Kernel
... – memory resident part of UNIX – majority written in C rest in assembler language (HW dependent, speed) – a.out (a plain C a.out program) – consists of functions • other programs can call (some of) these functions • called “system call function” ...
... – memory resident part of UNIX – majority written in C rest in assembler language (HW dependent, speed) – a.out (a plain C a.out program) – consists of functions • other programs can call (some of) these functions • called “system call function” ...
What is an Operating System?
... bits, it is amazing how many things a computer can represent: numbers, letters, images, movies, sounds, documents, and programs, to name a few. A byte is 8 bits, and on most computers it is the smallest convenient chunk of storage. For example, most computers don’t have an instruction to move a bit ...
... bits, it is amazing how many things a computer can represent: numbers, letters, images, movies, sounds, documents, and programs, to name a few. A byte is 8 bits, and on most computers it is the smallest convenient chunk of storage. For example, most computers don’t have an instruction to move a bit ...
Chapter 1 - cse.sc.edu
... Given enough bits, it is amazing how many things a computer can represent: numbers, letters, images, movies, sounds, documents, and programs, to name a few. A byte is 8 bits, and on most computers it is the smallest convenient chunk of storage. For example, most computers don’t have an instruction t ...
... Given enough bits, it is amazing how many things a computer can represent: numbers, letters, images, movies, sounds, documents, and programs, to name a few. A byte is 8 bits, and on most computers it is the smallest convenient chunk of storage. For example, most computers don’t have an instruction t ...
ppt
... (a) would be useful for UDP-based service, e.g. NTP (network time protocol) (b) is the most commonly used - matches the TCP connection model (c) is used where the service is encapsulated as an object. E.g. could have multiple shared whiteboards with one thread each. Each object has only one thread, ...
... (a) would be useful for UDP-based service, e.g. NTP (network time protocol) (b) is the most commonly used - matches the TCP connection model (c) is used where the service is encapsulated as an object. E.g. could have multiple shared whiteboards with one thread each. Each object has only one thread, ...
File
... 5. What are the goals of operating systems? Operating systems must 1. Provide for efficient use of computer hardware. 2. Provide a reliable environment for the running of programs. 3. Handle errors reasonably and with sufficient feedback. 4. Provide services (tools, languages) for users. 5. Hide the ...
... 5. What are the goals of operating systems? Operating systems must 1. Provide for efficient use of computer hardware. 2. Provide a reliable environment for the running of programs. 3. Handle errors reasonably and with sufficient feedback. 4. Provide services (tools, languages) for users. 5. Hide the ...
File System
... Second type avoids copying large messages by pointing to a shared memory section object created for the channel ...
... Second type avoids copying large messages by pointing to a shared memory section object created for the channel ...
ch1
... Given enough bits, it is amazing how many things a computer can represent: numbers, letters, images, movies, sounds, documents, and programs, to name a few. A byte is 8 bits, and on most computers it is the smallest convenient chunk of storage. For example, most computers don’t have an instruction t ...
... Given enough bits, it is amazing how many things a computer can represent: numbers, letters, images, movies, sounds, documents, and programs, to name a few. A byte is 8 bits, and on most computers it is the smallest convenient chunk of storage. For example, most computers don’t have an instruction t ...
No Slide Title
... Second type avoids copying large messages by pointing to a shared memory section object created for the channel ...
... Second type avoids copying large messages by pointing to a shared memory section object created for the channel ...
SimOS: A Fast Operating System Simulation Environment
... Significant amounts of time and money are spent on the development, tuning, and maintenance of operating system software. These costs are partly due to the high standards of correctness and performance expected by the users of operating systems. The presence of bugs in the system software can have v ...
... Significant amounts of time and money are spent on the development, tuning, and maintenance of operating system software. These costs are partly due to the high standards of correctness and performance expected by the users of operating systems. The presence of bugs in the system software can have v ...
Lecture3-os-support
... • Compiler checks safe memory access • In addition there are manifests w.r.t. what the process will and will not do • This way you get protection • And no need for hardware protection domains – everything can run in a single address space • Singularity: an OS from Microsoft implemented these concept ...
... • Compiler checks safe memory access • In addition there are manifests w.r.t. what the process will and will not do • This way you get protection • And no need for hardware protection domains – everything can run in a single address space • Singularity: an OS from Microsoft implemented these concept ...
Introduction - McMaster Computing and Software
... Timesharing (multitasking) is logical extension of multiprogramming ...
... Timesharing (multitasking) is logical extension of multiprogramming ...
PowerPoint Chapter 13
... Block devices include disk drives Commands include read, write, seek Raw I/O or file-system access Memory-mapped file access possible Character devices include keyboards, mice, serial ports Commands include get, put Libraries layered on top allow line editing ...
... Block devices include disk drives Commands include read, write, seek Raw I/O or file-system access Memory-mapped file access possible Character devices include keyboards, mice, serial ports Commands include get, put Libraries layered on top allow line editing ...
Chapter 13: I/O Systems I/O Hardware
... ■ Block devices include disk drives ✦ Commands include read, write, seek ✦ Raw I/O or file-system access ✦ Memory-mapped file access possible ■ Character devices include keyboards, mice, serial ports ✦ Commands include get, put ✦ Libraries layered on top allow line editing ...
... ■ Block devices include disk drives ✦ Commands include read, write, seek ✦ Raw I/O or file-system access ✦ Memory-mapped file access possible ■ Character devices include keyboards, mice, serial ports ✦ Commands include get, put ✦ Libraries layered on top allow line editing ...
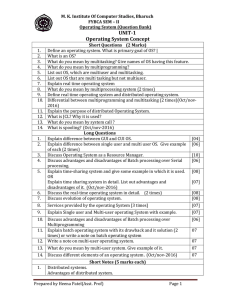
UNIT-1 Operating System Concept
... List the advantages of linked allocation over contiguous allocation. Explain the role of DMA Differentiate between SCAN and C-SCAN disk scheduling policy. List out different characteristic of I/O devices. 2times. (Oct/nov-2016) What do you mean by block device? Does contiguous allocation suffer form ...
... List the advantages of linked allocation over contiguous allocation. Explain the role of DMA Differentiate between SCAN and C-SCAN disk scheduling policy. List out different characteristic of I/O devices. 2times. (Oct/nov-2016) What do you mean by block device? Does contiguous allocation suffer form ...
File System - dhdurso.org index to available resources
... The block and fragment sizes are set during file-system creation according to the intended use of the file system: – If many small files are expected, the fragment size should be small. – If repeated transfers of large files are expected, the basic block size should be large. The maximum block-to-fr ...
... The block and fragment sizes are set during file-system creation according to the intended use of the file system: – If many small files are expected, the fragment size should be small. – If repeated transfers of large files are expected, the basic block size should be large. The maximum block-to-fr ...
Introduction
... in hardware. Is it possible to construct a secure operating system for these computer systems? Give arguments both that it is and that it is not possible. Answer: An operating system for a machine of this type would need to remain in control (or monitor mode) at all times. This could be accomplished ...
... in hardware. Is it possible to construct a secure operating system for these computer systems? Give arguments both that it is and that it is not possible. Answer: An operating system for a machine of this type would need to remain in control (or monitor mode) at all times. This could be accomplished ...
The 27 Year Old Microkernel - foundry27
... Ex: Blocking kernel causes current thread to be blocked, another to be made RUNNING > __ker_exit implements this ...
... Ex: Blocking kernel causes current thread to be blocked, another to be made RUNNING > __ker_exit implements this ...
Chapter 1: Introduction
... The basic unit of computer storage is the bit. A bit can contain one of two values, 0 and 1. All other storage in a computer is based on collections of bits. Given enough bits, it is amazing how many things a computer can represent: numbers, letters, images, movies, sounds, documents, and programs, ...
... The basic unit of computer storage is the bit. A bit can contain one of two values, 0 and 1. All other storage in a computer is based on collections of bits. Given enough bits, it is amazing how many things a computer can represent: numbers, letters, images, movies, sounds, documents, and programs, ...
Real-time Operating Systems - Institute of Computer Engineering
... Tasks are executed inside kernel memory space, which prevents threads to be swapped-out and also the number of TLB misses is reduced. Threads are executed in processor supervisor mode (i.e. ring level 0 in i386 arch), have full access to the underlying hardware. Since the RTOS and the applicat ...
... Tasks are executed inside kernel memory space, which prevents threads to be swapped-out and also the number of TLB misses is reduced. Threads are executed in processor supervisor mode (i.e. ring level 0 in i386 arch), have full access to the underlying hardware. Since the RTOS and the applicat ...
9781439079201_PPT_ch12
... – File organization • Example: file records stored noncontiguously • Time consuming and requires compaction (CPU time) ...
... – File organization • Example: file records stored noncontiguously • Time consuming and requires compaction (CPU time) ...
Introduction
... Given enough bits, it is amazing how many things a computer can represent: numbers, letters, images, movies, sounds, documents, and programs, to name a few. A byte is 8 bits, and on most computers it is the smallest convenient chunk of storage. For example, most computers don’t have an instruction t ...
... Given enough bits, it is amazing how many things a computer can represent: numbers, letters, images, movies, sounds, documents, and programs, to name a few. A byte is 8 bits, and on most computers it is the smallest convenient chunk of storage. For example, most computers don’t have an instruction t ...
Plan 9 from Bell Labs
.png?width=300)
Plan 9 from Bell Labs is a distributed operating system, originally developed by the Computing Sciences Research Center at Bell Labs between the mid-1980s and 2002. It takes some of the principles of Unix, developed in the same research group, but extends these to a networked environment with graphics terminals.In Plan 9, virtually all computing resources, including files, network connections, and peripheral devices, are represented through the file system rather than specialized interfaces. A unified network protocol called 9P ties a network of computers running Plan 9 together, allowing them to share all resources so represented.The name Plan 9 from Bell Labs is a reference to the Ed Wood 1959 cult science fiction Z-movie Plan 9 from Outer Space. Also, Glenda, the Plan 9 Bunny, is presumably a reference to Wood's film Glen or Glenda. The system continues to be used and developed by operating system researchers and hobbyists.