A Fully Retroactive Priority Queues
... each non-leaf node x, we store a single partially retroactive priority queue that tracks all updates to the subtree rooted at x. Before continuing, it is important to note that a fully retroactive priority queue can be built from scratch, given k updates, in O(k log k) time. We see later that this p ...
... each non-leaf node x, we store a single partially retroactive priority queue that tracks all updates to the subtree rooted at x. Before continuing, it is important to note that a fully retroactive priority queue can be built from scratch, given k updates, in O(k log k) time. We see later that this p ...
Chapter 15
... (depending on the details of the code), and even if it does, the error message may be quite strange – Look for a missing when a program that uses nodes
with type parameters gets a strange error message or
doesn't run correctly
...
... (depending on the details of the code), and even if it does, the error message may be quite strange – Look for a missing
I n - Virginia Tech
... switch statement: Take complexity of most expensive case. Subroutine call: Complexity of the subroutine. ...
... switch statement: Take complexity of most expensive case. Subroutine call: Complexity of the subroutine. ...
Unit 7 Powerpoint Presentation
... which elements may be deleted at one end called the “TOP” of stack. -- A stack is a last-in-first-out ( LIFO ) structure. -- Insertion operation is referred as “PUSH” and deletion operation is referred as “POP”. -- The most accessible element in the stack is the element at the position “TOP”. -- Sta ...
... which elements may be deleted at one end called the “TOP” of stack. -- A stack is a last-in-first-out ( LIFO ) structure. -- Insertion operation is referred as “PUSH” and deletion operation is referred as “POP”. -- The most accessible element in the stack is the element at the position “TOP”. -- Sta ...
File - MCA Galgotias University
... Traversing a linked list To traverse the list, we need a “walking” pointer, which is a pointer that moves from node to node as each element is processed. We start traversing by setting the walking pointer to the first node in the list. Then, using a loop, we continue until all of the data has been ...
... Traversing a linked list To traverse the list, we need a “walking” pointer, which is a pointer that moves from node to node as each element is processed. We start traversing by setting the walking pointer to the first node in the list. Then, using a loop, we continue until all of the data has been ...
Fully-Functional Succinct Trees
... and a large number of operations on the tree can be supported in constant time under the word-RAM model. However existing data structures are not satisfactory in both theory and practice because (1) the lower-order term is Ω(n log log n/ log n), which cannot be neglected in practice, (2) the hidden ...
... and a large number of operations on the tree can be supported in constant time under the word-RAM model. However existing data structures are not satisfactory in both theory and practice because (1) the lower-order term is Ω(n log log n/ log n), which cannot be neglected in practice, (2) the hidden ...
Suffix Trees and their Applications
... Suffix trees are very useful for many string processing problems. They are data structures that are built up from strings and “really turn” the string “inside out” [GK97]. This way they provide answer to a lot of important questions in linear time (e.g. “Does text contain a word ?” in , the length o ...
... Suffix trees are very useful for many string processing problems. They are data structures that are built up from strings and “really turn” the string “inside out” [GK97]. This way they provide answer to a lot of important questions in linear time (e.g. “Does text contain a word ?” in , the length o ...
Optimal Purely Functional Priority Queues
... in a binomial queue is the root of one of the trees. We can find this minimum element in O(log n) time by scanning through the roots. To insert a new element into a queue, we first create a new singleton tree (i.e., a binomial tree of rank 0). We then step through the existing trees in increasing or ...
... in a binomial queue is the root of one of the trees. We can find this minimum element in O(log n) time by scanning through the roots. To insert a new element into a queue, we first create a new singleton tree (i.e., a binomial tree of rank 0). We then step through the existing trees in increasing or ...
CS3114_09212011 - People
... switch statement: Take complexity of most expensive case. Subroutine call: Complexity of the subroutine. ...
... switch statement: Take complexity of most expensive case. Subroutine call: Complexity of the subroutine. ...
Package `data.tree`
... • "check": if the name conformance should be checked and warnings should be printed in case of non-conformance (the default) • "no-warn": if the name conformance should be checked, but no warnings should be printed in case of non-conformance (if you expect nonconformance) • "no-check" or FALSE: if t ...
... • "check": if the name conformance should be checked and warnings should be printed in case of non-conformance (the default) • "no-warn": if the name conformance should be checked, but no warnings should be printed in case of non-conformance (if you expect nonconformance) • "no-check" or FALSE: if t ...
2004: Gang Qian
... Figure 20: The NSP-tree after splitting old Node 4 and Node 2 ...............................117 Figure 21: The resulting SHTs corresponding to Figure 20......................................117 Figure 22: Benefit of two scans ........................................................................ ...
... Figure 20: The NSP-tree after splitting old Node 4 and Node 2 ...............................117 Figure 21: The resulting SHTs corresponding to Figure 20......................................117 Figure 22: Benefit of two scans ........................................................................ ...
Lab Manual Data Structures (P) COT-213 and IT-215
... give a function to display the current information. The program should give user a choice for inserting a data or to display the current data. Implement the program for Student structures (contains student_name, ...
... give a function to display the current information. The program should give user a choice for inserting a data or to display the current data. Implement the program for Student structures (contains student_name, ...
Optimal Purely Functional Priority Queues
... binary number might result in a long cascade of carries. We can reduce the cost of an insert to at most a single link by borrowing a technique from random-access lists (Okasaki, 1995b). Random-access lists are based on a variant number system, called skew binary numbers (Myers, 1983), in which addin ...
... binary number might result in a long cascade of carries. We can reduce the cost of an insert to at most a single link by borrowing a technique from random-access lists (Okasaki, 1995b). Random-access lists are based on a variant number system, called skew binary numbers (Myers, 1983), in which addin ...
Chapter 17 - University of Arizona
... In a singly linked structure, the instance variable data of each Node refers to an object in memory, which could be of any type. The instance variable next of each Node object references another node containing the next element in the collection. One of these Node objects stores null to mark the end ...
... In a singly linked structure, the instance variable data of each Node refers to an object in memory, which could be of any type. The instance variable next of each Node object references another node containing the next element in the collection. One of these Node objects stores null to mark the end ...
17 - Arizona Computer Science
... In a singly linked structure, the instance variable data of each Node refers to an object in memory, which could be of any type. The instance variable next of each Node object references another node containing the next element in the collection. One of these Node objects stores null to mark the end ...
... In a singly linked structure, the instance variable data of each Node refers to an object in memory, which could be of any type. The instance variable next of each Node object references another node containing the next element in the collection. One of these Node objects stores null to mark the end ...
I n - Virginia Tech
... switch statement: Take complexity of most expensive case. Subroutine call: Complexity of the subroutine. ...
... switch statement: Take complexity of most expensive case. Subroutine call: Complexity of the subroutine. ...
recdata
... Show (ipl BT) = sum of the lengths of the paths from the root to all nodes in the tree. Prove by structural induction Base case. 0 is needed to get the proper value for a tree with a single node. Assume (ipl (left BT)) and (ipl (right BT)) compute the sum of the lengths of paths in the left an ...
... Show (ipl BT) = sum of the lengths of the paths from the root to all nodes in the tree. Prove by structural induction Base case. 0 is needed to get the proper value for a tree with a single node. Assume (ipl (left BT)) and (ipl (right BT)) compute the sum of the lengths of paths in the left an ...
Data Structures Through C - MLR Institute of Technology
... 5. The record of observations along with the detailed experimental Algorithm of the experiment in the immediate last session should be submitted and certified staff member in-charge 6. Not more than 3 students in a group are permitted to perform the experiment on the set. 7. The group-wise division ...
... 5. The record of observations along with the detailed experimental Algorithm of the experiment in the immediate last session should be submitted and certified staff member in-charge 6. Not more than 3 students in a group are permitted to perform the experiment on the set. 7. The group-wise division ...
The Skip Quadtree: A Simple Dynamic Data Structure for
... in a quadtree, as well as update and range query operations, involve finding the most significant binary digit at which two coordinates of two points differ. This can be done in O(1) machine instructions if we have a most-significant-bit instruction, or by using floating-point or extended-precision ...
... in a quadtree, as well as update and range query operations, involve finding the most significant binary digit at which two coordinates of two points differ. This can be done in O(1) machine instructions if we have a most-significant-bit instruction, or by using floating-point or extended-precision ...
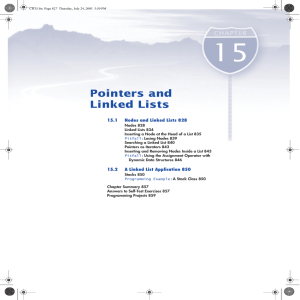
Pointers and Linked Lists
... The expression on the left side of the assignment operator may require a bit of explanation. The variable head is a pointer variable. So, the expression *head is the thing it points to, namely the node (dynamic variable) containing "rolls" and the integer 10. This node, referred to by *head, is a st ...
... The expression on the left side of the assignment operator may require a bit of explanation. The variable head is a pointer variable. So, the expression *head is the thing it points to, namely the node (dynamic variable) containing "rolls" and the integer 10. This node, referred to by *head, is a st ...
Data Structures Analysis
... dictionary operations (find, insert, delete). Remember: - binary search trees (BST) - AVL (balanced BST) ...
... dictionary operations (find, insert, delete). Remember: - binary search trees (BST) - AVL (balanced BST) ...
Abstract Efficient Data Structures for Tamper-Evident Logging
... tree and the semantics for tamper-evident logging are applicable to this alternative threat model with only minor changes. Under the semantics of forward-integrity, membership auditing just-added events is unnecessary because tamper-evidence only applies to events occurring before the Byzantine fai ...
... tree and the semantics for tamper-evident logging are applicable to this alternative threat model with only minor changes. Under the semantics of forward-integrity, membership auditing just-added events is unnecessary because tamper-evidence only applies to events occurring before the Byzantine fai ...
I/O-efficient Point Location using Persistent B
... Any vertical line l in the plane introduces an “above-below” order on the segments it intersects. We will “sweep” the plane from left to right with a vertical line Our “critical” x-axis points are the endpoints of all segments Michal Balas ...
... Any vertical line l in the plane introduces an “above-below” order on the segments it intersects. We will “sweep” the plane from left to right with a vertical line Our “critical” x-axis points are the endpoints of all segments Michal Balas ...
Eindhoven University of Technology MASTER An experimental
... Spatial data management is required in several areas such as computer aided design (CAD), VLSI design, geo-data applications etc. Data objects in such a spatial database are multi-dimensional (typically 2D or 3D). It is important to be able to search and retrieve objects using their spatial position ...
... Spatial data management is required in several areas such as computer aided design (CAD), VLSI design, geo-data applications etc. Data objects in such a spatial database are multi-dimensional (typically 2D or 3D). It is important to be able to search and retrieve objects using their spatial position ...
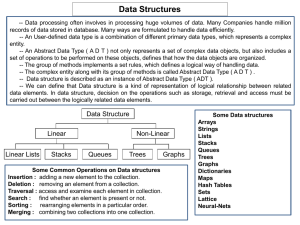
Data structure - IndiaStudyChannel.com
... Data structure In computer science, a data structure is a way of storing data in a computer so that it can be used efficiently. Often a carefully chosen data structure will allow the most efficient algorithm to be used. The choice of the data structure often begins from the choice of an abstract dat ...
... Data structure In computer science, a data structure is a way of storing data in a computer so that it can be used efficiently. Often a carefully chosen data structure will allow the most efficient algorithm to be used. The choice of the data structure often begins from the choice of an abstract dat ...
Binary tree
In computer science, a binary tree is a tree data structure in which each node has at most two children, which are referred to as the left child and the right child. A recursive definition using just set theory notions is that a (non-empty) binary tree is a triple (L, S, R), where L and R are binary trees or the empty set and S is a singleton set. Some authors allow the binary tree to be the empty set as well.From a graph theory perspective, binary (and K-ary) trees as defined here are actually arborescences. A binary tree may thus be also called a bifurcating arborescence—a term which actually appears in some very old programming books, before the modern computer science terminology prevailed. It is also possible to interpret a binary tree as an undirected, rather than a directed graph, in which case a binary tree is an ordered, rooted tree. Some authors use rooted binary tree instead of binary tree to emphasize the fact that the tree is rooted, but as defined above, a binary tree is always rooted. A binary tree is a special case of an ordered K-ary tree, where k is 2.In computing, binary trees are seldom used solely for their structure. Much more typical is to define a labeling function on the nodes, which associates some value to each node. Binary trees labelled this way are used to implement binary search trees and binary heaps, and are used for efficient searching and sorting. The designation of non-root nodes as left or right child even when there is only one child present matters in some of these applications, in particular it is significant in binary search trees. In mathematics, what is termed binary tree can vary significantly from author to author. Some use the definition commonly used in computer science, but others define it as every non-leaf having exactly two children and don't necessarily order (as left/right) the children either.