Data Searching and Binary Search
... search by allowing for insertion and deletion of data records. • Dynamic binary tree search makes actual use of the binary ...
... search by allowing for insertion and deletion of data records. • Dynamic binary tree search makes actual use of the binary ...
2011
... Write a short note on linked list including the storage structure, advantage, and disadvantage. Write a pseudo code to add a node in the linked list at the end of the linked list. Write a pseudo code to add a node at the front of the linked list. Write a pseudo code to add a node at particular posit ...
... Write a short note on linked list including the storage structure, advantage, and disadvantage. Write a pseudo code to add a node in the linked list at the end of the linked list. Write a pseudo code to add a node at the front of the linked list. Write a pseudo code to add a node at particular posit ...
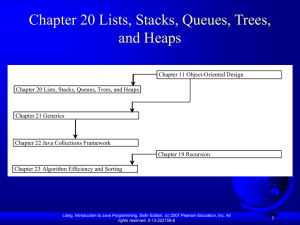
Chapter 19 Java Data Structures
... exceeded, create a new larger array and copy all the elements from the current array to the new array. The other approach is to use a linked structure. A linked structure consists of nodes. Each node is dynamically created to hold an element. All the nodes are linked together to form a list. Liang, ...
... exceeded, create a new larger array and copy all the elements from the current array to the new array. The other approach is to use a linked structure. A linked structure consists of nodes. Each node is dynamically created to hold an element. All the nodes are linked together to form a list. Liang, ...
Scalable Distributed Data Structures: A Survey
... a file across multiple servers of a distributed system. Furthermore, an SDDS has a focused view on efficiency considerations, disregarding other aspects completely. Consider a file that contains a set of records and is managed by a single server at a single node of a computer network, accessed by a ...
... a file across multiple servers of a distributed system. Furthermore, an SDDS has a focused view on efficiency considerations, disregarding other aspects completely. Consider a file that contains a set of records and is managed by a single server at a single node of a computer network, accessed by a ...
Numerical Representations as Purely Functional Data
... • they can be used in purely functional programming languages without language extensions; • they can also be used in imperative languages (especially those with garbage collection support), where they avoid expensive copy operations; • being read-only, they offer greater potential for performance i ...
... • they can be used in purely functional programming languages without language extensions; • they can also be used in imperative languages (especially those with garbage collection support), where they avoid expensive copy operations; • being read-only, they offer greater potential for performance i ...
AVL tree
... • To delete a node from an AVL tree, we will use similar ideas with the ones we used for insertion. • We will reduce the problem to the case when the node x to be deleted has at most one child. • Suppose x has two children. Find the immediate predecessor y of x under inorder traversal by first takin ...
... • To delete a node from an AVL tree, we will use similar ideas with the ones we used for insertion. • We will reduce the problem to the case when the node x to be deleted has at most one child. • Suppose x has two children. Find the immediate predecessor y of x under inorder traversal by first takin ...
Data structure - E
... 35 A linked list whose last node points back to the list node instead of containing the null pointer________. (1) circular list (2) circular doubly linked list (3) linke list (4) doubly linked list 36 Which of the following is two way lists? (1) Grounded header list. (2) Circular header list. (3) li ...
... 35 A linked list whose last node points back to the list node instead of containing the null pointer________. (1) circular list (2) circular doubly linked list (3) linke list (4) doubly linked list 36 Which of the following is two way lists? (1) Grounded header list. (2) Circular header list. (3) li ...
Linked Lists (Chapter 6)
... Doubly Linked Lists • To enhance greater flexibility of movement, the linked representation could include two links in every node, each of which points to the nodes on either side of the given node • Such a linked representation known as doubly linked list • Each node has one or more data fields but ...
... Doubly Linked Lists • To enhance greater flexibility of movement, the linked representation could include two links in every node, each of which points to the nodes on either side of the given node • Such a linked representation known as doubly linked list • Each node has one or more data fields but ...
Performance Analysis of BSTs in System Software 1
... tables also do not efficiently support range queries needed to determine which existing VMAs overlap the range requested by a mmap or munmap call. BST-based data structures, on the other hand, have both these properties, so many kernels use BSTs for keeping track of VMAs: Linux before 2.4.10 used AV ...
... tables also do not efficiently support range queries needed to determine which existing VMAs overlap the range requested by a mmap or munmap call. BST-based data structures, on the other hand, have both these properties, so many kernels use BSTs for keeping track of VMAs: Linux before 2.4.10 used AV ...
TOPIC: LIST AND LINKED LIST
... This means we usually waste space rather than have program run out. It also means that it is difficult to construct ordered lists. In our implementation, data must be added to the end. If inserted before the end, all others beneath it must shuffle down. This is slow and inefficient. Insertion shuffl ...
... This means we usually waste space rather than have program run out. It also means that it is difficult to construct ordered lists. In our implementation, data must be added to the end. If inserted before the end, all others beneath it must shuffle down. This is slow and inefficient. Insertion shuffl ...
Preliminary version
... • cut(v): Given a nonroot node v, make it a root by We consider forests of rooted trees, heap-ordered with deleting the arc connecting v to its parent, thereby respect to distinct node labels. We view arcs as being breaking its tree in two. directed from child to parent, so that paths lead from The ...
... • cut(v): Given a nonroot node v, make it a root by We consider forests of rooted trees, heap-ordered with deleting the arc connecting v to its parent, thereby respect to distinct node labels. We view arcs as being breaking its tree in two. directed from child to parent, so that paths lead from The ...
Combining Binary Search Trees
... of splay trees concerns proving various bounds on the running time of splay trees and other BST data structures [4, 6, 7, 12, 15]. Sleator and Tarjan [15] proved a number of upper bounds on the performance of splay trees. The static optimality bound requires that any access sequence is executed with ...
... of splay trees concerns proving various bounds on the running time of splay trees and other BST data structures [4, 6, 7, 12, 15]. Sleator and Tarjan [15] proved a number of upper bounds on the performance of splay trees. The static optimality bound requires that any access sequence is executed with ...
Basic Data Structures
... // Here are the operations to be implemented. // Create and destroy a list list(); ~list(); // Get the number of items in the list ...
... // Here are the operations to be implemented. // Create and destroy a list list(); ~list(); // Get the number of items in the list ...
Self-Adjusting Binary Search Trees DANIEL DOMINIC
... We introduce splay trees by way of a specific application. Consider the problem of performing a sequence of accessoperations on a set of items selected from a totally ordered universe. Each item may have some associated information. The input to each operation is an item; the output of the operation ...
... We introduce splay trees by way of a specific application. Consider the problem of performing a sequence of accessoperations on a set of items selected from a totally ordered universe. Each item may have some associated information. The input to each operation is an item; the output of the operation ...
Chapter x - CHAPTER TITLE
... It is very important that the student understand that linked lists have this in common with strings: there is a NULL terminator for each. Even though they are spelled differently, they are both 0. (‘\0’ is one spelling for 0, and is a character. NULL is another spelling for 0; this one is an integer ...
... It is very important that the student understand that linked lists have this in common with strings: there is a NULL terminator for each. Even though they are spelled differently, they are both 0. (‘\0’ is one spelling for 0, and is a character. NULL is another spelling for 0; this one is an integer ...
linked list
... Fixed size Insertion into the middle of a contiguous array Removal from the middle of a contiguous array ...
... Fixed size Insertion into the middle of a contiguous array Removal from the middle of a contiguous array ...