lecture10 - Academic Server| Cleveland State University
... • IDS Systems can be defined as the tools, methods and resources to help identify, assess, and report unauthorized or unapproved network activity • Loosely compare IDS Systems to an alarm system • IDSs work at the network layer, they analyze packets to find specific patterns, if so an alert is logge ...
... • IDS Systems can be defined as the tools, methods and resources to help identify, assess, and report unauthorized or unapproved network activity • Loosely compare IDS Systems to an alarm system • IDSs work at the network layer, they analyze packets to find specific patterns, if so an alert is logge ...
Transport Layer protocols
... ( | IP’s CKS with the differences of following ) 1. Allowing odd # of data byte (by padding one byte of “0” ...
... ( | IP’s CKS with the differences of following ) 1. Allowing odd # of data byte (by padding one byte of “0” ...
Network and Web Basics. Architectures of Distributed
... • A network is a hardware and software data communication system that provides interconnection of computers and other devices. • A node (host) is an addressable device (computer) attached to a computer network. • An internet is a set of networks connected with routers. • The Internet is the larg ...
... • A network is a hardware and software data communication system that provides interconnection of computers and other devices. • A node (host) is an addressable device (computer) attached to a computer network. • An internet is a set of networks connected with routers. • The Internet is the larg ...
Routing Protocols - Cisco Networking Academy
... regenerate their SPF trees to find new shortest paths to each network, and update their routing tables with the changed routes. OSPF requires more router resources, such as RAM and CPU processing power, and is an advanced networking protocol that requires an experienced support staff. ...
... regenerate their SPF trees to find new shortest paths to each network, and update their routing tables with the changed routes. OSPF requires more router resources, such as RAM and CPU processing power, and is an advanced networking protocol that requires an experienced support staff. ...
Network Layer
... reason not to put the complexity in the hosts. 2. The subnet is a major international investment that will last for decades, so it should not be cluttered up with features that may become obsolete quickly. 3. Some applications, such as digitized voice and real-time data collection may regard speedy ...
... reason not to put the complexity in the hosts. 2. The subnet is a major international investment that will last for decades, so it should not be cluttered up with features that may become obsolete quickly. 3. Some applications, such as digitized voice and real-time data collection may regard speedy ...
Socket Programming
... Socket (InetAddress address, int port) - Creates a stream socket and connects it to the specified port number at the specified IP address. It will throws UnknownHostException or an IOException. getInputStream - Returns an input stream for this ...
... Socket (InetAddress address, int port) - Creates a stream socket and connects it to the specified port number at the specified IP address. It will throws UnknownHostException or an IOException. getInputStream - Returns an input stream for this ...
Socket Programming
... Socket (InetAddress address, int port) - Creates a stream socket and connects it to the specified port number at the specified IP address. It will throws UnknownHostException or an IOException. getInputStream - Returns an input stream for this ...
... Socket (InetAddress address, int port) - Creates a stream socket and connects it to the specified port number at the specified IP address. It will throws UnknownHostException or an IOException. getInputStream - Returns an input stream for this ...
Socket Programming - Wichita State University
... Socket (InetAddress address, int port) - Creates a stream socket and connects it to the specified port number at the specified IP address. It will throws UnknownHostException or an IOException. getInputStream - Returns an input stream for this ...
... Socket (InetAddress address, int port) - Creates a stream socket and connects it to the specified port number at the specified IP address. It will throws UnknownHostException or an IOException. getInputStream - Returns an input stream for this ...
Study on a Fast OSPF Route Reconstruction Method Under Network
... to the DR. If the DR does not respond to 4 hello packets from a neighbor, a neighbor detects DR failure and all neighbors start to elect new DR among their own neighbors. The hello packet interval is 10 sec (Hello Interval, default value), hence it takes 40 sec (Router Dead Interval) for neighbors t ...
... to the DR. If the DR does not respond to 4 hello packets from a neighbor, a neighbor detects DR failure and all neighbors start to elect new DR among their own neighbors. The hello packet interval is 10 sec (Hello Interval, default value), hence it takes 40 sec (Router Dead Interval) for neighbors t ...
HPSpaper - University of California, Irvine
... University of California Irvine. He received his BS degree in Computer Science from Massachusetts Institute of Technology in 1990. He received his MS and PhD degrees in Computer Science from the University of California San Diego in 1992 and 1997 respectively. He was a member of the faculty in the E ...
... University of California Irvine. He received his BS degree in Computer Science from Massachusetts Institute of Technology in 1990. He received his MS and PhD degrees in Computer Science from the University of California San Diego in 1992 and 1997 respectively. He was a member of the faculty in the E ...
AVVID QoS Infrastructure Design
... No matter what the PPS rating is… No matter if it’s the fastest switch ever… ...
... No matter what the PPS rating is… No matter if it’s the fastest switch ever… ...
Document
... • A larger portion of traffic is forwarded based on slower routing table • The amount of redirected traffic could easily overload the processor • And processor overload in turn can cause system failure ...
... • A larger portion of traffic is forwarded based on slower routing table • The amount of redirected traffic could easily overload the processor • And processor overload in turn can cause system failure ...
chapter4-2007
... If you use these slides (e.g., in a class) in substantially unaltered form, that you mention their source (after all, we’d like people to use our book!) If you post any slides in substantially unaltered form on a www site, that you note that they are adapted from (or perhaps identical to) our sl ...
... If you use these slides (e.g., in a class) in substantially unaltered form, that you mention their source (after all, we’d like people to use our book!) If you post any slides in substantially unaltered form on a www site, that you note that they are adapted from (or perhaps identical to) our sl ...
Hands-On Ethical Hacking and Network Security
... but I leave it as an exercise for readers to determine what satisfaction is obtained by the authors of tools that turn threat into reality and lay waste to millions of dollars of investments.” --"Real 802.11 Security", William Arbaugh and Jon Edney, as quoted in link Ch 11g ...
... but I leave it as an exercise for readers to determine what satisfaction is obtained by the authors of tools that turn threat into reality and lay waste to millions of dollars of investments.” --"Real 802.11 Security", William Arbaugh and Jon Edney, as quoted in link Ch 11g ...
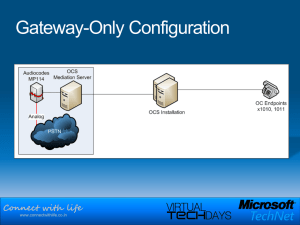
Connect with life
... High-speed connectivity continues to grow more ubiquitous Little tolerance for potentially complex operations Setting up a virtual private network (VPN) Finding a connection at a customer site Connecting from their home broadband connection ...
... High-speed connectivity continues to grow more ubiquitous Little tolerance for potentially complex operations Setting up a virtual private network (VPN) Finding a connection at a customer site Connecting from their home broadband connection ...
H3C SR8800 10G Core Routers
... H3C SR8800 10G Core Routers (hereinafter referred to as the SR8800) are developed by Hangzhou H3C Technologies Co., Ltd., based on its thorough research and deep understanding of user needs. The SR8800 can be widely deployed at IP backbone networks, metropolitan area networks (MANs) and the core and ...
... H3C SR8800 10G Core Routers (hereinafter referred to as the SR8800) are developed by Hangzhou H3C Technologies Co., Ltd., based on its thorough research and deep understanding of user needs. The SR8800 can be widely deployed at IP backbone networks, metropolitan area networks (MANs) and the core and ...
Presentation Title Size 30PT
... Enabled for both ILT and Blended Distance Learning (BDL) delivery 9 Chapters At least 1 complex hands-on lab per chapter and Packet Tracer activities Provided as separate .zip files downloaded from AC; not embedded in the GUI ...
... Enabled for both ILT and Blended Distance Learning (BDL) delivery 9 Chapters At least 1 complex hands-on lab per chapter and Packet Tracer activities Provided as separate .zip files downloaded from AC; not embedded in the GUI ...
A Delay-Tolerant Network Architecture for Challenged Internets
... Terrestrial mobile networks Unexpected partitions due to node mobility or RF interference ...
... Terrestrial mobile networks Unexpected partitions due to node mobility or RF interference ...
Introducing the ISC
... » Intelligent Networking PLUS » Multimedia with integrated voice/video/data » Limited only by the imagination • Lower barriers to entry for both system suppliers and service providers » Open architecture, protocols and APIs » Leverages any/all underlying transports (packet/frame/cell) » Dramatically ...
... » Intelligent Networking PLUS » Multimedia with integrated voice/video/data » Limited only by the imagination • Lower barriers to entry for both system suppliers and service providers » Open architecture, protocols and APIs » Leverages any/all underlying transports (packet/frame/cell) » Dramatically ...
mpls
... In MPLS Domain, all the traffic in a set of FECs might follow the same route. Example – a set of distinct address prefixes might all have the same egress node. In such case, the union of those FECs it itself a FEC. The procedure of binding a single label to a union of FECs which is itself a FEC, and ...
... In MPLS Domain, all the traffic in a set of FECs might follow the same route. Example – a set of distinct address prefixes might all have the same egress node. In such case, the union of those FECs it itself a FEC. The procedure of binding a single label to a union of FECs which is itself a FEC, and ...
slides
... Receive (NIC): insert received data into OS's socket Received (OS): remove received data from NIC's socket Control (OS, NIC): change socket states, etc. ...
... Receive (NIC): insert received data into OS's socket Received (OS): remove received data from NIC's socket Control (OS, NIC): change socket states, etc. ...
Chapter 6: The Internet
... 6 Cloud Computing The concept of cloud computing depends on a grid of servers and storage devices that offer Internet-accessible computing services ranging from hardware to office productivity applications and complex corporate data processing ...
... 6 Cloud Computing The concept of cloud computing depends on a grid of servers and storage devices that offer Internet-accessible computing services ranging from hardware to office productivity applications and complex corporate data processing ...
Wide-Area Ethernet Network Configuration for System
... The C-RAS substation LANs and the control center LANs carry Ethernet packets of specific types we will discuss. However, we note that the network communications, mostly SONET, are all time division multiplexed (TDM) formats, which operate in a deterministic or preordered data format and do not inher ...
... The C-RAS substation LANs and the control center LANs carry Ethernet packets of specific types we will discuss. However, we note that the network communications, mostly SONET, are all time division multiplexed (TDM) formats, which operate in a deterministic or preordered data format and do not inher ...