Document
... – Compiler: All possible identifiers allowed by the language vs. those used in some file of one program – Database: All possible student names vs. students enrolled – AI: All possible chess-board configurations vs. those considered by the current player Edition 2016 ...
... – Compiler: All possible identifiers allowed by the language vs. those used in some file of one program – Database: All possible student names vs. students enrolled – AI: All possible chess-board configurations vs. those considered by the current player Edition 2016 ...
The Pigeonhole Principle and Hashing
... Hashing and Association Tables (Maps, Dictionaries) A dictionary (or map or association table) is a collection of keyvalue pairs. In general, the objects in a table have no fixed order and each object is accessed by using the associated key. For example, we could have a table of motor vehicle drive ...
... Hashing and Association Tables (Maps, Dictionaries) A dictionary (or map or association table) is a collection of keyvalue pairs. In general, the objects in a table have no fixed order and each object is accessed by using the associated key. For example, we could have a table of motor vehicle drive ...
ppt - Dave Reed
... cost of search is proportional to number of items already mapped to same index e.g., using naïve "first letter" hash function, searching for "APPLE" might requires traversing a list of all words beginning with 'A' if hash function is fair, then will have roughly λ/tableSize items in each bucket ...
... cost of search is proportional to number of items already mapped to same index e.g., using naïve "first letter" hash function, searching for "APPLE" might requires traversing a list of all words beginning with 'A' if hash function is fair, then will have roughly λ/tableSize items in each bucket ...
hash function
... if the table becomes three-quarters full, then must resize create new table at least twice as big just copy over table entries to same locations??? NO! when you resize, you have to rehash existing entries new table size new hash function (+ different wraparound) ...
... if the table becomes three-quarters full, then must resize create new table at least twice as big just copy over table entries to same locations??? NO! when you resize, you have to rehash existing entries new table size new hash function (+ different wraparound) ...
y-fast Trees
... So our expected space is about 2n. More specifically, the probability P r[space > 4n] < 12 . If we clobber an element, we pick some other hash function for that bucket. We will need to choose new hash functions only an expected constant number of times per bucket, because we have a constant probabil ...
... So our expected space is about 2n. More specifically, the probability P r[space > 4n] < 12 . If we clobber an element, we pick some other hash function for that bucket. We will need to choose new hash functions only an expected constant number of times per bucket, because we have a constant probabil ...
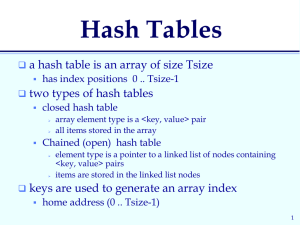
Hash Tables
... • The key is squared and the middle part of the result taken as the hash value. • To map the key 3121 into a hash table of size 1000, we square it 31212 = 9740641 and extract 406 as the hash value. • Works well if the keys do not contain a lot of leading or trailing zeros. • Non-integer keys have to ...
... • The key is squared and the middle part of the result taken as the hash value. • To map the key 3121 into a hash table of size 1000, we square it 31212 = 9740641 and extract 406 as the hash value. • Works well if the keys do not contain a lot of leading or trailing zeros. • Non-integer keys have to ...
Hashing 1
... • The key is squared and the middle part of the result taken as the hash value. • To map the key 3121 into a hash table of size 1000, we square it 31212 = 9740641 and extract 406 as the hash value. • Works well if the keys do not contain a lot of leading or trailing zeros. • Non-integer keys have to ...
... • The key is squared and the middle part of the result taken as the hash value. • To map the key 3121 into a hash table of size 1000, we square it 31212 = 9740641 and extract 406 as the hash value. • Works well if the keys do not contain a lot of leading or trailing zeros. • Non-integer keys have to ...
slides
... buckets are numbered 0 to b - 1 hash function maps elements to value in 0 to b – 1 operations use hash to determine which bucket an element belongs in and only searches/modifies this one bucket hash func. h(element) ...
... buckets are numbered 0 to b - 1 hash function maps elements to value in 0 to b – 1 operations use hash to determine which bucket an element belongs in and only searches/modifies this one bucket hash func. h(element) ...
hash function
... *legal disclaimer: performance can degrade to O(N) under bad/unlikely conditions however, careful setup and maintenance can ensure O(1) in practice ...
... *legal disclaimer: performance can degrade to O(N) under bad/unlikely conditions however, careful setup and maintenance can ensure O(1) in practice ...
DSLec(Hashing). - CSE246DataStructures
... digit indices of array will be sufficient. But if the 100 inventory with 5-digit of code then we have to use 5-digit indices of array but store only 100 records will waste the memory. Map key values to hash table addresses keys -> hash table address This applies to find, insert, and remove Usually: ...
... digit indices of array will be sufficient. But if the 100 inventory with 5-digit of code then we have to use 5-digit indices of array but store only 100 records will waste the memory. Map key values to hash table addresses keys -> hash table address This applies to find, insert, and remove Usually: ...
CS 61B Data Structures and Programming Methodology
... – Unfortunately, declaring an array of length 2645 is out of the question. – English has fewer than one million words, so we should be able to do better. ...
... – Unfortunately, declaring an array of length 2645 is out of the question. – English has fewer than one million words, so we should be able to do better. ...
notes
... • The key is usually a number, but can be a string or any other data type. – Non-numbers are converted to numbers when applying hashing. ...
... • The key is usually a number, but can be a string or any other data type. – Non-numbers are converted to numbers when applying hashing. ...
Data Structures (810:052) Lab 11 - Hashing Name:_________________
... function. A perfect hash function would take your set of target values and map each to a unique list/array index. Unfortunately, perfect hash functions are a rarity, so in general two or more target values might get mapped to the same hash-table index, called a collision. Collisions are handled by t ...
... function. A perfect hash function would take your set of target values and map each to a unique list/array index. Unfortunately, perfect hash functions are a rarity, so in general two or more target values might get mapped to the same hash-table index, called a collision. Collisions are handled by t ...
HashingFinal
... • Polynomial accumulation: for strings of a natural language, combine the character values (ASCII or Unicode) a 0 a 1 ... a n-1 by viewing them as the coefficients of a polynomial: a 0 + a 1 x + ...+ a n-1 x n-1 • For instance, choosing x = 33, 37, 39, or 41 gives at most 6 collisions on a vocabular ...
... • Polynomial accumulation: for strings of a natural language, combine the character values (ASCII or Unicode) a 0 a 1 ... a n-1 by viewing them as the coefficients of a polynomial: a 0 + a 1 x + ...+ a n-1 x n-1 • For instance, choosing x = 33, 37, 39, or 41 gives at most 6 collisions on a vocabular ...
word - Courses
... given input k should always produce the same output h(k ) . Since U m , and in general U is much larger than m, there must be at least two keys that have the same hash value, and therefore avoiding collisions altogether is impossible. Thus, while a well designed random looking hash function can mi ...
... given input k should always produce the same output h(k ) . Since U m , and in general U is much larger than m, there must be at least two keys that have the same hash value, and therefore avoiding collisions altogether is impossible. Thus, while a well designed random looking hash function can mi ...
Split-Ordered Lists: Lock-Free Extensible Hash Tables
... bits (LSB) of the key determines the bucket. It turns out that the so called recursive split-ordering is achieved by binary reversal of the keys. For example, the split-order of key 13 is reverse(1310 ) = reverse(000011012 ) = 101100002 , as shown in Figure 1. For technical reasons, it is convenient ...
... bits (LSB) of the key determines the bucket. It turns out that the so called recursive split-ordering is achieved by binary reversal of the keys. For example, the split-order of key 13 is reverse(1310 ) = reverse(000011012 ) = 101100002 , as shown in Figure 1. For technical reasons, it is convenient ...
Power Point 2000
... Basic idea: each table entry is associated with multiple (key, value) pairs Sequentially look through those pairs + incremental growth of the table - poor performance when an entry is associated with too many (key, value) pairs ...
... Basic idea: each table entry is associated with multiple (key, value) pairs Sequentially look through those pairs + incremental growth of the table - poor performance when an entry is associated with too many (key, value) pairs ...
Notes 33 Royden
... •Index functions are not always simple functions that compute an integer value from integer inputs. ...
... •Index functions are not always simple functions that compute an integer value from integer inputs. ...
Hashing
... Perfect hashing Goal: worst-case O(1) search space used O(m) static set of elements n = m2 ...
... Perfect hashing Goal: worst-case O(1) search space used O(m) static set of elements n = m2 ...
Hashing
... Insert and find operations can be implemented using a BST with average insert/find time of O(logn). However, a BST is generally a more powerful data structure than a hash table as it can easily support routines that require order, for example, finding the smallest/largest element. ...
... Insert and find operations can be implemented using a BST with average insert/find time of O(logn). However, a BST is generally a more powerful data structure than a hash table as it can easily support routines that require order, for example, finding the smallest/largest element. ...
Document
... 4.)* Download the Graph Theory Demo and implement a minimum spanning tree algorithm by Kruskal (the algorithm is easy but you will need to understand the original code written in lectures). Test it with a sufficiently large Graph. 5.)* Implement a simple Hash-Table, using the LinkedList method for c ...
... 4.)* Download the Graph Theory Demo and implement a minimum spanning tree algorithm by Kruskal (the algorithm is easy but you will need to understand the original code written in lectures). Test it with a sufficiently large Graph. 5.)* Implement a simple Hash-Table, using the LinkedList method for c ...
ppt (new version
... (i) Indicate what data structure B and pre-processing function PreProcess can be used to speed-up IsMember. What is the worstcase complexity of PreProcess? (ii) Write a function IsMember I that takes advantage of the data structure B. What is the worst-case complexity of IsMember ? What is pre-proce ...
... (i) Indicate what data structure B and pre-processing function PreProcess can be used to speed-up IsMember. What is the worstcase complexity of PreProcess? (ii) Write a function IsMember I that takes advantage of the data structure B. What is the worst-case complexity of IsMember ? What is pre-proce ...
Heap Sort
... data structure implemented as an array of objects, where the search keys correspond to the array indices ► Insert and find operations involve straight forward array accesses: O(1) time complexity ...
... data structure implemented as an array of objects, where the search keys correspond to the array indices ► Insert and find operations involve straight forward array accesses: O(1) time complexity ...
Rainbow table
A rainbow table is a precomputed table for reversing cryptographic hash functions, usually for cracking password hashes. Tables are usually used in recovering a plaintext password up to a certain length consisting of a limited set of characters. It is a practical example of a space/time trade-off, using less computer processing time and more storage than a brute-force attack which calculates a hash on every attempt, but more processing time and less storage than a simple lookup table with one entry per hash. Use of a key derivation function that employs a salt makes this attack infeasible.Rainbow tables are an application of an earlier, simpler algorithm by Martin Hellman.