Windows Server 2008 - Information Technology of Falcon
... – Wireless channel: recommended that you set your channels five channels apart, such as 1, 6, and 11 – SSID broadcast status: by default, APs are configured to transmit the SSID so that any wireless device in range can see the network Copyright © 2012 Cengage Learning. All rights reserved. ...
... – Wireless channel: recommended that you set your channels five channels apart, such as 1, 6, and 11 – SSID broadcast status: by default, APs are configured to transmit the SSID so that any wireless device in range can see the network Copyright © 2012 Cengage Learning. All rights reserved. ...
Lecture 9: Communication Security
... banking which requires a high level of security. It provides no confidentiality for user transactions and limited integrity. It is also vulnerable to ‘man-in-the-middle’ attacks. TLS provides confidentiality and integrity of data which are the basic required security services. Non-repudiation is not ...
... banking which requires a high level of security. It provides no confidentiality for user transactions and limited integrity. It is also vulnerable to ‘man-in-the-middle’ attacks. TLS provides confidentiality and integrity of data which are the basic required security services. Non-repudiation is not ...
Chapter 1. Introduction to Data Communications
... Reproduction or translation of this work beyond that named in Section 117 of the United States Copyright Act without the express written consent of the copyright owner is unlawful. Requests for further information should be addressed to the Permissions Department, John Wiley & Sons, Inc. Adopters of ...
... Reproduction or translation of this work beyond that named in Section 117 of the United States Copyright Act without the express written consent of the copyright owner is unlawful. Requests for further information should be addressed to the Permissions Department, John Wiley & Sons, Inc. Adopters of ...
port
... (frames) that contain the address on a target host. Joint broadcast messages collaps, so they have to be retransmitted. There is a protocol for LANs, the Ethernet. ...
... (frames) that contain the address on a target host. Joint broadcast messages collaps, so they have to be retransmitted. There is a protocol for LANs, the Ethernet. ...
Chapter 1 Introduction
... 1969, four nodes (universities) connected via IMPs to form a network – Software (NCP) Network Control Protocol provided communication between the hosts. 1972, Vint Cerf and Bob Kahn invented (TCP) Transmission Control Protocol ...
... 1969, four nodes (universities) connected via IMPs to form a network – Software (NCP) Network Control Protocol provided communication between the hosts. 1972, Vint Cerf and Bob Kahn invented (TCP) Transmission Control Protocol ...
transparencies
... Due to the newness of theses technologies, Network QOS (LBE, IP Premium, Multicast …) implementation is a very tricky and complex task. Dynamic QoS configuration and peering must be enhanced in order to work in multi-domain networks. ...
... Due to the newness of theses technologies, Network QOS (LBE, IP Premium, Multicast …) implementation is a very tricky and complex task. Dynamic QoS configuration and peering must be enhanced in order to work in multi-domain networks. ...
OneConnect® OCe11101-N
... New multi-core servers are enabling much higher virtualization ratios. OneConnect adapters support NetQueue for VMware and Virtual Machine Queue (VMQ) for Microsoft Windows Server 2008 Hyper-V to optimize performance and provide full 10Gb/s bandwidth per port. Universal Multi-Channel OneConnect Univ ...
... New multi-core servers are enabling much higher virtualization ratios. OneConnect adapters support NetQueue for VMware and Virtual Machine Queue (VMQ) for Microsoft Windows Server 2008 Hyper-V to optimize performance and provide full 10Gb/s bandwidth per port. Universal Multi-Channel OneConnect Univ ...
Software systems and issues operating systems file systems and databases applications
... What an operating system does • manages CPU, schedules and coordinates running programs – switches CPU among programs that are actually computing – suspends programs that are waiting for something (e.g., disk, network) – keeps individual programs from hogging resources ...
... What an operating system does • manages CPU, schedules and coordinates running programs – switches CPU among programs that are actually computing – suspends programs that are waiting for something (e.g., disk, network) – keeps individual programs from hogging resources ...
Simulators for Sensor Networks - University of Virginia, Department
... -Build a system that even a fool can use, and only a fool will use it. ...
... -Build a system that even a fool can use, and only a fool will use it. ...
CSEMS Lecture on Networking Basics
... Each Ethernet adapter has a unique 48-bit address. Hosts send bits to any other host in chunks called frames. Hub slavishly copies each bit from each port to every other port. Every host sees every bit. ...
... Each Ethernet adapter has a unique 48-bit address. Hosts send bits to any other host in chunks called frames. Hub slavishly copies each bit from each port to every other port. Every host sees every bit. ...
TCP/IP protokolu kopa
... The Internet Society (ISOC). A group of volunteers who manages the standards of TCP/IP The Internet Architecture Board (IAB) is the technical advisory group of ISOC, and responsible for setting standards, publishing RFCs and overseeing the Internet Standards process. RFCs. A document written by anyo ...
... The Internet Society (ISOC). A group of volunteers who manages the standards of TCP/IP The Internet Architecture Board (IAB) is the technical advisory group of ISOC, and responsible for setting standards, publishing RFCs and overseeing the Internet Standards process. RFCs. A document written by anyo ...
Aalborg Universitet Charaf, Hassan
... allowed to generate and send new encoded packets (i.e., new linear combinations of the packets they have previously received). An obvious benefit of using network coding is that a network node is no longer required to gather all data packets one by one; instead, it only has to receive enough linearl ...
... allowed to generate and send new encoded packets (i.e., new linear combinations of the packets they have previously received). An obvious benefit of using network coding is that a network node is no longer required to gather all data packets one by one; instead, it only has to receive enough linearl ...
Dominating-Set-Based Routing in Ad Hoc Wireless Networks
... advertisement messages (thereby reducing network bandwidth overhead). Each host maintains a route cache: source routes that it has learned . If a route is not found from route cache, the source attempts to discover one using route discovery. Route maintenance monitors the correct operation of a rout ...
... advertisement messages (thereby reducing network bandwidth overhead). Each host maintains a route cache: source routes that it has learned . If a route is not found from route cache, the source attempts to discover one using route discovery. Route maintenance monitors the correct operation of a rout ...
ppt
... The Internet Circa 1993 In 1993, the Internet consisted of one backbone (NSFNET) that connected 13 sites via 45 Mbs ...
... The Internet Circa 1993 In 1993, the Internet consisted of one backbone (NSFNET) that connected 13 sites via 45 Mbs ...
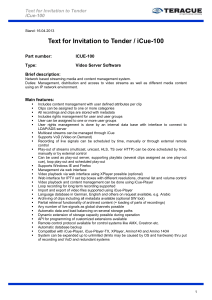
Text for Invitation to Tender / iCue-100 - COMM-TEC
... Network based streaming media and content management system. Duties: Management, distribution and access to video streams as well as different media content using an IP network environment. ...
... Network based streaming media and content management system. Duties: Management, distribution and access to video streams as well as different media content using an IP network environment. ...
Network management
... Although TCO has been widely accepted, many organizations disagree with the practice of including user “waste” time in the measure and prefer to focus on costing methods that examine only the direct costs of operating the computer. ...
... Although TCO has been widely accepted, many organizations disagree with the practice of including user “waste” time in the measure and prefer to focus on costing methods that examine only the direct costs of operating the computer. ...
ppt
... » responsible for the development and publication of the standard. (from RFC) » the coordinating committee for Internet design, engineering, and management. ...
... » responsible for the development and publication of the standard. (from RFC) » the coordinating committee for Internet design, engineering, and management. ...
Lecture18 - Philadelphia University
... WSN Architecture: • Nodes in the WSN are classified into two types according to their function: • Source node: It is any entity in the network that can provide information. It could be a sensor node, or an actuator node that provides feedback information about an operation. • Sink node: It is the ...
... WSN Architecture: • Nodes in the WSN are classified into two types according to their function: • Source node: It is any entity in the network that can provide information. It could be a sensor node, or an actuator node that provides feedback information about an operation. • Sink node: It is the ...
CPS221 Lecture: The Network Layer last revised 10/9/2014
... 2. The destination system is on a different subnet 3. The sending system can easily distinguish these two cases by comparing the subnet prefix portion of itself and the destination IP C. In the case of sending to another node on the same subnet, direct delivery can be used. 1. In this case, the send ...
... 2. The destination system is on a different subnet 3. The sending system can easily distinguish these two cases by comparing the subnet prefix portion of itself and the destination IP C. In the case of sending to another node on the same subnet, direct delivery can be used. 1. In this case, the send ...
Network Topology
... topologies in such a way that the resulting network does not exhibit one of the standard topologies (e.g., bus, star, ring, etc.). Two star networks connected together exhibit a hybrid network topology. A hybrid topology is always produced when two different basic network topologies are connec ...
... topologies in such a way that the resulting network does not exhibit one of the standard topologies (e.g., bus, star, ring, etc.). Two star networks connected together exhibit a hybrid network topology. A hybrid topology is always produced when two different basic network topologies are connec ...
例外(exception)とは何か
... Set of Protocols - A network includes a set of protocols to work together, called protocol suite/family - Each protocol in a protocol suite solves part of communication problem Need for Protocols - Hardware is low level and can’t be directly interacted with computer - Need mechanisms to distinguish ...
... Set of Protocols - A network includes a set of protocols to work together, called protocol suite/family - Each protocol in a protocol suite solves part of communication problem Need for Protocols - Hardware is low level and can’t be directly interacted with computer - Need mechanisms to distinguish ...