the same bucket. Instead, most hash table designs assume that hash collisions—different keys that are assigned by the hash function to the same bucket—will occur and must be accommodated in some way.In a well-dimensioned hash table, the average cost (number of instructions) for each lookup is independent of the number of elements stored in the table. Many hash table designs also allow arbitrary insertions and deletions of key-value pairs, at (amortized) constant average cost per operation.In many situations, hash tables turn out to be more efficient than search trees or any other table lookup structure. For this reason, they are widely used in many kinds of computer software, particularly for associative arrays, database indexing, caches, and sets.