Protection in General-Purpose Operating Systems
... feature built into the HTTP protocol uses PAP. The main weakness of PAP is that both the username and password are transmitted "in the clear" -- that is, in an unencrypted form ...
... feature built into the HTTP protocol uses PAP. The main weakness of PAP is that both the username and password are transmitted "in the clear" -- that is, in an unencrypted form ...
Living in a Network Centric World
... Data Networking Role, Components, and Challenges Elements that make up a network – Devices • To communicate with one another – Medium Connects devices together – Messages • Information over media – Rules • Govern how messages flow across networks ...
... Data Networking Role, Components, and Challenges Elements that make up a network – Devices • To communicate with one another – Medium Connects devices together – Messages • Information over media – Rules • Govern how messages flow across networks ...
Cramsession`s Net+ Online Study Guide
... back into the core. Looks dramatically different from the twisted pair cable and coaxial cable described above. Maximum cable length is 25 kilometers and transmission rates are up to 2 Gbps. Fiber optic cable carries laser light encoded with digital signals, and is capable of reliably transmitting b ...
... back into the core. Looks dramatically different from the twisted pair cable and coaxial cable described above. Maximum cable length is 25 kilometers and transmission rates are up to 2 Gbps. Fiber optic cable carries laser light encoded with digital signals, and is capable of reliably transmitting b ...
ppt
... •Research scope includes protocol design, implementation, performance evaluation, and usage-based validation •The goal is to enable mobile hosts to communicate with each other and with stationary or wired hosts, transparently, seamlessly, efficiently using the best network connectivity available WPI ...
... •Research scope includes protocol design, implementation, performance evaluation, and usage-based validation •The goal is to enable mobile hosts to communicate with each other and with stationary or wired hosts, transparently, seamlessly, efficiently using the best network connectivity available WPI ...
ppt
... Server – service software running on a single machine Client – process that can invoke a service using a set of ...
... Server – service software running on a single machine Client – process that can invoke a service using a set of ...
Guide to TCP/IP, Second Edition
... the destination host); and service delivery options to control packet and route priorities (seldom used, but worth understanding) • IP traffic can be prioritized using Differentiated Services or Type of Service designations Guide to TCP/IP, Second Edition ...
... the destination host); and service delivery options to control packet and route priorities (seldom used, but worth understanding) • IP traffic can be prioritized using Differentiated Services or Type of Service designations Guide to TCP/IP, Second Edition ...
GPRS
... and logical data interface to the base station subsystem (BSS) for packet data traffic. The BTS can also require a software upgrade but typically does not require hardware enhancements. When either voice or data traffic is originated at the subscriber mobile, it is transported over the air interface ...
... and logical data interface to the base station subsystem (BSS) for packet data traffic. The BTS can also require a software upgrade but typically does not require hardware enhancements. When either voice or data traffic is originated at the subscriber mobile, it is transported over the air interface ...
Hotspot Shield Vpn Getjar
... Hotspot Shield Vpn Getjar - A virtual private network (VPN) extends a private network across a public network, such as the Internet. It enables a computer or network-enabled device to send and receive data across shared or public networks as if it were directly connected to the private network, whil ...
... Hotspot Shield Vpn Getjar - A virtual private network (VPN) extends a private network across a public network, such as the Internet. It enables a computer or network-enabled device to send and receive data across shared or public networks as if it were directly connected to the private network, whil ...
Lecture_7-CTTC_20120422
... Mobility handling of inter-MME (pool) handover (triggered by eNodeB) inter-RAT handover (triggered by eNodeB) QoS “negotiation” with UE and eNodeB Security Ciphering and integrity protection of NAS signalling Secure control signalling transport on S1 interface (unless taken care of by a SEG ...
... Mobility handling of inter-MME (pool) handover (triggered by eNodeB) inter-RAT handover (triggered by eNodeB) QoS “negotiation” with UE and eNodeB Security Ciphering and integrity protection of NAS signalling Secure control signalling transport on S1 interface (unless taken care of by a SEG ...
Chen-WPC10-slide
... User Oriented Regional RegistrationBased Mobile Multicast Service Management in Mobile IP Networks Ing-Ray Chen and Ding-Chau Wang ...
... User Oriented Regional RegistrationBased Mobile Multicast Service Management in Mobile IP Networks Ing-Ray Chen and Ding-Chau Wang ...
an assessment of international voice traffic termination rates
... Following liberalisation of telecommunication markets around the world, there has been a trend of declining rates for incoming international termination. These rates, which were previously held at artificially high levels by government imposed monopolies, rapidly converged towards the levels availab ...
... Following liberalisation of telecommunication markets around the world, there has been a trend of declining rates for incoming international termination. These rates, which were previously held at artificially high levels by government imposed monopolies, rapidly converged towards the levels availab ...
(Ch.7, Part 2): Security in Networks – Part 2 – LONG version
... Only user’s msg (user’s data) encrypted All headers & trailers exposed (all created after encryption) ...
... Only user’s msg (user’s data) encrypted All headers & trailers exposed (all created after encryption) ...
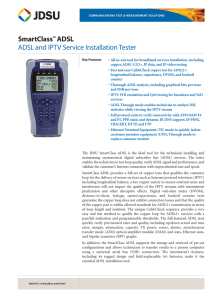
SmartClass™ ADSL ADSL and IPTV Service Installation Tester
... positioning. At the same time consumers are signing up for multiple services in this very competitive environment expecting the best service quality, making it imperative that operators quickly and cost-effectively install ADSL2+ lines with the confidence that their complex triple-play services are ...
... positioning. At the same time consumers are signing up for multiple services in this very competitive environment expecting the best service quality, making it imperative that operators quickly and cost-effectively install ADSL2+ lines with the confidence that their complex triple-play services are ...
IEEE 802.11 Wireless LAN Security Performance Using Multiple
... which uses an Ethernet-style contention algorithm that provides access to all traffic. Ordinary asynchronous traffic uses this coordination function (see Section 2.2.4). The upper MAC sublayer is the point coordination function (PCF), a centralised MAC algorithm that provides contention-free service ...
... which uses an Ethernet-style contention algorithm that provides access to all traffic. Ordinary asynchronous traffic uses this coordination function (see Section 2.2.4). The upper MAC sublayer is the point coordination function (PCF), a centralised MAC algorithm that provides contention-free service ...
IPv6 networks deployments
... • In addition to traditional “Unix” applications (ssh, telnet, web servers, …) • 6Net has run the following applications trials : – VoIP with SIP (SIP Express Router) + voice user agent (eg. Kphone IPv6) + PSTN gateway + MCU + VPN functionality – Streaming between mobile hosts, including MIP6 – Acce ...
... • In addition to traditional “Unix” applications (ssh, telnet, web servers, …) • 6Net has run the following applications trials : – VoIP with SIP (SIP Express Router) + voice user agent (eg. Kphone IPv6) + PSTN gateway + MCU + VPN functionality – Streaming between mobile hosts, including MIP6 – Acce ...
Sample
... The protocol is a set of rules about the format and meaning of data units exchanged by the peer entities within a layer The service is a set of primitives (operations) that a layer provider to the layer above it The interface tells the processes above it how to access it, that is, it specifies what ...
... The protocol is a set of rules about the format and meaning of data units exchanged by the peer entities within a layer The service is a set of primitives (operations) that a layer provider to the layer above it The interface tells the processes above it how to access it, that is, it specifies what ...
MPLS - 中正大學
... Switches are required to buffer cells from one packet until the entire packet is received Advantage : straightforward application of VC switching Disadvantage : New hardware (based on per-VC queuing) Delays at the merge points 中正資工/黃仁竑 ...
... Switches are required to buffer cells from one packet until the entire packet is received Advantage : straightforward application of VC switching Disadvantage : New hardware (based on per-VC queuing) Delays at the merge points 中正資工/黃仁竑 ...
Networking
... Delivery of IP over Ethernet Network cards have MAC-addresses, not IP addresses MAC addresses are not assigned systematically so can’t be used ...
... Delivery of IP over Ethernet Network cards have MAC-addresses, not IP addresses MAC addresses are not assigned systematically so can’t be used ...
Alteon Stackable Web switches 180 and ACEDirector
... port. This allows Web sessions to be switched ...
... port. This allows Web sessions to be switched ...
Network Working Group S. Blake Request for
... permit differentiated pricing of Internet service. This architecture is composed of a number of functional elements implemented in network nodes, including a small set of per-hop forwarding behaviors, packet classification functions, and traffic conditioning functions including metering, marking, sh ...
... permit differentiated pricing of Internet service. This architecture is composed of a number of functional elements implemented in network nodes, including a small set of per-hop forwarding behaviors, packet classification functions, and traffic conditioning functions including metering, marking, sh ...
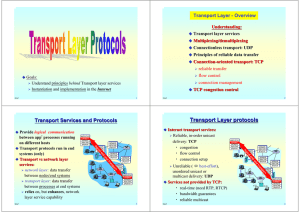
Transport Layer protocols
... ( | IP’s CKS with the differences of following ) 1. Allowing odd # of data byte (by padding one byte of “0” ...
... ( | IP’s CKS with the differences of following ) 1. Allowing odd # of data byte (by padding one byte of “0” ...