11 Secure electronic communication
... Staff aware of appropriate confidentiality of information (eg. clear screen and clear desk procedures) Preventative system maintenance undertaken regularly Software updates and patches applied as soon as they become available Secure messaging system (involving encryption) used for the electronic tra ...
... Staff aware of appropriate confidentiality of information (eg. clear screen and clear desk procedures) Preventative system maintenance undertaken regularly Software updates and patches applied as soon as they become available Secure messaging system (involving encryption) used for the electronic tra ...
COMPUTER CRIME Computer crime
... Malware bots – bots that are used for fraud, sabotage, denial-of-service attacks, or some other malicious purpose Zombies (or drones) – malware-bot-infected computers Bot ...
... Malware bots – bots that are used for fraud, sabotage, denial-of-service attacks, or some other malicious purpose Zombies (or drones) – malware-bot-infected computers Bot ...
VPN: Virtual Private Network
... corporate intranet over a shared infrastructure using dedicated connections. In this example, the VPN is often an alternative to fax, snail mail. The extranet VPN facilitates ecommerce. ...
... corporate intranet over a shared infrastructure using dedicated connections. In this example, the VPN is often an alternative to fax, snail mail. The extranet VPN facilitates ecommerce. ...
Application research and analysis based on Bitlocker
... then Windows 7 operating system uses of Bitlocker encryption system boot disk in the case of without installingtrusted platform module of TPM1.2 version. Encryption started, open the desktop icon, select the system disk (C:), click the right key and chooseBitlocker (B), requires the startup key when ...
... then Windows 7 operating system uses of Bitlocker encryption system boot disk in the case of without installingtrusted platform module of TPM1.2 version. Encryption started, open the desktop icon, select the system disk (C:), click the right key and chooseBitlocker (B), requires the startup key when ...
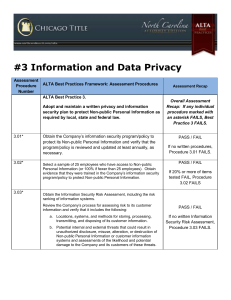
ALTA Assessment Procedures
... a. Obtain and review change management procedures when technology and business function changes are made. ...
... a. Obtain and review change management procedures when technology and business function changes are made. ...
Application Security
... • All these settings should be defined, implemented, and maintained as many are not shipped with secure defaults. This includes keeping all software up to date, including all code libraries used by the application. ...
... • All these settings should be defined, implemented, and maintained as many are not shipped with secure defaults. This includes keeping all software up to date, including all code libraries used by the application. ...
End of Chapter Solutions Template
... You would add a rule prohibiting any outbound HTTP traffic to the destination IP 197.34.5.56 on port 80. Case Project 2 You can two one of two things (or both). First, you can add your computer to the firewall’s list of “trusted” machines. The exact method varies depending on the firewall program yo ...
... You would add a rule prohibiting any outbound HTTP traffic to the destination IP 197.34.5.56 on port 80. Case Project 2 You can two one of two things (or both). First, you can add your computer to the firewall’s list of “trusted” machines. The exact method varies depending on the firewall program yo ...
CHENDU COLLEGE OF ENGINEERING &TECHNOLOGY
... 5. Sketch and explain the various components of system development life cycle waterfall methodology?(16) may/jun 2014 6. Describe the critical characteristics of information. how are they used in the study of computer security.(8) nov/dec2011 7. Explain the security system development life cycle in ...
... 5. Sketch and explain the various components of system development life cycle waterfall methodology?(16) may/jun 2014 6. Describe the critical characteristics of information. how are they used in the study of computer security.(8) nov/dec2011 7. Explain the security system development life cycle in ...
Security Policies, Standards, and Planning
... b. This section defines “fair and responsible use” of equipment and other organizational assets and should also address key legal issues, such as protection of personal information and privacy. 3. Prohibited use of equipment a. This section outlines what the issue or technology cannot be used for. U ...
... b. This section defines “fair and responsible use” of equipment and other organizational assets and should also address key legal issues, such as protection of personal information and privacy. 3. Prohibited use of equipment a. This section outlines what the issue or technology cannot be used for. U ...
Network Infrastructure Security Good Practice Guide
... The good practice set does not contain mandatory requirements that centers are required to implement. Instead, it outlines a number of good practices with respect to enterprise ICT security and acceptable use. The prudence of implementing specific good practices identified in this guide will depend ...
... The good practice set does not contain mandatory requirements that centers are required to implement. Instead, it outlines a number of good practices with respect to enterprise ICT security and acceptable use. The prudence of implementing specific good practices identified in this guide will depend ...
BIO-ELECTRO-INFO TECHNOLOGIES TO COMBAT TERRORISM
... install the wiretap. This can be done from any network connection and is called promiscuous mode sniffer. However this shared technology is fast changing to switched technology, which implies that sniffer would have to actively tap the wire. ...
... install the wiretap. This can be done from any network connection and is called promiscuous mode sniffer. However this shared technology is fast changing to switched technology, which implies that sniffer would have to actively tap the wire. ...
Permissions
... • Users do not have to remember multiple user names and passwords • Logins are controlled by Windows password policies • Logins can be mapped to a single user, or Windows group account • Non-Windows users (i.e. MAC) cannot log in to SQL Server © Wiley Inc. 2006. All Rights Reserved. ...
... • Users do not have to remember multiple user names and passwords • Logins are controlled by Windows password policies • Logins can be mapped to a single user, or Windows group account • Non-Windows users (i.e. MAC) cannot log in to SQL Server © Wiley Inc. 2006. All Rights Reserved. ...
Cyber-Insurance--I Do Not Think That Word
... third parties was not found to be anthat extension of injury reimburse processor for fees imposed the cyber-insurance coverage asathe the limited to parties suffered data breach. suffered by PFC. by card brands. processor did not suffer injury. ...
... third parties was not found to be anthat extension of injury reimburse processor for fees imposed the cyber-insurance coverage asathe the limited to parties suffered data breach. suffered by PFC. by card brands. processor did not suffer injury. ...
70-687 8.1 Lecture Slides Lesson 10
... • A wireless profile is a file that contains the wireless SSID, security type and encryption type and security keys. • If a wireless network is not broadcasting its SSID, you have to enter information such as the network’s SSID, security type, encrypting type and security key manually by going throu ...
... • A wireless profile is a file that contains the wireless SSID, security type and encryption type and security keys. • If a wireless network is not broadcasting its SSID, you have to enter information such as the network’s SSID, security type, encrypting type and security key manually by going throu ...
Document
... • Establish Switched Port Analyzer (SPAN) on the core switch or firewall – Mirrors all network traffic for IDS ...
... • Establish Switched Port Analyzer (SPAN) on the core switch or firewall – Mirrors all network traffic for IDS ...
Chapter 9
... This chapter discussed how to prevent intrusions by understanding how to interpret the signatures of both normal and abnormal network traffic. By being able to recognize the characteristics of a possible intrusion, you gain the ability to read log files and alert messages and react to them effective ...
... This chapter discussed how to prevent intrusions by understanding how to interpret the signatures of both normal and abnormal network traffic. By being able to recognize the characteristics of a possible intrusion, you gain the ability to read log files and alert messages and react to them effective ...
White Hat Hacking Tyler Schumacher Department of Computer
... hats looking to find and fix problems without prior consent of a company [2]. Some companies see that as a good thing, but all black hats do. Tsutomu Shimomura is a famous white hat. He was hacked himself, and then worked with the FBI to catch the black hat hacker, who was the most wanted cyber-crim ...
... hats looking to find and fix problems without prior consent of a company [2]. Some companies see that as a good thing, but all black hats do. Tsutomu Shimomura is a famous white hat. He was hacked himself, and then worked with the FBI to catch the black hat hacker, who was the most wanted cyber-crim ...
General Assembly 1 Background Guide
... The advent and rapid expansion of computing systems has made technology an irreplaceable aspect of daily life. Financial activities, academic work, and communications have been revolutionized by technology, and the disruption of these technologies and networks can wreak havoc on a global scale. The ...
... The advent and rapid expansion of computing systems has made technology an irreplaceable aspect of daily life. Financial activities, academic work, and communications have been revolutionized by technology, and the disruption of these technologies and networks can wreak havoc on a global scale. The ...
Suggested Syllabus Text and Course Resource Requirements for
... Browser is a special web browser that you download to take quizzes and exams in Canvas. If an exam requires LockDown Browser then you cannot open it with regular web browsers like Firefox, Safari or Chrome. LockDown browser temporarily locks up your computer’s other applications and resources so tha ...
... Browser is a special web browser that you download to take quizzes and exams in Canvas. If an exam requires LockDown Browser then you cannot open it with regular web browsers like Firefox, Safari or Chrome. LockDown browser temporarily locks up your computer’s other applications and resources so tha ...
Babu Madhav Institute of Information Technology, UTU 2017
... 7. ___________________________ attacks are used to commit financial crimes. 8. The first stage of web jacking is _____________________. 9. An illegal intrusion , posing as a genuine user is known as ______________________. 10. _________________ mean visual deception. 11. ___________________ are the ...
... 7. ___________________________ attacks are used to commit financial crimes. 8. The first stage of web jacking is _____________________. 9. An illegal intrusion , posing as a genuine user is known as ______________________. 10. _________________ mean visual deception. 11. ___________________ are the ...
Babu Madhav Institute of Information Technology, UTU 2015
... 7. ___________________________ attacks are used to commit financial crimes. 8. The first stage of web jacking is _____________________. 9. An illegal intrusion , posing as a genuine user is known as ______________________. 10. _________________ mean visual deception. 11. ___________________ are the ...
... 7. ___________________________ attacks are used to commit financial crimes. 8. The first stage of web jacking is _____________________. 9. An illegal intrusion , posing as a genuine user is known as ______________________. 10. _________________ mean visual deception. 11. ___________________ are the ...
Module 7 Active Directory and Account Management
... and plan its structure before you implement it • Implement the least number of domains possible • Implement only one domain on most small networks • When an organization is planning to reorganize, use OUs to reflect the organization’s structure • Create only the number of OUs that are absolutely nec ...
... and plan its structure before you implement it • Implement the least number of domains possible • Implement only one domain on most small networks • When an organization is planning to reorganize, use OUs to reflect the organization’s structure • Create only the number of OUs that are absolutely nec ...
LogMeIn Security – an In-Depth Look
... installing a remote access product. Remote access products are perceived as high risk factors, but mainly for psychological reasons. When a user first sees a remote access solution in action, their first negative reaction is usually with regard to the security implications. This is perfectly normal, ...
... installing a remote access product. Remote access products are perceived as high risk factors, but mainly for psychological reasons. When a user first sees a remote access solution in action, their first negative reaction is usually with regard to the security implications. This is perfectly normal, ...
Umfang von PCI-Audits reduzieren mit Cisco TrustSec - Analyse und Bewertung von Verizon
... applications. Compared to access control mechanisms based on network topology, Cisco TrustSec defines policies using logical policy groupings, so that secure access is consistently maintained even as resources are moved. De-coupling access policy from IP addresses and VLANs simplifies security polic ...
... applications. Compared to access control mechanisms based on network topology, Cisco TrustSec defines policies using logical policy groupings, so that secure access is consistently maintained even as resources are moved. De-coupling access policy from IP addresses and VLANs simplifies security polic ...