Example of Sparse Index Files
... " Insert all the search-key values in the two nodes into a single node (the one on the left), and delete the other ...
... " Insert all the search-key values in the two nodes into a single node (the one on the left), and delete the other ...
pdf-1
... structure if search-key does not form a primary key. ! If Li, Lj are leaf nodes and i < j, Li’s search-key values are less ...
... structure if search-key does not form a primary key. ! If Li, Lj are leaf nodes and i < j, Li’s search-key values are less ...
ppt
... structure if search-key does not form a primary key. If Li, Lj are leaf nodes and i < j, Li’s search-key values are less ...
... structure if search-key does not form a primary key. If Li, Lj are leaf nodes and i < j, Li’s search-key values are less ...
Indexing and Hashing
... structure if search-key does not form a primary key. ! If Li, Lj are leaf nodes and i < j, Li’s search-key values are less ...
... structure if search-key does not form a primary key. ! If Li, Lj are leaf nodes and i < j, Li’s search-key values are less ...
Load Balancing and Locality in Range
... Figure 1). This continues until the key becomes a singleton, which will result in, on average, O(log n) levels in the skip graph. For a complete description of the data structure, please see [2]. The search, insertion, and deletion algorithms for a skip graph are essentially the same as for a skip l ...
... Figure 1). This continues until the key becomes a singleton, which will result in, on average, O(log n) levels in the skip graph. For a complete description of the data structure, please see [2]. The search, insertion, and deletion algorithms for a skip graph are essentially the same as for a skip l ...
Chapter 12 Notes
... structure if search-key does not form a primary key. If Li, Lj are leaf nodes and i < j, Li’s search-key values are less ...
... structure if search-key does not form a primary key. If Li, Lj are leaf nodes and i < j, Li’s search-key values are less ...
Data Modeling - Temple Fox MIS
... • The only required field is CustomerID – the rest can be left blank. • CustomerID is defined as the primary key. ...
... • The only required field is CustomerID – the rest can be left blank. • CustomerID is defined as the primary key. ...
Physical Data Organization and Indexing
... • Algorithm guarantees that the number of separator entries in an index page is between /2 and – Hence the maximum search cost is log/2Q + 1 (with ISAM search cost depends on length of overflow chain) ...
... • Algorithm guarantees that the number of separator entries in an index page is between /2 and – Hence the maximum search cost is log/2Q + 1 (with ISAM search cost depends on length of overflow chain) ...
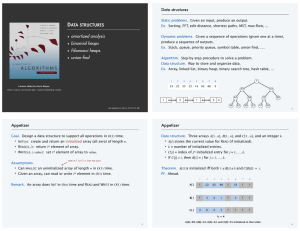
n+1
... - worst-case time per operation number of operations - ignores the correlated effects on the DS - this upper-bound is most often too pessimistic ...
... - worst-case time per operation number of operations - ignores the correlated effects on the DS - this upper-bound is most often too pessimistic ...
Container data structures Topics for this lecture
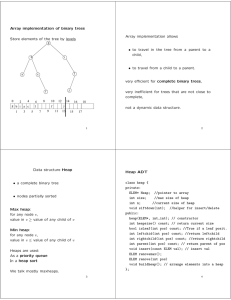
... bound, and thus a fixed capacity. Unlike most other programming languages, Eiffel allows resizing an array (resize). Feature force resizes an array if required. Resizing usually requires reallocating the array and copying the old values. Such operations are costly! ...
... bound, and thus a fixed capacity. Unlike most other programming languages, Eiffel allows resizing an array (resize). Feature force resizes an array if required. Resizing usually requires reallocating the array and copying the old values. Such operations are costly! ...
Efficient IP Table Lookup via Adaptive Stratified Trees with - IIT-CNR
... The AST construction algorithm is described in Section (5). Here we summarize the main new ideas. The best way to explain the gist of the algorithm is to visualize it geometrically. We first map the lookup problem into a predecessor search problem (see Section (4.2) for details). The equivalent inpu ...
... The AST construction algorithm is described in Section (5). Here we summarize the main new ideas. The best way to explain the gist of the algorithm is to visualize it geometrically. We first map the lookup problem into a predecessor search problem (see Section (4.2) for details). The equivalent inpu ...
read it here
... the sought location. The associativity of caches t is usually a small power of two, like 8 or 16. The set of possible cache locations for lines in memory is determined by simply masking out a few address bits. This approach implies that accessing too many locations with addresses differing exactly b ...
... the sought location. The associativity of caches t is usually a small power of two, like 8 or 16. The set of possible cache locations for lines in memory is determined by simply masking out a few address bits. This approach implies that accessing too many locations with addresses differing exactly b ...
MIS2502: Data Analytics SQL – Putting Information Into a Database
... • The only required field is CustomerID – the rest can be left blank. • CustomerID is defined as the primary key. ...
... • The only required field is CustomerID – the rest can be left blank. • CustomerID is defined as the primary key. ...
Locality Preserving Hashing Kang Zhao, Hongtao Lu and Jincheng Mei
... applications, the numerous hashing tables will cost considerable storage and query time. Besides, long codes will decrease the collision probability of similar samples, consequently resulting in low recall. Due to the shortcomings of data-independent methods, many data-dependent methods have been de ...
... applications, the numerous hashing tables will cost considerable storage and query time. Besides, long codes will decrease the collision probability of similar samples, consequently resulting in low recall. Due to the shortcomings of data-independent methods, many data-dependent methods have been de ...
Hash-Based Indexes - University of Houston
... 100MB file, 100 bytes/rec, 4K pages contains 1,000,000 records (as data entries) and 25,000 directory elements; chances are high that directory will fit in memory. Directory grows in spurts, and, if the distribution of hash values is skewed, directory can grow large. Multiple entries with same hash ...
... 100MB file, 100 bytes/rec, 4K pages contains 1,000,000 records (as data entries) and 25,000 directory elements; chances are high that directory will fit in memory. Directory grows in spurts, and, if the distribution of hash values is skewed, directory can grow large. Multiple entries with same hash ...
Coda Server Internals
... DirPages 2048 bytes each build up the directory divided into 64 32byte blobs Hash table for fast name lookups Blob Freelist Array of free blobs per page ...
... DirPages 2048 bytes each build up the directory divided into 64 32byte blobs Hash table for fast name lookups Blob Freelist Array of free blobs per page ...
ppt
... • Need to be able to add or delete items • Total number of items unknown • But an approximate maximum might be known ...
... • Need to be able to add or delete items • Total number of items unknown • But an approximate maximum might be known ...
TUKE-08-SRBD-02-Fyzicke-organizacie
... • The records of files R and S are both hashed to the same hash file, using the same hashing function on the join attributes A of R and B of S as hash keys. • First, a single pass through the file with fewer records (say, R) hashes its records to the hash file buckets (partitioning phase - records o ...
... • The records of files R and S are both hashed to the same hash file, using the same hashing function on the join attributes A of R and B of S as hash keys. • First, a single pass through the file with fewer records (say, R) hashes its records to the hash file buckets (partitioning phase - records o ...
ICOM4015-lec18
... • Adding an element: simple extension of the algorithm for finding an object Compute the hash code to locate the bucket in which the element should be inserted Try finding the object in that bucket If it is already present, do nothing; otherwise, ...
... • Adding an element: simple extension of the algorithm for finding an object Compute the hash code to locate the bucket in which the element should be inserted Try finding the object in that bucket If it is already present, do nothing; otherwise, ...
Hash table
In computing, a hash table (hash map) is a data structure used to implement an associative array, a structure that can map keys to values. A hash table uses a hash function to compute an index into an array of buckets or slots, from which the desired value can be found.Ideally, the hash function will assign each key to a unique bucket, but it is possible that two keys will generate an identical hash causing both keys to point to the same bucket. Instead, most hash table designs assume that hash collisions—different keys that are assigned by the hash function to the same bucket—will occur and must be accommodated in some way.In a well-dimensioned hash table, the average cost (number of instructions) for each lookup is independent of the number of elements stored in the table. Many hash table designs also allow arbitrary insertions and deletions of key-value pairs, at (amortized) constant average cost per operation.In many situations, hash tables turn out to be more efficient than search trees or any other table lookup structure. For this reason, they are widely used in many kinds of computer software, particularly for associative arrays, database indexing, caches, and sets.