Virtual Machine Monitors Dr. Marc E. Fiuczynski Research Scholar Princeton University
... All instructions that can inspect and modify privileged machine state will trap when executed from any but the most privileged state CPU architecture virtualizable if it supports running VCPU state on real CPU, and VMM retains real control of CPU ...
... All instructions that can inspect and modify privileged machine state will trap when executed from any but the most privileged state CPU architecture virtualizable if it supports running VCPU state on real CPU, and VMM retains real control of CPU ...
EN 1975155
... monitoring system performance. It uses Eclipse framework. Workbench supports VxWorks 6.x and backward compatible with VxWorks 5.5. Workbench contains editor, GNU compiler, debugger and simulator. The Workbench debugger helps to debug VxWorks 6.x targets. It supports debugging for single and multi-co ...
... monitoring system performance. It uses Eclipse framework. Workbench supports VxWorks 6.x and backward compatible with VxWorks 5.5. Workbench contains editor, GNU compiler, debugger and simulator. The Workbench debugger helps to debug VxWorks 6.x targets. It supports debugging for single and multi-co ...
introduction
... to a book case with the code and say: ‘‘Go learn that.’’ And this is only for the part that runs in the kernel. User programs like the GUI, libraries, and basic application software (things like Windows Explorer) can easily run to 10 or 20 times that amount. It should be clear now why operating syst ...
... to a book case with the code and say: ‘‘Go learn that.’’ And this is only for the part that runs in the kernel. User programs like the GUI, libraries, and basic application software (things like Windows Explorer) can easily run to 10 or 20 times that amount. It should be clear now why operating syst ...
P - GCG-42
... from each other, and from changing operating-system code and data. – Relocation register contains value of smallest physical address; limit register contains range of logical addresses – each logical address must be less than the limit register. ...
... from each other, and from changing operating-system code and data. – Relocation register contains value of smallest physical address; limit register contains range of logical addresses – each logical address must be less than the limit register. ...
Comparison of Amoeba Vs Mach Operating Systems
... became available. By 1986, the virtual memory and communication subsystems were running on the DEC VAX computer family, including multiprocessor versions of the VAX. Versions for the IBM RT/PC and for SUN 3 workstations followed shortly. 1987 saw the completion of the Encore Multimax and Sequent Ba ...
... became available. By 1986, the virtual memory and communication subsystems were running on the DEC VAX computer family, including multiprocessor versions of the VAX. Versions for the IBM RT/PC and for SUN 3 workstations followed shortly. 1987 saw the completion of the Encore Multimax and Sequent Ba ...
CPU 메모리 디스크 I/O 통합 CPU, 메모리, 디스크, I/O
... – Scanned data for a single run is currently over 200GB. Memory requirements are expected to grow significantly with the introduction of full body scan with more sensors – Would like the ability to use OpenMP for faster prototyping – Would like to standardize on x86 architecture due to lower costs a ...
... – Scanned data for a single run is currently over 200GB. Memory requirements are expected to grow significantly with the introduction of full body scan with more sensors – Would like the ability to use OpenMP for faster prototyping – Would like to standardize on x86 architecture due to lower costs a ...
This chapter covers the following key topics: • Operating Systems
... Computer programs written for multitasking operating systems themselves often contain multiple independent tasks that run concurrently. These little subprograms are called threads because they form a single thread of instruction execution within the program. Threads each have their own set of CPU re ...
... Computer programs written for multitasking operating systems themselves often contain multiple independent tasks that run concurrently. These little subprograms are called threads because they form a single thread of instruction execution within the program. Threads each have their own set of CPU re ...
The Impact of Architectural Trends on Operating System Performance
... the commercial database system took several tens of billion of instructions which would have taken several months of simulation time on the slowest CPU simulator. Checkpoints. SimOS can save the entire state of its simulated hardware at any time during a simulation. This saved state, which includes ...
... the commercial database system took several tens of billion of instructions which would have taken several months of simulation time on the slowest CPU simulator. Checkpoints. SimOS can save the entire state of its simulated hardware at any time during a simulation. This saved state, which includes ...
Introduction
... device and ask it to give an interrupt when it is finished. • At that point the driver returns. The operating system then blocks the caller if need be and looks for other work to do. • When the controller detects the end of the transfer, it generates an interrupt to signal completion. Interrupts are ...
... device and ask it to give an interrupt when it is finished. • At that point the driver returns. The operating system then blocks the caller if need be and looks for other work to do. • When the controller detects the end of the transfer, it generates an interrupt to signal completion. Interrupts are ...
ch1
... Each device controller is in charge of a specific type of device. More than one device may be attached. For instance, seven or more devices can be attached to the small computersystems interface (SCSI) controller. A device controller maintains some local buffer storage and a set of special-purpose r ...
... Each device controller is in charge of a specific type of device. More than one device may be attached. For instance, seven or more devices can be attached to the small computersystems interface (SCSI) controller. A device controller maintains some local buffer storage and a set of special-purpose r ...
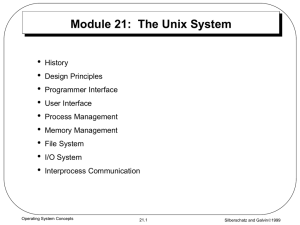
UNIX
... it is rather a naming space for all hardware devices (and their drivers) present in the system, including keyboard, screen etc. The contents of disks is made available in other part of root / hierarchy. ...
... it is rather a naming space for all hardware devices (and their drivers) present in the system, including keyboard, screen etc. The contents of disks is made available in other part of root / hierarchy. ...
Cellular Disco: resource management using
... allocation flexibility of shared-memory systems. Our experience with Cellular Disco shows that: 1. Hardware fault containment can be added to a virtual machine monitor with very low run-time overheads and implementation costs. With a negligible performance penalty over the existing virtualization ov ...
... allocation flexibility of shared-memory systems. Our experience with Cellular Disco shows that: 1. Hardware fault containment can be added to a virtual machine monitor with very low run-time overheads and implementation costs. With a negligible performance penalty over the existing virtualization ov ...
* Abstract
... allocation flexibility of shared-memory systems. Our experience with Cellular Disco shows that: 1. Hardware fault containment can be added to a virtual machine monitor with very low run-time overheads and implementation costs. With a negligible performance penalty over the existing virtualization ov ...
... allocation flexibility of shared-memory systems. Our experience with Cellular Disco shows that: 1. Hardware fault containment can be added to a virtual machine monitor with very low run-time overheads and implementation costs. With a negligible performance penalty over the existing virtualization ov ...
System Software
... engaged in analyzing a source program as the analysis phase of the language processor. Components engaged in synthesizing a target program constitute the synthesis phase. A specification of the source language forms the basis of source program analysis. The specification consists of three components ...
... engaged in analyzing a source program as the analysis phase of the language processor. Components engaged in synthesizing a target program constitute the synthesis phase. A specification of the source language forms the basis of source program analysis. The specification consists of three components ...
operating system concepts
... than a personal computer or single-user workstation? Answer: When there are few other users, the task is large, and the hardware is fast, timesharing makes sense. The full power of the system can be brought to bear on the user’s problem. The problem can be solved faster than on a personal computer. ...
... than a personal computer or single-user workstation? Answer: When there are few other users, the task is large, and the hardware is fast, timesharing makes sense. The full power of the system can be brought to bear on the user’s problem. The problem can be solved faster than on a personal computer. ...
Disco: Running Commodity Operating Systems on Scalable
... machine monitor schedules the virtual resources (processor and memory) of the virtual machines on the physical resources of the scalable multiprocessor. Virtual machine monitors, in combination with commodity and specialized operating systems, form a flexible system software solution for these machi ...
... machine monitor schedules the virtual resources (processor and memory) of the virtual machines on the physical resources of the scalable multiprocessor. Virtual machine monitors, in combination with commodity and specialized operating systems, form a flexible system software solution for these machi ...
9. File Systems and I/O Management
... several such blocks. The most important piece of metadata that must be tracked for a file is its location on disk, i.e., which blocks on disk hold the file’s contents. How does the file system allocate and track the various blocks that belong to a file? There are several ways of allocating blocks to ...
... several such blocks. The most important piece of metadata that must be tracked for a file is its location on disk, i.e., which blocks on disk hold the file’s contents. How does the file system allocate and track the various blocks that belong to a file? There are several ways of allocating blocks to ...
Experience Distributing Objects in an SMMP OS
... argue that the distributed implementations chosen are either optimal or even superior to equivalent highly-concurrent versions—rather it is to validate the methodology and gain insights into the techniques for constructing a system that can feasibly employ locality in a fine-grain fashion. For examp ...
... argue that the distributed implementations chosen are either optimal or even superior to equivalent highly-concurrent versions—rather it is to validate the methodology and gain insights into the techniques for constructing a system that can feasibly employ locality in a fine-grain fashion. For examp ...
Real-time operating system survey
... the task execution time can be estimated prior to execution and the resulting task schedules can be determined off-line. Periodic tasks typically arise from sensor data and control loops, however sporadic tasks can arise from unexpected events caused by the environment or by operator actions. A sche ...
... the task execution time can be estimated prior to execution and the resulting task schedules can be determined off-line. Periodic tasks typically arise from sensor data and control loops, however sporadic tasks can arise from unexpected events caused by the environment or by operator actions. A sche ...
Operating Systems (Notes to prepare in 1 night before Exam)
... 4. From 1970’s (Fourth Generation):- development of LSI(large scale integration) circuits, chips, OS; personal computer and workstation age; multiprocessor technology evolved; DOS and UNIX ...
... 4. From 1970’s (Fourth Generation):- development of LSI(large scale integration) circuits, chips, OS; personal computer and workstation age; multiprocessor technology evolved; DOS and UNIX ...
A Survey of Multiprocessor Operating System Kernels (DRAFT)
... times, and scalability is limited in that the shared global bus imposes limits on the maximum number of processors and memory modules it can accommodate. A NUMA architecture addresses the scalability problem by attaching local memory to each processor. Processors directly access local memory and com ...
... times, and scalability is limited in that the shared global bus imposes limits on the maximum number of processors and memory modules it can accommodate. A NUMA architecture addresses the scalability problem by attaching local memory to each processor. Processors directly access local memory and com ...
A. Windows Networking – (Supplementary/Advanced)
... The kernel distinguishes between interrupts and exceptions in the following way. An interrupt is an asynchronous event (one that can occur at any time) that is unrelated to what the processor is executing. Interrupts are generated primarily by I/O devices, processor clocks, or timers, and they can b ...
... The kernel distinguishes between interrupts and exceptions in the following way. An interrupt is an asynchronous event (one that can occur at any time) that is unrelated to what the processor is executing. Interrupts are generated primarily by I/O devices, processor clocks, or timers, and they can b ...
Memory Safety for Low-Level Software/Hardware Interactions
... (an API) between the kernel and the hardware that enables a lightweight run-time checker to protect hardware resources and their behaviors; and (2) we leverage the existing safety checking mechanisms of the safe execution environment to optimize the extra checks that are needed for this monitoring. ...
... (an API) between the kernel and the hardware that enables a lightweight run-time checker to protect hardware resources and their behaviors; and (2) we leverage the existing safety checking mechanisms of the safe execution environment to optimize the extra checks that are needed for this monitoring. ...
Memory Safety for Low-Level Software/Hardware Interactions
... (an API) between the kernel and the hardware that enables a lightweight run-time checker to protect hardware resources and their behaviors; and (2) we leverage the existing safety checking mechanisms of the safe execution environment to optimize the extra checks that are needed for this monitoring. ...
... (an API) between the kernel and the hardware that enables a lightweight run-time checker to protect hardware resources and their behaviors; and (2) we leverage the existing safety checking mechanisms of the safe execution environment to optimize the extra checks that are needed for this monitoring. ...
File System - dhdurso.org index to available resources
... The inode also contains 15 pointer to the disk blocks containing the files’s data contents. – First 12 point to direct blocks. – Next three point to indirect blocks First indirect block pointer is the address of a single indirect block — an index block containing the addresses of blocks that do co ...
... The inode also contains 15 pointer to the disk blocks containing the files’s data contents. – First 12 point to direct blocks. – Next three point to indirect blocks First indirect block pointer is the address of a single indirect block — an index block containing the addresses of blocks that do co ...