Security Brochure, PDF
... MFPs are often ignored as being any kind of security risk. While some risks are perhaps identified, they are often simply neglected, especially where sensitive documents and information are concerned. This is especially risky for those MFPs and printers located in public areas, where they can be acc ...
... MFPs are often ignored as being any kind of security risk. While some risks are perhaps identified, they are often simply neglected, especially where sensitive documents and information are concerned. This is especially risky for those MFPs and printers located in public areas, where they can be acc ...
Firewall and VPNs - Ohio State Computer Science and Engineering
... Screened Subnet Firewalls (with DMZ) Dominant architecture used today is the screened subnet firewall Commonly consists of two or more internal bastion hosts behind packet filtering router, with each host protecting trusted network: Connections from outside (untrusted network) routed through ...
... Screened Subnet Firewalls (with DMZ) Dominant architecture used today is the screened subnet firewall Commonly consists of two or more internal bastion hosts behind packet filtering router, with each host protecting trusted network: Connections from outside (untrusted network) routed through ...
Security Policies, Standards, and Planning
... b. This section defines “fair and responsible use” of equipment and other organizational assets and should also address key legal issues, such as protection of personal information and privacy. 3. Prohibited use of equipment a. This section outlines what the issue or technology cannot be used for. U ...
... b. This section defines “fair and responsible use” of equipment and other organizational assets and should also address key legal issues, such as protection of personal information and privacy. 3. Prohibited use of equipment a. This section outlines what the issue or technology cannot be used for. U ...
6 - Computer Science and Engineering
... Screened Subnet Firewalls (with DMZ) Dominant architecture used today is the screened subnet firewall Commonly consists of two or more internal bastion hosts behind packet filtering router, with each host protecting trusted network: Connections from outside (untrusted network) routed through ...
... Screened Subnet Firewalls (with DMZ) Dominant architecture used today is the screened subnet firewall Commonly consists of two or more internal bastion hosts behind packet filtering router, with each host protecting trusted network: Connections from outside (untrusted network) routed through ...
CEH
... You can gather company infrastructure details from job postings Look for company infrastructure postings such as “looking for system administrator to manage Solaris 10 network” This means that the company has Solaris networks on site E.g., www.jobsdb.com ...
... You can gather company infrastructure details from job postings Look for company infrastructure postings such as “looking for system administrator to manage Solaris 10 network” This means that the company has Solaris networks on site E.g., www.jobsdb.com ...
(FIPS) 140-2 - Aviat Networks
... Example: Lab can check code submitted by manufacturer. Well known code library function Glibc function is OK for general use but not quite random enough for encryption ...
... Example: Lab can check code submitted by manufacturer. Well known code library function Glibc function is OK for general use but not quite random enough for encryption ...
6 - Kuroski
... Screened Subnet Firewalls (with DMZ) Dominant architecture used today is the screened subnet firewall Commonly consists of two or more internal bastion hosts behind packet filtering router, with each host protecting trusted network: Connections from outside (untrusted network) routed through ...
... Screened Subnet Firewalls (with DMZ) Dominant architecture used today is the screened subnet firewall Commonly consists of two or more internal bastion hosts behind packet filtering router, with each host protecting trusted network: Connections from outside (untrusted network) routed through ...
Chapter 4 - Internal Controls In IT Systems
... access to the operating system also allows access to applications and the database. In addition, all read/write data functions are controlled by the operating system and any person who has access to the operating system can have access to data. Essentially, access to the operating system opens acces ...
... access to the operating system also allows access to applications and the database. In addition, all read/write data functions are controlled by the operating system and any person who has access to the operating system can have access to data. Essentially, access to the operating system opens acces ...
Evaluating Information Found on the Internet
... z The document names individuals and/or sources that provided non- published data used in the ...
... z The document names individuals and/or sources that provided non- published data used in the ...
No Slide Title - ECE Users Pages - Georgia Institute of Technology
... • A Georgia Tech student uses their personal PC and a commercial ISP to do a port scan on a commercial web site. • A Georgia Tech student sends a “spoofed mail” from the school account that appears to come from another user. • A Georgia Tech student uses a school computer and password guessing softw ...
... • A Georgia Tech student uses their personal PC and a commercial ISP to do a port scan on a commercial web site. • A Georgia Tech student sends a “spoofed mail” from the school account that appears to come from another user. • A Georgia Tech student uses a school computer and password guessing softw ...
all the web without the risk
... allowed network device for any Internet traffic in or out of the VM. This restriction ensures that, were malware to access the VM, it would not be able to see, map or attack any other infrastructure within the network. Using a second VPN from the server, users have the option to direct their traffic ...
... allowed network device for any Internet traffic in or out of the VM. This restriction ensures that, were malware to access the VM, it would not be able to see, map or attack any other infrastructure within the network. Using a second VPN from the server, users have the option to direct their traffic ...
Estimating Impact and Frequency of Risks to
... data are recorded and packaged offshore and transferred to other, sometimes multiple, locations onshore. For data to be correctly processed it is crucial that all steps involved are executed in a secure and safe manner free from deliberately and accidental fault introduction. Due to this, data is us ...
... data are recorded and packaged offshore and transferred to other, sometimes multiple, locations onshore. For data to be correctly processed it is crucial that all steps involved are executed in a secure and safe manner free from deliberately and accidental fault introduction. Due to this, data is us ...
Current Internet Threats
... Promote awareness Assist with computer security Provide guidance and resources to DePaul community ...
... Promote awareness Assist with computer security Provide guidance and resources to DePaul community ...
Survey of online attacks on E-Commerce sites
... Web based attacks are considered to be the greatest threat to the online business as it is related to confidentiality, availability, and integrity. The motive behind e-commerce attack is significantly different then other attacks; Web based attacks focus on an application itself and functions on lay ...
... Web based attacks are considered to be the greatest threat to the online business as it is related to confidentiality, availability, and integrity. The motive behind e-commerce attack is significantly different then other attacks; Web based attacks focus on an application itself and functions on lay ...
neutralizing credential theft and abuse
... techniques, the site can avoid being recognized as a phishing site. If the site is not categorized as bad, traditional security products, such as mail filtering solutions, do not stop the attack before it reaches the user, permitting users to interact with it as if it was a trusted site. This is a f ...
... techniques, the site can avoid being recognized as a phishing site. If the site is not categorized as bad, traditional security products, such as mail filtering solutions, do not stop the attack before it reaches the user, permitting users to interact with it as if it was a trusted site. This is a f ...
Don`t Wait for the Breach to Plan Your Reaction
... Sector-specific federal privacy and data protection laws. Most states require that “reasonable information security measures” be used. – Protect information from unauthorized access, destruction, use, modification and disclosure. – Use reasonable records retention/destruction procedures. ...
... Sector-specific federal privacy and data protection laws. Most states require that “reasonable information security measures” be used. – Protect information from unauthorized access, destruction, use, modification and disclosure. – Use reasonable records retention/destruction procedures. ...
PowerPoint-10b - Community College of Rhode Island
... What is Information Security? • Information Security: Task of guarding digital information • Information must be protective -on the devices that store, manipulate, and transmit the information through products, people, and procedures. ...
... What is Information Security? • Information Security: Task of guarding digital information • Information must be protective -on the devices that store, manipulate, and transmit the information through products, people, and procedures. ...
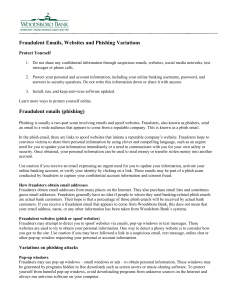
Fraudulent Emails, Websites and Phishing Variations Fraudulent
... How fraudsters obtain email addresses Fraudsters obtain email addresses from many places on the Internet. They also purchase email lists and sometimes guess email addresses. Fraudsters generally have no idea if people to whom they send banking-related phish emails are actual bank customers. Their ho ...
... How fraudsters obtain email addresses Fraudsters obtain email addresses from many places on the Internet. They also purchase email lists and sometimes guess email addresses. Fraudsters generally have no idea if people to whom they send banking-related phish emails are actual bank customers. Their ho ...
Green-Aware Security
... Energy consumption of SN and devices Social Networks (SNs) are one of the big phenomenon of Web 2.0, making Internet becoming always more an Internet of People. Users can ubiquitously access SN from different devices (laptop, handheld devices, top box devices, …) Access to SN is made through ...
... Energy consumption of SN and devices Social Networks (SNs) are one of the big phenomenon of Web 2.0, making Internet becoming always more an Internet of People. Users can ubiquitously access SN from different devices (laptop, handheld devices, top box devices, …) Access to SN is made through ...
Deleting POM Campaign Cause Report Data Associated with this
... When user deletes a POM campaign, all data records associated with this campaign would be removed from POM tables. They are no longer available in any POM report. In current POM design, when user deletes POM campaign, a popup box will display the message “Are you sure you want to delete this Campaig ...
... When user deletes a POM campaign, all data records associated with this campaign would be removed from POM tables. They are no longer available in any POM report. In current POM design, when user deletes POM campaign, a popup box will display the message “Are you sure you want to delete this Campaig ...
Rimini Street Technology Solution Brief-Oracle Security-LT
... your corporate, customer and partner data. We provide guidance on the implementation of a more holistic approach to security for your systems that can include the utilization of application firewalls, tightening encryption standards for networked traffic, ensuring PCI compliance for stored credit card ...
... your corporate, customer and partner data. We provide guidance on the implementation of a more holistic approach to security for your systems that can include the utilization of application firewalls, tightening encryption standards for networked traffic, ensuring PCI compliance for stored credit card ...
Logical attack advisory for U.S. and Canada
... Other Dispenser Security Authentication levels WILL NOT protect against Black Box attacks. The only protection against Black Box attacks is a combination of Level 3 Authentication AND USB dispenser component from APTRA XFS 06.03. For Personas ATMs: Fleet modernization is an important part of sta ...
... Other Dispenser Security Authentication levels WILL NOT protect against Black Box attacks. The only protection against Black Box attacks is a combination of Level 3 Authentication AND USB dispenser component from APTRA XFS 06.03. For Personas ATMs: Fleet modernization is an important part of sta ...
Exploration CCNA4 - Collin College Faculty Website Directory
... Assembling a security policy can be daunting. The ISO and IEC have published a security standard document called ISO/IEC 27002. The document consists of 12 sections: 1. Risk assessment 2. Security policy in collaboration with corporate management 3. Organization of information security 4. Asset mana ...
... Assembling a security policy can be daunting. The ISO and IEC have published a security standard document called ISO/IEC 27002. The document consists of 12 sections: 1. Risk assessment 2. Security policy in collaboration with corporate management 3. Organization of information security 4. Asset mana ...