SLES High Level Design Version 3.16 1
... Disk-based file systems................................................................................. 65 5.1.2.1 ext3 file system ......................................................................................... 65 5.1.2.2 ISO 9660 file system for CD-ROM .................................. ...
... Disk-based file systems................................................................................. 65 5.1.2.1 ext3 file system ......................................................................................... 65 5.1.2.2 ISO 9660 file system for CD-ROM .................................. ...
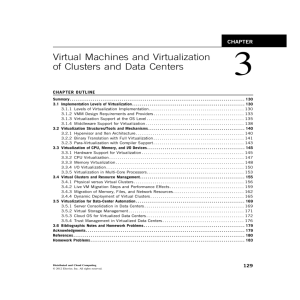
Virtual Machines and Virtualization of Clusters and Data Centers
... There are three requirements for a VMM. First, a VMM should provide an environment for programs which is essentially identical to the original machine. Second, programs run in this environment should show, at worst, only minor decreases in speed. Third, a VMM should be in complete control of the sys ...
... There are three requirements for a VMM. First, a VMM should provide an environment for programs which is essentially identical to the original machine. Second, programs run in this environment should show, at worst, only minor decreases in speed. Third, a VMM should be in complete control of the sys ...
SUSE Linux Enterprise Server 10 SP1 EAL4 High-Level Design Version 1.2.1
... 1.3 Conventions used in this document........................................................................................................1 1.4 Terminology...........................................................................................................................................2 2 ...
... 1.3 Conventions used in this document........................................................................................................1 1.4 Terminology...........................................................................................................................................2 2 ...
RHEL High Level Design Version 1.3
... xSeries, zSeries, zArchitecture, and z/VM are trademarks or registered trademarks of International Business Machines Corporation in the United States, other countries, or both. Linux is a registered trademark of Linus Torvalds. UNIX is a registered trademark of The Open Group in the United States an ...
... xSeries, zSeries, zArchitecture, and z/VM are trademarks or registered trademarks of International Business Machines Corporation in the United States, other countries, or both. Linux is a registered trademark of Linus Torvalds. UNIX is a registered trademark of The Open Group in the United States an ...
SLES High Level Design Version 2.25 1
... Intel and Pentium are trademarks of Intel Corporation in the United States, other countries, or both. Other company, product, and service names may be trademarks or service marks of others. This document is provided “AS IS” with no express or implied warranties. Use the information in this document ...
... Intel and Pentium are trademarks of Intel Corporation in the United States, other countries, or both. Other company, product, and service names may be trademarks or service marks of others. This document is provided “AS IS” with no express or implied warranties. Use the information in this document ...
DB401 64-bit Solutions on SQL Server
... All 32-bit applications are limited to a 4GB virtual address space (VAS) An application can utilize 2GB (3GB using /3gb, or 4GB in x64 WOW). Remainder is reserved for OS addresses Using AWE, some applications can use larger amounts of memory by mapping / unmapping additional memory into the VAS ...
... All 32-bit applications are limited to a 4GB virtual address space (VAS) An application can utilize 2GB (3GB using /3gb, or 4GB in x64 WOW). Remainder is reserved for OS addresses Using AWE, some applications can use larger amounts of memory by mapping / unmapping additional memory into the VAS ...
OPERATING SYSTEM CONCEPTS Avi Silberschatz Department of
... accessible data shared by the CPU and I/O devices. Main memory is a volatile storage device. It loses its contents in the case of system failure. The operating system is responsible for the following activities in connection with memory management: - Keep track of which parts of memory are currently ...
... accessible data shared by the CPU and I/O devices. Main memory is a volatile storage device. It loses its contents in the case of system failure. The operating system is responsible for the following activities in connection with memory management: - Keep track of which parts of memory are currently ...
Systematic setup of compartmentalised systems on the seL4
... of the system. They are controlled by bus managers and user level device drivers. The system architecture grants those compartments access to their hardware and connects them to client applications that require services of these devices. This thesis is about instantiation of such architectures on mo ...
... of the system. They are controlled by bus managers and user level device drivers. The system architecture grants those compartments access to their hardware and connects them to client applications that require services of these devices. This thesis is about instantiation of such architectures on mo ...
chapter 1 - University of Virginia
... is properly saved to the operating system (Anderson). This further increases that amount of work the operating system must perform. Computer systems use a multi-layered approach to memory. Bulk storage devices such as hard drives are used to store information because they are cheap, but they are als ...
... is properly saved to the operating system (Anderson). This further increases that amount of work the operating system must perform. Computer systems use a multi-layered approach to memory. Bulk storage devices such as hard drives are used to store information because they are cheap, but they are als ...
Bringing Virtualization to the x86 Architecture with
... virtualization support, and the industry around it had disaggregated into an ecosystem, with different vendors controlling the computers, CPUs, peripherals, operating systems, and applications, none of them asking for virtualization. We chose to build our solution independently of these vendors. As ...
... virtualization support, and the industry around it had disaggregated into an ecosystem, with different vendors controlling the computers, CPUs, peripherals, operating systems, and applications, none of them asking for virtualization. We chose to build our solution independently of these vendors. As ...
Bringing Virtualization to the x86 Architecture with the Original
... virtualization support, and the industry around it had disaggregated into an ecosystem, with different vendors controlling the computers, CPUs, peripherals, operating systems, and applications, none of them asking for virtualization. We chose to build our solution independently of these vendors. As ...
... virtualization support, and the industry around it had disaggregated into an ecosystem, with different vendors controlling the computers, CPUs, peripherals, operating systems, and applications, none of them asking for virtualization. We chose to build our solution independently of these vendors. As ...
xv6 - PDOS-MIT
... and to provide a more useful set of services than the hardware alone supports. The operating system manages and abstracts the low-level hardware, so that, for example, a word processor need not concern itself with which type of disk hardware is being used. It also multiplexes the hardware, allowing ...
... and to provide a more useful set of services than the hardware alone supports. The operating system manages and abstracts the low-level hardware, so that, for example, a word processor need not concern itself with which type of disk hardware is being used. It also multiplexes the hardware, allowing ...
Linked
... All jobs that enter the system are kept in the job pool (on disk). Several jobs from the job pool are kept in memory at the same time, and the CPU is multiplexed among them. The OS picks and begins execution of one of these jobs. If the job needs to wait for an I/O device the OS switches to executin ...
... All jobs that enter the system are kept in the job pool (on disk). Several jobs from the job pool are kept in memory at the same time, and the CPU is multiplexed among them. The OS picks and begins execution of one of these jobs. If the job needs to wait for an I/O device the OS switches to executin ...
I/O Paravirtualization at the Device File Boundary
... We address two fundamental challenges: (i) the guest process and the device drivers reside in different virtualization domains, creating a memory barrier for executing the driver memory operations on the guest process. Our solution to this problem is to redirect and execute the memory operations ef ...
... We address two fundamental challenges: (i) the guest process and the device drivers reside in different virtualization domains, creating a memory barrier for executing the driver memory operations on the guest process. Our solution to this problem is to redirect and execute the memory operations ef ...
ppt
... Descriptors are allocated by a domain, but accessible from within Xen. Access to the ring is controlled by two pairs of pointers. ...
... Descriptors are allocated by a domain, but accessible from within Xen. Access to the ring is controlled by two pairs of pointers. ...
Proceedings of the General Track: 2003 USENIX Annual Technical Conference
... allows a single server to run multiple, untrusted applications safely [Whitaker02, Meushaw00] and to provide security services such as monitoring systems for intrusions [Chen01, Dunlap02, Barnett02]. As a layer of software, VMMs build on a lowerlevel hardware or software platform and provide an inte ...
... allows a single server to run multiple, untrusted applications safely [Whitaker02, Meushaw00] and to provide security services such as monitoring systems for intrusions [Chen01, Dunlap02, Barnett02]. As a layer of software, VMMs build on a lowerlevel hardware or software platform and provide an inte ...
Proceedings of the General Track: 2003 USENIX Annual Technical Conference
... modular fashion, using several separate components. Although in some cases implementing such an adaptive algorithm may be simple, this approach allows adaptive algorithms to be updated and expanded while the system is running. Each independent algorithm can be developed as a separate component, hot- ...
... modular fashion, using several separate components. Although in some cases implementing such an adaptive algorithm may be simple, this approach allows adaptive algorithms to be updated and expanded while the system is running. Each independent algorithm can be developed as a separate component, hot- ...
Operating System Support for Virtual Machines
... allows a single server to run multiple, untrusted applications safely [Whitaker02, Meushaw00] and to provide security services such as monitoring systems for intrusions [Chen01, Dunlap02, Barnett02]. As a layer of software, VMMs build on a lowerlevel hardware or software platform and provide an inte ...
... allows a single server to run multiple, untrusted applications safely [Whitaker02, Meushaw00] and to provide security services such as monitoring systems for intrusions [Chen01, Dunlap02, Barnett02]. As a layer of software, VMMs build on a lowerlevel hardware or software platform and provide an inte ...
Operating System Support for Virtual Machines
... allows a single server to run multiple, untrusted applications safely [Whitaker02, Meushaw00] and to provide security services such as monitoring systems for intrusions [Chen01, Dunlap02, Barnett02]. As a layer of software, VMMs build on a lowerlevel hardware or software platform and provide an inte ...
... allows a single server to run multiple, untrusted applications safely [Whitaker02, Meushaw00] and to provide security services such as monitoring systems for intrusions [Chen01, Dunlap02, Barnett02]. As a layer of software, VMMs build on a lowerlevel hardware or software platform and provide an inte ...
Perf-tun-srv - Free graphics softwares
... release of the software described herein. The information contained in this document represents the current view of Microsoft Corporation on the issues discussed as of the date of publication. Because Microsoft must respond to changing market conditions, it should not be interpreted to be a commitme ...
... release of the software described herein. The information contained in this document represents the current view of Microsoft Corporation on the issues discussed as of the date of publication. Because Microsoft must respond to changing market conditions, it should not be interpreted to be a commitme ...
Operating systems
... Additional work that might be considered is learning about the particular systems that the students will have access to at your institution. This is still just a general overview, as specific interfaces are considered in Chapter 3. ...
... Additional work that might be considered is learning about the particular systems that the students will have access to at your institution. This is still just a general overview, as specific interfaces are considered in Chapter 3. ...
What is an Operating System? - Department of Mathematics and
... One or more CPUs, device controllers connect through common bus providing access to shared memory ...
... One or more CPUs, device controllers connect through common bus providing access to shared memory ...
Chapter 8: Device Chapter 8: Device Management
... Thin aluminum film sandwiched between two glass or plastic platters To write a bit, bit the drive uses a laser light to burn a small hole through the ...
... Thin aluminum film sandwiched between two glass or plastic platters To write a bit, bit the drive uses a laser light to burn a small hole through the ...
Operating system/IT0307
... Main‐Memory Management • Memory is a large array of words or bytes, each with its own address. It is a repository of quickly accessible data shared by the CPU and I/O devices. • Main memory is a volatile storage device. It loses its contents in the case of system failure. • The operating syste ...
... Main‐Memory Management • Memory is a large array of words or bytes, each with its own address. It is a repository of quickly accessible data shared by the CPU and I/O devices. • Main memory is a volatile storage device. It loses its contents in the case of system failure. • The operating syste ...
Operating System - GH Raisoni College Of Engineering Nagpur
... 12) Explain virtual memory management techniques? 13) Explain following memory allocation strategies with example A)First- fit B)Best- fit C)Worst- fit 14) Explain how address calculation is done segmentation? 15) Explain how to reduce memory overhead in paged system? 16) Explain how virtual memory ...
... 12) Explain virtual memory management techniques? 13) Explain following memory allocation strategies with example A)First- fit B)Best- fit C)Worst- fit 14) Explain how address calculation is done segmentation? 15) Explain how to reduce memory overhead in paged system? 16) Explain how virtual memory ...