Document
... networking software to connect to each other’s hard disks with the intention of directly exchanging files. To maintain acceptable network speeds, most Internet ...
... networking software to connect to each other’s hard disks with the intention of directly exchanging files. To maintain acceptable network speeds, most Internet ...
Data Communication & Network
... • Packet switching: storeand-forward messages a. operates on discrete blocks of data b. utilizes resources according to traffic demand c. send/receive messages at variable rate d. example: Internet ...
... • Packet switching: storeand-forward messages a. operates on discrete blocks of data b. utilizes resources according to traffic demand c. send/receive messages at variable rate d. example: Internet ...
Locating Equivalent
... system and, consequently, they propose mechanisms to overcome these limitations... 2. Structured DHT based P2P Overlays Structured - Overlay network topology is tightly controlled and content are placed not at random peers but at specified locations that will make subsequent queries more efficient ...
... system and, consequently, they propose mechanisms to overcome these limitations... 2. Structured DHT based P2P Overlays Structured - Overlay network topology is tightly controlled and content are placed not at random peers but at specified locations that will make subsequent queries more efficient ...
Local Area Networks
... • Each node uses a special device, called a network interface card (NIC). The card connects to the network media and controls the flow of data. • NICs must use a common network technology to communicate. The most popular network technologies for LANs are Ethernet, Fast Ethernet, and Token Ring. ...
... • Each node uses a special device, called a network interface card (NIC). The card connects to the network media and controls the flow of data. • NICs must use a common network technology to communicate. The most popular network technologies for LANs are Ethernet, Fast Ethernet, and Token Ring. ...
N4Less17.pps - GEOCITIES.ws
... • Each node uses a special device, called a network interface card (NIC). The card connects to the network media and controls the flow of data. • NICs must use a common network technology to communicate. The most popular network technologies for LANs are Ethernet, Fast Ethernet, and Token Ring. ...
... • Each node uses a special device, called a network interface card (NIC). The card connects to the network media and controls the flow of data. • NICs must use a common network technology to communicate. The most popular network technologies for LANs are Ethernet, Fast Ethernet, and Token Ring. ...
3 - Computer Network - Basic Concepts
... organization or entity but which also has limited connections to the networks of one or more other usually, but not necessarily, trusted organizations or entities by definition, an extranet cannot consist of a single LAN; it must have at least one connection with an external network. ...
... organization or entity but which also has limited connections to the networks of one or more other usually, but not necessarily, trusted organizations or entities by definition, an extranet cannot consist of a single LAN; it must have at least one connection with an external network. ...
Peer to Peer Network with Application
... Can ensure correct results Fast search Bottleneck for scalability Single point of failure Susceptible to denial of service • Malicious users • Lawsuits, legislation ...
... Can ensure correct results Fast search Bottleneck for scalability Single point of failure Susceptible to denial of service • Malicious users • Lawsuits, legislation ...
25th IEEE International Conference on Network Protocols
... submission. Papers cannot be previously published nor under review by another conference or journal. Papers containing plagiarized material will be subject to the IEEE plagiarism policy and will be rejected without review. Topics of interest include, but are not limited to: All aspects of network ...
... submission. Papers cannot be previously published nor under review by another conference or journal. Papers containing plagiarized material will be subject to the IEEE plagiarism policy and will be rejected without review. Topics of interest include, but are not limited to: All aspects of network ...
Networks
... Users share software File server enables all users to work with the same application program Building information resources Users create common pools of data that can be accessed by employees ...
... Users share software File server enables all users to work with the same application program Building information resources Users create common pools of data that can be accessed by employees ...
slides - Academia Sinica
... clients request “work unit” to process Communication is minimized Clients do not communicate ...
... clients request “work unit” to process Communication is minimized Clients do not communicate ...
Interacting Network Elements: Chaos and Congestion Propagation
... congestion propagation in a sequence of highly congested routers at Keo University, Japan in 1999. We think that this phenomenon will be a general feature in the new network environments. It will be verified why such propagation occurs in TCP/IP traffic. ...
... congestion propagation in a sequence of highly congested routers at Keo University, Japan in 1999. We think that this phenomenon will be a general feature in the new network environments. It will be verified why such propagation occurs in TCP/IP traffic. ...
Computer Networks
... organization or entity but which also has limited connections to the networks of one or more other usually, but not necessarily, trusted organizations or entities by definition, an extranet cannot consist of a single LAN; it must have at least one connection with an external network. ...
... organization or entity but which also has limited connections to the networks of one or more other usually, but not necessarily, trusted organizations or entities by definition, an extranet cannot consist of a single LAN; it must have at least one connection with an external network. ...
Napster & Gnutella
... • Peers respond with a “QueryHit” (contains contact info) • File transfers use direct connection using HTTP protocol’s GET method • When there is a firewall a "Push" packet is used – reroutes via Push path ...
... • Peers respond with a “QueryHit” (contains contact info) • File transfers use direct connection using HTTP protocol’s GET method • When there is a firewall a "Push" packet is used – reroutes via Push path ...
Lecture 9 & 10
... of four (or more) copper wires twisted around each other within a plastic sheath 2. Coaxial cable: carries a wide range of frequencies with ...
... of four (or more) copper wires twisted around each other within a plastic sheath 2. Coaxial cable: carries a wide range of frequencies with ...
This is a Powerpoint
... Freedom Foundation, high-tech trade groups (such as the National Association of Manufacturers), and others oppose network neutrality. ...
... Freedom Foundation, high-tech trade groups (such as the National Association of Manufacturers), and others oppose network neutrality. ...
Slide 1
... What is P2P systems? Multiple sites (at edge) Distributed resources Sites are autonomous (different owners) Sites are both clients and servers Sites have equal functionality ...
... What is P2P systems? Multiple sites (at edge) Distributed resources Sites are autonomous (different owners) Sites are both clients and servers Sites have equal functionality ...
FF36968971
... Efficient use of network resources but resource is small due to size limitation of the resource, it is very important to increase the scalability of the system with large system process. It is a type of decentralized and distributed network architecture in which every node act as a both supplier a ...
... Efficient use of network resources but resource is small due to size limitation of the resource, it is very important to increase the scalability of the system with large system process. It is a type of decentralized and distributed network architecture in which every node act as a both supplier a ...
Data Communication Network
... A great deal of technology is required for one device to connect and communicate with another, and many choices for physical connections and related software are possible ...
... A great deal of technology is required for one device to connect and communicate with another, and many choices for physical connections and related software are possible ...
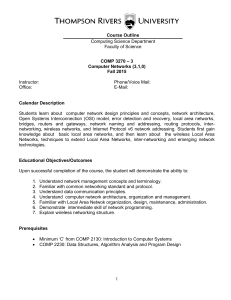
1 Course Outline Computing Science Department Faculty of Science
... Students learn about computer network design principles and concepts, network architecture, Open Systems Interconnection (OSI) model, error detection and recovery, local area networks, bridges, routers and gateways, network naming and addressing, routing protocols, internetworking, wireless networks ...
... Students learn about computer network design principles and concepts, network architecture, Open Systems Interconnection (OSI) model, error detection and recovery, local area networks, bridges, routers and gateways, network naming and addressing, routing protocols, internetworking, wireless networks ...
File
... 15. Network ___________________________ are the design of computers, devices, and media in a network. 16. What are the two categories of network architectures? a. _____________________________, b. _____________________________ 17. A server is a _______________ computer which controls access to hardw ...
... 15. Network ___________________________ are the design of computers, devices, and media in a network. 16. What are the two categories of network architectures? a. _____________________________, b. _____________________________ 17. A server is a _______________ computer which controls access to hardw ...
Nearcast: A Locality-Aware P2P Live Streaming Approach for
... • The topology mismatch problem brings great link stress (unnecessary traffic) in the Internet infrastructure and greatly degrades the system performance. • In this article, we address this problem and propose a localityaware P2P overlay construction method, called Nearcast, which builds an efficien ...
... • The topology mismatch problem brings great link stress (unnecessary traffic) in the Internet infrastructure and greatly degrades the system performance. • In this article, we address this problem and propose a localityaware P2P overlay construction method, called Nearcast, which builds an efficien ...
Peer-to-peer
Peer-to-peer (P2P) computing or networking is a distributed application architecture that partitions tasks or work loads between peers. Peers are equally privileged, equipotent participants in the application. They are said to form a peer-to-peer network of nodes.Peers make a portion of their resources, such as processing power, disk storage or network bandwidth, directly available to other network participants, without the need for central coordination by servers or stable hosts. Peers are both suppliers and consumers of resources, in contrast to the traditional client-server model in which the consumption and supply of resources is divided. Emerging collaborative P2P systems are going beyond the era of peers doing similar things while sharing resources, and are looking for diverse peers that can bring in unique resources and capabilities to a virtual community thereby empowering it to engage in greater tasks beyond those that can be accomplished by individual peers, yet that are beneficial to all the peers.While P2P systems had previously been used in many application domains, the architecture was popularized by the file sharing system Napster, originally released in 1999. The concept has inspired new structures and philosophies in many areas of human interaction. In such social contexts, peer-to-peer as a meme refers to the egalitarian social networking that has emerged throughout society, enabled by Internet technologies in general.