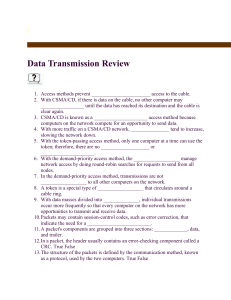
Data Transmission Review
... 22. Because single-segment 10Base2 Ethernet limits would be too confining for a large business, _________________ can be used to join Ethernet segments and extend the network to a total length of 925 meters (about 3035 feet). 23. A 10Base5 topology is also referred to as ___________________. 24. Fas ...
... 22. Because single-segment 10Base2 Ethernet limits would be too confining for a large business, _________________ can be used to join Ethernet segments and extend the network to a total length of 925 meters (about 3035 feet). 23. A 10Base5 topology is also referred to as ___________________. 24. Fas ...
HWBA54G Manual
... To access this wireless network clients are required to use encryption. This should be checked together with the item “Enable WEP”. The authentication mode defines configuration options for the sharing of wireless networks to verify identity and access privileges of roaming wireless network cards. Y ...
... To access this wireless network clients are required to use encryption. This should be checked together with the item “Enable WEP”. The authentication mode defines configuration options for the sharing of wireless networks to verify identity and access privileges of roaming wireless network cards. Y ...
Document
... What is SNMP? Simple Network Management Protocol UDP based, port 161 Community name functions as a password Many implementations allow access control via IP address ...
... What is SNMP? Simple Network Management Protocol UDP based, port 161 Community name functions as a password Many implementations allow access control via IP address ...
Downlaod File
... destinations with next hop addresses. When an IP packet is to be forwarded, a router uses its forwarding table to determine the next hop for the packet's destination (based on the destination IP address in the IP packet header), and forwards the packet appropriately. The next router then repeats thi ...
... destinations with next hop addresses. When an IP packet is to be forwarded, a router uses its forwarding table to determine the next hop for the packet's destination (based on the destination IP address in the IP packet header), and forwards the packet appropriately. The next router then repeats thi ...
Understanding Networking
... You have a phone number. You are the only one with this number. If two individuals had the same phone number the system wouldn’t work correctly. Would a caller get a busy signal if only one of the numbers was in use? Would both phones ring if neither was in use or would neither? Each computer connec ...
... You have a phone number. You are the only one with this number. If two individuals had the same phone number the system wouldn’t work correctly. Would a caller get a busy signal if only one of the numbers was in use? Would both phones ring if neither was in use or would neither? Each computer connec ...
Chapter6
... point (AP) Basic Service Set (BSS) (aka “cell”) in infrastructure mode contains: wireless hosts access point (AP): base station ad hoc mode: hosts only ...
... point (AP) Basic Service Set (BSS) (aka “cell”) in infrastructure mode contains: wireless hosts access point (AP): base station ad hoc mode: hosts only ...
Notes as Powerpoint Presentation
... • either dynamically or fixed • From the WAN all calls are to and from the WAN IP address ...
... • either dynamically or fixed • From the WAN all calls are to and from the WAN IP address ...
Network Security Management.pdf
... network. This framework has been used to find serious security holes on the Princeton University campus network and also in software from major vendors. ...
... network. This framework has been used to find serious security holes on the Princeton University campus network and also in software from major vendors. ...
pptx
... – packets from many ongoing exchanges can travel on one wire, – which makes it much cheaper to build a network – many computers can share the same wire without interfering. ...
... – packets from many ongoing exchanges can travel on one wire, – which makes it much cheaper to build a network – many computers can share the same wire without interfering. ...
Vulnerabilities - University of Wolverhampton
... attacks to multiple intermediaries at the same time, causing all of the intermediaries to direct their responses to the same victim. Attackers have also developed tools to look for network routers that do not filter broadcast traffic and networks where multiple hosts respond. These networks can the ...
... attacks to multiple intermediaries at the same time, causing all of the intermediaries to direct their responses to the same victim. Attackers have also developed tools to look for network routers that do not filter broadcast traffic and networks where multiple hosts respond. These networks can the ...
Introduction - Computer Sciences User Pages
... • Nodes: PC, special-purpose hardware… – hosts – switches ...
... • Nodes: PC, special-purpose hardware… – hosts – switches ...
ppt
... Infrastructure vs. Ad Hoc • Infrastructure mode – Wireless hosts are associated with a base station – Traditional services provided by the connected network – E.g., address assignment, routing, and DNS resolution ...
... Infrastructure vs. Ad Hoc • Infrastructure mode – Wireless hosts are associated with a base station – Traditional services provided by the connected network – E.g., address assignment, routing, and DNS resolution ...
$doc.title
... – Hold onto packets un5l another hop can take it from you – Eventually reach its des5na5on ...
... – Hold onto packets un5l another hop can take it from you – Eventually reach its des5na5on ...
MIS 4850 Systems Security
... authentication? a) their PINs are usually short like 4 characters for instance b) a 4-character PIN is too risky for access cards c) if an access card is lost, the best security measure is to cancel or disable it d) None of the above 4. You need to implement a wireless network with 3 Access Points a ...
... authentication? a) their PINs are usually short like 4 characters for instance b) a 4-character PIN is too risky for access cards c) if an access card is lost, the best security measure is to cancel or disable it d) None of the above 4. You need to implement a wireless network with 3 Access Points a ...
Wireless Security Update
... Cisco; LEAP provides authentication based on the Windows username and password logon (certificates are not required) EAP-TunneledTLS (EAP-TTLS) - Supports advanced authentication methods such as using tokens Protected EAP (PEAP) - Uses certificates similar to Secure Sockets Layer (SSL) with Web brow ...
... Cisco; LEAP provides authentication based on the Windows username and password logon (certificates are not required) EAP-TunneledTLS (EAP-TTLS) - Supports advanced authentication methods such as using tokens Protected EAP (PEAP) - Uses certificates similar to Secure Sockets Layer (SSL) with Web brow ...
Types of Encryption Algorithms
... and software • Know the vulnerabilities of the configuration • Know the threats and consider it in relation to the vulnerabilities to asses the risk • Authenticate and authorize the accessto network ...
... and software • Know the vulnerabilities of the configuration • Know the threats and consider it in relation to the vulnerabilities to asses the risk • Authenticate and authorize the accessto network ...
Networks
... LANs connect computers and peripherals within a building. Users can access software, data, and peripherals. LANs require special hardware and software. ...
... LANs connect computers and peripherals within a building. Users can access software, data, and peripherals. LANs require special hardware and software. ...
COEN 350
... Traceroute uses this to find the route to a given system. Useful for System Administration ...
... Traceroute uses this to find the route to a given system. Useful for System Administration ...
Basic DataCommunication
... A communication devices is any type of hardware capable of transmitting data, instructions, and information between a sending device and a receiving device A dial-up modem converts signals between analog and digital A digital modem sends and receives data and information to and from a digital line ...
... A communication devices is any type of hardware capable of transmitting data, instructions, and information between a sending device and a receiving device A dial-up modem converts signals between analog and digital A digital modem sends and receives data and information to and from a digital line ...
Lecture 11
... Logs may come from multiple systems, or a single system May lead to changes in logging May lead to a report of an event ...
... Logs may come from multiple systems, or a single system May lead to changes in logging May lead to a report of an event ...
Lecture 10
... Logs may come from multiple systems, or a single system May lead to changes in logging May lead to a report of an event ...
... Logs may come from multiple systems, or a single system May lead to changes in logging May lead to a report of an event ...
Lecture 10
... Logs may come from multiple systems, or a single system May lead to changes in logging May lead to a report of an event ...
... Logs may come from multiple systems, or a single system May lead to changes in logging May lead to a report of an event ...
The Network Layer
... within a LAN (company or home nowadays). They are not intended to go on the public internet. ...
... within a LAN (company or home nowadays). They are not intended to go on the public internet. ...