lesson17
... messaging system that enables SQL Server to communicate over the network. – Endpoints provide a reliable, securable, scalable messaging system that enables SQL Server to communicate over the network. – For database mirroring, a server instance requires its own dedicated database mirroring endpoint. ...
... messaging system that enables SQL Server to communicate over the network. – Endpoints provide a reliable, securable, scalable messaging system that enables SQL Server to communicate over the network. – For database mirroring, a server instance requires its own dedicated database mirroring endpoint. ...
View Project Report - DOC
... 3 RBAC for GIAC Enterprises 3.1 RBAC on a Small Scale Having limited resources, some companies may overlook the importance of clearly defined roles and responsibilities. Business continuity as well as future business expansion relies heavily on documented process and the ability to outline job funct ...
... 3 RBAC for GIAC Enterprises 3.1 RBAC on a Small Scale Having limited resources, some companies may overlook the importance of clearly defined roles and responsibilities. Business continuity as well as future business expansion relies heavily on documented process and the ability to outline job funct ...
Topology Control in Mobile Ad Hoc Networks with Cooperative
... decoding and then forward the decoding result to the destinations. If multiple nodes are available for cooperation, their antennas can employ a space-time code in transmitting the relay signals. It is shown that cooperation at the physical layer can achieve full levels of diversity similar to a MIMO ...
... decoding and then forward the decoding result to the destinations. If multiple nodes are available for cooperation, their antennas can employ a space-time code in transmitting the relay signals. It is shown that cooperation at the physical layer can achieve full levels of diversity similar to a MIMO ...
Wavenis Ecosystem - Integrator catalog
... Aresa was originally a national initiative led by Orange Lab. The project focused on largescale wireless sensor networks distributed throughout the area being monitored. The key goal of this research was to achieve low energy consumption for the overall system and its communications, which is why Wa ...
... Aresa was originally a national initiative led by Orange Lab. The project focused on largescale wireless sensor networks distributed throughout the area being monitored. The key goal of this research was to achieve low energy consumption for the overall system and its communications, which is why Wa ...
Basic Internetworking
... (c) Suppose we simply drop P, after sending out a query, when cache lookup fails. How would this behave? (Some early ARP implementations allegedly did this) CSS432: Internetworking ...
... (c) Suppose we simply drop P, after sending out a query, when cache lookup fails. How would this behave? (Some early ARP implementations allegedly did this) CSS432: Internetworking ...
Distributed Firewall
... To implement a distributed firewall, we need a security policy language that can describe which connections are acceptable, an authentication mechanism, and a policy distribution scheme. As a policy specification language, we use the KeyNote trust-management system, further described in Section 7.1. ...
... To implement a distributed firewall, we need a security policy language that can describe which connections are acceptable, an authentication mechanism, and a policy distribution scheme. As a policy specification language, we use the KeyNote trust-management system, further described in Section 7.1. ...
September 2012
... require remote management of their functionality. It is likely that M2Mes will be deployed in very large quantities, and many of them will also be mobile, making it unrealistic or impossible for operators or subscribers to send personnel to manage or service them. These requirements introduce a numb ...
... require remote management of their functionality. It is likely that M2Mes will be deployed in very large quantities, and many of them will also be mobile, making it unrealistic or impossible for operators or subscribers to send personnel to manage or service them. These requirements introduce a numb ...
IPSec
... • In order to communicate, each pair of hosts must set up SA with each other • Acts as virtual connection for which various parameters are set: ...
... • In order to communicate, each pair of hosts must set up SA with each other • Acts as virtual connection for which various parameters are set: ...
Networking Components and Devices
... As with a hub, computers connect to a switch via a length of twisted-pair cable. Multiple switches are often interconnected to create larger networks. Despite their similarity in appearance and their identical physical connections to computers, switches offer significant operational advantages over ...
... As with a hub, computers connect to a switch via a length of twisted-pair cable. Multiple switches are often interconnected to create larger networks. Despite their similarity in appearance and their identical physical connections to computers, switches offer significant operational advantages over ...
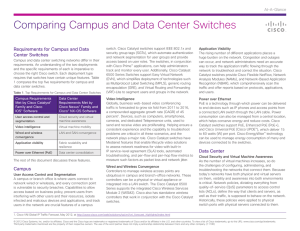
Paper
... These challenges spill over into other areas, such as troubleshooting. The Cisco Nexus 1000V Series Switches provide the solution to these problems by providing visibility into the virtual machine environment while extending the features and functions of the Cisco Nexus portfolio. The Cisco Virtual ...
... These challenges spill over into other areas, such as troubleshooting. The Cisco Nexus 1000V Series Switches provide the solution to these problems by providing visibility into the virtual machine environment while extending the features and functions of the Cisco Nexus portfolio. The Cisco Virtual ...
Federal Systems Level Guidance for Securing
... with a framework we can use as a guideline for security throughout the entire system life cycle. Next we need to determine what type of operating system platform to use for our major applications. Well, there are many choices. Should we go with a Windows system? The Microsoft (MS) platforms have gre ...
... with a framework we can use as a guideline for security throughout the entire system life cycle. Next we need to determine what type of operating system platform to use for our major applications. Well, there are many choices. Should we go with a Windows system? The Microsoft (MS) platforms have gre ...
IPmux-4L_Product
... MPLS or IP networks with pseudowire technology • Ideal solution for PSTN access and TDM trunking • Provides cost-effective solution for converging new and legacy services over packet infrastructure IPmux-4L Beta 2009 Slide 3 ...
... MPLS or IP networks with pseudowire technology • Ideal solution for PSTN access and TDM trunking • Provides cost-effective solution for converging new and legacy services over packet infrastructure IPmux-4L Beta 2009 Slide 3 ...
Efficiently Discovering and Assessing
... Software). Moreover, many recognized common network management tools, such as HP's OpenView (Hewlett-Packard) and IBM's Tivoli (IBM) are based on closed proprietary technology. There are, however, many situations where SNMP cannot be used. Despite being a well-known protocol, commonly used on enterp ...
... Software). Moreover, many recognized common network management tools, such as HP's OpenView (Hewlett-Packard) and IBM's Tivoli (IBM) are based on closed proprietary technology. There are, however, many situations where SNMP cannot be used. Despite being a well-known protocol, commonly used on enterp ...
the slide presentation
... Pairing = Introducing 2 Bluetooth devices to each other • Both devices must be Bluetooth-enabled to pair • Not all Bluetooth-enabled devices are designed to be paired to each other • Both devices must be supported by the same profile ...
... Pairing = Introducing 2 Bluetooth devices to each other • Both devices must be Bluetooth-enabled to pair • Not all Bluetooth-enabled devices are designed to be paired to each other • Both devices must be supported by the same profile ...
NET331_lecture10
... threats A firewall protects all possible Information A firewall can protect you from a completely new threat If have a firewall you don’t need an anti-virus program ...
... threats A firewall protects all possible Information A firewall can protect you from a completely new threat If have a firewall you don’t need an anti-virus program ...
Pocket Guide - Industrial Networking Solutions
... much earlier than it did others. We were therefore able to demonstrate a pioneering spirit in several ways: in 1984, we built the University of Stuttgart fiber optic network. The result was a global premiere for ETHERNET over fiber optic networks. In 1990, we came out with the ”ETHERNET ring“, our n ...
... much earlier than it did others. We were therefore able to demonstrate a pioneering spirit in several ways: in 1984, we built the University of Stuttgart fiber optic network. The result was a global premiere for ETHERNET over fiber optic networks. In 1990, we came out with the ”ETHERNET ring“, our n ...
AN INTRODUCTION TO NETWORK, NETWORK TOPOLOGIES AND
... more flexible than dedicated server. They can be used not only to direct traffic and perform administrative action but often to serve as a front end for the administration to work with other applications or servers because it act as server as well as workstation. Many network uses both dedicated and ...
... more flexible than dedicated server. They can be used not only to direct traffic and perform administrative action but often to serve as a front end for the administration to work with other applications or servers because it act as server as well as workstation. Many network uses both dedicated and ...
IP connectivity access network
... both the CS CN domain and the IMS domain have their own services and cannot be used from another domain some services are similar and available in both domains (e.g., Voice over IP in IMS and speech telephony in CS CN) ...
... both the CS CN domain and the IMS domain have their own services and cannot be used from another domain some services are similar and available in both domains (e.g., Voice over IP in IMS and speech telephony in CS CN) ...
Technology Infrastructure: The Internet and the World Wide Web
... – Provides service speeds of 128 Kbps and upward in 128-Kbps increments ...
... – Provides service speeds of 128 Kbps and upward in 128-Kbps increments ...
WRT54GL User Guide
... lights up and will stay orange when the Router is powered on. The color orange indicates that the Router is not using the SecureEasySetup feature, while the color white indicates that the Router is using the SecureEasySetup feature. When the Router enters SecureEasySetup mode, the Cisco logo will tu ...
... lights up and will stay orange when the Router is powered on. The color orange indicates that the Router is not using the SecureEasySetup feature, while the color white indicates that the Router is using the SecureEasySetup feature. When the Router enters SecureEasySetup mode, the Cisco logo will tu ...
802.1X Authentication - Training
... Authentication After the authentication server authenticates the supplicant, the authentication server initiates the authentication stage of the process. During this phase the authenticator facilitates an exchange of keys between the supplicant and the authentication server. After these keys are est ...
... Authentication After the authentication server authenticates the supplicant, the authentication server initiates the authentication stage of the process. During this phase the authenticator facilitates an exchange of keys between the supplicant and the authentication server. After these keys are est ...
Ch 01 - Introducig VoIP Networks
... Secure RTP sRTP was first published by IETF in March 2004 as RFC 3711; it was designed t o provide encryption, message authentication, and integrity, and replay protection to RTP data in both unicast and multicast applications. sRTP also has a sister protocol, called Secure RTCP (sRTCP). sRTCP provi ...
... Secure RTP sRTP was first published by IETF in March 2004 as RFC 3711; it was designed t o provide encryption, message authentication, and integrity, and replay protection to RTP data in both unicast and multicast applications. sRTP also has a sister protocol, called Secure RTCP (sRTCP). sRTCP provi ...
WWG Draft Green Book v0.080 - ccsds cwe
... The Consultative Committee for Space Data Systems (CCSDS) is an organization officially established by the management of its members. The Committee meets periodically to address data systems problems that are common to all participants, and to formulate sound technical solutions to these problems. I ...
... The Consultative Committee for Space Data Systems (CCSDS) is an organization officially established by the management of its members. The Committee meets periodically to address data systems problems that are common to all participants, and to formulate sound technical solutions to these problems. I ...
Tier-1 ISP - Universidad Carlos III de Madrid
... Internet structure: network of networks “Tier-3” ISPs and local ISPs last hop (“access”) network (closest to end systems) ...
... Internet structure: network of networks “Tier-3” ISPs and local ISPs last hop (“access”) network (closest to end systems) ...
Vertical handover criteria and algorithm in IEEE 802.11 and 802.16
... the connection is transferred between two base stations using the same access technology: the signal strength is the common metric used to predict the connection loss and to find the best neighboring cell to associate to. The notion of vertical handover was introduced with the development of differe ...
... the connection is transferred between two base stations using the same access technology: the signal strength is the common metric used to predict the connection loss and to find the best neighboring cell to associate to. The notion of vertical handover was introduced with the development of differe ...
Wireless security
.jpg?width=300)
Wireless security is the prevention of unauthorized access or damage to computers using wireless networks. The most common types of wireless security are Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). WEP is a notoriously weak security standard. The password it uses can often be cracked in a few minutes with a basic laptop computer and widely available software tools. WEP is an old IEEE 802.11 standard from 1999, which was outdated in 2003 by WPA, or Wi-Fi Protected Access. WPA was a quick alternative to improve security over WEP. The current standard is WPA2; some hardware cannot support WPA2 without firmware upgrade or replacement. WPA2 uses an encryption device that encrypts the network with a 256-bit key; the longer key length improves security over WEP.Many laptop computers have wireless cards pre-installed. The ability to enter a network while mobile has great benefits. However, wireless networking is prone to some security issues. Hackers have found wireless networks relatively easy to break into, and even use wireless technology to hack into wired networks. As a result, it is very important that enterprises define effective wireless security policies that guard against unauthorized access to important resources. Wireless Intrusion Prevention Systems (WIPS) or Wireless Intrusion Detection Systems (WIDS) are commonly used to enforce wireless security policies.The risks to users of wireless technology have increased as the service has become more popular. There were relatively few dangers when wireless technology was first introduced. Hackers had not yet had time to latch on to the new technology, and wireless networks were not commonly found in the work place. However, there are many security risks associated with the current wireless protocols and encryption methods, and in the carelessness and ignorance that exists at the user and corporate IT level. Hacking methods have become much more sophisticated and innovative with wireless access. Hacking has also become much easier and more accessible with easy-to-use Windows- or Linux-based tools being made available on the web at no charge.Some organizations that have no wireless access points installed do not feel that they need to address wireless security concerns. In-Stat MDR and META Group have estimated that 95% of all corporate laptop computers that were planned to be purchased in 2005 were equipped with wireless cards. Issues can arise in a supposedly non-wireless organization when a wireless laptop is plugged into the corporate network. A hacker could sit out in the parking lot and gather information from it through laptops and/or other devices, or even break in through this wireless card–equipped laptop and gain access to the wired network.