Running IPv6 2006
... Copyright © 2006 by Iljitsch van Beijnum All rights reserved. No part of this work may be reproduced or transmitted in any form or by any means, electronic or mechanical, including photocopying, recording, or by any information storage or retrieval system, without the prior written permission of the ...
... Copyright © 2006 by Iljitsch van Beijnum All rights reserved. No part of this work may be reproduced or transmitted in any form or by any means, electronic or mechanical, including photocopying, recording, or by any information storage or retrieval system, without the prior written permission of the ...
Fibre Channel over Ethernet (FCoE) Data Center Bridging (DCB) Concepts and Protocols
... Use, copying, and distribution of any EMC software described in this publication requires an applicable software license. EMC2, EMC, and the EMC logo are registered trademarks or trademarks of EMC Corporation in the United State and other countries. All other trademarks used herein are the property ...
... Use, copying, and distribution of any EMC software described in this publication requires an applicable software license. EMC2, EMC, and the EMC logo are registered trademarks or trademarks of EMC Corporation in the United State and other countries. All other trademarks used herein are the property ...
Cisco MDS 9148S 16G Multilayer Fabric Switch Data Sheet
... Directory (AD), and TACACS+. It also deploys VSAN fabric isolation, intelligent, port-level packet inspection, Fibre Channel Security Protocol (FC-SP) host-to-switch and switch-to-switch authentication, Secure File Transfer Protocol (SFTP), Secure Shell Version 2 (SSHv2), and Simple Network Manageme ...
... Directory (AD), and TACACS+. It also deploys VSAN fabric isolation, intelligent, port-level packet inspection, Fibre Channel Security Protocol (FC-SP) host-to-switch and switch-to-switch authentication, Secure File Transfer Protocol (SFTP), Secure Shell Version 2 (SSHv2), and Simple Network Manageme ...
The History of nordunet
... involved were big and expensive, and joint use was economically necessary. To make it possible to operate the mainframe computers from a distance, connections with remote stations were established. At the beginning of the 1970s the University of Oslo took part in the joint purchase of a cdc compute ...
... involved were big and expensive, and joint use was economically necessary. To make it possible to operate the mainframe computers from a distance, connections with remote stations were established. At the beginning of the 1970s the University of Oslo took part in the joint purchase of a cdc compute ...
MF229dw/MF226dn/MF217w/MF216n
... Use only a power supply that meets the specified voltage requirements. Failure to do so may result in a fire or electrical shock. Do not use power cords other than the one provided, as this may result in a fire or electrical shock. Do not modify, pull, forcibly bend, or perform any other act that ma ...
... Use only a power supply that meets the specified voltage requirements. Failure to do so may result in a fire or electrical shock. Do not use power cords other than the one provided, as this may result in a fire or electrical shock. Do not modify, pull, forcibly bend, or perform any other act that ma ...
Amazon Virtual Private Cloud Network Administrator
... virtual private gateway, and the VPC. There are two lines between the customer gateway and virtual private gateway because the VPN connection consists of two tunnels. We chose this design to provide increased availability for the Amazon VPC service. If there's a device failure within AWS, your VPN c ...
... virtual private gateway, and the VPC. There are two lines between the customer gateway and virtual private gateway because the VPN connection consists of two tunnels. We chose this design to provide increased availability for the Amazon VPC service. If there's a device failure within AWS, your VPN c ...
What Is ASF? Services
... Knowing the service cluster needs, the platform validation data is consulted and a server layout is created. The platform validation data will determine how may servers are needed for the deployment and what role in the ASF environment each server will play. The network layout is then determined by ...
... Knowing the service cluster needs, the platform validation data is consulted and a server layout is created. The platform validation data will determine how may servers are needed for the deployment and what role in the ASF environment each server will play. The network layout is then determined by ...
IPv6 network management
... • CISCO-IETF-IP-MIB and CISCO-IETF-IP-FORWARDING-MIB are IPv6 MIBs that are defined as being protocol-independent, but are implemented only for IPv6 objects and tables tables. • In Cisco IOS Release 12.2(33)SRC, IP-MIB and IP-FORWARDMIB were updated to RFC 4293 and RFC 4292 standards • Also, informa ...
... • CISCO-IETF-IP-MIB and CISCO-IETF-IP-FORWARDING-MIB are IPv6 MIBs that are defined as being protocol-independent, but are implemented only for IPv6 objects and tables tables. • In Cisco IOS Release 12.2(33)SRC, IP-MIB and IP-FORWARDMIB were updated to RFC 4293 and RFC 4292 standards • Also, informa ...
wireless mesh networks
... Per-hop RTT is too much dependent on the traffic load/queuing delay, which interferes with the accuracy of per-hop RTT and thus, can easily lead to route instability. If a separate queue is assigned to probe packets, then it can accurately measure the link quality but cannot reflect the traffic load ...
... Per-hop RTT is too much dependent on the traffic load/queuing delay, which interferes with the accuracy of per-hop RTT and thus, can easily lead to route instability. If a separate queue is assigned to probe packets, then it can accurately measure the link quality but cannot reflect the traffic load ...
user manual
... This equipment has been tested and found to comply with the limits for a Class B digital device, pursuant to part 15 of the FCC Rules. These limits are designed to provide reasonable protection against harmful interference in a residential installation. This equipment generates, uses, and can radiat ...
... This equipment has been tested and found to comply with the limits for a Class B digital device, pursuant to part 15 of the FCC Rules. These limits are designed to provide reasonable protection against harmful interference in a residential installation. This equipment generates, uses, and can radiat ...
Wireless Design - Kenneth M. Chipps Ph.D. Home Page
... • In a network where the parts are connected with wires, in general, one need only decide where to place the parts and what capabilities each of these parts require to create an effective and efficient network ...
... • In a network where the parts are connected with wires, in general, one need only decide where to place the parts and what capabilities each of these parts require to create an effective and efficient network ...
IPv6 Deployment Status in KT/Korea
... strategy council driven by MIC • No Telco’s are now ready to deploy IPv6 as they see IPv6 as business, not as infrastructure upgrade • They’re still research-oriented even though they have IPv6 deployment plans – KT, SKT, etc KT Future Technology Laboratory ...
... strategy council driven by MIC • No Telco’s are now ready to deploy IPv6 as they see IPv6 as business, not as infrastructure upgrade • They’re still research-oriented even though they have IPv6 deployment plans – KT, SKT, etc KT Future Technology Laboratory ...
MG-SOFT MIB Browser
... Inform packets that were sent from arbitrary SNMP devices or applications on the network. With almost twenty years of continuous product development and maintenance and its usage in major IT and telecommunications companies you can be confident that MG-SOFT MIB Browser will effectively serve all you ...
... Inform packets that were sent from arbitrary SNMP devices or applications on the network. With almost twenty years of continuous product development and maintenance and its usage in major IT and telecommunications companies you can be confident that MG-SOFT MIB Browser will effectively serve all you ...
Cisco ASA 5500 Series SSL/IPsec VPN Edition
... ASA 5500 Series SSL/IPsec VPN Edition enables organizations to securely provide network access to a broad array of users, including mobile and fixed endpoints, remote offices, contractors, and business partners. Supporting a wide range of deployment and application environments, the Cisco ASA 5500 S ...
... ASA 5500 Series SSL/IPsec VPN Edition enables organizations to securely provide network access to a broad array of users, including mobile and fixed endpoints, remote offices, contractors, and business partners. Supporting a wide range of deployment and application environments, the Cisco ASA 5500 S ...
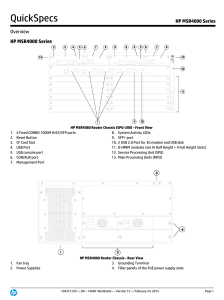
HP MSR4000 Series
... collects, maintains, and distributes dynamic public addresses through the VPN Address Management (VAM) protocol, making VPN establishment available between enterprise branches that use dynamic addresses to access the public network; compared to traditional VPN technologies, DVPN technology is more f ...
... collects, maintains, and distributes dynamic public addresses through the VPN Address Management (VAM) protocol, making VPN establishment available between enterprise branches that use dynamic addresses to access the public network; compared to traditional VPN technologies, DVPN technology is more f ...
EMC PowerPath Virtual Appliance
... longer running appliance, the preferred method is to set up an alias in your domain name server (DNS) to resolve the appliance hostname. b. (Optional) Set Search Domain(s) to a space-separated list of domains used in the network. For example, emc.com myhostname.emc.com. c. Set Name or IP Address of ...
... longer running appliance, the preferred method is to set up an alias in your domain name server (DNS) to resolve the appliance hostname. b. (Optional) Set Search Domain(s) to a space-separated list of domains used in the network. For example, emc.com myhostname.emc.com. c. Set Name or IP Address of ...
ipv6 technology and dns setup
... IPv4 has not been substantially changed since RFC 791 was published in 1981. IPv4 is robust, easily implemented and interoperable, and has stood the test of scaling an Internet to a global utility the size of today’s Internet. However, since the recent exponential growth of the Internet, IPv4 addres ...
... IPv4 has not been substantially changed since RFC 791 was published in 1981. IPv4 is robust, easily implemented and interoperable, and has stood the test of scaling an Internet to a global utility the size of today’s Internet. However, since the recent exponential growth of the Internet, IPv4 addres ...
SNMP/MIB Management
... • If all bytes are printable ASCII characters, the octet string is printed as an ASCII string. • If any byte is a non-printing character, the octet is printed as a hexadecimal. Therefore, the output of an SNMP manager may appear in an unexpected format. For example, a MAC address that happens to con ...
... • If all bytes are printable ASCII characters, the octet string is printed as an ASCII string. • If any byte is a non-printing character, the octet is printed as a hexadecimal. Therefore, the output of an SNMP manager may appear in an unexpected format. For example, a MAC address that happens to con ...
SUSE Linux Enterprise Desktop www.suse.com
... available on Linux, such as NIS or LDAP. It also deals with aspects of local security like access control lists, encryption and intrusion detection. In the network security part you learn how to secure your computers with firewalls and masquerading, and how to set up virtual private networks (VPN). ...
... available on Linux, such as NIS or LDAP. It also deals with aspects of local security like access control lists, encryption and intrusion detection. In the network security part you learn how to secure your computers with firewalls and masquerading, and how to set up virtual private networks (VPN). ...
TCPware Management Guide
... you have is correct, you may obtain an applicable copy of the license at: http://www.isc.org. This file is part of the ISC DHCP distribution. The documentation associated with this file is listed in the file DOCUMENTATION, included in the top-level directory of this release. Support and other servic ...
... you have is correct, you may obtain an applicable copy of the license at: http://www.isc.org. This file is part of the ISC DHCP distribution. The documentation associated with this file is listed in the file DOCUMENTATION, included in the top-level directory of this release. Support and other servic ...
iSCSI SAN Topologies Version 3.2 Jonghoon (Jason) Jeong
... TCP terminology............................................................................... TCP error recovery............................................................................ TCP network congestion.................................................................. IPv6 ................ ...
... TCP terminology............................................................................... TCP error recovery............................................................................ TCP network congestion.................................................................. IPv6 ................ ...