ITT04103-LAN-Topologies-Lecture-2
... data transfer doesn’t get affected. That is it has multiple links, so if one route is blocked then other routes can be used for data communication. • Each connection can have its own data load, so the traffic problem is eliminated. • It is easy to troubleshoot mesh topology compared with other topol ...
... data transfer doesn’t get affected. That is it has multiple links, so if one route is blocked then other routes can be used for data communication. • Each connection can have its own data load, so the traffic problem is eliminated. • It is easy to troubleshoot mesh topology compared with other topol ...
word
... The lower three layers usually are implemented on a hardware called the network interface controller. Having the NIC to have a processor in it makes it real smart and a number of operations such as error correction (CRC check), calculating routes, processing headers, etc… can be done in hardware. Ha ...
... The lower three layers usually are implemented on a hardware called the network interface controller. Having the NIC to have a processor in it makes it real smart and a number of operations such as error correction (CRC check), calculating routes, processing headers, etc… can be done in hardware. Ha ...
Ethernet Update
... Will look at the TCP/IP co-existence problem How to best deliver fibre performance to the application? Scalability Fault tolerance QoS Trunking ...
... Will look at the TCP/IP co-existence problem How to best deliver fibre performance to the application? Scalability Fault tolerance QoS Trunking ...
Document
... Schemes where every core knows which other core has a copy of its cached data are far too complex So each core (cache system) ‘snoops’ (i.e. watches continually) for activity concerned with data addresses which it has cached This has normally been implemented with a bus structure which is ‘glo ...
... Schemes where every core knows which other core has a copy of its cached data are far too complex So each core (cache system) ‘snoops’ (i.e. watches continually) for activity concerned with data addresses which it has cached This has normally been implemented with a bus structure which is ‘glo ...
Android Physical Extraction - FAQ
... this cannot be done when the device is locked. However, in some cases the user could have turned on USB debugging before locking the device. In this case you will be able to “bypass” the screen lock. If you successfully perform an extraction you will be able to see the Numeric password or pattern lo ...
... this cannot be done when the device is locked. However, in some cases the user could have turned on USB debugging before locking the device. In this case you will be able to “bypass” the screen lock. If you successfully perform an extraction you will be able to see the Numeric password or pattern lo ...
pdf file
... results indicate our network can model the data almost equivalent to the true model, with a different network structure (57 edges in our model versus 46 edges in the true model). We run WinMine using three different N values, 0.01 (default value), 0.002, and 8e-12, to adjust the network to have the ...
... results indicate our network can model the data almost equivalent to the true model, with a different network structure (57 edges in our model versus 46 edges in the true model). We run WinMine using three different N values, 0.01 (default value), 0.002, and 8e-12, to adjust the network to have the ...
- clicktechsolution.com
... In a single node topology, just a single device called dumb terminal is connected to the server Bus topology connects each device to a single cable and at either end of the cable terminator is used to remove unsent data from the cable In star topology, multiple devices are connected to a central con ...
... In a single node topology, just a single device called dumb terminal is connected to the server Bus topology connects each device to a single cable and at either end of the cable terminator is used to remove unsent data from the cable In star topology, multiple devices are connected to a central con ...
Document
... Start of frame – 1 dominant bit. A frame can only start when the bus is IDLE. All stations synchronize to the leading edge of the SOF bit Identifier – 11 (or 29 in version 2.0) bits. In order from most significant to least significant. The 7 most significant bits cannot be all recessive (all 1s) RTR ...
... Start of frame – 1 dominant bit. A frame can only start when the bus is IDLE. All stations synchronize to the leading edge of the SOF bit Identifier – 11 (or 29 in version 2.0) bits. In order from most significant to least significant. The 7 most significant bits cannot be all recessive (all 1s) RTR ...
File
... • Limited no of devices can be attached • Difficult to isolate problems • Sharing same cable slows response rates 10 ...
... • Limited no of devices can be attached • Difficult to isolate problems • Sharing same cable slows response rates 10 ...
Fundamentals of Computer Networks ECE 478/578
... Necessary to know what other fields to expect Typically “4” (for IPv4), and sometimes “6” (for IPv6) ...
... Necessary to know what other fields to expect Typically “4” (for IPv4), and sometimes “6” (for IPv6) ...
8085 Architecture & Its Assembly language programming
... We setup memory-buffers where we want received packets to be placed by the NIC We also create a list of buffer-descriptors and inform the NIC of its location and size Then, when ready, we tell the NIC to ‘Go!’ (i.e., start receiving), but to let us know when these receptions ...
... We setup memory-buffers where we want received packets to be placed by the NIC We also create a list of buffer-descriptors and inform the NIC of its location and size Then, when ready, we tell the NIC to ‘Go!’ (i.e., start receiving), but to let us know when these receptions ...
Abstract - Chennaisunday.com
... 4. Paging procedures for Slave:The inquirer identity is not known at the device that received an inquiry ID packet. After successful reply from the device in inquiry scan mode, instead, the inquirer knows the identity and the ...
... 4. Paging procedures for Slave:The inquirer identity is not known at the device that received an inquiry ID packet. After successful reply from the device in inquiry scan mode, instead, the inquirer knows the identity and the ...
Interconnection Networks
... • Need to match a wide range of I/O devices • Connects to the processor-memory bus or backplane bus ° Backplane Bus (industry standard) • Backplane: an interconnection structure within the chassis • Allow processors, memory, and I/O devices to coexist • Cost advantage: one single bus for all compone ...
... • Need to match a wide range of I/O devices • Connects to the processor-memory bus or backplane bus ° Backplane Bus (industry standard) • Backplane: an interconnection structure within the chassis • Allow processors, memory, and I/O devices to coexist • Cost advantage: one single bus for all compone ...
Communication Bus, Ethernet - Guide Specifications (Controls)
... telephone modem to a remote building. This interface shall allow any EMS operator’s station, as applicable, to communicate with any other remotely located, compatible, communications bus. ...
... telephone modem to a remote building. This interface shall allow any EMS operator’s station, as applicable, to communicate with any other remotely located, compatible, communications bus. ...
Controller Area Network (CAN) Basics
... pier to pier prioritized messages LIN master-slave single wire bus no quartz ...
... pier to pier prioritized messages LIN master-slave single wire bus no quartz ...
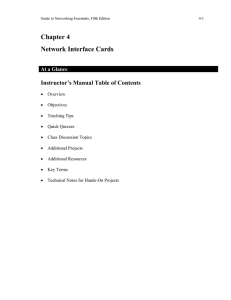
Guide to Networking Essentials, Fifth Edition
... operating system and a device for the purpose of sending and receiving input and output from that device. These drivers are operating system dependent. They also need to be kept up to date per information on the manufacturer’s Web site. diagnostic software — Specialized programs that can probe and ...
... operating system and a device for the purpose of sending and receiving input and output from that device. These drivers are operating system dependent. They also need to be kept up to date per information on the manufacturer’s Web site. diagnostic software — Specialized programs that can probe and ...
Networking Concepts
... • All of the stations in a star topology are connected to a central unit called a hub. – The hub offers a common connection for all stations on the network. Each station has its own direct cable connection to the hub. In most cases, this means more cable is required than for a bus topology. However, ...
... • All of the stations in a star topology are connected to a central unit called a hub. – The hub offers a common connection for all stations on the network. Each station has its own direct cable connection to the hub. In most cases, this means more cable is required than for a bus topology. However, ...
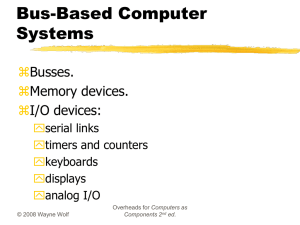
Networking for Embedded Systems
... Random-access memory Dynamic RAM is dense, requires refresh. Synchronous DRAM is dominant type. SDRAM uses clock to improve performance, pipeline memory accesses. ...
... Random-access memory Dynamic RAM is dense, requires refresh. Synchronous DRAM is dominant type. SDRAM uses clock to improve performance, pipeline memory accesses. ...
Media Access and Internet Working
... It receives incoming signal. It connected to ethernet adapter which is plugged into the host. transceiver ethernet ...
... It receives incoming signal. It connected to ethernet adapter which is plugged into the host. transceiver ethernet ...
Networked Connected Devices - Purdue University :: Computer
... • Control points can subscribe to events on state variables. • Events can be unicast or multicast (new in UPnP 1.1) – Multicast events allow devices to monitor state changes in other devices without implementing a control point. ...
... • Control points can subscribe to events on state variables. • Events can be unicast or multicast (new in UPnP 1.1) – Multicast events allow devices to monitor state changes in other devices without implementing a control point. ...
Slide 1
... • Typical I/O devices must transfer large amounts of data to memory of processor: – Disk must transfer complete block – Large packets from network – Regions of frame buffer ...
... • Typical I/O devices must transfer large amounts of data to memory of processor: – Disk must transfer complete block – Large packets from network – Regions of frame buffer ...
CIS 1140 Network Fundamentals
... – Motherboard uses to transmit data to computer’s components • Memory, processor, hard disk, NIC – Differ according to capacity • Defined by data path width and clock speed – Data path size • Parallel bits transmitting at any given time • Proportional to attached device’s speed Expansion slots – Mul ...
... – Motherboard uses to transmit data to computer’s components • Memory, processor, hard disk, NIC – Differ according to capacity • Defined by data path width and clock speed – Data path size • Parallel bits transmitting at any given time • Proportional to attached device’s speed Expansion slots – Mul ...
Low Pin Count

The Low Pin Count bus, or LPC bus, is used on IBM-compatible personal computers to connect low-bandwidth devices to the CPU, such as the boot ROM, ""legacy"" I/O devices (integrated into a super I/O chip), and Trusted Platform Module (TPM). ""Legacy"" I/O devices usually include serial and parallel ports, PS/2 keyboard, PS/2 mouse, and floppy disk controller.Most PC motherboards with a LPC bus have either a Platform Controller Hub (PCH) or a southbridge chip, which acts as the host and controls the LPC bus. All other devices connected to the physical wires of the LPC bus are peripherals.