OS - PESIT South
... 36. What are threads ? how do they differ from a process? Explain the difference in process level switching and thread level switching 37. Distinguish between symmetric and asymmetric communication between processes. 38. Define CPU utilization, throughput, and turnaround time, waiting time and respo ...
... 36. What are threads ? how do they differ from a process? Explain the difference in process level switching and thread level switching 37. Distinguish between symmetric and asymmetric communication between processes. 38. Define CPU utilization, throughput, and turnaround time, waiting time and respo ...
Protection of user process data in a secure platform architecture
... platform. An end user application is stored in the memory for controlling the processor and the memory, and operates on top of the operating system image. The secure platform is con?gured to provide a secure partition Within the memory for storing secret data associated With and acces sible by the e ...
... platform. An end user application is stored in the memory for controlling the processor and the memory, and operates on top of the operating system image. The secure platform is con?gured to provide a secure partition Within the memory for storing secret data associated With and acces sible by the e ...
Practical Taint-Based Protection using Demand Emulation
... an amorphous collection of bits, which may be used in arbitrary roles: In a stack-smashing attack, the data composing a web request is made to include modifications to a server’s call stack that compromise the system. Viruses and trojans may be attached to applications or included with email, and th ...
... an amorphous collection of bits, which may be used in arbitrary roles: In a stack-smashing attack, the data composing a web request is made to include modifications to a server’s call stack that compromise the system. Viruses and trojans may be attached to applications or included with email, and th ...
What is an Operating System?
... so frequently that users can interact with each job while it is running, creating interactive computing ...
... so frequently that users can interact with each job while it is running, creating interactive computing ...
On Memory Systems and Their Design
... what a typical processor requires. Disks are block-oriented devices, which means they read and write data only in large chunks; the typical granularity is 512 B. Processors, in contrast, typically operate at the granularity of 4 B or 8 B data words. To use a disk, a microprocessor must have addition ...
... what a typical processor requires. Disks are block-oriented devices, which means they read and write data only in large chunks; the typical granularity is 512 B. Processors, in contrast, typically operate at the granularity of 4 B or 8 B data words. To use a disk, a microprocessor must have addition ...
Chapter 1 - cse.sc.edu
... so frequently that users can interact with each job while it is running, creating interactive computing ...
... so frequently that users can interact with each job while it is running, creating interactive computing ...
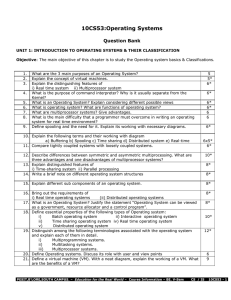
Dept. of Computer Science Engineering, School of Engineering
... Dept. of Computer Science Engineering, School of Engineering, Anurag Group of Institutions 39) In programmed I/O data transfer technique -------------triggers bus lines to select the proper device and to move bits into or put of a device register. Ans: UO instruction. 40) In ---------------- techni ...
... Dept. of Computer Science Engineering, School of Engineering, Anurag Group of Institutions 39) In programmed I/O data transfer technique -------------triggers bus lines to select the proper device and to move bits into or put of a device register. Ans: UO instruction. 40) In ---------------- techni ...
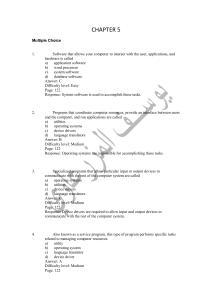
chapter 5
... Specialized programs that allow particular input or output devices to communicate with the rest of the computer system are called a) operating systems b) utilities c) device drivers d) language translators Answer: C Difficulty level: Medium Page: 122 Response: Device drivers are required to allow in ...
... Specialized programs that allow particular input or output devices to communicate with the rest of the computer system are called a) operating systems b) utilities c) device drivers d) language translators Answer: C Difficulty level: Medium Page: 122 Response: Device drivers are required to allow in ...
Chapter 3 Operating-System Structures 2
... Operating System Services • Program execution – system capability to load a program into memory and to run it. • I/O operations – since user programs cannot execute I/O operations directly, the operating system must provide some means to perform I/O. • File-system manipulation – program capability ...
... Operating System Services • Program execution – system capability to load a program into memory and to run it. • I/O operations – since user programs cannot execute I/O operations directly, the operating system must provide some means to perform I/O. • File-system manipulation – program capability ...
Live and Trustworthy Forensic Analysis of Commodity Production
... the alleged compromised host OS is transformed into a guest as it runs [10]. Since the hardware guarantees that the hypervisor is not accessible from the guest code, HyperSleuth remains persistent in the system for all the time necessary to perform the live analysis. On the contrary, other solutions ...
... the alleged compromised host OS is transformed into a guest as it runs [10]. Since the hardware guarantees that the hypervisor is not accessible from the guest code, HyperSleuth remains persistent in the system for all the time necessary to perform the live analysis. On the contrary, other solutions ...
ch1
... operating system running concurrently on one or more CPUs Concurrency by multiplexing the CPUs among the processes ...
... operating system running concurrently on one or more CPUs Concurrency by multiplexing the CPUs among the processes ...
operating system functions
... were complex and time-consuming. As the operating systems were written for ...
... were complex and time-consuming. As the operating systems were written for ...
ARMvisor: System Virtualization for ARM
... and allow hypervisor to manage the resource of system, guest operating system is de-privileged to execute in non-privilege mode while hypervisor is located in privilege level for resource management. Pure virtualization that executes guest OS directly in user mode is proposed under the premise that ...
... and allow hypervisor to manage the resource of system, guest operating system is de-privileged to execute in non-privilege mode while hypervisor is located in privilege level for resource management. Pure virtualization that executes guest OS directly in user mode is proposed under the premise that ...
Operating System Fundamentals
... Each layer is isolated and only interacts directly with the layer below or above it. If you make changes to any one layer, they only directly affect the layer next to it. For example, if you install a new hardware device you do not need to change anything about the user or applications. However, you ...
... Each layer is isolated and only interacts directly with the layer below or above it. If you make changes to any one layer, they only directly affect the layer next to it. For example, if you install a new hardware device you do not need to change anything about the user or applications. However, you ...
TotalView Change Log, 8.0
... Significant scalability and performance improvements This release focuses on a new scalability infrastructure on Linux, Blue Gene/Q and Cray platforms that uses efficient broadcast and reduction operations for a quantum leap in scalability. TotalView can now be used across hundreds of thousands of p ...
... Significant scalability and performance improvements This release focuses on a new scalability infrastructure on Linux, Blue Gene/Q and Cray platforms that uses efficient broadcast and reduction operations for a quantum leap in scalability. TotalView can now be used across hundreds of thousands of p ...
Introduction
... so frequently that users can interact with each job while it is running, creating interactive computing ...
... so frequently that users can interact with each job while it is running, creating interactive computing ...
What is an Operating System?
... system running concurrently on one or more CPUs Concurrency by multiplexing the CPUs among the processes / ...
... system running concurrently on one or more CPUs Concurrency by multiplexing the CPUs among the processes / ...
What is an Operating System?
... so frequently that users can interact with each job while it is running, creating interactive computing ...
... so frequently that users can interact with each job while it is running, creating interactive computing ...
File System
... recovered after a crash, just that the file system data structures (the metadata files) are undamaged and reflect some consistent state prior to the crash The log is stored in the third metadata file at the beginning of the ...
... recovered after a crash, just that the file system data structures (the metadata files) are undamaged and reflect some consistent state prior to the crash The log is stored in the third metadata file at the beginning of the ...
No Slide Title
... recovered after a crash, just that the file system data structures (the metadata files) are undamaged and reflect some consistent state prior to the crash The log is stored in the third metadata file at the beginning of the ...
... recovered after a crash, just that the file system data structures (the metadata files) are undamaged and reflect some consistent state prior to the crash The log is stored in the third metadata file at the beginning of the ...
Virtual Machine Monitors - Computer Sciences User Pages
... Years ago, IBM sold expensive mainframes to large organizations, and a problem arose: what if the organization wanted to run different operating systems on the machine at the same time? Some applications had been developed on one OS, and some on others, and thus the problem. As a solution, IBM intro ...
... Years ago, IBM sold expensive mainframes to large organizations, and a problem arose: what if the organization wanted to run different operating systems on the machine at the same time? Some applications had been developed on one OS, and some on others, and thus the problem. As a solution, IBM intro ...
Virtualization Explained:
... Virtualization allows IT professionals to operate multiple virtual machines on one physical server. This requires the single physical system to create and maintain multiple virtual systems. The core of virtualization is the virtual machine monitor(VMM), which handles many of the tasks essential to s ...
... Virtualization allows IT professionals to operate multiple virtual machines on one physical server. This requires the single physical system to create and maintain multiple virtual systems. The core of virtualization is the virtual machine monitor(VMM), which handles many of the tasks essential to s ...
Shared Memory IPC
... Many aspects of IPC mechanisms are duals of each other Which implies that these mechanisms have the same power First recognized in context of messages vs. procedure calls At least, IPC mechanisms can be simulated by each other Depends on model of computation And on philosophy of user In particular c ...
... Many aspects of IPC mechanisms are duals of each other Which implies that these mechanisms have the same power First recognized in context of messages vs. procedure calls At least, IPC mechanisms can be simulated by each other Depends on model of computation And on philosophy of user In particular c ...