Our Team is Proud to Deliver the Best Network Solutions
... Build and deploy services with minimal impact to the live network and business environment. ...
... Build and deploy services with minimal impact to the live network and business environment. ...
How to find your “Print Server” IP-unknown IP Number from device
... Source: Sercomm_d8:a0:78, this is the MAC-ID from the PS101 device Host Announcement: PSD8A078 this is the DEVICE NAME Line 11: Source: 192.168.150.231 this is the static IP Number from PS101 Now you just have to change your IP address and gateway address in your PC, to something "192.168.150.XXX" a ...
... Source: Sercomm_d8:a0:78, this is the MAC-ID from the PS101 device Host Announcement: PSD8A078 this is the DEVICE NAME Line 11: Source: 192.168.150.231 this is the static IP Number from PS101 Now you just have to change your IP address and gateway address in your PC, to something "192.168.150.XXX" a ...
Chapter 5 Overview of Network Services
... • The DNS protocol allows these clients to make requests to DNS servers in the network for the translation of names to IP addresses. • Hostnames and the DNS services that computer systems run are all linked together. • The Internet name that the DNS resolves to the IP address is also called the Host ...
... • The DNS protocol allows these clients to make requests to DNS servers in the network for the translation of names to IP addresses. • Hostnames and the DNS services that computer systems run are all linked together. • The Internet name that the DNS resolves to the IP address is also called the Host ...
glossary - So you Start
... domain registrar, pays a remuneration fixed by registrar in exchange for the allocation of a domain name. ...
... domain registrar, pays a remuneration fixed by registrar in exchange for the allocation of a domain name. ...
Topic 5 - Networking - St Andrew`s High School
... A Print server allows a user to access a printer attached to it. Print servers are often small dedicated devices attached to the network wherever a printer is required. A web server transmits and stores web pages. This would normally be used to provide access to an Intranet. As a web server and a we ...
... A Print server allows a user to access a printer attached to it. Print servers are often small dedicated devices attached to the network wherever a printer is required. A web server transmits and stores web pages. This would normally be used to provide access to an Intranet. As a web server and a we ...
Chapter One
... IP address reserved for communicating from a node to itself Value of the loopback address is always 127.0.0.1 (try it) ...
... IP address reserved for communicating from a node to itself Value of the loopback address is always 127.0.0.1 (try it) ...
Network2 - Rhema Impact Ministries
... The web browser (client) and web server cooperate so that the web browser can get a copy of the information from a web server. The server organizes information into pages called web pages. The web browser asks the web server for a web page, and the server sends the web page back to the web browser. ...
... The web browser (client) and web server cooperate so that the web browser can get a copy of the information from a web server. The server organizes information into pages called web pages. The web browser asks the web server for a web page, and the server sends the web page back to the web browser. ...
Preventing Social Engineering
... Remind employees to keep passwords secret Don’t make exceptions It’s not a grey area! ...
... Remind employees to keep passwords secret Don’t make exceptions It’s not a grey area! ...
IIUSA – Internet Institute
... Static versus Dynamic Routes • Static routes are established by a network administrator and manually input directly into the routing table • Dynamic routes are learned through the use of a Routing Protocol. Dynamic routes are adaptive. Changes to path availability or establishment of new paths are a ...
... Static versus Dynamic Routes • Static routes are established by a network administrator and manually input directly into the routing table • Dynamic routes are learned through the use of a Routing Protocol. Dynamic routes are adaptive. Changes to path availability or establishment of new paths are a ...
ABCD - Cisco
... A device that receives SIP requests, strips out the address in the request, checks its address tables for any other addresses that may be mapped to the one in the request, and then returns the results of the address mapping to the client. ...
... A device that receives SIP requests, strips out the address in the request, checks its address tables for any other addresses that may be mapped to the one in the request, and then returns the results of the address mapping to the client. ...
Speakers
... Yes there is Citrix/TS but it has never been 100% the desktop or office replacement for fulltime workers outside of the office. •Applications not supported on TS/Citrix (especially now that TS is 64bit only). •Multiple user environment resource issues. •General challenges supporting Citrix/TS enviro ...
... Yes there is Citrix/TS but it has never been 100% the desktop or office replacement for fulltime workers outside of the office. •Applications not supported on TS/Citrix (especially now that TS is 64bit only). •Multiple user environment resource issues. •General challenges supporting Citrix/TS enviro ...
Slides - CERN Indico
... – Memory-to-memory is somewhat deterministic, but disk-todisk has several uncontrolled variables. • Applications may use multiple streams for maximum exploitation of high-speed links. Lambda Station must be able to deal in aggregates. • Straggler flows persist after bulk of transfer has completed, a ...
... – Memory-to-memory is somewhat deterministic, but disk-todisk has several uncontrolled variables. • Applications may use multiple streams for maximum exploitation of high-speed links. Lambda Station must be able to deal in aggregates. • Straggler flows persist after bulk of transfer has completed, a ...
投影片 1
... destination vehicle as long as one exists. • Currently, our protocol is designed for IVC networks formed by a few vehicles moving on the same lane. ...
... destination vehicle as long as one exists. • Currently, our protocol is designed for IVC networks formed by a few vehicles moving on the same lane. ...
Chapter 13 PowerPoint Slides
... try to obtain TCP/IP configuration parameters from a DHCP server on the network. If a computer running Windows 2000 currently has a static TCP/IP configuration, you can change it to obtain its IP address automatically by selecting Obtain An IP Address Automatically in the Internet Protocol (TCP/IP) ...
... try to obtain TCP/IP configuration parameters from a DHCP server on the network. If a computer running Windows 2000 currently has a static TCP/IP configuration, you can change it to obtain its IP address automatically by selecting Obtain An IP Address Automatically in the Internet Protocol (TCP/IP) ...
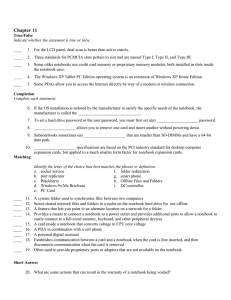
Chpt 11 - 07 test.doc
... 5. Some PDAs allow you to access the Internet directly by way of a modem or wireless connection. ...
... 5. Some PDAs allow you to access the Internet directly by way of a modem or wireless connection. ...
ch01 - Montana State University
... Reproduction or translation of this work beyond that named in Section 117 of the United States Copyright Act without the express written consent of the copyright owner is unlawful. Requests for further information should be addressed to the Permissions Department, John Wiley & Sons, Inc. Adopters of ...
... Reproduction or translation of this work beyond that named in Section 117 of the United States Copyright Act without the express written consent of the copyright owner is unlawful. Requests for further information should be addressed to the Permissions Department, John Wiley & Sons, Inc. Adopters of ...
WaveDeploy
... WaveBlade generates stateful, scalable, mobile clients, wired and wireless • Up to 500 clients / servers per test port, up to 1000 QoS test traffic flows per test port ...
... WaveBlade generates stateful, scalable, mobile clients, wired and wireless • Up to 500 clients / servers per test port, up to 1000 QoS test traffic flows per test port ...
AJ33201205
... MANET nodes might be battery-powered and might have very limited resources, this may make the use of heavy-weight security solutions undesirable. MANETs often suffer from security attacks because of its features like open medium, changing its topology dynamically, lack of central monitoring and mana ...
... MANET nodes might be battery-powered and might have very limited resources, this may make the use of heavy-weight security solutions undesirable. MANETs often suffer from security attacks because of its features like open medium, changing its topology dynamically, lack of central monitoring and mana ...
Network Infrastructure Insecurity
... certainly possibly to begin advertising invalid routes with little to stop it. – This can divert the traffic from other AS routers who trust the routes advertised by the compromised one. – Traffic can be intercepted, hijacked or ...
... certainly possibly to begin advertising invalid routes with little to stop it. – This can divert the traffic from other AS routers who trust the routes advertised by the compromised one. – Traffic can be intercepted, hijacked or ...
“Cut-outs” (propostas específicas de pesquisa) do Cap 3.
... Managing a large data network is immensely difficult, as evidenced by two interesting statistics. First, the cost of the people and systems that manage a network typically exceeds the cost of the underlying nodes and links. Second, more than half of network outages are caused by operator error, rath ...
... Managing a large data network is immensely difficult, as evidenced by two interesting statistics. First, the cost of the people and systems that manage a network typically exceeds the cost of the underlying nodes and links. Second, more than half of network outages are caused by operator error, rath ...
how to avoid getting on the front pages for the
... can have multiple addresses assigned to it—either many on one physical interface or one per many physical interfaces. Multiple addresses can be used to spread the load across multiple network interface cards, or some addresses can act as administrative addresses. A good example of this is the TSM po ...
... can have multiple addresses assigned to it—either many on one physical interface or one per many physical interfaces. Multiple addresses can be used to spread the load across multiple network interface cards, or some addresses can act as administrative addresses. A good example of this is the TSM po ...
3rd Edition: Chapter 4
... to this shorter prefix, and so reduce the size of their address table. E.g. ISP serves 128.9.14.0/24 and 128.9.15.0/24, it can tell other routers to send it all packets belonging to the prefix 128.9.14.0/23. ...
... to this shorter prefix, and so reduce the size of their address table. E.g. ISP serves 128.9.14.0/24 and 128.9.15.0/24, it can tell other routers to send it all packets belonging to the prefix 128.9.14.0/23. ...
Lecture 17
... they would not usually do • Doesn’t require server to save any information • Can be turned on and off easily • We would like many network security solutions to be like this one Advanced Network Security ...
... they would not usually do • Doesn’t require server to save any information • Can be turned on and off easily • We would like many network security solutions to be like this one Advanced Network Security ...
File - Itassignments
... normally sends several packets to the same destination. A system that receives an ARP reply stores the mapping in the cache memory and keeps it for 20 to 30 minutes unless the space in the cache is exhausted. Before sending an ARP request, the system first checks its cache to see if it can find the ...
... normally sends several packets to the same destination. A system that receives an ARP reply stores the mapping in the cache memory and keeps it for 20 to 30 minutes unless the space in the cache is exhausted. Before sending an ARP request, the system first checks its cache to see if it can find the ...