Computer Networks Sample Questions
... a. It requires centralized and dedicated server. b. It requires at least one administrator to provide centralized resources. c. it provide extensive user and resource security. d. it provides each user the ability to to manage his own shared resources. 10. Your company has several computers, which s ...
... a. It requires centralized and dedicated server. b. It requires at least one administrator to provide centralized resources. c. it provide extensive user and resource security. d. it provides each user the ability to to manage his own shared resources. 10. Your company has several computers, which s ...
Dynamic_networks
... The capability of single stage networks are limited but if we cascade enough of them together, they form a completely connected MIN (Multistage Interconnection Network). Switches can perform their own routing or can be controlled by a central router This type of networks can be classified into the f ...
... The capability of single stage networks are limited but if we cascade enough of them together, they form a completely connected MIN (Multistage Interconnection Network). Switches can perform their own routing or can be controlled by a central router This type of networks can be classified into the f ...
Job Class: 158814 Rev: 04/15 Exempt Page: 1
... Works with Systems Administrators to resolve system-networking issues. Works with Help Desk personnel to resolve end user networking issues. Manages, upgrades, and supports the campus network domain name services. Manages, upgrades and supports the campus network dynamic host name configuration serv ...
... Works with Systems Administrators to resolve system-networking issues. Works with Help Desk personnel to resolve end user networking issues. Manages, upgrades, and supports the campus network domain name services. Manages, upgrades and supports the campus network dynamic host name configuration serv ...
CryptoPro - Applied Security GmbH
... Secure Disk for BitLocker CryptPro Secure Disk for BitLocker enhances the functionality of Microsoft BitLocker by adding an independent Pre-Boot-Authentication (PBA) and allows the usage of well established authentication methods like user-ID/password, smartcard/PIN and biometry for multi-user opera ...
... Secure Disk for BitLocker CryptPro Secure Disk for BitLocker enhances the functionality of Microsoft BitLocker by adding an independent Pre-Boot-Authentication (PBA) and allows the usage of well established authentication methods like user-ID/password, smartcard/PIN and biometry for multi-user opera ...
NP_ch01
... General-purpose processor(s) for control tasks Special-purpose processor(s) for packet processing and ...
... General-purpose processor(s) for control tasks Special-purpose processor(s) for packet processing and ...
Intrusion Detection
... source IP: single, list, any, negation source port: TCP or UDP port; single, list, any, negation direction: unidirectional (->) or bidirectional (<->). dest IP, dest port: same format as sources ...
... source IP: single, list, any, negation source port: TCP or UDP port; single, list, any, negation direction: unidirectional (->) or bidirectional (<->). dest IP, dest port: same format as sources ...
Chapter 6 slides, Computer Networking, 3rd edition
... scans channels, listening for beacon frames containing AP’s name (SSID) and MAC address selects AP to associate with may perform authentication will typically run DHCP to get IP address in AP’s subnet Wireless, Mobile Networks 6-15 ...
... scans channels, listening for beacon frames containing AP’s name (SSID) and MAC address selects AP to associate with may perform authentication will typically run DHCP to get IP address in AP’s subnet Wireless, Mobile Networks 6-15 ...
Wireless LAN
... – Can be used with either Win95/98 or Win NT – Must be used on a computer with both Wireless and wired network connections – Can use remote administration to set parameters or monitor network ...
... – Can be used with either Win95/98 or Win NT – Must be used on a computer with both Wireless and wired network connections – Can use remote administration to set parameters or monitor network ...
IP-Forwarding
... Forwarding decisions based only on data link layer header, that is the MAC DA. Use a table made from observing which addresses are seen on each port. No more than 7 bridges in diameter. Today’s ethernet environments use lots of ethernet switches, reducing the collision domain. Collision domain is th ...
... Forwarding decisions based only on data link layer header, that is the MAC DA. Use a table made from observing which addresses are seen on each port. No more than 7 bridges in diameter. Today’s ethernet environments use lots of ethernet switches, reducing the collision domain. Collision domain is th ...
presentation source
... The problem of using TCP in wireless networks • Major causes for losses in wireless networks • lossy wireless links or hand-offs • TCP can not distinguish between: • Congestion loss • Error loss • When misunderstanding error loss as congestion loss, TCP sender back off => performance degradation. ...
... The problem of using TCP in wireless networks • Major causes for losses in wireless networks • lossy wireless links or hand-offs • TCP can not distinguish between: • Congestion loss • Error loss • When misunderstanding error loss as congestion loss, TCP sender back off => performance degradation. ...
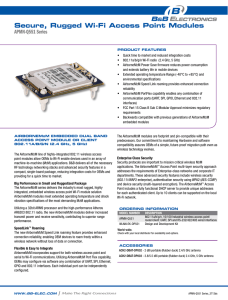
apMn-Q551
... applications. The AirborneM2M™ Access Point multi-layer security approach addresses the requirements of Enterprise-class networks and corporate IT departments. These advanced security features include wireless security (802.11i/WAP2 enterprise), authentication security using WPA2 (AES-CCMP) and devi ...
... applications. The AirborneM2M™ Access Point multi-layer security approach addresses the requirements of Enterprise-class networks and corporate IT departments. These advanced security features include wireless security (802.11i/WAP2 enterprise), authentication security using WPA2 (AES-CCMP) and devi ...
KDSM_Ozegovic_v3
... •flow control proxy controls the interaction between the technology used on the access network and on the core network •distributed and potentially inexpensive solution ...
... •flow control proxy controls the interaction between the technology used on the access network and on the core network •distributed and potentially inexpensive solution ...
No Slide Title
... • The bootstrap protocol (BOOTP) operates in a clientserver environment and only requires a single packet exchange to obtain IP information . • BOOTP packets can include the IP address, as well as the address of a router, the address of a server, and vendor-specific information. • One problem with B ...
... • The bootstrap protocol (BOOTP) operates in a clientserver environment and only requires a single packet exchange to obtain IP information . • BOOTP packets can include the IP address, as well as the address of a router, the address of a server, and vendor-specific information. • One problem with B ...
Riviera Utilities Position Description IT Network Engineer RIVIERA
... 3. Knowledge of operational and procedural aspects of computer systems, hardware, software and peripheral equipment. 4. Knowledge of network server installation, configuration, maintenance and troubleshooting. 5. Knowledge of a wide range of network systems, protocols and applications. 6. Knowledge ...
... 3. Knowledge of operational and procedural aspects of computer systems, hardware, software and peripheral equipment. 4. Knowledge of network server installation, configuration, maintenance and troubleshooting. 5. Knowledge of a wide range of network systems, protocols and applications. 6. Knowledge ...
shuffling:improving data security in ad hoc networks based
... The idea behind our protocol is to divide the initial message into parts then to encrypt and combine these parts by pairs. Then we exploit the characteristic of existence of single paths between nodes in an to increase the robustness of confidentiality. This is achieved by sending encrypted combinat ...
... The idea behind our protocol is to divide the initial message into parts then to encrypt and combine these parts by pairs. Then we exploit the characteristic of existence of single paths between nodes in an to increase the robustness of confidentiality. This is achieved by sending encrypted combinat ...
[slides] Wireless networks
... Different applications have different requirements for bandwidth, delay, jitter (e.g., 9.6Kbps for voice and 76.8Kbps for packetized video) ...
... Different applications have different requirements for bandwidth, delay, jitter (e.g., 9.6Kbps for voice and 76.8Kbps for packetized video) ...
Slide 1 - Your Flash File
... • An effective system combines elements into an architecture, or design, that is flexible, cost-effective, technically sound, and able to support the information needs of the business • System architecture translates the logical design of an information system into a physical structure that includes ...
... • An effective system combines elements into an architecture, or design, that is flexible, cost-effective, technically sound, and able to support the information needs of the business • System architecture translates the logical design of an information system into a physical structure that includes ...
Lecture 19
... #) of every outgoing datagram to (NAT IP address, new port #) . . . remote clients/servers will respond using (NAT IP address, new port #) as destination addr. remember (in NAT translation table) every (source IP address, port #) to (NAT IP address, new port #) ...
... #) of every outgoing datagram to (NAT IP address, new port #) . . . remote clients/servers will respond using (NAT IP address, new port #) as destination addr. remember (in NAT translation table) every (source IP address, port #) to (NAT IP address, new port #) ...
Ch. 2 Review Of Underlying Network Technologies
... – Sender supplies • Destination’s address • Source address (in most technologies) ...
... – Sender supplies • Destination’s address • Source address (in most technologies) ...
Review For Final - Eastern Illinois University
... a) Distinguish between IP address and host name. b) Which is the official address of a host? c) Does a server host need an IP address? d) Does your home PC need an IP address when you are on the Internet? e) Does a server host need a host name? f) Does your home PC need a host name when you are on t ...
... a) Distinguish between IP address and host name. b) Which is the official address of a host? c) Does a server host need an IP address? d) Does your home PC need an IP address when you are on the Internet? e) Does a server host need a host name? f) Does your home PC need a host name when you are on t ...















![[slides] Wireless networks](http://s1.studyres.com/store/data/008740196_1-40942f464a60beb9c165ab23a8eba523-300x300.png)