struct node - Information Service at Internet Computing Lab
... • Figure 12.5 illustrates the insertion of a node containing the character 'C' into an ordered list. • Part (a) of the figure shows the list and the new node just before the insertion. • Part (b) of the figure shows the result of inserting the new node. • The reassigned pointers are dotted arrows. • ...
... • Figure 12.5 illustrates the insertion of a node containing the character 'C' into an ordered list. • Part (a) of the figure shows the list and the new node just before the insertion. • Part (b) of the figure shows the result of inserting the new node. • The reassigned pointers are dotted arrows. • ...
Unimodal Regression via Prefix Isotonic
... ordering, and isotonic regression is often called monotonic regression, though in some application areas this term means the values decrease. Isotonic regression does not yield a smooth curve, but rather a collection of level sets where the regression is constant. Figure 1 gives an example of an iso ...
... ordering, and isotonic regression is often called monotonic regression, though in some application areas this term means the values decrease. Isotonic regression does not yield a smooth curve, but rather a collection of level sets where the regression is constant. Figure 1 gives an example of an iso ...
The LHAM log-structured history data access method
... 2.1 Partitioning the time dimension The basic idea of LHAM is to divide the entire time domain into successive intervals and to assign each interval to a separate storage component. The series of components, denoted as C0 , C1 , . . . , Cn , constitutes a partitioning of the history data based on th ...
... 2.1 Partitioning the time dimension The basic idea of LHAM is to divide the entire time domain into successive intervals and to assign each interval to a separate storage component. The series of components, denoted as C0 , C1 , . . . , Cn , constitutes a partitioning of the history data based on th ...
Functional data structures and algorithms - Milan Straka
... Versions of a fully persistent data structure form a rooted tree, where the root is the initial version of the structure and an edge denotes that a version was created from its predecessor. In case of partially persistent structures, versions form a directed path. Versions of a persistent data struc ...
... Versions of a fully persistent data structure form a rooted tree, where the root is the initial version of the structure and an edge denotes that a version was created from its predecessor. In case of partially persistent structures, versions form a directed path. Versions of a persistent data struc ...
Stronger Lempel-Ziv Based Compressed Text Indexing | SpringerLink
... occ) log u) and a space requirement of O(uHk (T )) bits, plus the text (as it is needed to operate) [41]. Navarro’s LZ-index [39, 40], on the other hand, is a compressed full-text self-index based on the Lempel-Ziv 1978 [48] (LZ78 for short) parsing of the text. See Sect. 2.3 for a description of th ...
... occ) log u) and a space requirement of O(uHk (T )) bits, plus the text (as it is needed to operate) [41]. Navarro’s LZ-index [39, 40], on the other hand, is a compressed full-text self-index based on the Lempel-Ziv 1978 [48] (LZ78 for short) parsing of the text. See Sect. 2.3 for a description of th ...
Oblivious Data Structures - Cryptology ePrint Archive
... Practical performance savings. We evaluated our oblivious data structures with various application scenarios in mind. For the outsourced cloud storage and secure processor settings, bandwidth blowup is the key metric; whereas for a secure computation setting, we consider the number of AES encryption ...
... Practical performance savings. We evaluated our oblivious data structures with various application scenarios in mind. For the outsourced cloud storage and secure processor settings, bandwidth blowup is the key metric; whereas for a secure computation setting, we consider the number of AES encryption ...
IDL, Interface Description Language
... This report defines a general mechanism, IDL, by which structured data can be precisely specified. The objective of this specification is to permit the data to be communicated between programs, or parts of a single program, in a safe and efficient manner. IDL grew out of work on the Production Quali ...
... This report defines a general mechanism, IDL, by which structured data can be precisely specified. The objective of this specification is to permit the data to be communicated between programs, or parts of a single program, in a safe and efficient manner. IDL grew out of work on the Production Quali ...
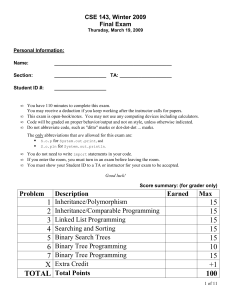
Linked Lists
... In array implementation of the linked lists a fixed set of nodes represented by an array is established at the beginning of the execution A pointer to a node is represented by the relative position of the node within the array. In array implementation, it is not possible to determine the number of n ...
... In array implementation of the linked lists a fixed set of nodes represented by an array is established at the beginning of the execution A pointer to a node is represented by the relative position of the node within the array. In array implementation, it is not possible to determine the number of n ...
Document
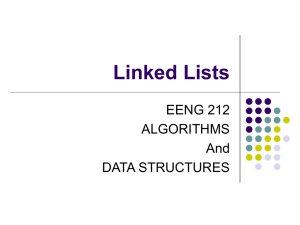
... 2. If the node reached by following the pointer above is not a leaf node, repeat the above procedure on the node, and follow the corresponding pointer. 3. Eventually reach a leaf node. If for some i, key Ki = k follow pointer Pi to the desired record or bucket. Else no record with search-key value k ...
... 2. If the node reached by following the pointer above is not a leaf node, repeat the above procedure on the node, and follow the corresponding pointer. 3. Eventually reach a leaf node. If for some i, key Ki = k follow pointer Pi to the desired record or bucket. Else no record with search-key value k ...
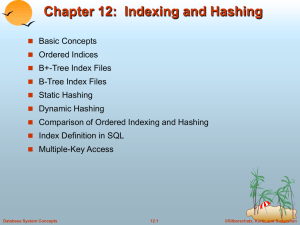
Optimal Purely Functional Priority Queues
... n. For example, consider a binomial queue of size 21. The binary representation of 21 is 10101, and the binomial queue contains trees of ranks 0, 2, and 4 (of sizes 1, 4, and 16, respectively). Note that a binomial queue of size n contains at most blog2 (n + 1)c trees. We are now ready to describe t ...
... n. For example, consider a binomial queue of size 21. The binary representation of 21 is 10101, and the binomial queue contains trees of ranks 0, 2, and 4 (of sizes 1, 4, and 16, respectively). Note that a binomial queue of size n contains at most blog2 (n + 1)c trees. We are now ready to describe t ...
Quadtree
A quadtree is a tree data structure in which each internal node has exactly four children. Quadtrees are most often used to partition a two-dimensional space by recursively subdividing it into four quadrants or regions. The regions may be square or rectangular, or may have arbitrary shapes. This data structure was named a quadtree by Raphael Finkel and J.L. Bentley in 1974. A similar partitioning is also known as a Q-tree. All forms of quadtrees share some common features: They decompose space into adaptable cells Each cell (or bucket) has a maximum capacity. When maximum capacity is reached, the bucket splits The tree directory follows the spatial decomposition of the quadtree.