WE-P1 Custom HMI for Commercial SCADA
... form. Every active image has property that contains the name of the coupled variable in RTDB. At final step Application Builder compiles GUI and custom library into the HMI application. At start up HMI connects to the RTDB and reads coupling information from widgets to link them to the RTDB in its m ...
... form. Every active image has property that contains the name of the coupled variable in RTDB. At final step Application Builder compiles GUI and custom library into the HMI application. At start up HMI connects to the RTDB and reads coupling information from widgets to link them to the RTDB in its m ...
Authentication Key - Pravin Shetty > Resume
... developed by Netscape to provide: Data Privacy through Encryption. Validate a peer's identify through Authentication and Certificates Assure message integrity through a Message Authentication Code (MAC). SSL, in practice, is only widely implemented in the Hypertext Transport Transfer Protocol ( ...
... developed by Netscape to provide: Data Privacy through Encryption. Validate a peer's identify through Authentication and Certificates Assure message integrity through a Message Authentication Code (MAC). SSL, in practice, is only widely implemented in the Hypertext Transport Transfer Protocol ( ...
2 DEvelopment tools
... form. Every active image has property that contains the name of the coupled variable in RTDB. At final step Application Builder compiles GUI and custom library into the HMI application. At start up HMI connects to the RTDB and reads coupling information from widgets to link them to the RTDB in its m ...
... form. Every active image has property that contains the name of the coupled variable in RTDB. At final step Application Builder compiles GUI and custom library into the HMI application. At start up HMI connects to the RTDB and reads coupling information from widgets to link them to the RTDB in its m ...
Local Area Networks; Ethernet
... • unreliable connectionless packet delivery service – every packet has 20-40B header with source & destination addresses, time to live: maximum number of hops before packet is discarded (each gateway decreases this by 1) checksum of header information (not of data itself) ...
... • unreliable connectionless packet delivery service – every packet has 20-40B header with source & destination addresses, time to live: maximum number of hops before packet is discarded (each gateway decreases this by 1) checksum of header information (not of data itself) ...
VSI-E Protocol Fundamentals
... Data Payload • Channel-stream encapsulated into an integer number of 32bit words in format. • DIM input => 32 individual bit streams • A subset of 2n is chosen to be ‘active bit streams’. • The ‘active bit streams’ are further subdivided into some number of mutually exclusive channels • each sample ...
... Data Payload • Channel-stream encapsulated into an integer number of 32bit words in format. • DIM input => 32 individual bit streams • A subset of 2n is chosen to be ‘active bit streams’. • The ‘active bit streams’ are further subdivided into some number of mutually exclusive channels • each sample ...
Chp. 6 - Cisco Networking Academy
... The HTTP protocol is not a secure protocol; information could easily be intercepted by other users as it is sent over the network. In order to provide security for the data, HTTP can be used with secure transport protocols. Requests for secure HTTP (https) are sent to port 443. These requests ...
... The HTTP protocol is not a secure protocol; information could easily be intercepted by other users as it is sent over the network. In order to provide security for the data, HTTP can be used with secure transport protocols. Requests for secure HTTP (https) are sent to port 443. These requests ...
CCNA2 - MTEE Server
... routing path or too many hops, the packet will eventually exceed the maximum hop count This is also known as reaching its time-to-live (TTL), because the TTL value typically matches the maximum hop count defined by the routing protocol M.Menelaou ...
... routing path or too many hops, the packet will eventually exceed the maximum hop count This is also known as reaching its time-to-live (TTL), because the TTL value typically matches the maximum hop count defined by the routing protocol M.Menelaou ...
Hour 4
... IP Options— This field supports a number of optional header settings primarily used for testing, debugging, and security. Options include Strict Source Route (a specific path router path that the datagram should follow), Internet Timestamp (a record of timestamps at each router), and security restri ...
... IP Options— This field supports a number of optional header settings primarily used for testing, debugging, and security. Options include Strict Source Route (a specific path router path that the datagram should follow), Internet Timestamp (a record of timestamps at each router), and security restri ...
A(t)
... Packet length, P, is the length of a packet in bits. Link length, L, is the length of a link in meters. Data rate, R, is the rate at which bits can be sent, in bits/second, or b/s.1 Propagation delay, PROP, is the time for one bit to travel along a link of length, L. PROP = L/c. Transmission time, T ...
... Packet length, P, is the length of a packet in bits. Link length, L, is the length of a link in meters. Data rate, R, is the rate at which bits can be sent, in bits/second, or b/s.1 Propagation delay, PROP, is the time for one bit to travel along a link of length, L. PROP = L/c. Transmission time, T ...
Ethernet manual (word document)
... VMX RS232 control guide for details on the RS232 control words. VMX uses a standard telnet style interface. The data contained in any incoming packet will be converted to RS232 commands. All RS232 feedback will be returned via another TCP packet. ...
... VMX RS232 control guide for details on the RS232 control words. VMX uses a standard telnet style interface. The data contained in any incoming packet will be converted to RS232 commands. All RS232 feedback will be returned via another TCP packet. ...
Example # 1
... An organization that is granted a large block of addresses may want to create clusters of networks (called subnets) and divide the addresses between the different subnets. As an example, suppose an organization is given the block 17.12.40.0/26, which contains 64 addresses. The organization has three ...
... An organization that is granted a large block of addresses may want to create clusters of networks (called subnets) and divide the addresses between the different subnets. As an example, suppose an organization is given the block 17.12.40.0/26, which contains 64 addresses. The organization has three ...
Thailand
... Private AS number assigned by WMO secretariat. The AS numbers for neighbour centres are: Bangkok RTH : AS 64769 Tokyo RTH : AS 64520 Kuala Lumpur NMC : AS 65154 Vientiane NMC : AS 64771 ...
... Private AS number assigned by WMO secretariat. The AS numbers for neighbour centres are: Bangkok RTH : AS 64769 Tokyo RTH : AS 64520 Kuala Lumpur NMC : AS 65154 Vientiane NMC : AS 64771 ...
Hijacking, Denial of Service, and Intrusion Detection
... Advertised Window Checksum Urgent Pointer Options ...
... Advertised Window Checksum Urgent Pointer Options ...
M*N - UCL Computer Science
... Avatars controlled by users and kept the newest information in the workstation ...
... Avatars controlled by users and kept the newest information in the workstation ...
On the Stability of the Information Carried by Traffic Flow
... monitoring the New Zealand Internet Exchange (NZIX) in July 2000 [15, 14]. These traces also include only the header bytes, while the application payload is fully removed. The header traces were captured using a DAG3.2E with a GPS synchronized mechanism at the New Zealand Internet Exchange, which se ...
... monitoring the New Zealand Internet Exchange (NZIX) in July 2000 [15, 14]. These traces also include only the header bytes, while the application payload is fully removed. The header traces were captured using a DAG3.2E with a GPS synchronized mechanism at the New Zealand Internet Exchange, which se ...
ppt
... Persistent HTTP • server leaves connection open after sending response • subsequent HTTP messages between same client/server are sent over connection ...
... Persistent HTTP • server leaves connection open after sending response • subsequent HTTP messages between same client/server are sent over connection ...
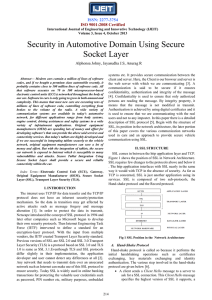
Security in Automotive Domain Using Secure Socket Layer
... 1.0 is same as SSL 3.1.Eventhough TLS and SSL protocols differ slightly in their implementation, the application developer and user cannot detect any differences at all [2]. Any network that needs to transmit data over an unsecured network such as Internet can make use of this SSL protocol to ensure ...
... 1.0 is same as SSL 3.1.Eventhough TLS and SSL protocols differ slightly in their implementation, the application developer and user cannot detect any differences at all [2]. Any network that needs to transmit data over an unsecured network such as Internet can make use of this SSL protocol to ensure ...
lesson19
... Sixteen Rx-descriptors (32-bytes each) Sixty-four receive-buffers (1024-bytes each) ...
... Sixteen Rx-descriptors (32-bytes each) Sixty-four receive-buffers (1024-bytes each) ...
IOSR Journal of Computer Engineering (IOSR-JCE)
... scenario presented in a graph that detailed the activity throughout the simulation. Graph 8 illustrates the Utilization of the server's CPU in the three scenarios. The graph shows that the CPU utilization becomes very high after applying the IPSec due to Encapsulating security payload. Utilization d ...
... scenario presented in a graph that detailed the activity throughout the simulation. Graph 8 illustrates the Utilization of the server's CPU in the three scenarios. The graph shows that the CPU utilization becomes very high after applying the IPSec due to Encapsulating security payload. Utilization d ...
Review for Quiz-1 - Communications Systems Center (CSC)
... • requires 2 RTTs per object • OS overhead for each TCP connection • browsers often open parallel TCP connections to fetch referenced objects Persistent HTTP • server leaves connection open after sending response • subsequent HTTP messages between same client/server sent over open connection ...
... • requires 2 RTTs per object • OS overhead for each TCP connection • browsers often open parallel TCP connections to fetch referenced objects Persistent HTTP • server leaves connection open after sending response • subsequent HTTP messages between same client/server sent over open connection ...
Review for midterm
... Persistent HTTP • server leaves connection open after sending response • subsequent HTTP messages between same client/server are sent over connection ...
... Persistent HTTP • server leaves connection open after sending response • subsequent HTTP messages between same client/server are sent over connection ...
Introduction to networking, protocol layers, TCP/IP protocol suite
... sends control information between the hosts routers generate most of this information inform hosts that a packet could not be delivered because of an error or a better route exists to a particular destination ...
... sends control information between the hosts routers generate most of this information inform hosts that a packet could not be delivered because of an error or a better route exists to a particular destination ...