iSCSI SAN Topologies Version 3.2 Jonghoon (Jason) Jeong
... TCP terminology............................................................................... TCP error recovery............................................................................ TCP network congestion.................................................................. IPv6 ................ ...
... TCP terminology............................................................................... TCP error recovery............................................................................ TCP network congestion.................................................................. IPv6 ................ ...
ES 203 178 - V1.1.1 - Functional architecture to support European
... case where the VoIP service provider and one or several network operators - all serving the customer in the establishment of an emergency call - are independent enterprises needing to co-operate to determine the location of the (nomadic) caller. The architecture identifies all necessary interfaces, ...
... case where the VoIP service provider and one or several network operators - all serving the customer in the establishment of an emergency call - are independent enterprises needing to co-operate to determine the location of the (nomadic) caller. The architecture identifies all necessary interfaces, ...
Introduction to Dynamic Routing Protocols
... The data networks that we use in our everyday lives to learn, play, and work range from small, local networks to large, global internetworks. At home, you might have a router and two or more computers. At work, your organization might have multiple routers and switches servicing the data communicati ...
... The data networks that we use in our everyday lives to learn, play, and work range from small, local networks to large, global internetworks. At home, you might have a router and two or more computers. At work, your organization might have multiple routers and switches servicing the data communicati ...
A. IMS/Internet interworking scenario.
... According to 3GPP standards, the central component of the UMTS security architecture is the Authentication and Key Agreement (AKA) procedure. The AKA serves to mutually authenticate the MS (i.e., the USIM) and the network, and at the same time exchange the session keys that will be used for encrypti ...
... According to 3GPP standards, the central component of the UMTS security architecture is the Authentication and Key Agreement (AKA) procedure. The AKA serves to mutually authenticate the MS (i.e., the USIM) and the network, and at the same time exchange the session keys that will be used for encrypti ...
APPENDIX D UNISYN OPEN ELECT VOTING SYSTEM PHYSICAL
... LCD touchscreen used for viewing directions given by the OVO as well as performing administrative functions, a ballot reader/scanner which reads hand marked ballots as well as those produced by the OVI, a ballot box which accepts the ballots read into the OVO as well as providing a storage compartme ...
... LCD touchscreen used for viewing directions given by the OVO as well as performing administrative functions, a ballot reader/scanner which reads hand marked ballots as well as those produced by the OVI, a ballot box which accepts the ballots read into the OVO as well as providing a storage compartme ...
Next Generation NP Solutions - ENUM
... » ITRS H.323/IM/Video URIs and MMS NP address lookup deployed using ENUM across the USA » Mobile Operators, message aggregators and message content providers using GSMA PathFinder ENUM for Global NP assisted message delivery » XConnect Global Alliance using ENUM Directory Server to route onnet traff ...
... » ITRS H.323/IM/Video URIs and MMS NP address lookup deployed using ENUM across the USA » Mobile Operators, message aggregators and message content providers using GSMA PathFinder ENUM for Global NP assisted message delivery » XConnect Global Alliance using ENUM Directory Server to route onnet traff ...
A.2 Use case for detach related measurements
... The present document has been developed within the 3 rd Generation Partnership Project (3GPP TM) and may be further elaborated for the purposes of 3GPP. The present document has not been subject to any approval process by the 3GPP Organizational Partners and shall not be implemented. This Specificat ...
... The present document has been developed within the 3 rd Generation Partnership Project (3GPP TM) and may be further elaborated for the purposes of 3GPP. The present document has not been subject to any approval process by the 3GPP Organizational Partners and shall not be implemented. This Specificat ...
Novell SUSE LINUX Enterprise Server
... Novell, Inc. makes no representations or warranties with respect to the contents or use of this documentation, and specifically disclaims any express or implied warranties of merchantability or fitness for any particular purpose. Further, Novell, Inc. reserves the right to revise this publication an ...
... Novell, Inc. makes no representations or warranties with respect to the contents or use of this documentation, and specifically disclaims any express or implied warranties of merchantability or fitness for any particular purpose. Further, Novell, Inc. reserves the right to revise this publication an ...
Cisco ASR 5x00 Packet Data Serving Node Administration Guide Version 15.0
... Cisco and the Cisco Logo are trademarks of Cisco Systems, Inc. and/or its affiliates in the U.S. and other countries. A listing of Cisco's trademarks can be found at www.cisco.com/go/trademarks. Third party trademarks mentioned are the property of their respective owners. The use of the word partner ...
... Cisco and the Cisco Logo are trademarks of Cisco Systems, Inc. and/or its affiliates in the U.S. and other countries. A listing of Cisco's trademarks can be found at www.cisco.com/go/trademarks. Third party trademarks mentioned are the property of their respective owners. The use of the word partner ...
“Computers in Communication” by Gordon Brebner
... That is, it presents computer communications as an activity that lies between the physical world of communication media and the logical world of computer users. If these external constraints are taken on trust, the details may be omitted by the reader. Chapter 12 is also concerned with constraints, ...
... That is, it presents computer communications as an activity that lies between the physical world of communication media and the logical world of computer users. If these external constraints are taken on trust, the details may be omitted by the reader. Chapter 12 is also concerned with constraints, ...
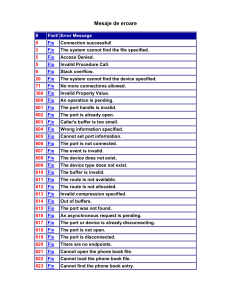
Mesaje de eroare
... Internet Connection Sharing cannot be enabled. The LAN connection selected as the private network is either not 783 N/A present, or is disconnected from the network. Please ensure that the LAN adapter is connected before enabling Internet Connection Sharing You cannot dial using this connecti ...
... Internet Connection Sharing cannot be enabled. The LAN connection selected as the private network is either not 783 N/A present, or is disconnected from the network. Please ensure that the LAN adapter is connected before enabling Internet Connection Sharing You cannot dial using this connecti ...
8 Security
... The present document has been developed within the 3rd Generation Partnership Project (3GPP TM) and may be further elaborated for the purposes of 3GPP. The present document has not been subject to any approval process by the 3GPP Organisational Partners and shall not be implemented. This Specificati ...
... The present document has been developed within the 3rd Generation Partnership Project (3GPP TM) and may be further elaborated for the purposes of 3GPP. The present document has not been subject to any approval process by the 3GPP Organisational Partners and shall not be implemented. This Specificati ...
TS 133 107
... The present document can be downloaded from: http://www.etsi.org/standards-search The present document may be made available in electronic versions and/or in print. The content of any electronic and/or print versions of the present document shall not be modified without the prior written authorizati ...
... The present document can be downloaded from: http://www.etsi.org/standards-search The present document may be made available in electronic versions and/or in print. The content of any electronic and/or print versions of the present document shall not be modified without the prior written authorizati ...
Leading Networking Solutions for Industrial
... Sustainable Security Solutions Comprehensive security features in switches, routers and firewalls according to latest standards like IEC62443 and best practices offers all around protection in mission critical networks. Regular updates of the device software enable customer’s networks to be complian ...
... Sustainable Security Solutions Comprehensive security features in switches, routers and firewalls according to latest standards like IEC62443 and best practices offers all around protection in mission critical networks. Regular updates of the device software enable customer’s networks to be complian ...
Configuration Example
... CD-ROM H3C delivers a CD-ROM together with each device. The CD-ROM contains a complete set of electronic documents of the product, including operation manuals and command manuals. After installing the reader program provided by the CD-ROM, you can search for the desired contents in a convenient way ...
... CD-ROM H3C delivers a CD-ROM together with each device. The CD-ROM contains a complete set of electronic documents of the product, including operation manuals and command manuals. After installing the reader program provided by the CD-ROM, you can search for the desired contents in a convenient way ...
PassFinder
... Operation (E&M Voice Port Command) .......................................................248 ...
... Operation (E&M Voice Port Command) .......................................................248 ...
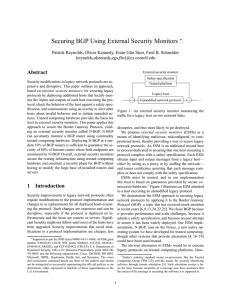
PDF
... ant with a safety specification. Installing an ESM to monitor each host in a distributed system ensures that all hosts in the system exhibit valid behavior. When some hosts are not monitored, then ESMs monitoring other hosts may be able to coordinate to derive guarantees about the behavior of unmoni ...
... ant with a safety specification. Installing an ESM to monitor each host in a distributed system ensures that all hosts in the system exhibit valid behavior. When some hosts are not monitored, then ESMs monitoring other hosts may be able to coordinate to derive guarantees about the behavior of unmoni ...
Avaya Session Border Controller for Enterprise
... applicable number of licenses and units of capacity for which the license is granted will be one (1), unless a different number of licenses or units of capacity is specified in the documentation or other materials available to you. “Software” means Avaya’s computer programs in object code, provided ...
... applicable number of licenses and units of capacity for which the license is granted will be one (1), unless a different number of licenses or units of capacity is specified in the documentation or other materials available to you. “Software” means Avaya’s computer programs in object code, provided ...
PDF - Complete Book (2.34 MB)
... You apply the per-topology configuration in router address family configuration mode of the global routing process (router configuration mode). The address family and subaddress family are specified when the device enters address family configuration mode. You specify the topology name and topology ...
... You apply the per-topology configuration in router address family configuration mode of the global routing process (router configuration mode). The address family and subaddress family are specified when the device enters address family configuration mode. You specify the topology name and topology ...
Trend Micro Smart Scan for OfficeScan 10 Getting
... All other product or company names may be trademarks or registered trademarks of their owners. Copyright© 1998-2009 Trend Micro Incorporated. All rights reserved. Document Part No. OSEM104052/90318 Release Date: April 2009 Protected by U.S. Patent No. 5,623,600; 5,889,943; 5,951,698; 6.119,165 ...
... All other product or company names may be trademarks or registered trademarks of their owners. Copyright© 1998-2009 Trend Micro Incorporated. All rights reserved. Document Part No. OSEM104052/90318 Release Date: April 2009 Protected by U.S. Patent No. 5,623,600; 5,889,943; 5,951,698; 6.119,165 ...