White Hat Hacking Tyler Schumacher Department of Computer
... There are also black hat hackers who rely on little network security flaws or cracking software. They use social engineering techniques to gain physical access to areas they should not be allowed to get to or to learn passwords. There are a number of different social engineering techniques. A black ...
... There are also black hat hackers who rely on little network security flaws or cracking software. They use social engineering techniques to gain physical access to areas they should not be allowed to get to or to learn passwords. There are a number of different social engineering techniques. A black ...
Networking II
... • Install routing protocol such as OLSR on router • Terminal nodes should be in ad-hoc mode as well ...
... • Install routing protocol such as OLSR on router • Terminal nodes should be in ad-hoc mode as well ...
smesh.org
... • Half-duplex communication system between multiple participants that share a single communication channel. • Only one user is granted Permissionto-Speak at a time (floor-control). ...
... • Half-duplex communication system between multiple participants that share a single communication channel. • Only one user is granted Permissionto-Speak at a time (floor-control). ...
Networks and Networking
... Data Communications Hardware Cable modem – provides Internet access via cable television lines DSL (Digital Subscriber Line) – Internet access via special line provided by a telephone company Satellite modem – Internet access via communications satellite ...
... Data Communications Hardware Cable modem – provides Internet access via cable television lines DSL (Digital Subscriber Line) – Internet access via special line provided by a telephone company Satellite modem – Internet access via communications satellite ...
lecture13 - Academic Server| Cleveland State University
... A client broadcasts to 255.255.255.255 The source IP address is set to 0.0.0.0 if client does not know its own IP address yet Port number: 67 for server, 68 for client Requires manual configuration of tables mapping IP address to Ethernet address at the BOOTP server ...
... A client broadcasts to 255.255.255.255 The source IP address is set to 0.0.0.0 if client does not know its own IP address yet Port number: 67 for server, 68 for client Requires manual configuration of tables mapping IP address to Ethernet address at the BOOTP server ...
OSS Licence Components Description
... This document describes the various components of a Pronto UniFi OSS. The Pronto Networks UniFi OSS is deployed using a group of servers. These functions include a Web Services Server for authenticating users, a Customer Portal server furnishing web pages to clients, Operations Support Services serv ...
... This document describes the various components of a Pronto UniFi OSS. The Pronto Networks UniFi OSS is deployed using a group of servers. These functions include a Web Services Server for authenticating users, a Customer Portal server furnishing web pages to clients, Operations Support Services serv ...
TCP 00F0 90 90 90 90 90 90 90 90 90 90 90 90 90 90 90 90
... worm from the infected host to the new target. Used authentication! To prevent sys admins from tampering with loaded code. If there was a transmission error, the loader would erase its tracks and exit. ...
... worm from the infected host to the new target. Used authentication! To prevent sys admins from tampering with loaded code. If there was a transmission error, the loader would erase its tracks and exit. ...
IP address
... large IP datagram are divided (“fragmented”) within net one datagram becomes several datagrams “reassembled” only at final destination IP header bits used to Adapted from: Computer Networking, Kurose/Ross identify, order related ...
... large IP datagram are divided (“fragmented”) within net one datagram becomes several datagrams “reassembled” only at final destination IP header bits used to Adapted from: Computer Networking, Kurose/Ross identify, order related ...
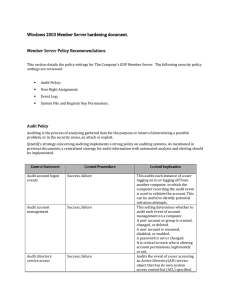
Server hardening - Cisco Security Solutions
... could mitigate the risk. However Microsoft set this by default on a default setup therfore this option does not need to be explicitly set (i.e not defined). Users with this privilege could expose sensitive data to the network by creating a new shared object. Do not assign this right to any users. Pr ...
... could mitigate the risk. However Microsoft set this by default on a default setup therfore this option does not need to be explicitly set (i.e not defined). Users with this privilege could expose sensitive data to the network by creating a new shared object. Do not assign this right to any users. Pr ...
Designing Protection System of LAN Security Bachelor’s Thesis (UAS)
... unpack all packets and steal critical information in Ethernet when they access to any node on the Ethernet to intercept. These are the security risks in Ethernet. Actually there are many free hacking tools in the Internet that could be intercept and attack a LAN. The current LAN security solutions a ...
... unpack all packets and steal critical information in Ethernet when they access to any node on the Ethernet to intercept. These are the security risks in Ethernet. Actually there are many free hacking tools in the Internet that could be intercept and attack a LAN. The current LAN security solutions a ...
Universal Communication Hub UCH
... The appropriate notification mechanism needs to be provisioned at the central Gateway Business Management System interface to allow proper operation. 2.1.1.2 Mobile Originated Fax Mobile Originated fax allows an off-the-shelf G3 fax machine to be used to send documents over the data network. After c ...
... The appropriate notification mechanism needs to be provisioned at the central Gateway Business Management System interface to allow proper operation. 2.1.1.2 Mobile Originated Fax Mobile Originated fax allows an off-the-shelf G3 fax machine to be used to send documents over the data network. After c ...
Multicasting in Mobile ad hoc networks
... Fast Handoff aims to reduce the handoff latency by using interaction between the radio and IP layers to detect the mobile movements. This can work only if the radio technology allows such interaction between layers.( its not solution for heterogenous wireless network) The packet loss during the hand ...
... Fast Handoff aims to reduce the handoff latency by using interaction between the radio and IP layers to detect the mobile movements. This can work only if the radio technology allows such interaction between layers.( its not solution for heterogenous wireless network) The packet loss during the hand ...
RIZZO - Security - Docbox
... Use cases, deployment modelling, protocol identification, validation of core security and privacy models Extension to non-NGN and non-Core functionality consistent with NGN and core functionality for local devices and their interfaces. ...
... Use cases, deployment modelling, protocol identification, validation of core security and privacy models Extension to non-NGN and non-Core functionality consistent with NGN and core functionality for local devices and their interfaces. ...
IOSR Journal of Computer Engineering (IOSR-JCE)
... wireless communication and has notched the top position in the wireless technology. But there still are a lot of securities concerns while using such wireless technologies, especially for Wimax where we have to transfer secure data at high rate from one station to another station. Wimax works at the ...
... wireless communication and has notched the top position in the wireless technology. But there still are a lot of securities concerns while using such wireless technologies, especially for Wimax where we have to transfer secure data at high rate from one station to another station. Wimax works at the ...
Networking Basics
... • If two devices send a message at the same time Collision!!! • If collision … then a) abort, b) wait a random time, and c) resend • Technical name for this process: ...
... • If two devices send a message at the same time Collision!!! • If collision … then a) abort, b) wait a random time, and c) resend • Technical name for this process: ...
Topology Patterns of a Community Network: Guifi.net
... Recall that the power law component of the complementary cumulative distribution function of a discrete random variable X is given by [21]: from table II we can see that from the 10,625 nodes of Catalunya base-graph, only 735 (around 7%) belong to the core-graph, the other nodes are terminals. The h ...
... Recall that the power law component of the complementary cumulative distribution function of a discrete random variable X is given by [21]: from table II we can see that from the 10,625 nodes of Catalunya base-graph, only 735 (around 7%) belong to the core-graph, the other nodes are terminals. The h ...
Secure Mobile IP with HIP Style Handshaking and
... the SPI associated with the new IP address. The whole handover process is protected by ESP, which prevents the third party bomb attack. There are three different types of address checking process[13]: 1. Readdress without re-keying, but with address check; 2. Readdress with mobile-initiated rekey; a ...
... the SPI associated with the new IP address. The whole handover process is protected by ESP, which prevents the third party bomb attack. There are three different types of address checking process[13]: 1. Readdress without re-keying, but with address check; 2. Readdress with mobile-initiated rekey; a ...
Safely Harnessing Wide Area Surrogate Computing -or-
... basic security policy for semi-trusted users is “trust, but verify”. Semi-trusted users’ network access is based on policies defined by the surrogate’s administrator. For example, a SkySurvey surrogate server might allow ratecontrolled access only to the IP address and port on which the database ser ...
... basic security policy for semi-trusted users is “trust, but verify”. Semi-trusted users’ network access is based on policies defined by the surrogate’s administrator. For example, a SkySurvey surrogate server might allow ratecontrolled access only to the IP address and port on which the database ser ...
Document
... Node failures do not affect the rest of the system Disadvantages All traffic passes through same hub, so network bandwidth is limited by hub speed ...
... Node failures do not affect the rest of the system Disadvantages All traffic passes through same hub, so network bandwidth is limited by hub speed ...
ZIGBEE GATEWAYS
... and leave a network, to apply security to frames and to route frames to their intended destinations. In addition, the discovery and maintenance of routes between devices devolve to the network layer. Also the discovery of one-hop neighbors and the storing of pertinent neighbor information are done a ...
... and leave a network, to apply security to frames and to route frames to their intended destinations. In addition, the discovery and maintenance of routes between devices devolve to the network layer. Also the discovery of one-hop neighbors and the storing of pertinent neighbor information are done a ...
Safely Harnessing Wide Area Surrogate Computing -or-
... basic security policy for semi-trusted users is “trust, but verify”. Semi-trusted users’ network access is based on policies defined by the surrogate’s administrator. For example, a SkySurvey surrogate server might allow ratecontrolled access only to the IP address and port on which the database ser ...
... basic security policy for semi-trusted users is “trust, but verify”. Semi-trusted users’ network access is based on policies defined by the surrogate’s administrator. For example, a SkySurvey surrogate server might allow ratecontrolled access only to the IP address and port on which the database ser ...
WLAN
... as the MAC addresses of clients (both wireless and wired), or to capture and disguise data packets, to gain access to network resources, or to launch man-in-the-middle (MITM) attacks. To prevent the installation of rogue APs, organizations must use monitoring software to actively monitor the radio ...
... as the MAC addresses of clients (both wireless and wired), or to capture and disguise data packets, to gain access to network resources, or to launch man-in-the-middle (MITM) attacks. To prevent the installation of rogue APs, organizations must use monitoring software to actively monitor the radio ...
Wireless security
.jpg?width=300)
Wireless security is the prevention of unauthorized access or damage to computers using wireless networks. The most common types of wireless security are Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). WEP is a notoriously weak security standard. The password it uses can often be cracked in a few minutes with a basic laptop computer and widely available software tools. WEP is an old IEEE 802.11 standard from 1999, which was outdated in 2003 by WPA, or Wi-Fi Protected Access. WPA was a quick alternative to improve security over WEP. The current standard is WPA2; some hardware cannot support WPA2 without firmware upgrade or replacement. WPA2 uses an encryption device that encrypts the network with a 256-bit key; the longer key length improves security over WEP.Many laptop computers have wireless cards pre-installed. The ability to enter a network while mobile has great benefits. However, wireless networking is prone to some security issues. Hackers have found wireless networks relatively easy to break into, and even use wireless technology to hack into wired networks. As a result, it is very important that enterprises define effective wireless security policies that guard against unauthorized access to important resources. Wireless Intrusion Prevention Systems (WIPS) or Wireless Intrusion Detection Systems (WIDS) are commonly used to enforce wireless security policies.The risks to users of wireless technology have increased as the service has become more popular. There were relatively few dangers when wireless technology was first introduced. Hackers had not yet had time to latch on to the new technology, and wireless networks were not commonly found in the work place. However, there are many security risks associated with the current wireless protocols and encryption methods, and in the carelessness and ignorance that exists at the user and corporate IT level. Hacking methods have become much more sophisticated and innovative with wireless access. Hacking has also become much easier and more accessible with easy-to-use Windows- or Linux-based tools being made available on the web at no charge.Some organizations that have no wireless access points installed do not feel that they need to address wireless security concerns. In-Stat MDR and META Group have estimated that 95% of all corporate laptop computers that were planned to be purchased in 2005 were equipped with wireless cards. Issues can arise in a supposedly non-wireless organization when a wireless laptop is plugged into the corporate network. A hacker could sit out in the parking lot and gather information from it through laptops and/or other devices, or even break in through this wireless card–equipped laptop and gain access to the wired network.