The APGAS Library: Resilient Parallel and Distributed Programming
... can spawn local and remote asynchronous tasks (async capability). A task can wait for the completion of all the tasks transitively spawned from it (finish capability). The X10 programming language [1] is an imperative, objectoriented language built upon the APGAS model. Recently X10 has been enriche ...
... can spawn local and remote asynchronous tasks (async capability). A task can wait for the completion of all the tasks transitively spawned from it (finish capability). The X10 programming language [1] is an imperative, objectoriented language built upon the APGAS model. Recently X10 has been enriche ...
call
... Functional languages • Computation=evaluation of math functions. – The output value of a “function” depends only on the arguments that are input to the function ...
... Functional languages • Computation=evaluation of math functions. – The output value of a “function” depends only on the arguments that are input to the function ...
Comparing Common Programming Languages to Parse
... needed only 12.5 seconds to parse the XML file, which makes it the second faster after C# on windows. Furthermore, Java used 40 seconds on Linux which makes it the fourth, after C#, Python, and C++. In terms of lines number, Java needed a lot of lines to write the code that parsed the XML file by us ...
... needed only 12.5 seconds to parse the XML file, which makes it the second faster after C# on windows. Furthermore, Java used 40 seconds on Linux which makes it the fourth, after C#, Python, and C++. In terms of lines number, Java needed a lot of lines to write the code that parsed the XML file by us ...
REAL TIME OPERATING SYSTEMS Lesson-10
... process when a message or event for that was waiting is obtained for the higher priority process. The RTOS kernel has the preemption points at the end of the critical code and therefore the RTOS can be preempted at those points by a real time high priority task. Only small sections in the RTOS funct ...
... process when a message or event for that was waiting is obtained for the higher priority process. The RTOS kernel has the preemption points at the end of the critical code and therefore the RTOS can be preempted at those points by a real time high priority task. Only small sections in the RTOS funct ...
Sams Teach Yourself Beginning Programming in
... Use of a term in this book should not be regarded as affecting the validity of any trademark or service mark. ...
... Use of a term in this book should not be regarded as affecting the validity of any trademark or service mark. ...
Document
... - Fault tolerant systems can be structured through 3 independent error-detection mechanisms - Processes even on different processors can monitor each other to ensure greater robustness. ...
... - Fault tolerant systems can be structured through 3 independent error-detection mechanisms - Processes even on different processors can monitor each other to ensure greater robustness. ...
02history - Computer Science and Electrical Engineering
... • Based on FLOW-MATIC which had such features as: • Names up to 12 characters, with embedded hyphens • English names for arithmetic operators • Data and code were completely separate • Verbs were first word in every statement • CODASYL committee (Conference on Data Systems Languages) developed a pro ...
... • Based on FLOW-MATIC which had such features as: • Names up to 12 characters, with embedded hyphens • English names for arithmetic operators • Data and code were completely separate • Verbs were first word in every statement • CODASYL committee (Conference on Data Systems Languages) developed a pro ...
Project Three
... code are able to manipulate or even see the data. Some object oriented languages also offer characteristics such as aliases, meaning multiple variables use the same space in memory or dynamic variables which will be given memory at runtime and can be deallocated to free up the space. Handling of Abs ...
... code are able to manipulate or even see the data. Some object oriented languages also offer characteristics such as aliases, meaning multiple variables use the same space in memory or dynamic variables which will be given memory at runtime and can be deallocated to free up the space. Handling of Abs ...
Programming Strategically for PK/PD Data
... used. Specified by a control file, which is processed to produce Fortran code that is complied and linked to other objective files to create executive files, NONMEM does not require sophisticate programming skills to build the model(9). This allows pharmacometricians to concentrate on analysis and i ...
... used. Specified by a control file, which is processed to produce Fortran code that is complied and linked to other objective files to create executive files, NONMEM does not require sophisticate programming skills to build the model(9). This allows pharmacometricians to concentrate on analysis and i ...
InfoWorld Home > Application Development > Languages and Standards > 7...
... CouchDB is just the beginning. A number of project managers dealing with "big data" are building systems for storing large volumes of data in a scalable way. Hibari [25], an open source project from Gemini Mobile [26], offers consistent, scalable clusters to store key-value pairs that repair themsel ...
... CouchDB is just the beginning. A number of project managers dealing with "big data" are building systems for storing large volumes of data in a scalable way. Hibari [25], an open source project from Gemini Mobile [26], offers consistent, scalable clusters to store key-value pairs that repair themsel ...
The Scala Experience Safe Programming Can be Fun!
... • Each step is very fast (a small constant number of operations) • There are log2(n) such steps • So it takes ~ log2(n) steps per search • Much faster then ~ n ...
... • Each step is very fast (a small constant number of operations) • There are log2(n) such steps • So it takes ~ log2(n) steps per search • Much faster then ~ n ...
COP2800 * Computer Programming Using JAVA
... PICTURE CREDIT: http://users.soe.ucsc.edu/~charlie/book/notes/summary1-4/sld016.htm ...
... PICTURE CREDIT: http://users.soe.ucsc.edu/~charlie/book/notes/summary1-4/sld016.htm ...
A Survey on SDN Programming Languages: Toward a Taxonomy
... This section discusses the SDN architecture and explains the different ways to program these networks. SDN aims to overcome the conventional network infrastructure limitations; in the existing pre-SDN network infrastructure, each device must be individually configured, eventually causing misconfigur ...
... This section discusses the SDN architecture and explains the different ways to program these networks. SDN aims to overcome the conventional network infrastructure limitations; in the existing pre-SDN network infrastructure, each device must be individually configured, eventually causing misconfigur ...
Computing Scheme of Work 2014 –Year 3
... are written for you to work through at your own pace. You don't need to know anything about programming at the start: you will learn enough at the first stage to write your own programs, and you may surprise yourself by how much you can achieve right away. http://nrich.maths.org/8045 There's a versi ...
... are written for you to work through at your own pace. You don't need to know anything about programming at the start: you will learn enough at the first stage to write your own programs, and you may surprise yourself by how much you can achieve right away. http://nrich.maths.org/8045 There's a versi ...
Ppt - Computer Science and Electrical Engineering
... Modified ALGOL 58 at 6-day meeting in Paris adding such new features as: • Block structure (local scope) • Two parameter passing methods • Subprogram recursion • Stack-dynamic arrays • Still no I/O and no string handling Successes: • The standard way to publish algorithms for over 20 years • All sub ...
... Modified ALGOL 58 at 6-day meeting in Paris adding such new features as: • Block structure (local scope) • Two parameter passing methods • Subprogram recursion • Stack-dynamic arrays • Still no I/O and no string handling Successes: • The standard way to publish algorithms for over 20 years • All sub ...
Chapter 1
... • Portable means that a program may be written on one type of computer and then run on a wide variety of computers, with little or no modification. • Java byte code runs on the JVM and not on any particular CPU; therefore, compiled Java programs are highly portable. • JVMs exist on many platforms: • ...
... • Portable means that a program may be written on one type of computer and then run on a wide variety of computers, with little or no modification. • Java byte code runs on the JVM and not on any particular CPU; therefore, compiled Java programs are highly portable. • JVMs exist on many platforms: • ...
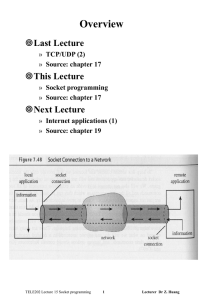
Document
... The socket function creates sockets on demand » result = socket(pf, type, protocol) » pf specifies the protocol family to be used with the socket – PF_INET, TCP/IP internet – PF_UNIX, UNIX file system – PF_APPLETALK, AppleTalk network » type specifies the type of communication desired – SOCK_STREAM ...
... The socket function creates sockets on demand » result = socket(pf, type, protocol) » pf specifies the protocol family to be used with the socket – PF_INET, TCP/IP internet – PF_UNIX, UNIX file system – PF_APPLETALK, AppleTalk network » type specifies the type of communication desired – SOCK_STREAM ...
Lecture 1
... The value of a built-in operator: machine instructions to execute The value of any name: the associated object in the environment To Evaluate a combination: (other than special form) a. Evaluate all of the sub-expressions in any order b. Apply the procedure that is the value of the leftmost subexpre ...
... The value of a built-in operator: machine instructions to execute The value of any name: the associated object in the environment To Evaluate a combination: (other than special form) a. Evaluate all of the sub-expressions in any order b. Apply the procedure that is the value of the leftmost subexpre ...
ppt
... • Assignment scores tend to be high – Serious handicap if you don’t hand a lab in • Tests have big bearing on letter grade – Wider range of scores – Only chance for us to evaluate individual performance ...
... • Assignment scores tend to be high – Serious handicap if you don’t hand a lab in • Tests have big bearing on letter grade – Wider range of scores – Only chance for us to evaluate individual performance ...
An Introduction to Control Structures
... • A BitSet object contains a number of bits, each of which represents a true or false value • You can use a Hashtable collection for keyvalue pairs • The Properties class extends Hashtable and suitable for writing to or reading from I/O streams • The Vector class supports a dynamically resizable lis ...
... • A BitSet object contains a number of bits, each of which represents a true or false value • You can use a Hashtable collection for keyvalue pairs • The Properties class extends Hashtable and suitable for writing to or reading from I/O streams • The Vector class supports a dynamically resizable lis ...
Lecture 12
... same code, perform computations on different portions of the workload, usually involving the periodic exchange of intermediate results. This paradigm can be further subdivided into two categories: The master-slave (or host-node ) model in which a separate ``control'' program termed the master is res ...
... same code, perform computations on different portions of the workload, usually involving the periodic exchange of intermediate results. This paradigm can be further subdivided into two categories: The master-slave (or host-node ) model in which a separate ``control'' program termed the master is res ...
9781285081953_PPT_ch14
... • setEnabled() method – Makes a component unavailable, and then makes it available again in turn – Use after a specific series of actions has taken place ...
... • setEnabled() method – Makes a component unavailable, and then makes it available again in turn – Use after a specific series of actions has taken place ...
AURA: A language with authorization and audit
... Data must be decrypted during computation Encryption must be used consistently with the policy Regulating information-flow through software is hard Auditing is at the wrong level of abstraction (Firewall, OS) Policy is usually expressed at the application level ...
... Data must be decrypted during computation Encryption must be used consistently with the policy Regulating information-flow through software is hard Auditing is at the wrong level of abstraction (Firewall, OS) Policy is usually expressed at the application level ...