Building an in-depth defense with Vectra and sandbox security
... Uses algorithms to detect infected hosts performing internal monetization (e.g., Bitcoin mining) or external monetization (e.g., ad click fraud). These are not targeted attacks. ...
... Uses algorithms to detect infected hosts performing internal monetization (e.g., Bitcoin mining) or external monetization (e.g., ad click fraud). These are not targeted attacks. ...
Computer networks
... A wide area network (WAN) is a computer network that covers a large geographic area such as a city, country, or spans even intercontinental distances. A WAN uses a communications channel that combines many types of media such as telephone lines, cables, and air waves. Enterprise private network An e ...
... A wide area network (WAN) is a computer network that covers a large geographic area such as a city, country, or spans even intercontinental distances. A WAN uses a communications channel that combines many types of media such as telephone lines, cables, and air waves. Enterprise private network An e ...
Operational Environment E P2600 Clause 4 Additions v1.0
... type of minimal physical security maintained at the facility so that only the authorized operators who run and maintain the various HCDs are permitted access to them. The susceptible assets in this case focus primarily on intellectual property of the university staff and students, although reprint o ...
... type of minimal physical security maintained at the facility so that only the authorized operators who run and maintain the various HCDs are permitted access to them. The susceptible assets in this case focus primarily on intellectual property of the university staff and students, although reprint o ...
All mesh networks are not created equal
... since each node typically has multiple available paths to choose between and can dynamically re-route or adapt its path based on changing conditions in the radio environment. The basic topology, combined with dynamic mesh intelligence, can deliver a selfconfiguring, self-healing infrastructure that ...
... since each node typically has multiple available paths to choose between and can dynamically re-route or adapt its path based on changing conditions in the radio environment. The basic topology, combined with dynamic mesh intelligence, can deliver a selfconfiguring, self-healing infrastructure that ...
Chapter 5 Lectures Notes
... more BSS networks connected via a common distribution system • APs can be positioned so that cells overlap to facilitate roaming – Wireless devices choose AP based on signal strength – Handoff ...
... more BSS networks connected via a common distribution system • APs can be positioned so that cells overlap to facilitate roaming – Wireless devices choose AP based on signal strength – Handoff ...
virtual private network(vpns)
... In the past, mobile workers used Remote Access Servers (RAS) over dial-up or ISDN leased lines to connect to company networks from remote locations (that is, when they were working from home or traveling). All things considered, RAS was probably more secure than the current practice of using a VPN, ...
... In the past, mobile workers used Remote Access Servers (RAS) over dial-up or ISDN leased lines to connect to company networks from remote locations (that is, when they were working from home or traveling). All things considered, RAS was probably more secure than the current practice of using a VPN, ...
Protection & Security
... The malicious code is executed without user intervention. The malicious code may be directed by a remote attacker once a connection is made. Resources used by the malicious code, such as file names and network addresses, are hardcoded in the binary. OS resources (processes, memory) used by the malic ...
... The malicious code is executed without user intervention. The malicious code may be directed by a remote attacker once a connection is made. Resources used by the malicious code, such as file names and network addresses, are hardcoded in the binary. OS resources (processes, memory) used by the malic ...
Wireless LANs and Introduction to IP
... • Active scanning -- Probes sent actively when mobile joins the network or moves around and out of coverage. • Passive scanning -- APs send beacons -- mobiles hear and if they find a more attractive AP, they can switch. ...
... • Active scanning -- Probes sent actively when mobile joins the network or moves around and out of coverage. • Passive scanning -- APs send beacons -- mobiles hear and if they find a more attractive AP, they can switch. ...
Network Perimeter Defense
... Risk Assessment Risk factors • Worth • Attraction • Threat • Vulnerability • Probability ...
... Risk Assessment Risk factors • Worth • Attraction • Threat • Vulnerability • Probability ...
ppt - CSE Home
... Tunnel broadcasts via the Oracle Direct broadcast traffic from your network to all other students’ networks by way of the oracle Goal: Service sharing across networks (e.g., for iTunes playlists) ...
... Tunnel broadcasts via the Oracle Direct broadcast traffic from your network to all other students’ networks by way of the oracle Goal: Service sharing across networks (e.g., for iTunes playlists) ...
ppt - Stanford Crypto group
... Programs contain bugs and are vulnerable to attack Network protocols may contain; Design weaknesses (SSH CRC) Implementation flaws (SSL, NTP, FTP, SMTP...) ...
... Programs contain bugs and are vulnerable to attack Network protocols may contain; Design weaknesses (SSH CRC) Implementation flaws (SSL, NTP, FTP, SMTP...) ...
Sachin Shetty - Tennessee State University
... Web: http://faculty.tnstate.edu/sshetty Education Ph.D., Modeling and Simulation, August 2007, Old Dominion University M.S., Computer Science, August 2002, University of Toledo B.E., Computer Engineering, August 1998, University of Mumbai, Mumbai, India. ...
... Web: http://faculty.tnstate.edu/sshetty Education Ph.D., Modeling and Simulation, August 2007, Old Dominion University M.S., Computer Science, August 2002, University of Toledo B.E., Computer Engineering, August 1998, University of Mumbai, Mumbai, India. ...
Document
... We must secure entire networked system, not just an individual component Solutions must be robust/adapt to new threats as much as possible ...
... We must secure entire networked system, not just an individual component Solutions must be robust/adapt to new threats as much as possible ...
Dynamic Network Selection for Robust Communications – Why Disruption Tolerance Matters
... happen as well that further unknown candidate networks become available in between. Balancing all these aspects and analyzing their effects on the decision process and the resulting communication performance will be one of the main focuses in our further research activities. Reliability: The estimat ...
... happen as well that further unknown candidate networks become available in between. Balancing all these aspects and analyzing their effects on the decision process and the resulting communication performance will be one of the main focuses in our further research activities. Reliability: The estimat ...
PSWG Closed Door Proposal - Western Electricity Coordinating
... The PSWG has a need for closed sessions as defined in the WECC Board Policy on Closed Sessions for Member Groups (Closed Session Policy). The Closed Session Policy permits closed sessions “to prevent the public disclosure of information identified in Section 7.6.1 of the Bylaws”; including: “to rece ...
... The PSWG has a need for closed sessions as defined in the WECC Board Policy on Closed Sessions for Member Groups (Closed Session Policy). The Closed Session Policy permits closed sessions “to prevent the public disclosure of information identified in Section 7.6.1 of the Bylaws”; including: “to rece ...
Lecture 16: Architectural Considerations
... Performance mechanisms that operate on individual flows (admission control, resource allocation, IntServ, ATM QoS) should be considered for access. Performance mechanisms that operate on aggregated flows (DiffServ, WFQ RED/WRED, and MPLS all fit in here) should be considered for core and distributio ...
... Performance mechanisms that operate on individual flows (admission control, resource allocation, IntServ, ATM QoS) should be considered for access. Performance mechanisms that operate on aggregated flows (DiffServ, WFQ RED/WRED, and MPLS all fit in here) should be considered for core and distributio ...
full Lenght Paper...
... applications for this network. While capturing important characteristics, this description does not make explicit how MANETs map into the Internet architecture – and does therefore not allow evaluation of existing IP protocols and their applicability on MANETs. Similarly, the lack of a clear archite ...
... applications for this network. While capturing important characteristics, this description does not make explicit how MANETs map into the Internet architecture – and does therefore not allow evaluation of existing IP protocols and their applicability on MANETs. Similarly, the lack of a clear archite ...
mobile - cs.wisc.edu
... – Requires addition of some infrastructure – Has no geographical limitations – Requires no modifications to IP addresses or IP address format – Supports security • Could be even more important than physically connected routing ...
... – Requires addition of some infrastructure – Has no geographical limitations – Requires no modifications to IP addresses or IP address format – Supports security • Could be even more important than physically connected routing ...
WiHawk
... Appends IP with bypass String If vulnerability found prints IP with bypass string ...
... Appends IP with bypass String If vulnerability found prints IP with bypass string ...
Importance of SETA programs
... Three types of programs * Security Education * Security Training * Security Awareness ...
... Three types of programs * Security Education * Security Training * Security Awareness ...
Essential Elements of Medical Networks
... - Ethernet transmits data at up to ten million bits per second (10 Mbps) - Fast Ethernet supports up to 100 Mbps, Gigabit Ethernet (‘Gig E’) supports up to 1000 Mbps, 10 Gig Ethernet supports speeds up to 10 gigabits per second. - supports networks of twisted-pair and fiber-optic cabling. (coax is o ...
... - Ethernet transmits data at up to ten million bits per second (10 Mbps) - Fast Ethernet supports up to 100 Mbps, Gigabit Ethernet (‘Gig E’) supports up to 1000 Mbps, 10 Gig Ethernet supports speeds up to 10 gigabits per second. - supports networks of twisted-pair and fiber-optic cabling. (coax is o ...
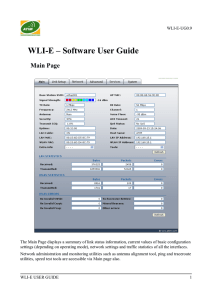
WLI-E – Software User Guide
... link speeds to better service particular customers and/or particular applications like VoIP and video which require greater consistency, stability, and lower latency performance. Uptime: This is the running total of time the device has been running since last power up (hardreboot) or software upgrad ...
... link speeds to better service particular customers and/or particular applications like VoIP and video which require greater consistency, stability, and lower latency performance. Uptime: This is the running total of time the device has been running since last power up (hardreboot) or software upgrad ...
Literature Review - Rhodes University
... after a day if more than 4 attempts are exceeded. Oracle claims to have a safe password management and also enables users to make very strong passwords. In addition Oracle does not allow a user to use the same password consecutively. ...
... after a day if more than 4 attempts are exceeded. Oracle claims to have a safe password management and also enables users to make very strong passwords. In addition Oracle does not allow a user to use the same password consecutively. ...
Network
... – Peer-to-Peer Network – One of two basic types of LANs wherein each computer user acts as a server. Each computer stores password and sharing information for its own resources. Usually has fewer than 10 computers. • NOS (Network Operating System) – Special operating system on a server containing ut ...
... – Peer-to-Peer Network – One of two basic types of LANs wherein each computer user acts as a server. Each computer stores password and sharing information for its own resources. Usually has fewer than 10 computers. • NOS (Network Operating System) – Special operating system on a server containing ut ...
Wireless security
.jpg?width=300)
Wireless security is the prevention of unauthorized access or damage to computers using wireless networks. The most common types of wireless security are Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). WEP is a notoriously weak security standard. The password it uses can often be cracked in a few minutes with a basic laptop computer and widely available software tools. WEP is an old IEEE 802.11 standard from 1999, which was outdated in 2003 by WPA, or Wi-Fi Protected Access. WPA was a quick alternative to improve security over WEP. The current standard is WPA2; some hardware cannot support WPA2 without firmware upgrade or replacement. WPA2 uses an encryption device that encrypts the network with a 256-bit key; the longer key length improves security over WEP.Many laptop computers have wireless cards pre-installed. The ability to enter a network while mobile has great benefits. However, wireless networking is prone to some security issues. Hackers have found wireless networks relatively easy to break into, and even use wireless technology to hack into wired networks. As a result, it is very important that enterprises define effective wireless security policies that guard against unauthorized access to important resources. Wireless Intrusion Prevention Systems (WIPS) or Wireless Intrusion Detection Systems (WIDS) are commonly used to enforce wireless security policies.The risks to users of wireless technology have increased as the service has become more popular. There were relatively few dangers when wireless technology was first introduced. Hackers had not yet had time to latch on to the new technology, and wireless networks were not commonly found in the work place. However, there are many security risks associated with the current wireless protocols and encryption methods, and in the carelessness and ignorance that exists at the user and corporate IT level. Hacking methods have become much more sophisticated and innovative with wireless access. Hacking has also become much easier and more accessible with easy-to-use Windows- or Linux-based tools being made available on the web at no charge.Some organizations that have no wireless access points installed do not feel that they need to address wireless security concerns. In-Stat MDR and META Group have estimated that 95% of all corporate laptop computers that were planned to be purchased in 2005 were equipped with wireless cards. Issues can arise in a supposedly non-wireless organization when a wireless laptop is plugged into the corporate network. A hacker could sit out in the parking lot and gather information from it through laptops and/or other devices, or even break in through this wireless card–equipped laptop and gain access to the wired network.