Model FVL328 ProSafe High-Speed VPN Firewall Reference
... make changes to the products described in this document without notice. NETGEAR does not assume any liability that may occur due to the use or application of the product(s) or circuit layout(s) described herein. ...
... make changes to the products described in this document without notice. NETGEAR does not assume any liability that may occur due to the use or application of the product(s) or circuit layout(s) described herein. ...
CN 2015 1-2 - DSpace
... 1.Resource sharing.---- May be Software of Hardware 2.High reliability.---Alternative Sources of data Important in banks, military, Air traffic control ...
... 1.Resource sharing.---- May be Software of Hardware 2.High reliability.---Alternative Sources of data Important in banks, military, Air traffic control ...
PDF
... Hop count is 2 10.5.5.3 (GigabitEthernet3/0), from 10.5.5.3, Send flag is 0x0 Composite metric is (28672/28416), Route is Internal Vector metric: Minimum bandwidth is 100000 Kbit Total delay is 120 microseconds Reliability is 255/255 Load is 1/255 Minimum MTU is 1500 Hop count is 2 Router 1 will not ...
... Hop count is 2 10.5.5.3 (GigabitEthernet3/0), from 10.5.5.3, Send flag is 0x0 Composite metric is (28672/28416), Route is Internal Vector metric: Minimum bandwidth is 100000 Kbit Total delay is 120 microseconds Reliability is 255/255 Load is 1/255 Minimum MTU is 1500 Hop count is 2 Router 1 will not ...
Basic Network Security - Kenneth M. Chipps Ph.D. Home Page
... 1000) to a targeted server • The server replies with the usual SYNACK response, but the malicious host never responds with the final ACK to complete the handshake • This ties up the server until it eventually runs out of resources and cannot respond to a valid host request ...
... 1000) to a targeted server • The server replies with the usual SYNACK response, but the malicious host never responds with the final ACK to complete the handshake • This ties up the server until it eventually runs out of resources and cannot respond to a valid host request ...
IPv4/IPv6 Translation: Framework
... addresses are maintained in the translator as the IPv4 address pool. – In the stateless mode, there is no IPv4 address pool in the translator. A special block of IPv4 addresses are reserved, embedded in the IPv6 addresses and represented by the IPv6 end systems. ...
... addresses are maintained in the translator as the IPv4 address pool. – In the stateless mode, there is no IPv4 address pool in the translator. A special block of IPv4 addresses are reserved, embedded in the IPv6 addresses and represented by the IPv6 end systems. ...
www.uettaxila.edu.pk
... This is even truer for developing countries and rural areas for which the cost/profitability and the demand factors are essential. This obviously includes adequate coverage, reliability, performances (throughput), capacity and applications. ...
... This is even truer for developing countries and rural areas for which the cost/profitability and the demand factors are essential. This obviously includes adequate coverage, reliability, performances (throughput), capacity and applications. ...
Cisco 827 Router Cabling and Setup Quick Start Guide
... If you have a Cisco 827-4V router, you can connect an analog telephone or fax machine to your router. Use the cables provided with these devices. The gray PHONE 4, 3, 2, and 1 ports are RJ-11 connectors. If you are outside of North America, you must buy and attach adapters that allow your telephones ...
... If you have a Cisco 827-4V router, you can connect an analog telephone or fax machine to your router. Use the cables provided with these devices. The gray PHONE 4, 3, 2, and 1 ports are RJ-11 connectors. If you are outside of North America, you must buy and attach adapters that allow your telephones ...
information
... “ An assault on system security that derives from an intelligent threat, i.e., an intelligent act that is a deliberate attempt (especially in the sense of a method or technique) to evade security services and violate the security policy of the system.” ...
... “ An assault on system security that derives from an intelligent threat, i.e., an intelligent act that is a deliberate attempt (especially in the sense of a method or technique) to evade security services and violate the security policy of the system.” ...
Offset Time-Emulated Architecture for Optical Burst Switching - Modelling and Performance Evaluation
... The evolution of the transport networking is driven by continuously increasing traffic demand due to the introduction of broadband Internet access and new end-user business applications as well as the continuing paradigm shift from voice to data services. These trends have emerged at the same time a ...
... The evolution of the transport networking is driven by continuously increasing traffic demand due to the introduction of broadband Internet access and new end-user business applications as well as the continuing paradigm shift from voice to data services. These trends have emerged at the same time a ...
Re-architecting Congestion Control for Consistent High Performance
... degrades severely. For example, TCP Illinois [38] uses both loss and delay to form an event-control mapping, but its throughput collapses with even a small amount of random loss, or when network conditions are dynamic (§4). More examples are in §5. Most unfortunately, if some control actions are ind ...
... degrades severely. For example, TCP Illinois [38] uses both loss and delay to form an event-control mapping, but its throughput collapses with even a small amount of random loss, or when network conditions are dynamic (§4). More examples are in §5. Most unfortunately, if some control actions are ind ...
JNCIA Study Guide - Open Shortest Path First (OSPF)
... Once a link-state router begins operating on a network link, information associated with that logical network is added to its local link-state database. The local router then sends Hello messages on its operational links to determine whether other link-state routers are operating on the interfaces a ...
... Once a link-state router begins operating on a network link, information associated with that logical network is added to its local link-state database. The local router then sends Hello messages on its operational links to determine whether other link-state routers are operating on the interfaces a ...
Data Link Layer Switching
... Bridge must not segment frames that are too large Frames that are too long are dropped Implies a loss of transparency Special case 802.6 – DQDB transmits each frame in several cells ...
... Bridge must not segment frames that are too large Frames that are too long are dropped Implies a loss of transparency Special case 802.6 – DQDB transmits each frame in several cells ...
Introducing TCP/IP
... – When TCP/IP is configured on the client computer, the Obtain an IP address automatically option button is the only necessary set-up element. Everything is automatic – The next time the workstation attempts to access the network (older versions of Windows must be rebooted first), it broadcasts a DH ...
... – When TCP/IP is configured on the client computer, the Obtain an IP address automatically option button is the only necessary set-up element. Everything is automatic – The next time the workstation attempts to access the network (older versions of Windows must be rebooted first), it broadcasts a DH ...
Feature Description
... known as streams, from each of the transmit antennas that results in the space dimension being reused, or multiplexed. If the transmitter is equipped with Ntx antennas and the receiver has Nrx ...
... known as streams, from each of the transmit antennas that results in the space dimension being reused, or multiplexed. If the transmitter is equipped with Ntx antennas and the receiver has Nrx ...
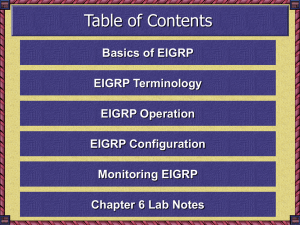
Chapter 8: Advanced Routing Protocols
... EIGRP Components (continued) • Reliable Transport Protocol (RTP) – Because EIGRP is protocol-independent, it cannot use existing Transport layer protocols to carry its various packet types – Instead, Cisco developed an entirely new layer 4 protocol – RTP can actually provide both reliable and unrel ...
... EIGRP Components (continued) • Reliable Transport Protocol (RTP) – Because EIGRP is protocol-independent, it cannot use existing Transport layer protocols to carry its various packet types – Instead, Cisco developed an entirely new layer 4 protocol – RTP can actually provide both reliable and unrel ...
Title Subtitle - Aalborg Universitet
... — one in each or single label in combined field, negotiated by LDP • Further fields in stack are encoded with ‘shim’ header in PPP/LAN format — must be at least one, with bottom label distinguished with ‘explicit NULL’ • TTL is carried in top label in stack, as a proxy for ATM header (that lacks TTL ...
... — one in each or single label in combined field, negotiated by LDP • Further fields in stack are encoded with ‘shim’ header in PPP/LAN format — must be at least one, with bottom label distinguished with ‘explicit NULL’ • TTL is carried in top label in stack, as a proxy for ATM header (that lacks TTL ...
Simple Network Management Protocol (SNMP) Primer
... and getNextRequest commands with the Read-Only community name. Read-Write: A Read-Write setting allows the value of the MIB object to be accessed as well as modified. A client can issue the setRequest command as well as the getRequest and getNextRequest. If one tries to access an SNMP Agent with the ...
... and getNextRequest commands with the Read-Only community name. Read-Write: A Read-Write setting allows the value of the MIB object to be accessed as well as modified. A client can issue the setRequest command as well as the getRequest and getNextRequest. If one tries to access an SNMP Agent with the ...
Handbuch – Sunrise Internet Box
... This user manual is dedicated to the Sunrise Internet Box product. This equipment is a gateway which gives users broadband Internet access from their computer, tablet, smartphone or game console by various Ethernet (10, 100 or 1000 BASE-T) or Wi-Fi (IEEE 802.11n or 802.11ac) interfaces via an ADSL/A ...
... This user manual is dedicated to the Sunrise Internet Box product. This equipment is a gateway which gives users broadband Internet access from their computer, tablet, smartphone or game console by various Ethernet (10, 100 or 1000 BASE-T) or Wi-Fi (IEEE 802.11n or 802.11ac) interfaces via an ADSL/A ...
Proceedings of the FREENIX Track: 2002 USENIX Annual Technical Conference
... that has gained popularity in the last years. The Linux source code is publicly available1 , which makes Linux an attractive tool for the computer science researchers in various research areas. Therefore, a large number of people have contributed to Linux development during its lifetime. However, ma ...
... that has gained popularity in the last years. The Linux source code is publicly available1 , which makes Linux an attractive tool for the computer science researchers in various research areas. Therefore, a large number of people have contributed to Linux development during its lifetime. However, ma ...
Congestion Control in Linux TCP
... that has gained popularity in the last years. The Linux source code is publicly available1 , which makes Linux an attractive tool for the computer science researchers in various research areas. Therefore, a large number of people have contributed to Linux development during its lifetime. However, ma ...
... that has gained popularity in the last years. The Linux source code is publicly available1 , which makes Linux an attractive tool for the computer science researchers in various research areas. Therefore, a large number of people have contributed to Linux development during its lifetime. However, ma ...
MinBD: Minimally-Buffered Deflection Routing for Energy
... stage consists of two-input blocks arranged into two stages of two blocks each. This arrangement can send a flit on any input to any output. (Note that it cannot perform all possible permutations of inputs to outputs, but as we will see, it is sufficient for correct operation that at least one flit ...
... stage consists of two-input blocks arranged into two stages of two blocks each. This arrangement can send a flit on any input to any output. (Note that it cannot perform all possible permutations of inputs to outputs, but as we will see, it is sufficient for correct operation that at least one flit ...
HLP: A Next Generation Inter
... generates many updates. • This is misleading because they do not point out that BGP can send many prefix route changes within a single update, even if it does touch many ASs. – The importance of isolation is being exaggerated. ...
... generates many updates. • This is misleading because they do not point out that BGP can send many prefix route changes within a single update, even if it does touch many ASs. – The importance of isolation is being exaggerated. ...
wireless mesh networks
... If a probing node embeds the information of nw from all its neighbors to the probe packet Then each of its neighbors can derive the packet delivery ratio from the neighbor to the probing node With the delivery ratio at both forward and reverse directions, denoted by df and dr, respectively, ET ...
... If a probing node embeds the information of nw from all its neighbors to the probe packet Then each of its neighbors can derive the packet delivery ratio from the neighbor to the probing node With the delivery ratio at both forward and reverse directions, denoted by df and dr, respectively, ET ...
6 – Transport Layer
... RPC connects applications over the network with the familiar abstraction of procedure calls • Stubs package parameters/results into a message • UDP with retransmissions is a low-latency transport ...
... RPC connects applications over the network with the familiar abstraction of procedure calls • Stubs package parameters/results into a message • UDP with retransmissions is a low-latency transport ...
Overview of Scalable Networks
... • Whatever value is specified with the bandwidth command, EIGRP always takes 50% of it (by default). • Remember: The bandwidth command is only used by routing protocols—it has no effect on user traffic when the protocol is EIGRP. The router does not use this command for any other purpose. • For exam ...
... • Whatever value is specified with the bandwidth command, EIGRP always takes 50% of it (by default). • Remember: The bandwidth command is only used by routing protocols—it has no effect on user traffic when the protocol is EIGRP. The router does not use this command for any other purpose. • For exam ...