Ch02 - Computer Systems Technology Internet Site
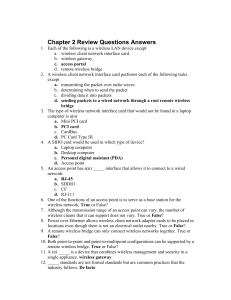
... 13. Industry-sponsored organizations that want to promote a specific technology are known as _____. consortia 14. The _____ organization has been establishing network standards for almost 25 years. IEEE 15. The _____ is a consortium that tests and certifies wireless products. Wi-Fi Alliance 16. Lis ...
... 13. Industry-sponsored organizations that want to promote a specific technology are known as _____. consortia 14. The _____ organization has been establishing network standards for almost 25 years. IEEE 15. The _____ is a consortium that tests and certifies wireless products. Wi-Fi Alliance 16. Lis ...
Internet and LAN Technology
... Wi-Fi • WEP (Wired Equivalent Privacy) encrypts data traveling over wireless networks • Equipment required for a wireless network – Wi-Fi card – Wireless access point ...
... Wi-Fi • WEP (Wired Equivalent Privacy) encrypts data traveling over wireless networks • Equipment required for a wireless network – Wi-Fi card – Wireless access point ...
tutorial1
... Routing with subnetting • When a router get a packet, it isolates by Net mask the packet net id address - if the packet is destined to other network then the router sends it to another router; otherwise the router isolates by Subnet mask at subnet id address of the packet – if it destined to another ...
... Routing with subnetting • When a router get a packet, it isolates by Net mask the packet net id address - if the packet is destined to other network then the router sends it to another router; otherwise the router isolates by Subnet mask at subnet id address of the packet – if it destined to another ...
The Network - Communication Management Services
... Avg 50-70 Kbps UL Avg 400-700 Kbps DL Peak 144 Kbps UL Peak 2 Mbps DL ...
... Avg 50-70 Kbps UL Avg 400-700 Kbps DL Peak 144 Kbps UL Peak 2 Mbps DL ...
Networking on the International Space Station
... Very fast but non-routable Self-tuning and self-configuring Suitable for small networks such as OPS LAN Uses broadcasts to locate other computers on the network. TCP/IP (Transmission Control Protocol / Internet Protocol) Most common network protocol in the world Routable ...
... Very fast but non-routable Self-tuning and self-configuring Suitable for small networks such as OPS LAN Uses broadcasts to locate other computers on the network. TCP/IP (Transmission Control Protocol / Internet Protocol) Most common network protocol in the world Routable ...
EE 122: Computer Networks
... – Global state, local computation – Flood local topology information – Each router computes shortest paths on graph – Requires routers to have globally consistent state ...
... – Global state, local computation – Flood local topology information – Each router computes shortest paths on graph – Requires routers to have globally consistent state ...
Mobile ICN Applications for an Event with Large Crowds
... Large crowds often gather for a limited duration of time due to a popular event such as a sports event or outdoor festival. When operators dimension cellular networks, the design is based on regular demands and load on the network during peak hours. There is however a limit to how much capacity can ...
... Large crowds often gather for a limited duration of time due to a popular event such as a sports event or outdoor festival. When operators dimension cellular networks, the design is based on regular demands and load on the network during peak hours. There is however a limit to how much capacity can ...
Networking Concepts
... Define the term Computer Network. A computer network consists of two or more computers that are linked in order to share resources such as printers, exchange files and allow communication. State the types of computer networks based on the geographical area covered by them. ...
... Define the term Computer Network. A computer network consists of two or more computers that are linked in order to share resources such as printers, exchange files and allow communication. State the types of computer networks based on the geographical area covered by them. ...
L21 - Security
... – Prefix hijacking: another AS originates the prefix – BGP does not verify that the AS is authorized ...
... – Prefix hijacking: another AS originates the prefix – BGP does not verify that the AS is authorized ...
ad hoc wireless networks
... Considering the transmitted power of all nodes in the network, it must be optimized with respect to all layers that it impacts. As increasing transmit power at the physical layer reduce PER and that decrease the retransmission required at the access layer, but a high transmit power from one node of ...
... Considering the transmitted power of all nodes in the network, it must be optimized with respect to all layers that it impacts. As increasing transmit power at the physical layer reduce PER and that decrease the retransmission required at the access layer, but a high transmit power from one node of ...
CPSC 6126 Computer Security
... Why Hide Internal IP Addresses? • The first step in an attack usually is to find potential victim hosts • Sniffer programs read IP packet streams for IP addresses of potential target hosts • With proxy server, sniffers will not learn IP addresses of internal hosts Sniffer Host IP Address ...
... Why Hide Internal IP Addresses? • The first step in an attack usually is to find potential victim hosts • Sniffer programs read IP packet streams for IP addresses of potential target hosts • With proxy server, sniffers will not learn IP addresses of internal hosts Sniffer Host IP Address ...
Portfolio: National Networks
... 3. Keep abreast of trends in the IT industry and provide input to the development of the ABC data network in order to provide an optimum service to ABC clients. 4. Ensure that all project work is implemented in compliance with the relevant TA&D policies, including architectural and security standard ...
... 3. Keep abreast of trends in the IT industry and provide input to the development of the ABC data network in order to provide an optimum service to ABC clients. 4. Ensure that all project work is implemented in compliance with the relevant TA&D policies, including architectural and security standard ...
Intrusion Detection and Prevention
... IP Address Spoofing • Fools perimeter router into accepting a packet with a spoofed IP address • Difficult to trace back to attacker’s node • Done by IP packet crafting • Ethernet address can also be spoofed ...
... IP Address Spoofing • Fools perimeter router into accepting a packet with a spoofed IP address • Difficult to trace back to attacker’s node • Done by IP packet crafting • Ethernet address can also be spoofed ...
Introduction to Communications and Networks
... Simple and inexpensive Client/Server: All clients must request service from the server The server is also called a host Different servers perform different tasks: File server, network server, etc. ...
... Simple and inexpensive Client/Server: All clients must request service from the server The server is also called a host Different servers perform different tasks: File server, network server, etc. ...
`12
... Networking and Communications and Cognitive Radio Networks. In this talk, I will summarize our recent research results on quantum and nano photonic devices, including terahertz quantum cascade lasers, terahertz quantum well photodetectors, organic/inorganic hybrid optical upconersion devices, scanni ...
... Networking and Communications and Cognitive Radio Networks. In this talk, I will summarize our recent research results on quantum and nano photonic devices, including terahertz quantum cascade lasers, terahertz quantum well photodetectors, organic/inorganic hybrid optical upconersion devices, scanni ...
Hijacking, Denial of Service, and Intrusion Detection
... • Feasible – packet must be received on an interface that has a valid forward path to the source • Loose – Source IP can match any valid route, only drops unroutable sources ...
... • Feasible – packet must be received on an interface that has a valid forward path to the source • Loose – Source IP can match any valid route, only drops unroutable sources ...
ppt
... – No notion of load or other application-layer metrics – Convergence time can be slow (as BGP or IGP convergence) ...
... – No notion of load or other application-layer metrics – Convergence time can be slow (as BGP or IGP convergence) ...
Network overview - Mr. Schneemann`s Web Page Edtechnology
... ARP Table Not only does your network card have it's own address but it is constantly broadcasting that address to all of the other computers on the LAN. In turn, each computer on the LAN maintains a table that lists the names and MAC addresses of each computer on the local area network. The table i ...
... ARP Table Not only does your network card have it's own address but it is constantly broadcasting that address to all of the other computers on the LAN. In turn, each computer on the LAN maintains a table that lists the names and MAC addresses of each computer on the local area network. The table i ...
EC310: Applications of Cyber Engineering Alpha: ____________________ Exam #2
... No, the first and last IP addresses of the false network are 8.9.7.80 and 8.9.7.95, respectively. The webserver’s IP address does not fall within that range. Thus, all traffic destined for the website will not go to the attacker, but towards the webserver as normal. e. List and briefly describe two ...
... No, the first and last IP addresses of the false network are 8.9.7.80 and 8.9.7.95, respectively. The webserver’s IP address does not fall within that range. Thus, all traffic destined for the website will not go to the attacker, but towards the webserver as normal. e. List and briefly describe two ...
security leaflet
... Develop’s security standards In today’s business company data have to cross a lot of different data highways. Nearly every work process and workflow starts, ends or is somehow related to your multifunctional office device. A lot of your business data is running through your ineo system. This is the ...
... Develop’s security standards In today’s business company data have to cross a lot of different data highways. Nearly every work process and workflow starts, ends or is somehow related to your multifunctional office device. A lot of your business data is running through your ineo system. This is the ...
投影片 1 - PEARL
... 802.15.4 specification defines methods by which devices can form networks Networks are known as Personal Area Networks (PANs) Each network has a unique PAN ID Three type of nodes – coordinator, routers, end device ...
... 802.15.4 specification defines methods by which devices can form networks Networks are known as Personal Area Networks (PANs) Each network has a unique PAN ID Three type of nodes – coordinator, routers, end device ...