The Nightingale-Bamford School
... to the downloading of screensavers, wallpaper, music, and instant messaging software. You should never download or install any software onto Nightingale network drives or disks, unless you have written permission from the Nightingale Network Administrator or Director of Technology. You also should n ...
... to the downloading of screensavers, wallpaper, music, and instant messaging software. You should never download or install any software onto Nightingale network drives or disks, unless you have written permission from the Nightingale Network Administrator or Director of Technology. You also should n ...
Network+ (N10-005) Cram Notes
... 2. SNMP (161/162) - Simple Network Management Protocol which is used for managing network devices. 3. FTP (20/21) - File Transfer Protocol which is used for transferring files across the network. 4. TFTP (69) - Trivial File Transfer Protocol which is a low overhead fast transfer FTP protocol. 5. SMT ...
... 2. SNMP (161/162) - Simple Network Management Protocol which is used for managing network devices. 3. FTP (20/21) - File Transfer Protocol which is used for transferring files across the network. 4. TFTP (69) - Trivial File Transfer Protocol which is a low overhead fast transfer FTP protocol. 5. SMT ...
IOSR Journal of Electronics and Communication Engineering (IOSR-JECE)
... from one node to another node. Usually upon deployment a node does not have knowledge about its specific neighbours. A high quality network means there must be an efficient packet transmission between nodes without any delay. In order to make a wireless network an efficient network, the neighbour no ...
... from one node to another node. Usually upon deployment a node does not have knowledge about its specific neighbours. A high quality network means there must be an efficient packet transmission between nodes without any delay. In order to make a wireless network an efficient network, the neighbour no ...
Social network analysis
... • Fetching Direct links take 1 to 2 sec (maximum) – Direct links are 530. • Fetching Direct + Friend-Friend link took nearly 3 min. Number of indirect links depends. In my case, it was 3,000 (approx.) ...
... • Fetching Direct links take 1 to 2 sec (maximum) – Direct links are 530. • Fetching Direct + Friend-Friend link took nearly 3 min. Number of indirect links depends. In my case, it was 3,000 (approx.) ...
009_namingaddressing
... An Ethernet network uses two hardware addresses which identify the source and destination of each frame sent by the Ethernet. The destination address (all 1's) may also identify a broadcast packet (to be sent to all connected computers). The hardware address is also known as the Medium Access Contro ...
... An Ethernet network uses two hardware addresses which identify the source and destination of each frame sent by the Ethernet. The destination address (all 1's) may also identify a broadcast packet (to be sent to all connected computers). The hardware address is also known as the Medium Access Contro ...
Effective Key Management in Dynamic Wireless
... Such type of encryption is well-suited for sensor nodes because of their limited energy and processing capability. Asymmetric key based approaches have been proposed for dynamic WSNs. These approaches take advantage of public key cryptography (PKC) such as elliptic curve cryptography (ECC) or iden ...
... Such type of encryption is well-suited for sensor nodes because of their limited energy and processing capability. Asymmetric key based approaches have been proposed for dynamic WSNs. These approaches take advantage of public key cryptography (PKC) such as elliptic curve cryptography (ECC) or iden ...
How to Cheat at Securing Windows 2000 TCP/IP
... the same physical wire. The point they should remember is that the combination of IP address and subnet mask can segregate the physical network into logically separate networks. Multiple routes can be configured between networks, providing TCP/IP with a measure of fault tolerance. Computers can act ...
... the same physical wire. The point they should remember is that the combination of IP address and subnet mask can segregate the physical network into logically separate networks. Multiple routes can be configured between networks, providing TCP/IP with a measure of fault tolerance. Computers can act ...
doc.gold.ac.uk
... Online Security Issues Overview • Early Internet days – Most popular use: electronic mail ...
... Online Security Issues Overview • Early Internet days – Most popular use: electronic mail ...
Securing TCP/IP
... The Internet Protocol (IP) is a network protocol that provides essential routing functions for all packets transiting a TCP/IP network. By this point in your computer science education, you’re probably familiar with the concept of how IP addresses uniquely identify network destinations. Each system ...
... The Internet Protocol (IP) is a network protocol that provides essential routing functions for all packets transiting a TCP/IP network. By this point in your computer science education, you’re probably familiar with the concept of how IP addresses uniquely identify network destinations. Each system ...
Kyocera KR1 Mobile Router User Guide
... you want, when and where you want it. A WLAN (wireless local area network) transmits and receives data with radio signals instead of wires. WLANs are used increasingly in both home and office environments, and public areas such as airports, coffee shops, and universities. Innovative ways to utilize ...
... you want, when and where you want it. A WLAN (wireless local area network) transmits and receives data with radio signals instead of wires. WLANs are used increasingly in both home and office environments, and public areas such as airports, coffee shops, and universities. Innovative ways to utilize ...
start slide: headline arial bold 38 pt, 0 pt leading
... … when will 5 GHz WLANs come? IEEE802.11b (2.4 GHz) is now taking over the market. There are developments to enhance IEEE802.11b for – more bandwidth (up to 54 Mbit/s) – QoS (despite many applications do not need QoS at all) – network issues (access control and handover). 5 GHz systems will b ...
... … when will 5 GHz WLANs come? IEEE802.11b (2.4 GHz) is now taking over the market. There are developments to enhance IEEE802.11b for – more bandwidth (up to 54 Mbit/s) – QoS (despite many applications do not need QoS at all) – network issues (access control and handover). 5 GHz systems will b ...
IEEE C802.16ppc-10/0055r1 Project Title
... Figure 1: AMS Initiated Connection Establishment from the Idle State ...
... Figure 1: AMS Initiated Connection Establishment from the Idle State ...
Intrusion Detection
... Coordinated large-scale attacks at the victim machines, by a large number of attacking machines e.g., The February 7-11, 2000 attacks: A combination of 4 DDoS attacks (Trinoo, TFN, TFN2K, and Stacheldraht) ...
... Coordinated large-scale attacks at the victim machines, by a large number of attacking machines e.g., The February 7-11, 2000 attacks: A combination of 4 DDoS attacks (Trinoo, TFN, TFN2K, and Stacheldraht) ...
Security of IP Routing Protocols
... complex, properly configuring, administering, and securing them becomes increasingly difficult. ...
... complex, properly configuring, administering, and securing them becomes increasingly difficult. ...
IOSR Journal of Computer Engineering (IOSR-JCE)
... Reset function is frequently called in several states of the client server communication process during the typical DCCP communication scenario. A DCCP-Reset can be initiated by both server and client and a DCCP agent resets the connection if any feature negotiation fails during the handshake. After ...
... Reset function is frequently called in several states of the client server communication process during the typical DCCP communication scenario. A DCCP-Reset can be initiated by both server and client and a DCCP agent resets the connection if any feature negotiation fails during the handshake. After ...
Virtual private networks
... Interconnect VPN services, 2) Dial-up VPN services, 3) Extranet VPN services. LAN Interconnect VPN. LAN Interconnect VPN services help to interconnect local area networks located at multiple geographic areas over the shared network infrastructure. Typically, this service is used to connect multiple ...
... Interconnect VPN services, 2) Dial-up VPN services, 3) Extranet VPN services. LAN Interconnect VPN. LAN Interconnect VPN services help to interconnect local area networks located at multiple geographic areas over the shared network infrastructure. Typically, this service is used to connect multiple ...
Network Connectivity_PPT_ch09
... • A computer becomes a server when software is installed on it that provides a network service to client computers • The term “server” is also used in three contexts: – Server operating system – OS installed on a computer designed to share network resources and provide other network services – Serve ...
... • A computer becomes a server when software is installed on it that provides a network service to client computers • The term “server” is also used in three contexts: – Server operating system – OS installed on a computer designed to share network resources and provide other network services – Serve ...
What is routing?
... Maybe based on DNS Maybe a separate namespace Maybe IP addresses are used for location ...
... Maybe based on DNS Maybe a separate namespace Maybe IP addresses are used for location ...
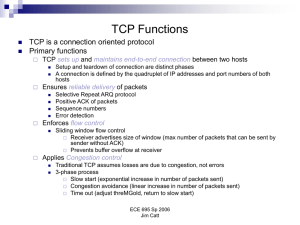
Factors that influence TCP performance
... Handle loss events that are not due to congestion differently Anticipate loss event due to handoffs, proactively manage these Improves bandwidth utilization and lowers probability of packet loss ...
... Handle loss events that are not due to congestion differently Anticipate loss event due to handoffs, proactively manage these Improves bandwidth utilization and lowers probability of packet loss ...
Peer-to-Peer Networking Overview
... tasks. The modern personal computer (PC) has a very fast processor, vast memory, and a large hard disk, none of which are being fully utilized when performing common computing tasks such as e-mail and Web browsing. The modern PC can easily act as both a client and server (a peer) for many types of a ...
... tasks. The modern personal computer (PC) has a very fast processor, vast memory, and a large hard disk, none of which are being fully utilized when performing common computing tasks such as e-mail and Web browsing. The modern PC can easily act as both a client and server (a peer) for many types of a ...
EE 122: Computer Networks
... – Delegation of address blocks to customers? – As a result, the registries are often out of date ...
... – Delegation of address blocks to customers? – As a result, the registries are often out of date ...
Wireless security
.jpg?width=300)
Wireless security is the prevention of unauthorized access or damage to computers using wireless networks. The most common types of wireless security are Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). WEP is a notoriously weak security standard. The password it uses can often be cracked in a few minutes with a basic laptop computer and widely available software tools. WEP is an old IEEE 802.11 standard from 1999, which was outdated in 2003 by WPA, or Wi-Fi Protected Access. WPA was a quick alternative to improve security over WEP. The current standard is WPA2; some hardware cannot support WPA2 without firmware upgrade or replacement. WPA2 uses an encryption device that encrypts the network with a 256-bit key; the longer key length improves security over WEP.Many laptop computers have wireless cards pre-installed. The ability to enter a network while mobile has great benefits. However, wireless networking is prone to some security issues. Hackers have found wireless networks relatively easy to break into, and even use wireless technology to hack into wired networks. As a result, it is very important that enterprises define effective wireless security policies that guard against unauthorized access to important resources. Wireless Intrusion Prevention Systems (WIPS) or Wireless Intrusion Detection Systems (WIDS) are commonly used to enforce wireless security policies.The risks to users of wireless technology have increased as the service has become more popular. There were relatively few dangers when wireless technology was first introduced. Hackers had not yet had time to latch on to the new technology, and wireless networks were not commonly found in the work place. However, there are many security risks associated with the current wireless protocols and encryption methods, and in the carelessness and ignorance that exists at the user and corporate IT level. Hacking methods have become much more sophisticated and innovative with wireless access. Hacking has also become much easier and more accessible with easy-to-use Windows- or Linux-based tools being made available on the web at no charge.Some organizations that have no wireless access points installed do not feel that they need to address wireless security concerns. In-Stat MDR and META Group have estimated that 95% of all corporate laptop computers that were planned to be purchased in 2005 were equipped with wireless cards. Issues can arise in a supposedly non-wireless organization when a wireless laptop is plugged into the corporate network. A hacker could sit out in the parking lot and gather information from it through laptops and/or other devices, or even break in through this wireless card–equipped laptop and gain access to the wired network.