Part I: Introduction
... Streaming from Web server (2) Alternative: set up connection between server and player Web browser requests and receives a meta file (a file describing the object) instead of receiving the file itself; Content-type header indicates specific audio/video application Browser launches media playe ...
... Streaming from Web server (2) Alternative: set up connection between server and player Web browser requests and receives a meta file (a file describing the object) instead of receiving the file itself; Content-type header indicates specific audio/video application Browser launches media playe ...
Selling an Idea or a Product
... Epoch # – uniquely identifies which set of sequence numbers are being used. ...
... Epoch # – uniquely identifies which set of sequence numbers are being used. ...
ppt - Pacific University
... • therefore, other chat clients can implement it – AOL used to change the protocol very often to frustrate the efforts of those trying to build an AIM chat client – Microsoft never fully disclosed the protocol for MSN Messenger – Why would a company do this? ...
... • therefore, other chat clients can implement it – AOL used to change the protocol very often to frustrate the efforts of those trying to build an AIM chat client – Microsoft never fully disclosed the protocol for MSN Messenger – Why would a company do this? ...
Deep Packet Inspection - Computer Science and Engineering
... A class of packet processing applications need to inspect packets deeper than the protocol headers and analyze its payload – Network Security – HTTP load balancing – XML processing – Content-based billing and forwarding ...
... A class of packet processing applications need to inspect packets deeper than the protocol headers and analyze its payload – Network Security – HTTP load balancing – XML processing – Content-based billing and forwarding ...
Chapter-8 - Keep in Touch with Sanjeev Maharjan
... If one of the fragments gets lost, the complete datagram is considered lost. It is possible that fragments of the same IP datagram reach the destination host via multiple routes. Finally, Since they may pass through networks with a smaller MTU than the sender’s one, they are subject to further ...
... If one of the fragments gets lost, the complete datagram is considered lost. It is possible that fragments of the same IP datagram reach the destination host via multiple routes. Finally, Since they may pass through networks with a smaller MTU than the sender’s one, they are subject to further ...
Wireless Networks
... Set up home networks so that a couch potato can remotely monitor air-conditioning, the oven, and children’s Internet surfing Call home from a remote location to turn appliances on and off, set the alarm, and monitor activity ...
... Set up home networks so that a couch potato can remotely monitor air-conditioning, the oven, and children’s Internet surfing Call home from a remote location to turn appliances on and off, set the alarm, and monitor activity ...
Revision Lecture Distributed Computing systems
... • Necessary in non-broadcast networks (cf Internet) : Hop by Hop • Distance-vector algorithm for each node – stores table of state & cost information of links, cost infinity for faulty links – determines route taken by packet (the next hop) – periodically updates the table and sends to neighbors – m ...
... • Necessary in non-broadcast networks (cf Internet) : Hop by Hop • Distance-vector algorithm for each node – stores table of state & cost information of links, cost infinity for faulty links – determines route taken by packet (the next hop) – periodically updates the table and sends to neighbors – m ...
Chapter 4: Communication
... exchange discrete messages • Streaming: one-way communication; a “session” consists of multiple messages from the sender that are related either by send order, temporal proximity, etc. ...
... exchange discrete messages • Streaming: one-way communication; a “session” consists of multiple messages from the sender that are related either by send order, temporal proximity, etc. ...
ppt - People @EECS
... source user dest user (Call it UDP/IP) IP Header (20 bytes) 16-bit source port 16-bit UDP length ...
... source user dest user (Call it UDP/IP) IP Header (20 bytes) 16-bit source port 16-bit UDP length ...
final examination - School of Computer Science
... cs.uwindsor.ca/60-367/image01.jpeg) can be sent over the same persistent connection. A) True B) False ...
... cs.uwindsor.ca/60-367/image01.jpeg) can be sent over the same persistent connection. A) True B) False ...
Napster & Gnutella
... • Peers respond with a “QueryHit” (contains contact info) • File transfers use direct connection using HTTP protocol’s GET method • When there is a firewall a "Push" packet is used – reroutes via Push path ...
... • Peers respond with a “QueryHit” (contains contact info) • File transfers use direct connection using HTTP protocol’s GET method • When there is a firewall a "Push" packet is used – reroutes via Push path ...
Guide to Firewalls and Network Security with Intrusion Detection and
... such as port, IP address, and protocol Review the header, strip it off, and replace it with a new header before sending it to a specific location within the network Fundamental components of firewalls ...
... such as port, IP address, and protocol Review the header, strip it off, and replace it with a new header before sending it to a specific location within the network Fundamental components of firewalls ...
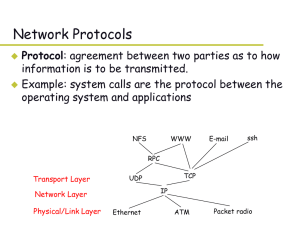
No Slide Title - comp
... – User Datagram Protocol (UDP): Mainly provide a demultiplexing service. – Transmission Control Protocol (TCP): Provide a reliable byte-stream service – Remote Procedure Call (RPC): Provide services to transaction-based applications. – Real Time Protocol (RTP): Provide services for transporting real ...
... – User Datagram Protocol (UDP): Mainly provide a demultiplexing service. – Transmission Control Protocol (TCP): Provide a reliable byte-stream service – Remote Procedure Call (RPC): Provide services to transaction-based applications. – Real Time Protocol (RTP): Provide services for transporting real ...
Presentation16
... receiver ~ network addressing • Sending data not a non-existent node could be sending to any one of thousands (on a large network) of potential receiver nodes all nodes must have a unique identifier, generally known as a network address – analogous to a telephone number all nodes must also hav ...
... receiver ~ network addressing • Sending data not a non-existent node could be sending to any one of thousands (on a large network) of potential receiver nodes all nodes must have a unique identifier, generally known as a network address – analogous to a telephone number all nodes must also hav ...
Presentation (powerpoint) - The DBAbstract Server Project
... - Provide 2-way decryption / encryption of clientserver connection - Spawn a Server Thread for every accepted connection The Server Worker Thread - Check if loop conditions are encountered - Find the Right Adapter to serve the specific Client - Interrogate the found Adapter with Client’s queries - C ...
... - Provide 2-way decryption / encryption of clientserver connection - Spawn a Server Thread for every accepted connection The Server Worker Thread - Check if loop conditions are encountered - Find the Right Adapter to serve the specific Client - Interrogate the found Adapter with Client’s queries - C ...
3rd Edition: Chapter 2
... conceptual and implementation aspects of network application protocols transport-layer service models client-server paradigm peer-to-peer paradigm ...
... conceptual and implementation aspects of network application protocols transport-layer service models client-server paradigm peer-to-peer paradigm ...
Ping, traceroute, etc.
... a packet from your computer (the local host) to some other host on the network – It doesn’t actually follow a single packet but sends out a series of packets – The packets are restricted in the number of “hops” they can take • It is limited by the time-to-live (TTL) field ...
... a packet from your computer (the local host) to some other host on the network – It doesn’t actually follow a single packet but sends out a series of packets – The packets are restricted in the number of “hops” they can take • It is limited by the time-to-live (TTL) field ...
CAS: Central Authentication Service
... – reliable stream (circuit) transmission in 2 directions – most things we think of as "Internet" use TCP ...
... – reliable stream (circuit) transmission in 2 directions – most things we think of as "Internet" use TCP ...
20060208-highspipv6-ricciulli
... Extract from header a set of offset pointers into the packet starting from the first Internet Protocol (IP) byte The following offsets are memorized for each packet – Header start V6 – Header start V4 – High-Level Protocol (HLP) start – Payload Start – Hop-by-Hop – Routing – Fragment – Destination – ...
... Extract from header a set of offset pointers into the packet starting from the first Internet Protocol (IP) byte The following offsets are memorized for each packet – Header start V6 – Header start V4 – High-Level Protocol (HLP) start – Payload Start – Hop-by-Hop – Routing – Fragment – Destination – ...
Computer Network Unit-V
... Checksum: An optional 16-bit checksum computed over the entire UDP datagram plus a special “pseudo header” of fields. See below for more information. ...
... Checksum: An optional 16-bit checksum computed over the entire UDP datagram plus a special “pseudo header” of fields. See below for more information. ...
Remote Access
... • Two common types of VPNs include: – Remote-access VPN or virtual private dial-up network (VPDN): user-to-LAN connection used by remote users – Site-to-site VPN: multiple sites can connect to other sites over the Internet ...
... • Two common types of VPNs include: – Remote-access VPN or virtual private dial-up network (VPDN): user-to-LAN connection used by remote users – Site-to-site VPN: multiple sites can connect to other sites over the Internet ...
Chapter 8 Internet Protocols
... —No unnecessary overhead for connection setup —Can work with different network types • does not demand too much services from the actual network ...
... —No unnecessary overhead for connection setup —Can work with different network types • does not demand too much services from the actual network ...
Apple Darwin Streaming Server
... Real-time Real-time streaming works with: a streaming media server a client media player a Real-Time Streaming Protocol (RTSP) No file is ever downloaded Media is played by the client software as it is delivered ...
... Real-time Real-time streaming works with: a streaming media server a client media player a Real-Time Streaming Protocol (RTSP) No file is ever downloaded Media is played by the client software as it is delivered ...
Computer Networks (COMP2322) Assignment Four (95 marks in
... checksum (for both IP and TCP) can detect the errors with probability pIP. The error detection events are mutually independent. Compute the probability that the errors can be detected for scenarios (a) and (b). 4. [20 marks] The figure below shows a Wireshark trace of a web session: from a client wi ...
... checksum (for both IP and TCP) can detect the errors with probability pIP. The error detection events are mutually independent. Compute the probability that the errors can be detected for scenarios (a) and (b). 4. [20 marks] The figure below shows a Wireshark trace of a web session: from a client wi ...