GTS SAN Usage A UNIX SysAdmin`s View of How A SAN Works
... Hides Individual Devices Provide One Large Virtual Resource ...
... Hides Individual Devices Provide One Large Virtual Resource ...
15-441 Lecture 5
... standard for data transport over optical fiber. •One of the design goals was to be backwards compatible with many older telco standards. •Beside minimal framing functionality, it provides many other functions: ...
... standard for data transport over optical fiber. •One of the design goals was to be backwards compatible with many older telco standards. •Beside minimal framing functionality, it provides many other functions: ...
Datasheet - EnOcean Alliance
... with 256 telegrams), the application can even be used on a UMTS or GPRS connected device. ...
... with 256 telegrams), the application can even be used on a UMTS or GPRS connected device. ...
Basics of Networking
... A connection oriented socket. Connection is established Messages are acknowledged when received. Acknowledge bytes received to ensure the correctness of message In actuality, built on top of datagram socket with extra messages to maintain connection state Used in TCP protocol ...
... A connection oriented socket. Connection is established Messages are acknowledged when received. Acknowledge bytes received to ensure the correctness of message In actuality, built on top of datagram socket with extra messages to maintain connection state Used in TCP protocol ...
Computer Networking From LANs to WANs: Hardware, Software
... Serial Data Communication (cont’d.) • Parity bits – Determine error in the received character – Odd parity • Occurs if odd number of 1s ...
... Serial Data Communication (cont’d.) • Parity bits – Determine error in the received character – Odd parity • Occurs if odd number of 1s ...
R7200 SDSL Routers
... and e-mail servers, transferring large files, video teleconferencing and connecting remote corporate locations. The multispeed feature of SDSL enables initial service configuration at any speed, then as bandwidth needs grow, increases speed up to 1.5 Mbps with no additional hardware investment. ...
... and e-mail servers, transferring large files, video teleconferencing and connecting remote corporate locations. The multispeed feature of SDSL enables initial service configuration at any speed, then as bandwidth needs grow, increases speed up to 1.5 Mbps with no additional hardware investment. ...
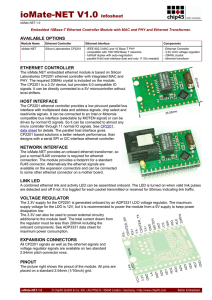
ioMate-NET V1.0 Infosheet
... The 3.3V supply for the CP2201 is generated onboard by an ADP3331 LDO voltage regulator. The maximum supply voltage for the LDO is 12V, but it is recommended to power the module from a 5V supply to keep power dissipation low. The 3.3V can also be used to power external circuitry additional to the mo ...
... The 3.3V supply for the CP2201 is generated onboard by an ADP3331 LDO voltage regulator. The maximum supply voltage for the LDO is 12V, but it is recommended to power the module from a 5V supply to keep power dissipation low. The 3.3V can also be used to power external circuitry additional to the mo ...
Presentation
... • Modems transfer bits over the phone line • Three possible errors can occur: a bit can be lost, an extraneous bit can be introduced, or a bit can be flipped (changed from zero to one or from one to zero) • The most basic form of error correction involves the start and stop bits • Each eight-bit byt ...
... • Modems transfer bits over the phone line • Three possible errors can occur: a bit can be lost, an extraneous bit can be introduced, or a bit can be flipped (changed from zero to one or from one to zero) • The most basic form of error correction involves the start and stop bits • Each eight-bit byt ...
Bit and Byte Stuffing
... Asynchronous transmission :: each character (or byte) is treated independently for clock (bit) and character (byte) synchronization purposes and the receiver resynchronizes at the start of each character received. Synchronous transmission :: the complete frame is transmitted as a contiguous string o ...
... Asynchronous transmission :: each character (or byte) is treated independently for clock (bit) and character (byte) synchronization purposes and the receiver resynchronizes at the start of each character received. Synchronous transmission :: the complete frame is transmitted as a contiguous string o ...
Bit and Byte Stuffing
... Character or byte level : recognizing the start and end of each character (or small unit of data) Block or message level : recognize the start and end of each large unit of data (in networks this is a frame). Networks: Bit and Byte Stuffing ...
... Character or byte level : recognizing the start and end of each character (or small unit of data) Block or message level : recognize the start and end of each large unit of data (in networks this is a frame). Networks: Bit and Byte Stuffing ...
Networks: Bit and Byte Stuffing
... – Character or byte level : recognizing the start and end of each character (or small unit of data) – Block or message level : recognize the start and end of each large unit of data (in networks this is a frame). Networks: Bit and Byte Stuffing ...
... – Character or byte level : recognizing the start and end of each character (or small unit of data) – Block or message level : recognize the start and end of each large unit of data (in networks this is a frame). Networks: Bit and Byte Stuffing ...
ppt
... Character or byte level : recognizing the start and end of each character (or small unit of data) Block or message level : recognize the start and end of each large unit of data (in networks this is a frame). Networks: Bit and Byte Stuffing ...
... Character or byte level : recognizing the start and end of each character (or small unit of data) Block or message level : recognize the start and end of each large unit of data (in networks this is a frame). Networks: Bit and Byte Stuffing ...
01_NF_CH04_OSITransportLayer
... Establishing a Session - The Transport layer can provide this connection orientation by creating a sessions between the applications. These connections prepare the applications to communicate with each other before any data is transmitted. Reliable Delivery - The Transport layer can ensure that all ...
... Establishing a Session - The Transport layer can provide this connection orientation by creating a sessions between the applications. These connections prepare the applications to communicate with each other before any data is transmitted. Reliable Delivery - The Transport layer can ensure that all ...
Canold
... The message acceptance filters and masks are used to determine if a message in the message assembly buffer should be loaded into either of the receive buffers. Once a valid message has been received into the Message Assembly Buffer (MAB), the identifier fields of the message are compared to the filt ...
... The message acceptance filters and masks are used to determine if a message in the message assembly buffer should be loaded into either of the receive buffers. Once a valid message has been received into the Message Assembly Buffer (MAB), the identifier fields of the message are compared to the filt ...
Mini Tower Computer
... NOTICE: The voltage selection switch must be set to the 115-V position even though the AC power available in Japan is 100 V. Also, ensure that your monitor and attached devices are electrically rated to operate with the AC power available in your location. ...
... NOTICE: The voltage selection switch must be set to the 115-V position even though the AC power available in Japan is 100 V. Also, ensure that your monitor and attached devices are electrically rated to operate with the AC power available in your location. ...
(CCNA) 3.Transport Layer Protocols
... and receivers to exchange information about their availability or ability to communicate with one another, “best effort” delivery. (Type supported by IP, UDP). Not reliable, but faster and may be good enough. Also upper layer apps may worry about errors and reliability processing, so no need to do i ...
... and receivers to exchange information about their availability or ability to communicate with one another, “best effort” delivery. (Type supported by IP, UDP). Not reliable, but faster and may be good enough. Also upper layer apps may worry about errors and reliability processing, so no need to do i ...
Bit and Byte Stuffing
... Starting/ending bytes [byte stuffing] Starting/ending flags [bit stuffing] Using physical layer coding violations (i.e., invalid physical codes) Bit and Byte Stuffing ...
... Starting/ending bytes [byte stuffing] Starting/ending flags [bit stuffing] Using physical layer coding violations (i.e., invalid physical codes) Bit and Byte Stuffing ...
Transport Layer Protocols TCP and UDP
... and receivers to exchange information about their availability or ability to communicate with one another, “best effort” delivery. (Type supported by IP, UDP). Not reliable, but faster and may be good enough. Also upper layer apps may worry about errors and reliability processing, so no need to do i ...
... and receivers to exchange information about their availability or ability to communicate with one another, “best effort” delivery. (Type supported by IP, UDP). Not reliable, but faster and may be good enough. Also upper layer apps may worry about errors and reliability processing, so no need to do i ...
Document
... and receivers to exchange information about their availability or ability to communicate with one another, “best effort” delivery. (Type supported by IP, UDP). Not reliable, but faster and may be good enough. Also upper layer apps may worry about errors and reliability processing, so no need to do i ...
... and receivers to exchange information about their availability or ability to communicate with one another, “best effort” delivery. (Type supported by IP, UDP). Not reliable, but faster and may be good enough. Also upper layer apps may worry about errors and reliability processing, so no need to do i ...
pushpavathi_a
... as a message with the highest priority will never take longer than 259 bit times for transmission. 4.4. ERROR HANDLING The following mechanisms are used in the CAN protocol for error detection: A transmitter checks whether sent out bits appear on the bus. Cyclic redundancy check (CRC) Bit stuf ...
... as a message with the highest priority will never take longer than 259 bit times for transmission. 4.4. ERROR HANDLING The following mechanisms are used in the CAN protocol for error detection: A transmitter checks whether sent out bits appear on the bus. Cyclic redundancy check (CRC) Bit stuf ...
Inner Boards
... CQM1H to a ControllerLink network. Large amounts of data can be transferred easily and flexibly with personal computers as well with other Omron PLCs that support Controller Link. ...
... CQM1H to a ControllerLink network. Large amounts of data can be transferred easily and flexibly with personal computers as well with other Omron PLCs that support Controller Link. ...
IP20 Ethernet Switches and Media Converter
... and Media Converter For industrial and harsh commercial environments where the need for IP 67 connectivity is not required, Ethernet switching components can be housed in a protective controls enclosure. However, the vibration and temperature operating ranges offered by standard datacoms switches an ...
... and Media Converter For industrial and harsh commercial environments where the need for IP 67 connectivity is not required, Ethernet switching components can be housed in a protective controls enclosure. However, the vibration and temperature operating ranges offered by standard datacoms switches an ...
SPI - Personal Web Pages
... they were requested to develop a communication system between three ECUs (electronic control units) in vehicles by Mercedes. • They found that an UART is no longer suitable in this situation because it is used in point-to-point communication. The need for a multi-master communication system became i ...
... they were requested to develop a communication system between three ECUs (electronic control units) in vehicles by Mercedes. • They found that an UART is no longer suitable in this situation because it is used in point-to-point communication. The need for a multi-master communication system became i ...
Serial port

In computing, a serial port is a serial communication physical interface through which information transfers in or out one bit at a time (in contrast to a parallel port). Throughout most of the history of personal computers, data was transferred through serial ports to devices such as modems, terminals and various peripherals.While such interfaces as Ethernet, FireWire, and USB all send data as a serial stream, the term ""serial port"" usually identifies hardware more or less compliant to the RS-232 standard, intended to interface with a modem or with a similar communication device.Modern computers without serial ports may require serial-to-USB converters to allow compatibility with RS 232 serial devices. Serial ports are still used in applications such as industrial automation systems, scientific instruments, point of sale systems and some industrial and consumer products. Server computers may use a serial port as a control console for diagnostics. Network equipment (such as routers and switches) often use serial console for configuration. Serial ports are still used in these areas as they are simple, cheap and their console functions are highly standardized and widespread. A serial port requires very little supporting software from the host system.