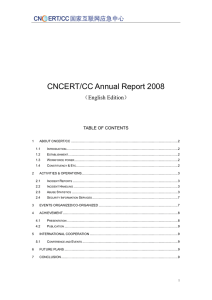
CNCERT/CC Annual Report 2008
... The workshop was held on 23rd March 2008 at APEC-TEL37 in Tokyo. 12 experts gave the presentations to share their experiences and skills regarding to Botnet. The workshop provided an atmosphere that encourages the sharing of knowledge and experiences of effective solutions for preventing, detecting ...
... The workshop was held on 23rd March 2008 at APEC-TEL37 in Tokyo. 12 experts gave the presentations to share their experiences and skills regarding to Botnet. The workshop provided an atmosphere that encourages the sharing of knowledge and experiences of effective solutions for preventing, detecting ...
Chapter 1 Study Outline
... B. Information security involves identifying the threats and vulnerabilities of the organization and managing them appropriately. C. Implementing a proper information security system is not a one-time activity. It requires a constant vigilance against new security threats that might arise. D. The ne ...
... B. Information security involves identifying the threats and vulnerabilities of the organization and managing them appropriately. C. Implementing a proper information security system is not a one-time activity. It requires a constant vigilance against new security threats that might arise. D. The ne ...
Document
... effects on your organization. 2. Security topology covers four primary areas of concern (design goals, security zones, technologies, and business requirements). Describe each area including key topics in each area. 3. Discuss software threats classified as malicious code on page 81 of your text. ...
... effects on your organization. 2. Security topology covers four primary areas of concern (design goals, security zones, technologies, and business requirements). Describe each area including key topics in each area. 3. Discuss software threats classified as malicious code on page 81 of your text. ...
D1S1_TSV404_Course_Intro_2011_v1
... ■ The information systems security office has areas that can be improved upon, especially C&A, RA and CP. ■ Embedding security into the SDLC is the best methodology NIST 80064R2 ■ Accountability is important from the system owner, to OIS, to the vendor implementing the controls ■ Standard reporting ...
... ■ The information systems security office has areas that can be improved upon, especially C&A, RA and CP. ■ Embedding security into the SDLC is the best methodology NIST 80064R2 ■ Accountability is important from the system owner, to OIS, to the vendor implementing the controls ■ Standard reporting ...
Chapter 9
... To protect the contents of IP packets To provide defense against network attacks through packet filtering and the enforcement of trusted communication. Attacks that IPSec can prevent and reduce: Packet Sniffing Man in the Middle Data Modification Denial of Service Identity Spoofing ...
... To protect the contents of IP packets To provide defense against network attacks through packet filtering and the enforcement of trusted communication. Attacks that IPSec can prevent and reduce: Packet Sniffing Man in the Middle Data Modification Denial of Service Identity Spoofing ...
Phoenix SIEM (Security Information and Event
... Director and CTO at Kenindus Limited . Holds a Bachelor of Science degree in Computer Information Management from Life University in Atlanta, Georgia and a Masters in Small Business and Entrepreneurship from Plymouth State in Plymouth, New Hampshire. I have more than 10 years experience in cyber sec ...
... Director and CTO at Kenindus Limited . Holds a Bachelor of Science degree in Computer Information Management from Life University in Atlanta, Georgia and a Masters in Small Business and Entrepreneurship from Plymouth State in Plymouth, New Hampshire. I have more than 10 years experience in cyber sec ...
networkworld - Sift Security
... developed at MIT and Stanford universities, Sifter is able to find previously unknown threats. The next element, Investigator, is the UI that combines graph, search and dashboards. The graph UI makes it easy to see patterns and pivot across entities to trace an incident across the environment. Cust ...
... developed at MIT and Stanford universities, Sifter is able to find previously unknown threats. The next element, Investigator, is the UI that combines graph, search and dashboards. The graph UI makes it easy to see patterns and pivot across entities to trace an incident across the environment. Cust ...
Network Security
... Outline of the Course • This chapter serves as an introduction to the entire course. The remainder of the book is organized into three parts: • Part One : Provides a concise survey of the cryptographic algorithms and protocols underlying network security applications, including encryption, hash fun ...
... Outline of the Course • This chapter serves as an introduction to the entire course. The remainder of the book is organized into three parts: • Part One : Provides a concise survey of the cryptographic algorithms and protocols underlying network security applications, including encryption, hash fun ...
Network Security
... Outline of the Course • This chapter serves as an introduction to the entire course. The remainder of the book is organized into three parts: • Part One : Provides a concise survey of the cryptographic algorithms and protocols underlying network security applications, including encryption, hash fun ...
... Outline of the Course • This chapter serves as an introduction to the entire course. The remainder of the book is organized into three parts: • Part One : Provides a concise survey of the cryptographic algorithms and protocols underlying network security applications, including encryption, hash fun ...
Network and Systems - University of Glasgow
... Define the overheads wrt management, operation and security functions associated with deploying a network server Identify all network servers and establish their purpose, security requirements, user base and support staff Limit the exposure of network servers to those apps that are critical for thei ...
... Define the overheads wrt management, operation and security functions associated with deploying a network server Identify all network servers and establish their purpose, security requirements, user base and support staff Limit the exposure of network servers to those apps that are critical for thei ...
Robust. Reliable. Factory Line. Industrial Security redefined protecting industrial networks
... (QoS) functionalities and helps with intrusion detection and antivirus protection. The mGuard portfolio is complemented by a highly scalable device management software. Innominate products are marketed worldwide under the mGuard brand through system integrators and OEM partners. Further information ...
... (QoS) functionalities and helps with intrusion detection and antivirus protection. The mGuard portfolio is complemented by a highly scalable device management software. Innominate products are marketed worldwide under the mGuard brand through system integrators and OEM partners. Further information ...
Visualization
... Correlation uses software technology to analyze aggregated data, in real-time, to determine if specific patterns exist. These patterns of similar security events often correspond to specific securityattacks – whether denial of service,anti virus, or some other form of attack. Visualization, the fina ...
... Correlation uses software technology to analyze aggregated data, in real-time, to determine if specific patterns exist. These patterns of similar security events often correspond to specific securityattacks – whether denial of service,anti virus, or some other form of attack. Visualization, the fina ...
Advanced Linux Security
... • Role-based access control (RBAC) is used to define a set of roles that can be assigned to users. • SELinux further extends the RBAC model to restrict roles to specified TE domains, and roles can be arranged in a priority hierarchy. • The security context of a process contains a role attribute and ...
... • Role-based access control (RBAC) is used to define a set of roles that can be assigned to users. • SELinux further extends the RBAC model to restrict roles to specified TE domains, and roles can be arranged in a priority hierarchy. • The security context of a process contains a role attribute and ...
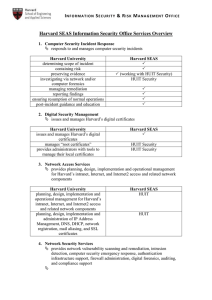
Harvard SEAS Information Security Office Services Overview
... notifies user or resource owner and triggers incident response service Inspects network traffic to identify security vulnerabilities in networkconnected systems or devices. monitors, detects and, as necessary, protects High Risk Confidential Information detects and reports on computers that exhibit ...
... notifies user or resource owner and triggers incident response service Inspects network traffic to identify security vulnerabilities in networkconnected systems or devices. monitors, detects and, as necessary, protects High Risk Confidential Information detects and reports on computers that exhibit ...
Operating System Security Chapter 9 Operating System Security
... risks and ranking them • To assess risks – Start with a list of the assets that must be protected – Rank the importance of the assets – Create a list of events that could cause data loss, whether from natural, man-made, or malicious causes • Make sure to include management in this process ...
... risks and ranking them • To assess risks – Start with a list of the assets that must be protected – Rank the importance of the assets – Create a list of events that could cause data loss, whether from natural, man-made, or malicious causes • Make sure to include management in this process ...
Document
... health department and technology services officials said during a press conference at the State Office Building. “Less sensitive” information was described as names, dates of birth and addresses. Officials said there may be some overlap between the groups, and information is still being reviewed. Th ...
... health department and technology services officials said during a press conference at the State Office Building. “Less sensitive” information was described as names, dates of birth and addresses. Officials said there may be some overlap between the groups, and information is still being reviewed. Th ...
The Top Ten of Security
... – The “reading room” for SANS, a large computer security training organization. ...
... – The “reading room” for SANS, a large computer security training organization. ...
Addressing security threats and vulnerabilities
... • Specific to business – DoS attack on the company Web Server • Threats that are not directed – DDoS • Widely known threats – worms, viruses • External threats – originates from outside the company (not the network) • Internal threats – originates from within the company (eg technically savvy users) ...
... • Specific to business – DoS attack on the company Web Server • Threats that are not directed – DDoS • Widely known threats – worms, viruses • External threats – originates from outside the company (not the network) • Internal threats – originates from within the company (eg technically savvy users) ...
Module F - Columbus State University
... allocated memory can hold. The extra data slops over into the adjacent memory area, overwriting what was already there, including data or instructions. Malicious hackers have become proficient at leveraging such overflows to introduce their own code into programs, effectively hijacking the computer. ...
... allocated memory can hold. The extra data slops over into the adjacent memory area, overwriting what was already there, including data or instructions. Malicious hackers have become proficient at leveraging such overflows to introduce their own code into programs, effectively hijacking the computer. ...
Department of Information Resources, State
... Put them in order Work the list from high to low Every item needs a compensating control http://csrc.nist.gov/publications/nistpubs/8 00-30/sp800-30.pdf ...
... Put them in order Work the list from high to low Every item needs a compensating control http://csrc.nist.gov/publications/nistpubs/8 00-30/sp800-30.pdf ...
TNS03%20Introduction%20to%20Network%20Security
... Reviewing logs and records Procedures to determine if these items meet standards ...
... Reviewing logs and records Procedures to determine if these items meet standards ...
Airport security
Airport security refers to the techniques and methods used in protecting passengers, staff and aircraft which use the airports from accidental/malicious harm, crime and other threats.