6. Basic concept of the Cybersecurity Information Exchange
... Response Teams (CIRTS), both within and between jurisdictions, will: a) have information to enable decision making and action to substantially enhance the confidentiality, integrity and availability of global telecommunication/ICT facilities and services; b) have adopted secure collaborative process ...
... Response Teams (CIRTS), both within and between jurisdictions, will: a) have information to enable decision making and action to substantially enhance the confidentiality, integrity and availability of global telecommunication/ICT facilities and services; b) have adopted secure collaborative process ...
About the Presentations
... One-Time Password Software • Two types of one-time passwords are available: – Challenge-response passwords • Authenticating computer or firewall generates a random number (the challenge) and sends it to the user, who enters a secret PIN or password (the ...
... One-Time Password Software • Two types of one-time passwords are available: – Challenge-response passwords • Authenticating computer or firewall generates a random number (the challenge) and sends it to the user, who enters a secret PIN or password (the ...
How to Detect Mainframe Intrusion Attempts
... Is your Mainframe Safe? - Delivery > TCP Vs. UDP TCP (Transmission Control Protocol) Port transmissions connect directly to the computer it’s sending data to, and stay connected for the duration of the transfer. With this method, the two computers can guarantee that the data has arrived safely an ...
... Is your Mainframe Safe? - Delivery > TCP Vs. UDP TCP (Transmission Control Protocol) Port transmissions connect directly to the computer it’s sending data to, and stay connected for the duration of the transfer. With this method, the two computers can guarantee that the data has arrived safely an ...
Safe & Secure Environment for Students
... of known malicious based on deep content analysis botnet traffic and unknown across all ports malware traffic at connection time Presentation_ID ...
... of known malicious based on deep content analysis botnet traffic and unknown across all ports malware traffic at connection time Presentation_ID ...
01 - Quick Heal
... What does it do? • It allows attackers to remotely access an infected system. • Systems infected by this worm can be used to launch distributed denial of service (DDoS) attacks. • It may be used to install additional Trojan malware or other forms of malicious software. • It might also open ports on ...
... What does it do? • It allows attackers to remotely access an infected system. • Systems infected by this worm can be used to launch distributed denial of service (DDoS) attacks. • It may be used to install additional Trojan malware or other forms of malicious software. • It might also open ports on ...
PLCsecurity_@_ABT-ABOC_20070122 - Indico
... ► I can stop any PLC at CERN. ► I can modify its contents. ► I just need an Ethernet connection to it. ► I (engineer, operator) might have finger-trouble. ► I (virus) do not care that it’s a PLC. ► I (attacker) might do this on purpose. ...
... ► I can stop any PLC at CERN. ► I can modify its contents. ► I just need an Ethernet connection to it. ► I (engineer, operator) might have finger-trouble. ► I (virus) do not care that it’s a PLC. ► I (attacker) might do this on purpose. ...
Risk Analysis - University at Albany
... – determination of state of risk associated with a system based upon thorough analysis – includes recommendations to support subsequent security controls/decisions. – takes into account business, as well as legal constraints. ...
... – determination of state of risk associated with a system based upon thorough analysis – includes recommendations to support subsequent security controls/decisions. – takes into account business, as well as legal constraints. ...
Application Security
... • OWASP’s CSRF Guardcan be used to automatically include such tokens in your Java EE, .NET, or PHP application. OWASP’s ESAPI includes token generators and validators that developers can use to protect their transactions. Access more information security training for campus technical staff and earn ...
... • OWASP’s CSRF Guardcan be used to automatically include such tokens in your Java EE, .NET, or PHP application. OWASP’s ESAPI includes token generators and validators that developers can use to protect their transactions. Access more information security training for campus technical staff and earn ...
HoneyPot1 - Security Research
... •Increased knowledge: knowing how to respond & prevent future attacks •Identification and Classification: Find out who is attacking you and profile them ...
... •Increased knowledge: knowing how to respond & prevent future attacks •Identification and Classification: Find out who is attacking you and profile them ...
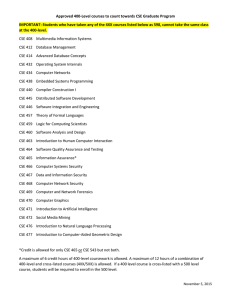
Approved 400-Level courses to count towards CSE Graduate
... Approved 400-Level courses to count towards CSE Graduate Program IMPORTANT: Students who have taken any of the 4XX courses listed below as 598, cannot take the same class at the 400-level. CSE 408 Multimedia Information Systems CSE 412 Database Management CSE 414 Advanced Database Concepts CSE 432 O ...
... Approved 400-Level courses to count towards CSE Graduate Program IMPORTANT: Students who have taken any of the 4XX courses listed below as 598, cannot take the same class at the 400-level. CSE 408 Multimedia Information Systems CSE 412 Database Management CSE 414 Advanced Database Concepts CSE 432 O ...
Reed - Virtual Local Area Networks in Security
... of the routers and the network itself. VLANs also give the network administrator the ability to form virtual workgroups for departments, divisions or groups throughout an enterprise. It is common for different departments or groups to work together in organizations on certain projects that may last ...
... of the routers and the network itself. VLANs also give the network administrator the ability to form virtual workgroups for departments, divisions or groups throughout an enterprise. It is common for different departments or groups to work together in organizations on certain projects that may last ...
SNMP Simple Network Management Protocol - CS-UCY
... • Security model of SNMPv3 has two components: 1.Instead of granting access rights to a community, SNMPv3 grants access to users. 2. Access can be restricted to sections of the MIB (Versionbased Access Control Module (VACM). Access rights can be limited • by specifying a range of valid IP addresses ...
... • Security model of SNMPv3 has two components: 1.Instead of granting access rights to a community, SNMPv3 grants access to users. 2. Access can be restricted to sections of the MIB (Versionbased Access Control Module (VACM). Access rights can be limited • by specifying a range of valid IP addresses ...
Protecting the connected barrels | Cybersecurity for
... sors and programmable logic controllers are intended to perform tasks with 24X7 availability as their primary attribute, followed by integrity and confidentiality. In contrast, IT systems such as enterprise resource planning have a reverse priority order of confidentiality, integrity, and availabili ...
... sors and programmable logic controllers are intended to perform tasks with 24X7 availability as their primary attribute, followed by integrity and confidentiality. In contrast, IT systems such as enterprise resource planning have a reverse priority order of confidentiality, integrity, and availabili ...
SNMP Vulnerabilities - Department of Computer Science
... SNMP is a standard protocol that is used by network professionals to manage networks and systems. By using computer applications that incorporate SNMP, network operators can query a device on their network to get its status, be alerted to a change in its status, or make configuration changes. SNMP i ...
... SNMP is a standard protocol that is used by network professionals to manage networks and systems. By using computer applications that incorporate SNMP, network operators can query a device on their network to get its status, be alerted to a change in its status, or make configuration changes. SNMP i ...
BIND - University of Guelph
... 5. Authentication tag binds the output data with the code that has generated it. 6. BINDs undoes the protection it has set up for the protection. 7. BINDs returns the authenticator to the process. ...
... 5. Authentication tag binds the output data with the code that has generated it. 6. BINDs undoes the protection it has set up for the protection. 7. BINDs returns the authenticator to the process. ...
Aspects of Biological Evolution and Their
... .rhost file can either contain a list of machine-user name pairs, one per line, of systems and users that have access to the machine or simply a line containing the machine name. In the first case the rights that these users have access to are based on the position of the .rhost file in the director ...
... .rhost file can either contain a list of machine-user name pairs, one per line, of systems and users that have access to the machine or simply a line containing the machine name. In the first case the rights that these users have access to are based on the position of the .rhost file in the director ...
PaaS Acceptable Use Policy
... scanning, and avoidance of third party network security, restrictions or limitations. ...
... scanning, and avoidance of third party network security, restrictions or limitations. ...
Application research and analysis based on Bitlocker
... option selected "allows Bitlockerisas without compatible TPM", confirm exit from the local group policy editor, then Windows 7 operating system uses of Bitlocker encryption system boot disk in the case of without installingtrusted platform module of TPM1.2 version. Encryption started, open the deskt ...
... option selected "allows Bitlockerisas without compatible TPM", confirm exit from the local group policy editor, then Windows 7 operating system uses of Bitlocker encryption system boot disk in the case of without installingtrusted platform module of TPM1.2 version. Encryption started, open the deskt ...
Acceptable Use Policy
... of its Clients. Any questions or comments regarding this AUP should be directed to [email protected] or [email protected] 2) Prohibited Content. Clients shall not allow the posting, transmission, or storage of data and content on or through the Services which constitutes a violation of any relevan ...
... of its Clients. Any questions or comments regarding this AUP should be directed to [email protected] or [email protected] 2) Prohibited Content. Clients shall not allow the posting, transmission, or storage of data and content on or through the Services which constitutes a violation of any relevan ...
ipSecMicrosof
... through a NAT device that allows UDP traffic. The Internet Key Exchange (IKE) protocol automatically detects the presence of a NAT device and uses ...
... through a NAT device that allows UDP traffic. The Internet Key Exchange (IKE) protocol automatically detects the presence of a NAT device and uses ...
1 Notification of the Office of the Securities and Exchange
... and deregister the old devices to ensure that the use of mobile devices complies with the information security policy. The intermediary may use other registration technology instead if considered appropriate; (2) establish a measure for protection of confidential or sensitive data in case of loss of ...
... and deregister the old devices to ensure that the use of mobile devices complies with the information security policy. The intermediary may use other registration technology instead if considered appropriate; (2) establish a measure for protection of confidential or sensitive data in case of loss of ...
Advanced Operating Systems, CSci555
... Security is more than mix of point solutions • Today’s security tools work with no coordinated policy – Firewalls and Virtual Private Networks – Authentication and Public Key Infrastructure – Intrusion Detection and limited response • We need better coordination – Intrusion response affected at fir ...
... Security is more than mix of point solutions • Today’s security tools work with no coordinated policy – Firewalls and Virtual Private Networks – Authentication and Public Key Infrastructure – Intrusion Detection and limited response • We need better coordination – Intrusion response affected at fir ...
Title Size 30PT
... Snort is the most widely deployed IDS/IPS technology worldwide. With millions of downloads and nearly 400,000 registered users, Snort has become the de facto standard for IPS. See more at http://www.snort.org. Never designed to be application aware Presentation_ID ...
... Snort is the most widely deployed IDS/IPS technology worldwide. With millions of downloads and nearly 400,000 registered users, Snort has become the de facto standard for IPS. See more at http://www.snort.org. Never designed to be application aware Presentation_ID ...
Security of Cookies in a computer lab setting
... – Provides high security because no cookies are formed – Takes away from the “Full Web Experience” ...
... – Provides high security because no cookies are formed – Takes away from the “Full Web Experience” ...