6 - University of South Florida St. Petersburg
... Dominant architecture used today is the screened subnet firewall Commonly consists of two or more internal bastion hosts behind packet filtering router, with each host protecting trusted network: Connections from outside (untrusted network) routed through external filtering router Connection ...
... Dominant architecture used today is the screened subnet firewall Commonly consists of two or more internal bastion hosts behind packet filtering router, with each host protecting trusted network: Connections from outside (untrusted network) routed through external filtering router Connection ...
Mainline How Secure Are You K12 Security Preseo Rev 1
... measure must be employed "during any use of such computers by minors." The law also provides that the library "may disable the technology protection measure concerned, during use by an adult, to enable access for bona fide research or other lawful purpose." Libraries that do not receive E-Rate disco ...
... measure must be employed "during any use of such computers by minors." The law also provides that the library "may disable the technology protection measure concerned, during use by an adult, to enable access for bona fide research or other lawful purpose." Libraries that do not receive E-Rate disco ...
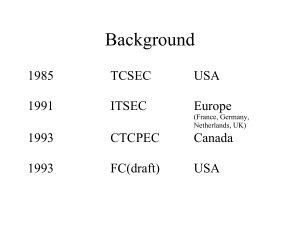
Common Criteria
... I. Introduction and General Model DefinitionsTarget of Evaluation (TOE) — An IT product or system and its associated administrator and user guidance documentation that is the subject of an evaluation. ...
... I. Introduction and General Model DefinitionsTarget of Evaluation (TOE) — An IT product or system and its associated administrator and user guidance documentation that is the subject of an evaluation. ...
Lecture11 - The University of Texas at Dallas
... The problem: establishing trust in open systems Interactions between strangers - In conventional systems user identity is known in advance and can be used for performing access control - In open systems partecipants may have no pre-existing relationship and may not share a common security domain ...
... The problem: establishing trust in open systems Interactions between strangers - In conventional systems user identity is known in advance and can be used for performing access control - In open systems partecipants may have no pre-existing relationship and may not share a common security domain ...
Lecture3 - The University of Texas at Dallas
... The problem: establishing trust in open systems Interactions between strangers - In conventional systems user identity is known in advance and can be used for performing access control - In open systems partecipants may have no pre-existing relationship and may not share a common security domain ...
... The problem: establishing trust in open systems Interactions between strangers - In conventional systems user identity is known in advance and can be used for performing access control - In open systems partecipants may have no pre-existing relationship and may not share a common security domain ...
Chapter 9
... • CIA security triad (CIA triad) Three security concepts important to information on the Internet: confidentiality, integrity, and availability. ...
... • CIA security triad (CIA triad) Three security concepts important to information on the Internet: confidentiality, integrity, and availability. ...
Introduction to Healthcare Information Technology
... • A legal health record is the documentation of healthcare services provided to an individual • Legal health records may be disposed of by shredding, sanitizing, or degaussing (for electronic ...
... • A legal health record is the documentation of healthcare services provided to an individual • Legal health records may be disposed of by shredding, sanitizing, or degaussing (for electronic ...
How Organizations Are Using Fortscale`s User Behavior Analytics
... Fortscale constantly identifies new users and new machines in an enterprise and generates reports analysts can review to ensure these accounts and machines are valid in the network. On one occasion, Fortscale detected a new user account in the enterprise and began analyzing activity to build a basel ...
... Fortscale constantly identifies new users and new machines in an enterprise and generates reports analysts can review to ensure these accounts and machines are valid in the network. On one occasion, Fortscale detected a new user account in the enterprise and began analyzing activity to build a basel ...
Threat Awareness and Defense Sec Briefing 51.00
... sought in the old Cold War days toward basic research and development processes. Such targets also include the technology and trade secrets of U.S. high-tech companies—everything from cost analyses, marketing plans, contract bids and proprietary software to the high-tech data itself. Any information ...
... sought in the old Cold War days toward basic research and development processes. Such targets also include the technology and trade secrets of U.S. high-tech companies—everything from cost analyses, marketing plans, contract bids and proprietary software to the high-tech data itself. Any information ...
What is Beta Testing? - KV Institute of Management and Information
... Beta version of the software is released to a limited number of end-users of the product to obtain feedback on the product quality. Beta testing reduces product failure risks and provides increased quality of the product through customer validation. ...
... Beta version of the software is released to a limited number of end-users of the product to obtain feedback on the product quality. Beta testing reduces product failure risks and provides increased quality of the product through customer validation. ...
Chapter 6
... • S-HTTP provides a number of security features, including: – Client and server authentication – Spontaneous encryption ...
... • S-HTTP provides a number of security features, including: – Client and server authentication – Spontaneous encryption ...
Chapter 8
... entity was not their final IP destination, as a result of which an attempt was made to find a route to forward them to that final destination. In entities which do not act as IP Gateways, this ...
... entity was not their final IP destination, as a result of which an attempt was made to find a route to forward them to that final destination. In entities which do not act as IP Gateways, this ...
Chapter 8
... entity was not their final IP destination, as a result of which an attempt was made to find a route to forward them to that final destination. In entities which do not act as IP Gateways, this ...
... entity was not their final IP destination, as a result of which an attempt was made to find a route to forward them to that final destination. In entities which do not act as IP Gateways, this ...
Firewalls
... Screened Subnet Firewalls (with DMZ) Dominant architecture used today is the screened subnet firewall Commonly consists of two or more internal bastion hosts behind packet filtering router, with each host protecting trusted network: Connections from outside (untrusted network) routed through ...
... Screened Subnet Firewalls (with DMZ) Dominant architecture used today is the screened subnet firewall Commonly consists of two or more internal bastion hosts behind packet filtering router, with each host protecting trusted network: Connections from outside (untrusted network) routed through ...
Security+ Guide to Network Security Fundamentals, Third
... Complex security schemes are often compromised by employees themselves to make them easier for (trusted) users to work with ...
... Complex security schemes are often compromised by employees themselves to make them easier for (trusted) users to work with ...
Enhanced Security Models for Operating Systems: A Cryptographic
... Under Vault architecture, System administrator uses fingerprinting to protect themselves against threats. Two types of fingerprinting: ...
... Under Vault architecture, System administrator uses fingerprinting to protect themselves against threats. Two types of fingerprinting: ...
Top-Ten Web Security Vulnerabilities
... Our products should emphasize security right out of the box” Bill Gates ...
... Our products should emphasize security right out of the box” Bill Gates ...
eCommerce&Security
... Privacy: it is in accessible to anyone except the sender and receiver. Integrity: data has not been altered during transmission. Authenticity: the receiver can be sure it came form the sender. Non-fabrication: the sender is sure that the receiver is genuine. Non-repudiation: the sender cannot deny s ...
... Privacy: it is in accessible to anyone except the sender and receiver. Integrity: data has not been altered during transmission. Authenticity: the receiver can be sure it came form the sender. Non-fabrication: the sender is sure that the receiver is genuine. Non-repudiation: the sender cannot deny s ...
D-Lib Magazine - Forum on Information Standards in Heritage
... a major problem of interoperability. To achieve a full picture of the existing knowledge of a single feature in the historic environment, it is often necessary to draw upon information from a variety of different HEIRs. To review the full range of knowledge about a particular aspect of the historic ...
... a major problem of interoperability. To achieve a full picture of the existing knowledge of a single feature in the historic environment, it is often necessary to draw upon information from a variety of different HEIRs. To review the full range of knowledge about a particular aspect of the historic ...
lecture 1 - Philadelphia University
... whether an asset has been damaged, how, and who has caused the damage. – Response ( post-action)– to take measures that allow recovery of assets or recovery from damage, and minimize losses. – Reflection – plans/processes that focus on security improvements. ...
... whether an asset has been damaged, how, and who has caused the damage. – Response ( post-action)– to take measures that allow recovery of assets or recovery from damage, and minimize losses. – Reflection – plans/processes that focus on security improvements. ...
Cyber Security Education Consortium 2008 Retreat
... • Control Systems protocols with little or no security • Migration to TCP/IP networks with its inherent vulnerabilities ...
... • Control Systems protocols with little or no security • Migration to TCP/IP networks with its inherent vulnerabilities ...
Ecommerce: Security and Control
... Do we design systems that overcontrolled, and therefore not functional, or unrestricted and undercontrolled? ...
... Do we design systems that overcontrolled, and therefore not functional, or unrestricted and undercontrolled? ...