Virtualization - WordPress.com
... virtualization, requiring operating system changes but resulting in near native performance. • As Xen requires collaboration (modifications to the guest operating system), only those operating systems that are patched can be virtualized over Xen. From the perspective of Linux, which is itself open s ...
... virtualization, requiring operating system changes but resulting in near native performance. • As Xen requires collaboration (modifications to the guest operating system), only those operating systems that are patched can be virtualized over Xen. From the perspective of Linux, which is itself open s ...
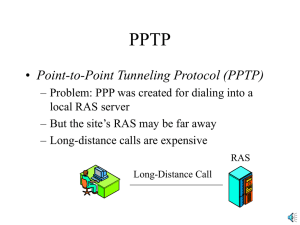
PPTP
... – Access concentrator receives the original IP packet, which has the destination IP address of the access concentrator – Adds a new IP header with the IP address of the RAS – Adds an enhanced general routing encapsulation (GRE) header for security ...
... – Access concentrator receives the original IP packet, which has the destination IP address of the access concentrator – Adds a new IP header with the IP address of the RAS – Adds an enhanced general routing encapsulation (GRE) header for security ...
Virtualization
... virtualization, requiring operating system changes but resulting in near native performance. • As Xen requires collaboration (modifications to the guest operating system), only those operating systems that are patched can be virtualized over Xen. From the perspective of Linux, which is itself open s ...
... virtualization, requiring operating system changes but resulting in near native performance. • As Xen requires collaboration (modifications to the guest operating system), only those operating systems that are patched can be virtualized over Xen. From the perspective of Linux, which is itself open s ...
Defending the Cloud from the Full Stack Hack
... Use APIs to snapshot the disk, mount snapshots on different system, and extract everything without touching the network or system Zero indication from traditional controls that any access has taken place Same is true of cloud databases, I don’t need your passwords or even SQL Injection, I just need ...
... Use APIs to snapshot the disk, mount snapshots on different system, and extract everything without touching the network or system Zero indication from traditional controls that any access has taken place Same is true of cloud databases, I don’t need your passwords or even SQL Injection, I just need ...
About the Presentations
... One-Time Password Software • Two types of one-time passwords are available: – Challenge-response passwords • Authenticating computer or firewall generates a random number (the challenge) and sends it to the user, who enters a secret PIN or password (the ...
... One-Time Password Software • Two types of one-time passwords are available: – Challenge-response passwords • Authenticating computer or firewall generates a random number (the challenge) and sends it to the user, who enters a secret PIN or password (the ...
8. Enabling cybersecurity information exchange
... The Cybersecurity Information Exchange Framework (CYBEX) is intended to accomplish a simple, limited objective – namely a common global means for cybersecurity entities to exchange cybersecurity information. Such entities typically consist of organizations, persons, objects, or processes possessing ...
... The Cybersecurity Information Exchange Framework (CYBEX) is intended to accomplish a simple, limited objective – namely a common global means for cybersecurity entities to exchange cybersecurity information. Such entities typically consist of organizations, persons, objects, or processes possessing ...
Exam Topics in This Chapter
... filtering, and Advanced Malware Protection (AMP). This module runs as a separate application from the classic Cisco ASA software. The Cisco ASA FirePOWER module can be a hardware module on the ASA 5585-X only or a software module that runs in an SSD in all other models. The Cisco ASA FirePOWER modul ...
... filtering, and Advanced Malware Protection (AMP). This module runs as a separate application from the classic Cisco ASA software. The Cisco ASA FirePOWER module can be a hardware module on the ASA 5585-X only or a software module that runs in an SSD in all other models. The Cisco ASA FirePOWER modul ...
6.1. Elliptic Curve Cryptography
... clues as possible about either the key (or) the plain text that produced it. An important distinction between crypto algorithms is whether they are secret key (or) public key algorithms. A secret key algorithm is symmetric, (or) it uses same key for encryption and also for decryption. The security o ...
... clues as possible about either the key (or) the plain text that produced it. An important distinction between crypto algorithms is whether they are secret key (or) public key algorithms. A secret key algorithm is symmetric, (or) it uses same key for encryption and also for decryption. The security o ...
Risk Analysis - University at Albany
... • Different stakeholders have various perception of risk • Several sources of threats exist simultaneously Sanjay Goel, School of Business/Center for Information Forensics and Assurance University at Albany Proprietary Information ...
... • Different stakeholders have various perception of risk • Several sources of threats exist simultaneously Sanjay Goel, School of Business/Center for Information Forensics and Assurance University at Albany Proprietary Information ...
View Slide Presentation - Association for Pathology Informatics
... Provide a collaboration space in which researchers may construct and manage retrospective tissue distribution protocols. ...
... Provide a collaboration space in which researchers may construct and manage retrospective tissue distribution protocols. ...
Chapter16-PresentationDistilled
... against scenarios that attempt to break the final system. It can also include penetration testing where the company attempts to break into their own systems to find vulnerabilities as if they were hackers. Whereas normal testing focuses on passing user requirements, security testing focuses on survi ...
... against scenarios that attempt to break the final system. It can also include penetration testing where the company attempts to break into their own systems to find vulnerabilities as if they were hackers. Whereas normal testing focuses on passing user requirements, security testing focuses on survi ...
Network Security
... Sniffing Sniffing, also called eavesdropping, is the act of monitoring network traffic for data, such as cleartext passwords or configuration information. Vulnerabilities Weak physical security Lack of encryption when sending sensitive data Router(config)# line vty 0 4 Router(config-line)# ...
... Sniffing Sniffing, also called eavesdropping, is the act of monitoring network traffic for data, such as cleartext passwords or configuration information. Vulnerabilities Weak physical security Lack of encryption when sending sensitive data Router(config)# line vty 0 4 Router(config-line)# ...
Safe & Secure Environment for Students
... the most of its computing technology – while receiving only appropriate Internet content – Previous filtering solution provided inadequate integration with user directories, ...
... the most of its computing technology – while receiving only appropriate Internet content – Previous filtering solution provided inadequate integration with user directories, ...
SNMP Simple Network Management Protocol - CS-UCY
... • SNMP manager and an SNMP agent communicate using the SNMP protocol – Generally: Manager sends queries and agent responds – Exception: Traps are initiated by agent. ...
... • SNMP manager and an SNMP agent communicate using the SNMP protocol – Generally: Manager sends queries and agent responds – Exception: Traps are initiated by agent. ...
Acceptable Use Policy
... ETAN will consider the list mailing to be unsolicited. Any Client‐maintained mailing list must also allow any party on the list to remove itself automatically and permanently. Other prohibited mailing activities include, but are not limited to, the following: a) Use of ETAN’s network for the receipt ...
... ETAN will consider the list mailing to be unsolicited. Any Client‐maintained mailing list must also allow any party on the list to remove itself automatically and permanently. Other prohibited mailing activities include, but are not limited to, the following: a) Use of ETAN’s network for the receipt ...
M3AAWG Anti-Abuse Best Common Practices for Hosting and Cloud
... customer or prospect that their practices do not abide by the terms and Acceptable Use Policy of the system they are on or where they are trying to provision an environment. Making efforts to target clients who will be a good fit for the hosting company is another way to preserve the safety of the h ...
... customer or prospect that their practices do not abide by the terms and Acceptable Use Policy of the system they are on or where they are trying to provision an environment. Making efforts to target clients who will be a good fit for the hosting company is another way to preserve the safety of the h ...
3 Responding to Incidents
... 1.6.3 Unauthorized Utilization of Resources It is not always necessary to access another user's account in order to attack an IS. An intruder can access information or plant Trojan horse programs simply by misusing available services or via social engineering. 1.6.4 Disruption of Denial of Services ...
... 1.6.3 Unauthorized Utilization of Resources It is not always necessary to access another user's account in order to attack an IS. An intruder can access information or plant Trojan horse programs simply by misusing available services or via social engineering. 1.6.4 Disruption of Denial of Services ...
PaaS Acceptable Use Policy
... Distribution of Malware: The Cloud Services shall not be used for the storage, distribution, fabrication, or use of malware, including without limitation, virus software, root kits, password crackers, adware, key stroke capture programs and other programs normally used in malicious activity. The use ...
... Distribution of Malware: The Cloud Services shall not be used for the storage, distribution, fabrication, or use of malware, including without limitation, virus software, root kits, password crackers, adware, key stroke capture programs and other programs normally used in malicious activity. The use ...
Intelligent Cybersecurity for the Real World Hermes Romero Regional Security Sales, Sourcefire
... Xen 3.3.2/3.4.2 on Soucefire 4.x platforms only. © 2013 Cisco and/or its affiliates. All rights reserved. ...
... Xen 3.3.2/3.4.2 on Soucefire 4.x platforms only. © 2013 Cisco and/or its affiliates. All rights reserved. ...
Governance Guidance - Top Actions
... information needs. They can represent a sizeable expenditure to acquire and maintain, and can be critical to the ongoing viability of the enterprise. As an indication of the importance members of senior management give to information assets and their protection, they should be involved with, or endo ...
... information needs. They can represent a sizeable expenditure to acquire and maintain, and can be critical to the ongoing viability of the enterprise. As an indication of the importance members of senior management give to information assets and their protection, they should be involved with, or endo ...
Governance Guidance
... information needs. They can represent a sizeable expenditure to acquire and maintain, and can be critical to the ongoing viability of the enterprise. As an indication of the importance members of senior management give to information assets and their protection, they should be involved with, or endo ...
... information needs. They can represent a sizeable expenditure to acquire and maintain, and can be critical to the ongoing viability of the enterprise. As an indication of the importance members of senior management give to information assets and their protection, they should be involved with, or endo ...
Governance Guidance - Top Actions
... information needs. They can represent a sizeable expenditure to acquire and maintain, and can be critical to the ongoing viability of the enterprise. As an indication of the importance members of senior management give to information assets and their protection, they should be involved with, or endo ...
... information needs. They can represent a sizeable expenditure to acquire and maintain, and can be critical to the ongoing viability of the enterprise. As an indication of the importance members of senior management give to information assets and their protection, they should be involved with, or endo ...
Junos Pulse Access Control Service
... antivirus, anti-malware, and personal firewalls. It also enables custom checks of elements such as registry and port status for Windows-based devices, and can perform a Message Digest 5 (MD5) checksum to verify application validity. Mobile devices running Apple iOS or Android initially connect to a ...
... antivirus, anti-malware, and personal firewalls. It also enables custom checks of elements such as registry and port status for Windows-based devices, and can perform a Message Digest 5 (MD5) checksum to verify application validity. Mobile devices running Apple iOS or Android initially connect to a ...
Advanced Operating Systems, CSci555
... Base conditions require presentation or availability of credential – Matching the condition brings in additional policy elements. ...
... Base conditions require presentation or availability of credential – Matching the condition brings in additional policy elements. ...
Advanced Operating Systems, CSci555 - CCSS
... malicious code. – Returns fall information to hide effect of malicious code. – Some root kits have countermeasures to attempts to detect the root kits. – Blue pill makes itself hyper-root Copyright © 1995-2008 Clifford Neuman - UNIVERSITY OF SOUTHERN CALIFORNIA - INFORMATION SCIENCES INSTITUTE ...
... malicious code. – Returns fall information to hide effect of malicious code. – Some root kits have countermeasures to attempts to detect the root kits. – Blue pill makes itself hyper-root Copyright © 1995-2008 Clifford Neuman - UNIVERSITY OF SOUTHERN CALIFORNIA - INFORMATION SCIENCES INSTITUTE ...