Check Your Understanding Chapter 7 Part 1 For a quick review to
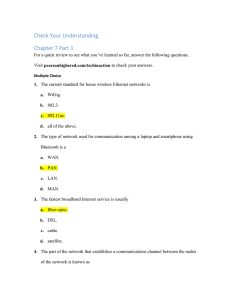
... 1. The current standard for home wireless Ethernet networks is a. WiGig. b. 802.3. c. 802.11ac. d. all of the above. 2. The type of network used for communication among a laptop and smartphone using Bluetooth is a a. WAN. b. PAN. c. LAN. d. MAN. 3. The fastest broadband Internet service is usually a ...
... 1. The current standard for home wireless Ethernet networks is a. WiGig. b. 802.3. c. 802.11ac. d. all of the above. 2. The type of network used for communication among a laptop and smartphone using Bluetooth is a a. WAN. b. PAN. c. LAN. d. MAN. 3. The fastest broadband Internet service is usually a ...
Chapter 4 Computer Networks – Part 2
... for longer range wireless networking connections. Mobile WiMAX is the mobile version of the WiMAX wireless networking standard. ...
... for longer range wireless networking connections. Mobile WiMAX is the mobile version of the WiMAX wireless networking standard. ...
Wireless Networking
... Essentially, this technology is a variation of the IEEE 802.11 specification known as 802.11b Focuses on Direct-Sequence Spread Spectrum (DSSS) ...
... Essentially, this technology is a variation of the IEEE 802.11 specification known as 802.11b Focuses on Direct-Sequence Spread Spectrum (DSSS) ...
Wireless Multi-Client Bridge/AP 2611CB3 PLUS (Deluxe) 2.4 GHz
... (2.4GHz, 11Mbps) wireless standard. It's the best way to add wireless capability to your existing wired network, or to add bandwidth to your wireless installation. To protect your wireless connectivity, it can encrypt all wireless transmissions through 64/128-bit WEP data encryption. The MAC address ...
... (2.4GHz, 11Mbps) wireless standard. It's the best way to add wireless capability to your existing wired network, or to add bandwidth to your wireless installation. To protect your wireless connectivity, it can encrypt all wireless transmissions through 64/128-bit WEP data encryption. The MAC address ...
Tsou_2003AAG. ppt - Internet Mapping Services for San Diego
... – There is a strong need to develop an easy-to-use, inexpensive set of field survey tools ...
... – There is a strong need to develop an easy-to-use, inexpensive set of field survey tools ...
rural access in Nepal
... it is economically viable to use wireless IP network Depending on appropriate low-cost antennae, wireless bridges, access points, Wi-Fi networks can be one of cost-effective options Rural Digital Library aims to respond to demand for ICT services to rural communities. Grid of Wi-Fi links between rur ...
... it is economically viable to use wireless IP network Depending on appropriate low-cost antennae, wireless bridges, access points, Wi-Fi networks can be one of cost-effective options Rural Digital Library aims to respond to demand for ICT services to rural communities. Grid of Wi-Fi links between rur ...
Giuseppe Razzano , Neeli R. Prasad , Roberto De Paolis
... 802.11i is the new version of the standard, finalized in 2004 by IEEE Taskgroup i, with the aim of solving the weaknesses of WEP-based wireless security. Substantial components of the 802.11i standard were already released before the standard was released and products are available on the market, un ...
... 802.11i is the new version of the standard, finalized in 2004 by IEEE Taskgroup i, with the aim of solving the weaknesses of WEP-based wireless security. Substantial components of the 802.11i standard were already released before the standard was released and products are available on the market, un ...
Wireless Multi-Client Bridge/AP 2611CB3 PLUS (Deluxe)
... The Wireless Multi-Client Bridge/Access Point operates in the 2.4 GHz frequency spectrum supporting the 802.11b (2.4GHz, 11Mbps) wireless standards. It's the best way to add wireless capability to your existing wired network, or to add bandwidth to your wireless installation. To protect your wireles ...
... The Wireless Multi-Client Bridge/Access Point operates in the 2.4 GHz frequency spectrum supporting the 802.11b (2.4GHz, 11Mbps) wireless standards. It's the best way to add wireless capability to your existing wired network, or to add bandwidth to your wireless installation. To protect your wireles ...
SpeedTouch™ 585(i) v6
... freedom at lightning-fast speeds. The SpeedTouch 585(i) is an 802.11a/g wireless LAN access point with integrated ADSL. Featuring an integrated 10/100Mb/s 4-port switch, the SpeedTouch 585(i) offers seamless connection of wired and wireless worlds from anywhere in the home. The SpeedTouch 585(i) let ...
... freedom at lightning-fast speeds. The SpeedTouch 585(i) is an 802.11a/g wireless LAN access point with integrated ADSL. Featuring an integrated 10/100Mb/s 4-port switch, the SpeedTouch 585(i) offers seamless connection of wired and wireless worlds from anywhere in the home. The SpeedTouch 585(i) let ...
Infrastructure Provider Company Embraced BYOD and Faced
... devices, publishing the security policies and compliance requirements. The most important aspect was to conditionally apply the policies while connected to corporate network through Wi-Fi based Geo-Fence solution provided by 1Mobility. This allows specific restrictions to be applied on the devices w ...
... devices, publishing the security policies and compliance requirements. The most important aspect was to conditionally apply the policies while connected to corporate network through Wi-Fi based Geo-Fence solution provided by 1Mobility. This allows specific restrictions to be applied on the devices w ...
Power Point - Toronto Users Group
... • 900 MHz (cordless telephones, proprietary wireless) • 2.4 GHz (cordless telephones, microwave ovens, Bluetooth, 802.11b, 802.11g) • 5.8 GHz (cordless telephones) ...
... • 900 MHz (cordless telephones, proprietary wireless) • 2.4 GHz (cordless telephones, microwave ovens, Bluetooth, 802.11b, 802.11g) • 5.8 GHz (cordless telephones) ...
Wi-Fi structure
... – CHANGE the SSID -- Vendors typically set the SSID of products to a simple, generic name, like the company name or “default” – Good Security: Pick a hard-to-guess SSID, such as a mix of letters and numbers with no obvious identifying logic. ...
... – CHANGE the SSID -- Vendors typically set the SSID of products to a simple, generic name, like the company name or “default” – Good Security: Pick a hard-to-guess SSID, such as a mix of letters and numbers with no obvious identifying logic. ...
www.sunvistacomputerclub.com
... AP, log in, and select the encryption method and passphrase. To find the IP address that is needed, select “start/run”, put “cmd.exe” in the box, and click “Ok”. In the window that pops up, type “ipconfig /all”. The address listed as the “Default gateway” for the wired interface is what you need.. ...
... AP, log in, and select the encryption method and passphrase. To find the IP address that is needed, select “start/run”, put “cmd.exe” in the box, and click “Ok”. In the window that pops up, type “ipconfig /all”. The address listed as the “Default gateway” for the wired interface is what you need.. ...
09-0226 MBR1100 Data Sheet.ai
... built-in failover capability, the MBR1100 automatically switches to a secondary ISP (either wired or wireless) networking when the primary ISP service is interrupted. Once service is restored, the MBR1100 will automatically failback to the primary wired ISP keeping your business online without inter ...
... built-in failover capability, the MBR1100 automatically switches to a secondary ISP (either wired or wireless) networking when the primary ISP service is interrupted. Once service is restored, the MBR1100 will automatically failback to the primary wired ISP keeping your business online without inter ...
Wi-Fi
... The obstacle itself is not relevant; it could be as simple as nodes 1 and 3 being as far away from 2 as possible, so the radio waves cannot reach the full distance from 1 to 3. From the perspective of node 1, node 3 is a "hidden" node. If a simple transmit-and-pray protocol was used, it would be eas ...
... The obstacle itself is not relevant; it could be as simple as nodes 1 and 3 being as far away from 2 as possible, so the radio waves cannot reach the full distance from 1 to 3. From the perspective of node 1, node 3 is a "hidden" node. If a simple transmit-and-pray protocol was used, it would be eas ...
SkyExtender DualBand
... The SkyExtender™ DualBand’s unique integration of a long-range mesh backhaul and industry-standard 802.11 access point gives service providers great flexibility when deploying Wi-Fi access networks. With the extended range of the mesh backhaul, Wi-Fi can be deployed in dense coverage patterns, like ...
... The SkyExtender™ DualBand’s unique integration of a long-range mesh backhaul and industry-standard 802.11 access point gives service providers great flexibility when deploying Wi-Fi access networks. With the extended range of the mesh backhaul, Wi-Fi can be deployed in dense coverage patterns, like ...
Vi-Card
... LED indication of supply power, USB connection, SD card access, interface & Wi-Fi Status. ...
... LED indication of supply power, USB connection, SD card access, interface & Wi-Fi Status. ...
weather parameters_IoT
... exchange data with each other by using wireless sensor networks. Embedded systems play a vital role in IoT; these embedded systems use an admixture of digital and analog subsystems in gathering information from sensors. In such a complex scenario, the application of the IoT paradigm shift towards me ...
... exchange data with each other by using wireless sensor networks. Embedded systems play a vital role in IoT; these embedded systems use an admixture of digital and analog subsystems in gathering information from sensors. In such a complex scenario, the application of the IoT paradigm shift towards me ...
Chapter 8 Power Point Solutions Define communications including
... Chapter 8 Power Point Solutions 1. Define communications including connectivity, the wireless revolution, and communication systems. Computer communications is the process of sharing data, programs and information between two or more computers. Connectivity uses computer networks to link people and ...
... Chapter 8 Power Point Solutions 1. Define communications including connectivity, the wireless revolution, and communication systems. Computer communications is the process of sharing data, programs and information between two or more computers. Connectivity uses computer networks to link people and ...
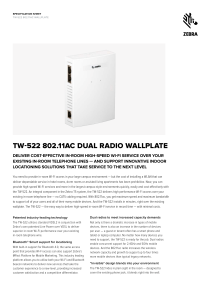
TW-522 802.11ac Dual Radio Wallplate Specification Sheet
... per user — a guest or tenant often has a smart phone and tablet or laptop computer. No matter how many devices you need to support, the TW-522 is ready for the job. Dual radios enable concurrent support for 2.4GHz and 5GHz mobile devices. And the 802.11ac radio increases the wireless network capacit ...
... per user — a guest or tenant often has a smart phone and tablet or laptop computer. No matter how many devices you need to support, the TW-522 is ready for the job. Dual radios enable concurrent support for 2.4GHz and 5GHz mobile devices. And the 802.11ac radio increases the wireless network capacit ...
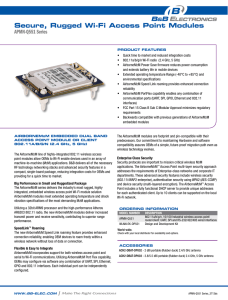
apMn-Q551
... • AirborneM2M Power Save firmware reduces power consumption and extends battery life in mobile devices • Extended operating temperature Range (-40°C to +85°C) and environmental specifications • AirborneM2M Speed Link roaming provides enhanced connection reliability • AirborneM2M PortF ...
... • AirborneM2M Power Save firmware reduces power consumption and extends battery life in mobile devices • Extended operating temperature Range (-40°C to +85°C) and environmental specifications • AirborneM2M Speed Link roaming provides enhanced connection reliability • AirborneM2M PortF ...
Wi-Fi
Wi-Fi (or WiFi) is a local area wireless computer networking technology that allows electronic devices to network, mainly using the 2.4 gigahertz (12 cm) UHF and 5 gigahertz (6 cm) SHF ISM radio bands.The Wi-Fi Alliance defines Wi-Fi as any ""wireless local area network"" (WLAN) product based on the Institute of Electrical and Electronics Engineers' (IEEE) 802.11 standards. However, the term ""Wi-Fi"" is used in general English as a synonym for ""WLAN"" since most modern WLANs are based on these standards. ""Wi-Fi"" is a trademark of the Wi-Fi Alliance. The ""Wi-Fi Certified"" trademark can only be used by Wi-Fi products that successfully complete Wi-Fi Alliance interoperability certification testing.Many devices can use Wi-Fi, e.g. personal computers, video-game consoles, smartphones, digital cameras, tablet computers and digital audio players. These can connect to a network resource such as the Internet via a wireless network access point. Such an access point (or hotspot) has a range of about 20 meters (66 feet) indoors and a greater range outdoors. Hotspot coverage can be as small as a single room with walls that block radio waves, or as large as many square kilometres achieved by using multiple overlapping access points. Wi-Fi can be less secure than wired connections, such as Ethernet, precisely because an intruder does not need a physical connection. Web pages that use TLS are secure, but unencrypted internet access can easily be detected by intruders. Because of this, Wi-Fi has adopted various encryption technologies. The early encryption WEP proved easy to break. Higher quality protocols (WPA, WPA2) were added later. An optional feature added in 2007, called Wi-Fi Protected Setup (WPS), had a serious flaw that allowed an attacker to recover the router's password. The Wi-Fi Alliance has since updated its test plan and certification program to ensure all newly certified devices resist attacks.