Optimal Verification of Operations on Dynamic Sets
... both important properties in the context of data querying. Indeed, the works in [2, 11, 17] are primarily designed to provide secrecy of the outsourced computations, and as such, the client makes use of some secret information to outsource the computation as a circuit and in an encrypted form. This ...
... both important properties in the context of data querying. Indeed, the works in [2, 11, 17] are primarily designed to provide secrecy of the outsourced computations, and as such, the client makes use of some secret information to outsource the computation as a circuit and in an encrypted form. This ...
Efficient Data Structures and Algorithms for Range
... This thesis would not have been possible without the help of many people due to various reasons. First and foremost, I would like to express my sincere gratitude to my advisor Dr. Kannan Srinathan for continuous encouragement in exploring various research areas irrespective of his own interest and p ...
... This thesis would not have been possible without the help of many people due to various reasons. First and foremost, I would like to express my sincere gratitude to my advisor Dr. Kannan Srinathan for continuous encouragement in exploring various research areas irrespective of his own interest and p ...
Answering Top-k Queries Over a Mixture of Attractive and Repulsive
... plane, each point generates four projections in four directions. We call these projections left lower projection (abbr. llp), right lower projection (abbr. rlp), left upper projection (abbr. lup) and right upper projection (abbr. rup). An example is shown in Figure 2b. From geometric reasoning, proj ...
... plane, each point generates four projections in four directions. We call these projections left lower projection (abbr. llp), right lower projection (abbr. rlp), left upper projection (abbr. lup) and right upper projection (abbr. rup). An example is shown in Figure 2b. From geometric reasoning, proj ...
2. Non-Linear Data Structure: - In non linear data
... of the AR) 5. The Program Counter is set to the location of the first bytecode of the method being called 6. Copies the calling parameters into the Parameter region 7. Initializes local variables in the local variable region While the method executes, the local variables and parameters are simply fo ...
... of the AR) 5. The Program Counter is set to the location of the first bytecode of the method being called 6. Copies the calling parameters into the Parameter region 7. Initializes local variables in the local variable region While the method executes, the local variables and parameters are simply fo ...
CS 171: Introduction to Computer Science II Linked List
... • Example: remove “be” from the linked list • Search the item, then remove it • Need to keep the reference to the previous element as well as current element. • Need to consider the case when current is first Node current = first; Node previous = first; while (current != null && !current.item.equals ...
... • Example: remove “be” from the linked list • Search the item, then remove it • Need to keep the reference to the previous element as well as current element. • Need to consider the case when current is first Node current = first; Node previous = first; while (current != null && !current.item.equals ...
Data Structures and Algorithms for Data
... Through the years, I was fortunate to supervise semester and master projects of several exceptional students. I feel that I have to mention at least a few of them. First, I want to thank Ngoc Duy Pham for the preliminary exploration of the techniques used in the ScalaMeter framework. It was a pleasu ...
... Through the years, I was fortunate to supervise semester and master projects of several exceptional students. I feel that I have to mention at least a few of them. First, I want to thank Ngoc Duy Pham for the preliminary exploration of the techniques used in the ScalaMeter framework. It was a pleasu ...
2nd Workshop on Algorithm Engineering WAE`98 { Proceedings
... elements in the same workpiece. They are the reason why the problem is non-trivial, since we have no knowledge whether an edge is neighboured to one, several or no other edges (Figure 8). Consider two edges that are situated next to each other. The gap between them may have been intended by the engi ...
... elements in the same workpiece. They are the reason why the problem is non-trivial, since we have no knowledge whether an edge is neighboured to one, several or no other edges (Figure 8). Consider two edges that are situated next to each other. The gap between them may have been intended by the engi ...
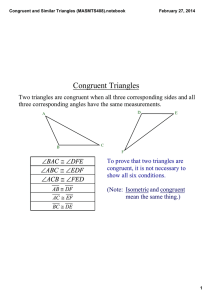
congruent triangles
... CONGRUENT TRIANGLES Definition of congruent triangles: Two triangles are congruent if and only if their vertices can be matched up so that corresponding parts of the triangles are congruent. ...
... CONGRUENT TRIANGLES Definition of congruent triangles: Two triangles are congruent if and only if their vertices can be matched up so that corresponding parts of the triangles are congruent. ...
Implementations of stack menu driven program. Implementations of
... have a natural order. Elements are removed from the stack in the reverse order to the order of their addition. Therefore, the lower elements are those that have been on the stack the longest ...
... have a natural order. Elements are removed from the stack in the reverse order to the order of their addition. Therefore, the lower elements are those that have been on the stack the longest ...
21 Collections of data
... 21 Collections of data As illustrated in the "Air Traffic Controller" example in Chapter 20, arrays can be used to store collections of data. But arrays do have limitations (e.g. you have to specify a maximum size), and they don't provide any useful support function that might help manage a data col ...
... 21 Collections of data As illustrated in the "Air Traffic Controller" example in Chapter 20, arrays can be used to store collections of data. But arrays do have limitations (e.g. you have to specify a maximum size), and they don't provide any useful support function that might help manage a data col ...
Congruent and Similar Triangles (MASMTS408).notebook
... 3) If two angles and the contained side of one triangle are congruent to two corresponding angles and contained side of another triangle, then the triangles are congruent. This is called the Angle Side Angle ...
... 3) If two angles and the contained side of one triangle are congruent to two corresponding angles and contained side of another triangle, then the triangles are congruent. This is called the Angle Side Angle ...
Concise Notes on Data Structures and Algorithms
... Concise Notes on Data Structures and Algorithms Ruby Edition Christopher Fox ...
... Concise Notes on Data Structures and Algorithms Ruby Edition Christopher Fox ...
Quadtree
A quadtree is a tree data structure in which each internal node has exactly four children. Quadtrees are most often used to partition a two-dimensional space by recursively subdividing it into four quadrants or regions. The regions may be square or rectangular, or may have arbitrary shapes. This data structure was named a quadtree by Raphael Finkel and J.L. Bentley in 1974. A similar partitioning is also known as a Q-tree. All forms of quadtrees share some common features: They decompose space into adaptable cells Each cell (or bucket) has a maximum capacity. When maximum capacity is reached, the bucket splits The tree directory follows the spatial decomposition of the quadtree.