What is the internet
... and "address" the packets correctly. The communicating computers--not the network itself--were also given the responsibility to ensure that the communication was accomplished. ...
... and "address" the packets correctly. The communicating computers--not the network itself--were also given the responsibility to ensure that the communication was accomplished. ...
ch3_OSI_2
... processes at this time with port addresses a, b, and c. The receiving computer is running two processes at this time with port addresses j and k. Process a in the sending computer needs to communicate with process j in the receiving computer. Note that although physical addresses change from hop to ...
... processes at this time with port addresses a, b, and c. The receiving computer is running two processes at this time with port addresses j and k. Process a in the sending computer needs to communicate with process j in the receiving computer. Note that although physical addresses change from hop to ...
Midterm Test - 18Jul08 - Solutions
... a. LAN c. peer-to-peer network b. internetwork d. client/server network 5. Most ____ consist of collections of typical end-user PCs linked by a common network medium. a. LANs c. peer-to-peer networks b. internetworks d. client/server networks 6. The emerging standard for WPANs is the IEEE ____ stand ...
... a. LAN c. peer-to-peer network b. internetwork d. client/server network 5. Most ____ consist of collections of typical end-user PCs linked by a common network medium. a. LANs c. peer-to-peer networks b. internetworks d. client/server networks 6. The emerging standard for WPANs is the IEEE ____ stand ...
service user
... Supporting multiple connections on one machine Mapping of multiple connections at one level to a single connection at another Carrying a number of connections on one fiber optic ...
... Supporting multiple connections on one machine Mapping of multiple connections at one level to a single connection at another Carrying a number of connections on one fiber optic ...
No Slide Title
... All devices are connected to one another in the shape of a closed loop, so that each device is connected directly to two other devices, one on either side of it. ...
... All devices are connected to one another in the shape of a closed loop, so that each device is connected directly to two other devices, one on either side of it. ...
4 Communication networks
... Send data to every other computer. Most hubs can accept a maximum of 24 connections Can be extended by connecting two or more hubs together. ...
... Send data to every other computer. Most hubs can accept a maximum of 24 connections Can be extended by connecting two or more hubs together. ...
IntroductiontoInform.. - Home (www.dginter.net)
... Hopefully they both listen for silence before speaking. ...
... Hopefully they both listen for silence before speaking. ...
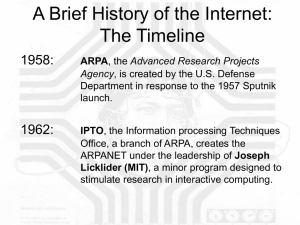
A Brief History of the Internet: The Timeline
... standardization of communication protocols ensues – TCP, or “transmission control protocol”, is developed and by 1978 the IP (inter-networking protocol) is added by Vint Cerf of Stanford, creating the network standard used today, TCP/IP. In 1974, the UNIX operating system is released by Bell labs, a ...
... standardization of communication protocols ensues – TCP, or “transmission control protocol”, is developed and by 1978 the IP (inter-networking protocol) is added by Vint Cerf of Stanford, creating the network standard used today, TCP/IP. In 1974, the UNIX operating system is released by Bell labs, a ...
Week-10.3-2
... use to connect a home computer to the Internet – A phone modem converts computer data into an analog audio signal for transfer over a telephone line, and then a modem at the destination converts it back again into data – A digital subscriber line (DSL) uses regular copper phone lines to transfer dig ...
... use to connect a home computer to the Internet – A phone modem converts computer data into an analog audio signal for transfer over a telephone line, and then a modem at the destination converts it back again into data – A digital subscriber line (DSL) uses regular copper phone lines to transfer dig ...
CCNA1 3.0-11 TCPIP Transport & Application Layers
... provides best-effort delivery across a network. TCP operates at Layer 4, and is a connection-oriented service that provides flow control as well as reliability. By pairing these protocols, a wider range of services is provided. ...
... provides best-effort delivery across a network. TCP operates at Layer 4, and is a connection-oriented service that provides flow control as well as reliability. By pairing these protocols, a wider range of services is provided. ...
Backbone: the main connecting cable that runs from one end of the
... single organization such as a university, company, or government institution. Each domain is an autonomous system that can be configured as the local authority desires, perhaps even as a global collection of WANs. Dotted Decimal- IP address are traditionally written in dotted decimal notation in whi ...
... single organization such as a university, company, or government institution. Each domain is an autonomous system that can be configured as the local authority desires, perhaps even as a global collection of WANs. Dotted Decimal- IP address are traditionally written in dotted decimal notation in whi ...
Chapter One
... Switches Subdivide a network into smaller logical pieces Create multiple, smaller collision domains In a half duplex switched network there are only two devices in each collision domain. In a full-duplex switched environment there is only 1 device in each collision domain (0 % chance of collision) ...
... Switches Subdivide a network into smaller logical pieces Create multiple, smaller collision domains In a half duplex switched network there are only two devices in each collision domain. In a full-duplex switched environment there is only 1 device in each collision domain (0 % chance of collision) ...
Document
... 0 : physical network transmission bandwidth i : max packet length of i-th layer I : packet header length of i-th layer ni : data length of i-th layer i : calling expense (routing,traffic control, error detecting, buffer management, connection maintaining) ...
... 0 : physical network transmission bandwidth i : max packet length of i-th layer I : packet header length of i-th layer ni : data length of i-th layer i : calling expense (routing,traffic control, error detecting, buffer management, connection maintaining) ...
Layer Number Layer Designation Function Responsibility Page
... Routers use the logical address in a network layer header to determine the next hop router to forward the packet to Routers can use access lists, created by an administrator, to control security on the types of packets that are allowed to enter or exit an interface Routers can provide layer 2 bridgi ...
... Routers use the logical address in a network layer header to determine the next hop router to forward the packet to Routers can use access lists, created by an administrator, to control security on the types of packets that are allowed to enter or exit an interface Routers can provide layer 2 bridgi ...
BOOTP Packet Format - Texas Tech University
... • Describes the format a message must take • Enables multi-platform computers to communicate ...
... • Describes the format a message must take • Enables multi-platform computers to communicate ...
20040720-SURFnet6-Radius
... • SURFnet5 is still world leading network, but… – NREN users need new services that current networks cannot support – Data communication infrastructures will become part of the Grid and will be integrated in scientific instruments – Hybrid networks delivering IP and Lambda Services can meet user dem ...
... • SURFnet5 is still world leading network, but… – NREN users need new services that current networks cannot support – Data communication infrastructures will become part of the Grid and will be integrated in scientific instruments – Hybrid networks delivering IP and Lambda Services can meet user dem ...
View File
... … specific msgs sent … specific actions taken when msgs received, or other events network protocols: machines rather than humans all communication activity in Internet governed by protocols ...
... … specific msgs sent … specific actions taken when msgs received, or other events network protocols: machines rather than humans all communication activity in Internet governed by protocols ...
Ports and IPv6
... Present IPv4 is used This is 32 bits, and has about 4,300,000,000 address spaces (2^32 – 1) IPv6 is started to be implemented. IPv6 is 128 bits giving 3.4 x 10^38 ...
... Present IPv4 is used This is 32 bits, and has about 4,300,000,000 address spaces (2^32 – 1) IPv6 is started to be implemented. IPv6 is 128 bits giving 3.4 x 10^38 ...
Chapter 36 Network Management & SNMP
... client application program (manager) runs on network management computer Server process (agent) listens on UDP port 161 on network device ...
... client application program (manager) runs on network management computer Server process (agent) listens on UDP port 161 on network device ...
IP_tec - iptel.org
... based on what information (hops, delay, cost, ...) ? how often does it change (hop vs. delay)? where is routing information stored? algorithm used to compute routes? ...
... based on what information (hops, delay, cost, ...) ? how often does it change (hop vs. delay)? where is routing information stored? algorithm used to compute routes? ...
MM_Introduction
... based on what information (hops, delay, cost, ...) ? how often does it change (hop vs. delay)? where is routing information stored? algorithm used to compute routes? ...
... based on what information (hops, delay, cost, ...) ? how often does it change (hop vs. delay)? where is routing information stored? algorithm used to compute routes? ...
William Stallings Data and Computer Communications
... • Usually owned by same organization as attached devices • Data rates much higher • Usually broadcast systems • Now some switched systems and ATM are being introduced ...
... • Usually owned by same organization as attached devices • Data rates much higher • Usually broadcast systems • Now some switched systems and ATM are being introduced ...
How Client/Server Networks Work
... here’s a good chance the office computer you use to access data and files, send e-mail, access the Internet, and print out reports is a small piece of a larger puzzle known as a network. Whether it involves two computers connected by a cable or hundreds of computers linked by telephone lines, networ ...
... here’s a good chance the office computer you use to access data and files, send e-mail, access the Internet, and print out reports is a small piece of a larger puzzle known as a network. Whether it involves two computers connected by a cable or hundreds of computers linked by telephone lines, networ ...
Recursive InterNetwork Architecture (RINA)

The Recursive InterNetwork Architecture (RINA) is a computer network architecture that unifies distributed computing and telecommunications. RINA's fundamental principle is that computer networking is just Inter-Process Communication or IPC. RINA reconstructs the overall structure of the Internet, forming a model that comprises a single repeating layer, the DIF (Distributed IPC Facility), which is the minimal set of components required to allow distributed IPC between application processes. RINA inherently supports mobility, multi-homing and Quality of Service without the need for extra mechanisms, provides a secure and programmable environment, motivates for a more competitive marketplace, and allows for a seamless adoption.