Lecture Notes- Data Structures
... type arrayName [ arraySize ]; This is called a single-dimensional array. The arraySize must be an integer constant greater than zero and type can be any valid C data type. For example, to declare a 10element array called balance of type double, use this statement − double balance[10]; Here balance i ...
... type arrayName [ arraySize ]; This is called a single-dimensional array. The arraySize must be an integer constant greater than zero and type can be any valid C data type. For example, to declare a 10element array called balance of type double, use this statement − double balance[10]; Here balance i ...
Comparative Study of 2-heap, Skew
... 2-Heap:- 2-heap is almost a Complete Binary Tree. It is called 2-heap because it consists at most two children node and also satisfies the heap property. It is filled on all levels, except last, where filled from left to right. A Heapify operation is performed to form a heap from set of values. Almo ...
... 2-Heap:- 2-heap is almost a Complete Binary Tree. It is called 2-heap because it consists at most two children node and also satisfies the heap property. It is filled on all levels, except last, where filled from left to right. A Heapify operation is performed to form a heap from set of values. Almo ...
11. Linked lists
... can be used to implement bounded sequences. Sequences can also be implemented using linked lists. The two implementations have very different properties, and commonly the application at hand makes one implementation a clear choice over the other. Understanding how to make the choice requires that we ...
... can be used to implement bounded sequences. Sequences can also be implemented using linked lists. The two implementations have very different properties, and commonly the application at hand makes one implementation a clear choice over the other. Understanding how to make the choice requires that we ...
DATA STRUCTURES The term data structure is used to describe the
... The start pointer is an ordinary local pointer variable, so it is drawn separately on theleft top to show that it is in the stack. The list nodes are drawn on the right to showthat they are allocated in the heap. Implementation of Single Linked List: Before writing the code to build the above list, ...
... The start pointer is an ordinary local pointer variable, so it is drawn separately on theleft top to show that it is in the stack. The list nodes are drawn on the right to showthat they are allocated in the heap. Implementation of Single Linked List: Before writing the code to build the above list, ...
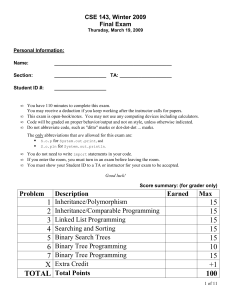
Problem Description Earned Max 1 Inheritance/Polymorphism 2
... For example, tree.nodesAtLevels(4, 5) returns 6 because -8, 80, -2, 57, 1, and 27 are in that range of levels. Your method should throw an IllegalArgumentException if the minimum passed is less than 1 or is greater than the maximum passed. It is legal for the minimum and/or maximum to be larger than ...
... For example, tree.nodesAtLevels(4, 5) returns 6 because -8, 80, -2, 57, 1, and 27 are in that range of levels. Your method should throw an IllegalArgumentException if the minimum passed is less than 1 or is greater than the maximum passed. It is legal for the minimum and/or maximum to be larger than ...
CS 61B Reader Data Structures (Into Java)
... Fair this may be, but it is usually very hard to compute. In this course, therefore, I will say very little about average cases, leaving that to your next course on algorithms. We’ve summarized over inputs by considering worst-case times; now let’s consider how we can summarize over machines. Just a ...
... Fair this may be, but it is usually very hard to compute. In this course, therefore, I will say very little about average cases, leaving that to your next course on algorithms. We’ve summarized over inputs by considering worst-case times; now let’s consider how we can summarize over machines. Just a ...
Chapter 11: Priority Queues and Heaps
... containers the smallest element is always the first value. While the bag does not support direct access to the first element (as does, say, the queue), we can nevertheless obtain access to this value by means of an iterator. This makes it very easy to implement a priority queue using an ordered bag ...
... containers the smallest element is always the first value. While the bag does not support direct access to the first element (as does, say, the queue), we can nevertheless obtain access to this value by means of an iterator. This makes it very easy to implement a priority queue using an ordered bag ...
AN EXAMINATION OF FAST SIMILARITY SEARCH TREES
... points in a coordinate space – a special case of metric spaces – where points can be viewed as vectors. Such spaces satisfy some addition properties that can be exploited in indexing structures. Along with calculating the distance between two vectors other operations include vector addition and subt ...
... points in a coordinate space – a special case of metric spaces – where points can be viewed as vectors. Such spaces satisfy some addition properties that can be exploited in indexing structures. Along with calculating the distance between two vectors other operations include vector addition and subt ...
ABSTRACT The Binary Search Tree serves as an important
... C++ is a zero pointer. A zero pointer is often called a “Null Pointer” but we felt that could cause the reader confusion between “Null Pointer” and “Null Tree”. ...
... C++ is a zero pointer. A zero pointer is often called a “Null Pointer” but we felt that could cause the reader confusion between “Null Pointer” and “Null Tree”. ...
Introduction to Data Structure
... We often speak of "extra" memory needed, not counting the memory needed to store the input itself. Again, we use natural (but fixed-length) units to measure this. ...
... We often speak of "extra" memory needed, not counting the memory needed to store the input itself. Again, we use natural (but fixed-length) units to measure this. ...
Double-Ended Priority Queues
... using the standard array representation of a complete binary tree2 [15]. The correspondence property becomes min[i] ≤ max[i], 1 ≤ i ≤ n/2 . In the min-max pair heaps of [17] and the interval heaps of [16], the two heaps are stored in a single array minmax and we have minmax[i].min being the i’th el ...
... using the standard array representation of a complete binary tree2 [15]. The correspondence property becomes min[i] ≤ max[i], 1 ≤ i ≤ n/2 . In the min-max pair heaps of [17] and the interval heaps of [16], the two heaps are stored in a single array minmax and we have minmax[i].min being the i’th el ...
space-efficient data structures for collections of textual data
... number of users with query latencies in the order of milliseconds. At the same time, a large part of the users’ interactions with the services is logged to be later analyzed; mining large databases of user actions enables discovery of usage patterns that can be used to improve the quality of the ser ...
... number of users with query latencies in the order of milliseconds. At the same time, a large part of the users’ interactions with the services is logged to be later analyzed; mining large databases of user actions enables discovery of usage patterns that can be used to improve the quality of the ser ...
Linked Data Structures Linked lists
... we did in Section 10) or with a linked list. While it is possible to implement a Queue ADT with a dynamic array, the implementation is a bit tricky. Queues are typically implemented with linked lists. The only concern is that an add_back operation is normally O(n). However, if we maintain a pointer ...
... we did in Section 10) or with a linked list. While it is possible to implement a Queue ADT with a dynamic array, the implementation is a bit tricky. Queues are typically implemented with linked lists. The only concern is that an add_back operation is normally O(n). However, if we maintain a pointer ...
The BoND-tree: An Efficient Indexing Method for Box Queries in Non-ordered Discrete Data Spaces, IEEE Transactions on Data and Knowledge Engineering, 2013, Changqing Chen, Alok Watve, Sakti Pramanik, Qiang Zhu
... that work well for similarity queries do not necessarily support box(window) queries efficiently. This is because query conditions for box queries are specified for each dimension separately—any indexed vector which has conflicts with the query condition on any dimension is pruned away immediately f ...
... that work well for similarity queries do not necessarily support box(window) queries efficiently. This is because query conditions for box queries are specified for each dimension separately—any indexed vector which has conflicts with the query condition on any dimension is pruned away immediately f ...
Fully Persistent B-Trees - Department of Computer Science
... for the update complexity. To achieve the result, we first present a new B-Tree implementation that supports searches and updates in O(logB n) I/Os, using O(n/B) blocks of space. Moreover, every update makes in the worst case a constant number of modifications to the data structure. We make these B- ...
... for the update complexity. To achieve the result, we first present a new B-Tree implementation that supports searches and updates in O(logB n) I/Os, using O(n/B) blocks of space. Moreover, every update makes in the worst case a constant number of modifications to the data structure. We make these B- ...
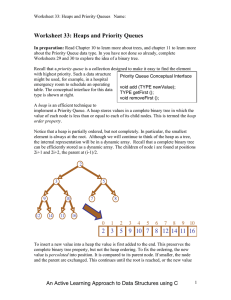
Worksheet 33: Heaps and Priority Queues
... value of each node is less than or equal to each of its child nodes. This is termed the heap order property. Notice that a heap is partially ordered, but not completely. In particular, the smallest element is always at the root. Although we will continue to think of the heap as a tree, the internal ...
... value of each node is less than or equal to each of its child nodes. This is termed the heap order property. Notice that a heap is partially ordered, but not completely. In particular, the smallest element is always at the root. Although we will continue to think of the heap as a tree, the internal ...
Open Data Structures (in C++)
... roughly 16 minutes and 40 seconds. Sixteen minutes is an eon in computer time, but a person might be willing to put up with it (if he or she were headed out for a coffee break). Bigger data sets: Now consider a company like Google, that indexes over 8.5 billion web pages. By our calculations, doing ...
... roughly 16 minutes and 40 seconds. Sixteen minutes is an eon in computer time, but a person might be willing to put up with it (if he or she were headed out for a coffee break). Bigger data sets: Now consider a company like Google, that indexes over 8.5 billion web pages. By our calculations, doing ...
Combining Orthogonal Range Search and Line Simplification Using
... queries as well. This ability to answer stabbing queries is what has been utilized and developed further in the data structure presented here. To solve the line simplification part of the problem, an algorithm presented by Zhilin Li and Stan Openshaw in 1992 was used. This algorithm creates approxim ...
... queries as well. This ability to answer stabbing queries is what has been utilized and developed further in the data structure presented here. To solve the line simplification part of the problem, an algorithm presented by Zhilin Li and Stan Openshaw in 1992 was used. This algorithm creates approxim ...
View
... Allocated memory can be many types: Contiguous memory allocation: Allocation of adjacent memory locations Non-Contiguous memory allocation: Allocation of non adjacent memory locations Heap: Collection of all free memory locations available for allocation De-allocation: Releasing of allocated ...
... Allocated memory can be many types: Contiguous memory allocation: Allocation of adjacent memory locations Non-Contiguous memory allocation: Allocation of non adjacent memory locations Heap: Collection of all free memory locations available for allocation De-allocation: Releasing of allocated ...
Making Data Structures Confluently Persistent
... has been made on the problem of obtaining a general transformation that can make any pointer based data structure confluently persistent. In this paper we get back to DSST’s original question, whether one can find some general transformation that would make any pointer based data structure that allo ...
... has been made on the problem of obtaining a general transformation that can make any pointer based data structure confluently persistent. In this paper we get back to DSST’s original question, whether one can find some general transformation that would make any pointer based data structure that allo ...
DdsLect99
... concern to both designers and users, but such interpretation takes place outside the computer system itself. The computer system itself processes and manipulates symbols representing data values according to fixed rules, without regard to the meanings humans attach to those values or their represent ...
... concern to both designers and users, but such interpretation takes place outside the computer system itself. The computer system itself processes and manipulates symbols representing data values according to fixed rules, without regard to the meanings humans attach to those values or their represent ...
Open Data Structures (in Java)
... roughly 16 minutes and 40 seconds. Sixteen minutes is an eon in computer time, but a person might be willing to put up with it (if he or she were headed out for a coffee break). Bigger data sets: Now consider a company like Google, that indexes over 8.5 billion web pages. By our calculations, doing ...
... roughly 16 minutes and 40 seconds. Sixteen minutes is an eon in computer time, but a person might be willing to put up with it (if he or she were headed out for a coffee break). Bigger data sets: Now consider a company like Google, that indexes over 8.5 billion web pages. By our calculations, doing ...
Screen PDF - Open Data Structures
... roughly 16 minutes and 40 seconds. Sixteen minutes is an eon in computer time, but a person might be willing to put up with it (if he or she were headed out for a coffee break). Bigger data sets: Now consider a company like Google, that indexes over 8.5 billion web pages. By our calculations, doing ...
... roughly 16 minutes and 40 seconds. Sixteen minutes is an eon in computer time, but a person might be willing to put up with it (if he or she were headed out for a coffee break). Bigger data sets: Now consider a company like Google, that indexes over 8.5 billion web pages. By our calculations, doing ...
Deletion Without Rebalancing in Non-Blocking Self
... Studies [26] have also shown that it is common that in real-world applications, keys of data elements in an access sequence are partially sorted (some degree of presortedness) instead of randomly. As an example, when entering student grades of a course into a database, the data are likely to be ente ...
... Studies [26] have also shown that it is common that in real-world applications, keys of data elements in an access sequence are partially sorted (some degree of presortedness) instead of randomly. As an example, when entering student grades of a course into a database, the data are likely to be ente ...
Wavelet Trees for All
... exactly n bits at each level, and at most n bits in the last one. Thus, ndlg σe is an upper bound to the total number of bits it stores. Storing the topology of the tree requires O(σ lg n) further bits, if we are careful enough to use O(lg n) bits for the pointers. This extra space may be a problem ...
... exactly n bits at each level, and at most n bits in the last one. Thus, ndlg σe is an upper bound to the total number of bits it stores. Storing the topology of the tree requires O(σ lg n) further bits, if we are careful enough to use O(lg n) bits for the pointers. This extra space may be a problem ...
Binary tree
In computer science, a binary tree is a tree data structure in which each node has at most two children, which are referred to as the left child and the right child. A recursive definition using just set theory notions is that a (non-empty) binary tree is a triple (L, S, R), where L and R are binary trees or the empty set and S is a singleton set. Some authors allow the binary tree to be the empty set as well.From a graph theory perspective, binary (and K-ary) trees as defined here are actually arborescences. A binary tree may thus be also called a bifurcating arborescence—a term which actually appears in some very old programming books, before the modern computer science terminology prevailed. It is also possible to interpret a binary tree as an undirected, rather than a directed graph, in which case a binary tree is an ordered, rooted tree. Some authors use rooted binary tree instead of binary tree to emphasize the fact that the tree is rooted, but as defined above, a binary tree is always rooted. A binary tree is a special case of an ordered K-ary tree, where k is 2.In computing, binary trees are seldom used solely for their structure. Much more typical is to define a labeling function on the nodes, which associates some value to each node. Binary trees labelled this way are used to implement binary search trees and binary heaps, and are used for efficient searching and sorting. The designation of non-root nodes as left or right child even when there is only one child present matters in some of these applications, in particular it is significant in binary search trees. In mathematics, what is termed binary tree can vary significantly from author to author. Some use the definition commonly used in computer science, but others define it as every non-leaf having exactly two children and don't necessarily order (as left/right) the children either.