An upper level management position in Information
... corporate website. SOCworks, a division of Sonics, provides web accessible application services using semiconductor design tools developed by Sonics. That infrastructure consisted of a combination of VALinux, Dell and Sun hardware running a VALinux modified version of RedHat 6.2, RedHat 7.1, and Sol ...
... corporate website. SOCworks, a division of Sonics, provides web accessible application services using semiconductor design tools developed by Sonics. That infrastructure consisted of a combination of VALinux, Dell and Sun hardware running a VALinux modified version of RedHat 6.2, RedHat 7.1, and Sol ...
Fondamenti di Internet: “Aspetti pratici delle reti di telecomunicazioni ”
... lclean: removes temporary files from a lab directory linfo: provides information about a lab without starting it ltest: allows to run tests to check that the lab is working properly ...
... lclean: removes temporary files from a lab directory linfo: provides information about a lab without starting it ltest: allows to run tests to check that the lab is working properly ...
“VoxNet: An Interactive, Rapidly-Deployable Acoustic Monitoring Platform,”
... important class of sensor network applications, from habitat monitoring and bioacoustic census to security applications and virtual fences. VoxNet is a complete hardware and software platform for distributed acoustic monitoring applications that focuses on three key goals: (1) rapid deployment in re ...
... important class of sensor network applications, from habitat monitoring and bioacoustic census to security applications and virtual fences. VoxNet is a complete hardware and software platform for distributed acoustic monitoring applications that focuses on three key goals: (1) rapid deployment in re ...
3rd Edition: Chapter 2 - Northwestern Networks Group
... Packet switching allows more users to use network! r 1 Mbit link r Each user: m 100 kbps when “active” m active 10% of time r Circuit-switching: m 10 users ...
... Packet switching allows more users to use network! r 1 Mbit link r Each user: m 100 kbps when “active” m active 10% of time r Circuit-switching: m 10 users ...
View File
... V sends a syn+ack to X X discards syn+ack leaving an half open connection at V. Many open connections exhausts resources at V ⇒ DoS ...
... V sends a syn+ack to X X discards syn+ack leaving an half open connection at V. Many open connections exhausts resources at V ⇒ DoS ...
What is data communication? - Information Systems
... • LANs normally offer much higher data transmission rates than WANs. – This difference is apparent in the network oriented protocols only. ...
... • LANs normally offer much higher data transmission rates than WANs. – This difference is apparent in the network oriented protocols only. ...
Data Link Layer
... so that if there is a network failure only the data sent after the checkpoint must be resent Provides name recognition and security needed to allow two applications to communicate ...
... so that if there is a network failure only the data sent after the checkpoint must be resent Provides name recognition and security needed to allow two applications to communicate ...
What is the Network
... computers with private IP addresses to connect to the Internet. • The NAT router maps private to public addresses and vice versa. • Security feature of NAT – Hides hosts on private networks ...
... computers with private IP addresses to connect to the Internet. • The NAT router maps private to public addresses and vice versa. • Security feature of NAT – Hides hosts on private networks ...
ANANDH.C.BOSE Email Id: Career
... 3. Seminar : DIN loop Based Inter-domain Multicast with MPLS Description: To overcome the existing scalability problems, DIN loop (Data-In-Network loop) based multicast with MPLS (multiprotocol label switching) is proposed to optimize inter-domain multicast. In this, multiple DIN Nodes in the core n ...
... 3. Seminar : DIN loop Based Inter-domain Multicast with MPLS Description: To overcome the existing scalability problems, DIN loop (Data-In-Network loop) based multicast with MPLS (multiprotocol label switching) is proposed to optimize inter-domain multicast. In this, multiple DIN Nodes in the core n ...
Transport Protocols for Wireless Multimedia Sensor Network
... Monitors the physiological status of the wearer and transmits the information to the medical professional over the Internet Nose-on-a-chip It is a MEMS-based sensor It can detect 400 species of gases and transmit a signal indicating the level to a ...
... Monitors the physiological status of the wearer and transmits the information to the medical professional over the Internet Nose-on-a-chip It is a MEMS-based sensor It can detect 400 species of gases and transmit a signal indicating the level to a ...
How to Check a M580 ERIO System for Cabling Errors CRC errors
... How to Check a M580 ERIO System for Cabling Errors CRC errors are good indicators of hardware level faults like interference or cabling mistakes. In distributed IO networks this information is accessible via web interface on ConneXium managed switches but in an Ethernet Remote IO network these switc ...
... How to Check a M580 ERIO System for Cabling Errors CRC errors are good indicators of hardware level faults like interference or cabling mistakes. In distributed IO networks this information is accessible via web interface on ConneXium managed switches but in an Ethernet Remote IO network these switc ...
Niall Robinson
... IP Over DWDM : The Next Step Building a data-centric network free of bandwidth restrictions and spatial boundaries ...
... IP Over DWDM : The Next Step Building a data-centric network free of bandwidth restrictions and spatial boundaries ...
Introduction
... Packetswitched networks. Multipleaccess Networks. Layered architecture, ARPANET. Internet. OSI model Integrated services. ATM. ...
... Packetswitched networks. Multipleaccess Networks. Layered architecture, ARPANET. Internet. OSI model Integrated services. ATM. ...
pptx - University of Pittsburgh
... Not guaranteed to converge to zero training error, may converge to local optima or oscillate indefinitely. However, in practice, does converge to low error for many large networks on real data. Thousands of epochs (epoch = network sees all training data once) may be required, hours or days to train. ...
... Not guaranteed to converge to zero training error, may converge to local optima or oscillate indefinitely. However, in practice, does converge to low error for many large networks on real data. Thousands of epochs (epoch = network sees all training data once) may be required, hours or days to train. ...
A Survey of Energy efficient Network Protocols for Wireless Networks
... • Same priority of operation of mobiles so that all mobiles remain powered for as long as possible. • Packet cost: Do not route packets through low power mobile routes. ...
... • Same priority of operation of mobiles so that all mobiles remain powered for as long as possible. • Packet cost: Do not route packets through low power mobile routes. ...
Why the SurfBeam System Should Be Your Internet
... working to transform satellite broadband with ViaSat-1, expected to be the world’s largest capacity broadband satellite. In addition to satellites and ground system technology, our technical staff focuses on this challenge from many other angles. Data processing and acceleration techniques, more eff ...
... working to transform satellite broadband with ViaSat-1, expected to be the world’s largest capacity broadband satellite. In addition to satellites and ground system technology, our technical staff focuses on this challenge from many other angles. Data processing and acceleration techniques, more eff ...
Network protocols
... This protocol is used to automatically assign IP addresses to “hosts” or work stations on a network. A DHCP server is normally configured to perform this task. BIT 1102: Communications Technology & the Internet ...
... This protocol is used to automatically assign IP addresses to “hosts” or work stations on a network. A DHCP server is normally configured to perform this task. BIT 1102: Communications Technology & the Internet ...
ecs251_w2013_final
... computer scientists specializing in parallel databases and shared-nothing architectures, have been critical of the breadth of problems that MapReduce can be used for. They called its interface too lowlevel and questioned whether it really represents the paradigm shift its proponents have claimed it ...
... computer scientists specializing in parallel databases and shared-nothing architectures, have been critical of the breadth of problems that MapReduce can be used for. They called its interface too lowlevel and questioned whether it really represents the paradigm shift its proponents have claimed it ...
LAN design
... • Redistributes less optimal protocols to maintain optimal protocols across the core • Uses summarised routes to core to simplify routing tables ...
... • Redistributes less optimal protocols to maintain optimal protocols across the core • Uses summarised routes to core to simplify routing tables ...
The Network - Communication Management Services
... compared to total number of sessions established on the Network during a calendar month ...
... compared to total number of sessions established on the Network during a calendar month ...
Introduction - School of Electrical Engineering and Computer Science
... Node 1 uses random number to encrypted the public key of node 2 Node 2 decrypted the message using its private key From the random number, both node can encrypt and decrypt the data ...
... Node 1 uses random number to encrypted the public key of node 2 Node 2 decrypted the message using its private key From the random number, both node can encrypt and decrypt the data ...
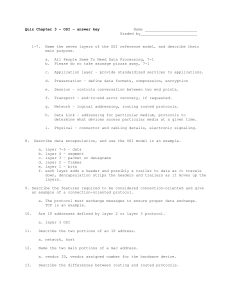
Quiz on ICND chapter 3
... 9. Describe the features required to be considered connection-oriented and give an example of a connection-oriented protocol. a. The protocol must exchange messages to ensure proper data exchange. ...
... 9. Describe the features required to be considered connection-oriented and give an example of a connection-oriented protocol. a. The protocol must exchange messages to ensure proper data exchange. ...
PowerPoint
... and C. Nodes A and C want to exchange information through the middle node B. Node A first transmits packet x to node B, and node C transmits packet y to node B. Node B broadcasts x XOR y (not x and y in sequence). Since node A has packet x, and node C has packet y, node A can decode y and node C can ...
... and C. Nodes A and C want to exchange information through the middle node B. Node A first transmits packet x to node B, and node C transmits packet y to node B. Node B broadcasts x XOR y (not x and y in sequence). Since node A has packet x, and node C has packet y, node A can decode y and node C can ...