What is a Network?
... • A network is a group of computers and other devices (such as printers) that are connected by some type of transmission media. • Networks may be as small as two computers connected by a cable in a home office or as large as several thousand computers connected across the world via a combination of ...
... • A network is a group of computers and other devices (such as printers) that are connected by some type of transmission media. • Networks may be as small as two computers connected by a cable in a home office or as large as several thousand computers connected across the world via a combination of ...
Connected Devices Interfacing (CDI)
... services the means to optimally exploit the network capabilities, by means of the implementation of APIs towards networking elements NetIC will provide an abstraction of the physical network resources, as well as the capability to control them (up to certain limitations given by the physical resour ...
... services the means to optimally exploit the network capabilities, by means of the implementation of APIs towards networking elements NetIC will provide an abstraction of the physical network resources, as well as the capability to control them (up to certain limitations given by the physical resour ...
Charles Whitfield Jr
... Served as a member of the Network Lab Control team. Network Lab Technician successfully designed, implemented, and monitored maintenance of the Network Elements of Lucent’s Wavestar Optical Line System OLS (A dense Wavelength division Multiplexer with the capacity to transport up to 80 signals). Add ...
... Served as a member of the Network Lab Control team. Network Lab Technician successfully designed, implemented, and monitored maintenance of the Network Elements of Lucent’s Wavestar Optical Line System OLS (A dense Wavelength division Multiplexer with the capacity to transport up to 80 signals). Add ...
... Permanent Secretaries and Heads of Departments are asked to invite applications from suitably qualified officers in their Ministries/Departments to fill the post of Network Manager (MIS/IT 6) in the Information Communication and Technology Branch, Ministry of Transport Works and Housing, salary rang ...
No Slide Title
... • iBGP when used as IGP • carries global routes around network • injected with eircom customer routes ...
... • iBGP when used as IGP • carries global routes around network • injected with eircom customer routes ...
Boolean network (BN) has been a powerful tool for system biology
... neural network, social network, multiagent systems, and so on. These applications are based on the identification of the BNs. But it is difficult to identify the BNs directly due to the lack of tools for the logical system. ...
... neural network, social network, multiagent systems, and so on. These applications are based on the identification of the BNs. But it is difficult to identify the BNs directly due to the lack of tools for the logical system. ...
Introduction to Networking & telecommunications
... Packets are short (averaging a few hundred bytes) because networking devices handle short messages more efficiently ...
... Packets are short (averaging a few hundred bytes) because networking devices handle short messages more efficiently ...
Chapter 3
... systems “on the same page” asynchronous - start signal is sent, then a character, then a stop signal – receiving system sets up a timing mechanism ...
... systems “on the same page” asynchronous - start signal is sent, then a character, then a stop signal – receiving system sets up a timing mechanism ...
Extended Learning Module E
... Your wireless signal reaches beyond your walls Many wireless networks are vulnerable to eavesdropping (sniffing) Not all security methods are robust Unauthorized internal access points Laptops may automatically connect to networks they previously connected to Rogue (evil twin) access points nearby ...
... Your wireless signal reaches beyond your walls Many wireless networks are vulnerable to eavesdropping (sniffing) Not all security methods are robust Unauthorized internal access points Laptops may automatically connect to networks they previously connected to Rogue (evil twin) access points nearby ...
foundationsChap1
... ◦ Multiplex a single bus/wire/channel across multiple hosts ◦ Limitations :geographical distance limitations and number of nodes connected. All styles of Networks must cope with Scalability ...
... ◦ Multiplex a single bus/wire/channel across multiple hosts ◦ Limitations :geographical distance limitations and number of nodes connected. All styles of Networks must cope with Scalability ...
Lecture 2 Digital Data Representation (1)
... INTENDED LEARNING OUTCOMES This lecture covers: Networking concepts and terminology Common networking and communications applications Technical issues related to networks, including the major types of ...
... INTENDED LEARNING OUTCOMES This lecture covers: Networking concepts and terminology Common networking and communications applications Technical issues related to networks, including the major types of ...
MAN Metropolitan Area Network = A metropolitan
... PAN Personal area network = PAN - is a computer network organized around an individual person. PROTOCOL In information technology, a protocol is the special set of rules that end points in a telecommunication connection use when they communicate. FIREWALL In computing, a firewall is a network securi ...
... PAN Personal area network = PAN - is a computer network organized around an individual person. PROTOCOL In information technology, a protocol is the special set of rules that end points in a telecommunication connection use when they communicate. FIREWALL In computing, a firewall is a network securi ...
CS 294-7: Introduction to Packet Radio Networks
... – Routing: choosing routes based on link connectivity » Routing schemes: • Flooding methods--inefficient utilization, but simple and may be best strategy for rapidly changing network topologies • Point-to-Point Routing--sequence of links associated with src-dst pair AKA “connection-oriented” routing ...
... – Routing: choosing routes based on link connectivity » Routing schemes: • Flooding methods--inefficient utilization, but simple and may be best strategy for rapidly changing network topologies • Point-to-Point Routing--sequence of links associated with src-dst pair AKA “connection-oriented” routing ...
Job Description - Members First Credit Union
... Provide technical expertise as a team member in the development and operational support of the core infrastructure systems and services. Lead the design, test, and deployment of new or enhanced network services, both physically and virtually. Perform server troubleshooting and triage during service ...
... Provide technical expertise as a team member in the development and operational support of the core infrastructure systems and services. Lead the design, test, and deployment of new or enhanced network services, both physically and virtually. Perform server troubleshooting and triage during service ...
annual meeting of shareholders confirms corporate
... Vienna, Strasbourg, Berlin, Hamburg, Munich, Memmingen, Karlsruhe, Düsseldorf and Mönchengladbach. Now, GRENKE will be able to connect as many locations in Europe as required. As soon as an additional location is hooked up, it is able to communicate with all the other locations. As a result, GRENKE ...
... Vienna, Strasbourg, Berlin, Hamburg, Munich, Memmingen, Karlsruhe, Düsseldorf and Mönchengladbach. Now, GRENKE will be able to connect as many locations in Europe as required. As soon as an additional location is hooked up, it is able to communicate with all the other locations. As a result, GRENKE ...
tutorial 1 - Portal UniMAP
... 5. What is the business case for voice and data network convergence? Since PDNs were overwhelmingly used for data transmission alone, the average business customer needed two distinct networks: the telephone system for voice, and PDN for computer connections. Using and maintaining two separate netwo ...
... 5. What is the business case for voice and data network convergence? Since PDNs were overwhelmingly used for data transmission alone, the average business customer needed two distinct networks: the telephone system for voice, and PDN for computer connections. Using and maintaining two separate netwo ...
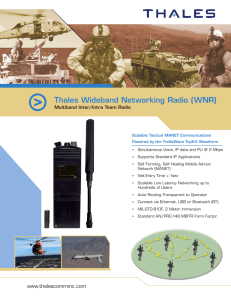
Thales Wideband Networking Radio (WNR)
... communications unit. It is designed to provide robust voice and data communication in the most challenging RF environments. This unique tactical Mobile Ad-Hoc Networking (MANET) product enables rapid deployment of high throughput networks across the harshest conditions. The Thales WNR PHY and MAC la ...
... communications unit. It is designed to provide robust voice and data communication in the most challenging RF environments. This unique tactical Mobile Ad-Hoc Networking (MANET) product enables rapid deployment of high throughput networks across the harshest conditions. The Thales WNR PHY and MAC la ...
Optical Packet/Burst Switching
... problems such as low resource utilization and large recovery times after changes in the network topology or in the traffic demand. ...
... problems such as low resource utilization and large recovery times after changes in the network topology or in the traffic demand. ...